/test | 测试是否为只读系统 |
## 在 Glitch 部署重点
这里只作重点的展示,更详细可以参考项目: https://github.com/fscarmen2/X-for-Glitch


 ## 在 Daki 部署重点
## 在 Daki 部署重点






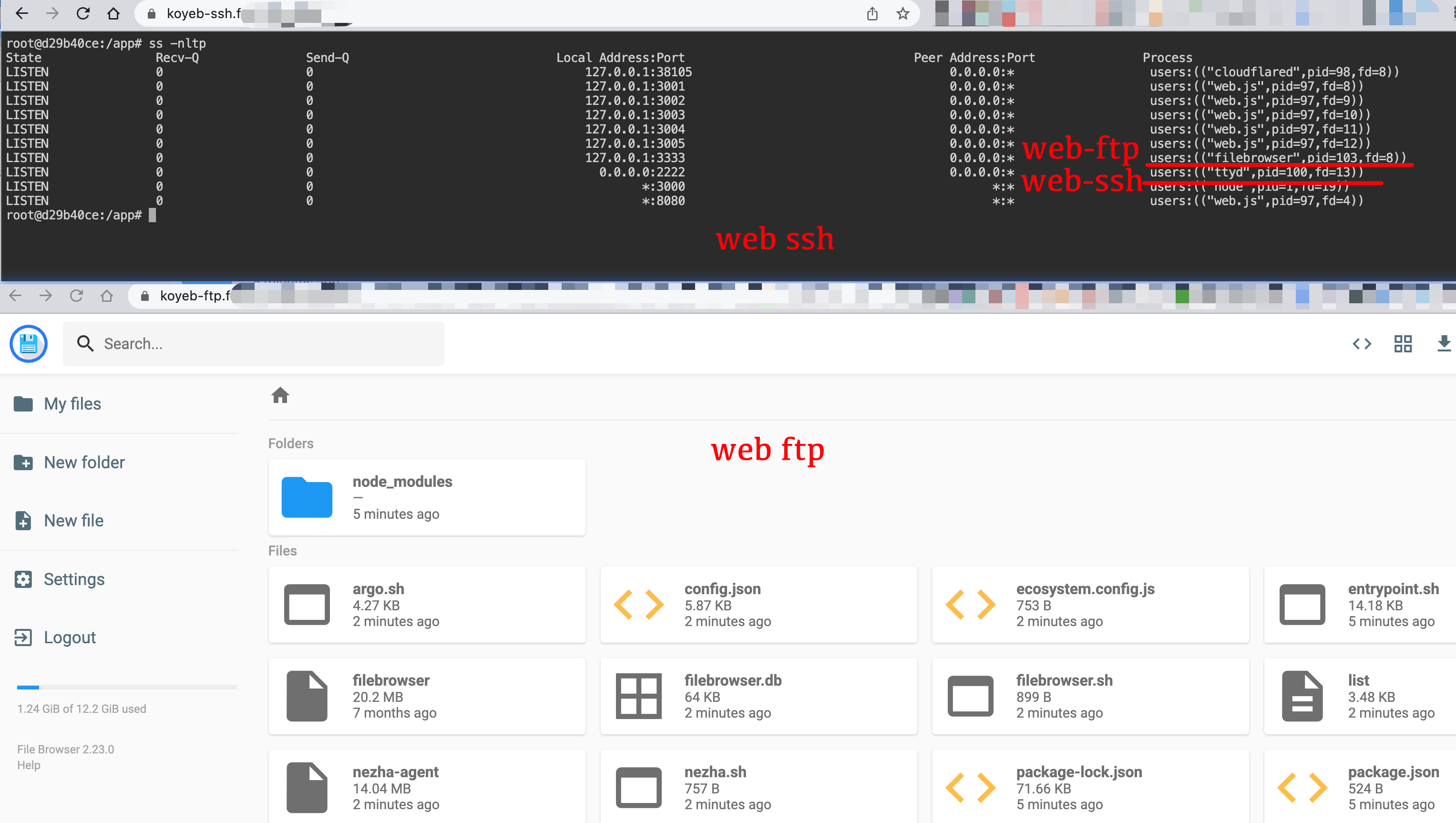
 ## ttyd webssh / filebrowser webftp 的部署
* 原理
```
+---------+ argo +---------+ http +--------+ ssh +-----------+
| browser | <==========> | CF edge | <==========> | ttyd | <=======> | ssh server|
+---------+ argo +---------+ websocket +--------+ ssh +-----------+
+---------+ argo +---------+ http +--------------+ ftp +-----------+
| browser | <==========> | CF edge | <==========> | filebrowser | <=======> | ftp server|
+---------+ argo +---------+ websocket +--------------+ ftp +-----------+
```
* 使用 Json 方式建的隧道
## ttyd webssh / filebrowser webftp 的部署
* 原理
```
+---------+ argo +---------+ http +--------+ ssh +-----------+
| browser | <==========> | CF edge | <==========> | ttyd | <=======> | ssh server|
+---------+ argo +---------+ websocket +--------+ ssh +-----------+
+---------+ argo +---------+ http +--------------+ ftp +-----------+
| browser | <==========> | CF edge | <==========> | filebrowser | <=======> | ftp server|
+---------+ argo +---------+ websocket +--------------+ ftp +-----------+
```
* 使用 Json 方式建的隧道



 ## 鸣谢下列作者的文章和项目:
* 前端 JS 在大佬 Nike Jeff 的项目 基础上,为了通用性和扩展功能作修改,https://github.com/hrzyang/glitch-trojan
* 后端全部原创,如转载须注明来源。
## 免责声明:
* 本程序仅供学习了解, 非盈利目的,请于下载后 24 小时内删除, 不得用作任何商业用途, 文字、数据及图片均有所属版权, 如转载须注明来源。
* 使用本程序必循遵守部署免责声明。使用本程序必循遵守部署服务器所在地、所在国家和用户所在国家的法律法规, 程序作者不对使用者任何不当行为负责。
================================================
FILE: entrypoint.sh
================================================
#!/usr/bin/env bash
# 设置各变量,WS 路径前缀。(注意:伪装路径不需要 / 符号开始,为避免不必要的麻烦,请不要使用特殊符号.)
WSPATH=${WSPATH:-'argo'}
UUID=${UUID:-'de04add9-5c68-8bab-950c-08cd5320df18'}
WEB_USERNAME=${WEB_USERNAME:-'admin'}
WEB_PASSWORD=${WEB_PASSWORD:-'password'}
# 哪吒4个参数,ssl/tls 看是否需要,不需要的话可以留空,删除或在这4行最前面加 # 以注释
NEZHA_SERVER="$NEZHA_SERVER"
NEZHA_PORT="$NEZHA_PORT"
NEZHA_KEY="$NEZHA_KEY"
NEZHA_TLS="$NEZHA_TLS"
# Argo 固定域名隧道的两个参数,这个可以填 Json 内容或 Token 内容,不需要的话可以留空,删除或在这三行最前面加 # 以注释
ARGO_AUTH=''
ARGO_DOMAIN="$ARGO_DOMAIN"
# ttyd / filebrowser argo 域名
SSH_DOMAIN="$SSH_AUTH"
FTP_DOMAIN="$FTP_AUTH"
# 安装系统依赖
check_dependencies() {
DEPS_CHECK=("wget" "unzip" "ss" "tar")
DEPS_INSTALL=(" wget" " unzip" " iproute2" "tar")
for ((i=0;i<${#DEPS_CHECK[@]};i++)); do [[ ! $(type -p ${DEPS_CHECK[i]}) ]] && DEPS+=${DEPS_INSTALL[i]}; done
[ -n "$DEPS" ] && { apt-get update >/dev/null 2>&1; apt-get install -y $DEPS >/dev/null 2>&1; }
}
# 生成 X 配置文件
generate_config() {
cat > config.json << EOF
{
"log":{
"access":"/dev/null",
"error":"/dev/null",
"loglevel":"none"
},
"inbounds":[
{
"port":8080,
"protocol":"vless",
"settings":{
"clients":[
{
"id":"${UUID}",
"flow":"xtls-rprx-vision"
}
],
"decryption":"none",
"fallbacks":[
{
"dest":3001
},
{
"path":"/${WSPATH}-vless",
"dest":3002
},
{
"path":"/${WSPATH}-vmess",
"dest":3003
},
{
"path":"/${WSPATH}-trojan",
"dest":3004
},
{
"path":"/${WSPATH}-shadowsocks",
"dest":3005
}
]
},
"streamSettings":{
"network":"tcp"
}
},
{
"port":3001,
"listen":"127.0.0.1",
"protocol":"vless",
"settings":{
"clients":[
{
"id":"${UUID}"
}
],
"decryption":"none"
},
"streamSettings":{
"network":"ws",
"security":"none"
}
},
{
"port":3002,
"listen":"127.0.0.1",
"protocol":"vless",
"settings":{
"clients":[
{
"id":"${UUID}",
"level":0
}
],
"decryption":"none"
},
"streamSettings":{
"network":"ws",
"security":"none",
"wsSettings":{
"path":"/${WSPATH}-vless"
}
},
"sniffing":{
"enabled":true,
"destOverride":[
"http",
"tls",
"quic"
],
"metadataOnly":false
}
},
{
"port":3003,
"listen":"127.0.0.1",
"protocol":"vmess",
"settings":{
"clients":[
{
"id":"${UUID}",
"alterId":0
}
]
},
"streamSettings":{
"network":"ws",
"wsSettings":{
"path":"/${WSPATH}-vmess"
}
},
"sniffing":{
"enabled":true,
"destOverride":[
"http",
"tls",
"quic"
],
"metadataOnly":false
}
},
{
"port":3004,
"listen":"127.0.0.1",
"protocol":"trojan",
"settings":{
"clients":[
{
"password":"${UUID}"
}
]
},
"streamSettings":{
"network":"ws",
"security":"none",
"wsSettings":{
"path":"/${WSPATH}-trojan"
}
},
"sniffing":{
"enabled":true,
"destOverride":[
"http",
"tls",
"quic"
],
"metadataOnly":false
}
},
{
"port":3005,
"listen":"127.0.0.1",
"protocol":"shadowsocks",
"settings":{
"clients":[
{
"method":"chacha20-ietf-poly1305",
"password":"${UUID}"
}
],
"decryption":"none"
},
"streamSettings":{
"network":"ws",
"wsSettings":{
"path":"/${WSPATH}-shadowsocks"
}
},
"sniffing":{
"enabled":true,
"destOverride":[
"http",
"tls",
"quic"
],
"metadataOnly":false
}
}
],
"dns":{
"servers":[
"https+local://8.8.8.8/dns-query"
]
},
"outbounds":[
{
"protocol":"freedom"
},
{
"tag":"WARP",
"protocol":"wireguard",
"settings":{
"secretKey":"YFYOAdbw1bKTHlNNi+aEjBM3BO7unuFC5rOkMRAz9XY=",
"address":[
"172.16.0.2/32",
"2606:4700:110:8a36:df92:102a:9602:fa18/128"
],
"peers":[
{
"publicKey":"bmXOC+F1FxEMF9dyiK2H5/1SUtzH0JuVo51h2wPfgyo=",
"allowedIPs":[
"0.0.0.0/0",
"::/0"
],
"endpoint":"162.159.193.10:2408"
}
],
"reserved":[78, 135, 76],
"mtu":1280
}
}
],
"routing":{
"domainStrategy":"AsIs",
"rules":[
{
"type":"field",
"domain":[
"domain:openai.com",
"domain:ai.com"
],
"outboundTag":"WARP"
}
]
}
}
EOF
}
generate_argo() {
cat > argo.sh << ABC
#!/usr/bin/env bash
ARGO_AUTH=${ARGO_AUTH}
ARGO_DOMAIN=${ARGO_DOMAIN}
SSH_DOMAIN=${SSH_DOMAIN}
FTP_DOMAIN=${FTP_DOMAIN}
# 下载并运行 Argo
check_file() {
[ ! -e cloudflared ] && wget -O cloudflared https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-amd64 && chmod +x cloudflared
}
run() {
if [[ -n "\${ARGO_AUTH}" && -n "\${ARGO_DOMAIN}" ]]; then
if [[ "\$ARGO_AUTH" =~ TunnelSecret ]]; then
echo "\$ARGO_AUTH" | sed 's@{@{"@g;s@[,:]@"\0"@g;s@}@"}@g' > tunnel.json
cat > tunnel.yml << EOF
tunnel: \$(sed "s@.*TunnelID:\(.*\)}@\1@g" <<< "\$ARGO_AUTH")
credentials-file: $(pwd)/tunnel.json
protocol: http2
ingress:
- hostname: \$ARGO_DOMAIN
service: http://localhost:8080
EOF
[ -n "\${SSH_DOMAIN}" ] && cat >> tunnel.yml << EOF
- hostname: \$SSH_DOMAIN
service: http://localhost:2222
EOF
[ -n "\${FTP_DOMAIN}" ] && cat >> tunnel.yml << EOF
- hostname: \$FTP_DOMAIN
service: http://localhost:3333
EOF
cat >> tunnel.yml << EOF
- service: http_status:404
EOF
nohup ./cloudflared tunnel --edge-ip-version auto --config tunnel.yml run 2>/dev/null 2>&1 &
elif [[ \$ARGO_AUTH =~ ^[A-Z0-9a-z=]{120,250}$ ]]; then
nohup ./cloudflared tunnel --edge-ip-version auto --protocol http2 run --token ${ARGO_AUTH} 2>/dev/null 2>&1 &
fi
else
nohup ./cloudflared tunnel --edge-ip-version auto --protocol http2 --no-autoupdate --url http://localhost:8080 2>/dev/null 2>&1 &
sleep 5
local LOCALHOST=\$(ss -nltp | grep '"cloudflared"' | awk '{print \$4}')
ARGO_DOMAIN=\$(wget -qO- http://\$LOCALHOST/quicktunnel | cut -d\" -f4)
fi
}
export_list() {
VMESS="{ \"v\": \"2\", \"ps\": \"Argo-Vmess\", \"add\": \"icook.hk\", \"port\": \"443\", \"id\": \"${UUID}\", \"aid\": \"0\", \"scy\": \"none\", \"net\": \"ws\", \"type\": \"none\", \"host\": \"\${ARGO_DOMAIN}\", \"path\": \"/${WSPATH}-vmess?ed=2048\", \"tls\": \"tls\", \"sni\": \"\${ARGO_DOMAIN}\", \"alpn\": \"\" }"
cat > list << EOF
*******************************************
V2-rayN:
----------------------------
vless://${UUID}@icook.hk:443?encryption=none&security=tls&sni=\${ARGO_DOMAIN}&type=ws&host=\${ARGO_DOMAIN}&path=%2F${WSPATH}-vless?ed=2048#Argo-Vless
----------------------------
vmess://\$(echo \$VMESS | base64 -w0)
----------------------------
trojan://${UUID}@icook.hk:443?security=tls&sni=\${ARGO_DOMAIN}&type=ws&host=\${ARGO_DOMAIN}&path=%2F${WSPATH}-trojan?ed=2048#Argo-Trojan
----------------------------
ss://$(echo "chacha20-ietf-poly1305:${UUID}@icook.hk:443" | base64 -w0)@icook.hk:443#Argo-Shadowsocks
由于该软件导出的链接不全,请自行处理如下: 传输协议: WS , 伪装域名: \${ARGO_DOMAIN} ,路径: /${WSPATH}-shadowsocks?ed=2048 , 传输层安全: tls , sni: \${ARGO_DOMAIN}
*******************************************
小火箭:
----------------------------
vless://${UUID}@icook.hk:443?encryption=none&security=tls&type=ws&host=\${ARGO_DOMAIN}&path=/${WSPATH}-vless?ed=2048&sni=\${ARGO_DOMAIN}#Argo-Vless
----------------------------
vmess://$(echo "none:${UUID}@icook.hk:443" | base64 -w0)?remarks=Argo-Vmess&obfsParam=\${ARGO_DOMAIN}&path=/${WSPATH}-vmess?ed=2048&obfs=websocket&tls=1&peer=\${ARGO_DOMAIN}&alterId=0
----------------------------
trojan://${UUID}@icook.hk:443?peer=\${ARGO_DOMAIN}&plugin=obfs-local;obfs=websocket;obfs-host=\${ARGO_DOMAIN};obfs-uri=/${WSPATH}-trojan?ed=2048#Argo-Trojan
----------------------------
ss://$(echo "chacha20-ietf-poly1305:${UUID}@icook.hk:443" | base64 -w0)?obfs=wss&obfsParam=\${ARGO_DOMAIN}&path=/${WSPATH}-shadowsocks?ed=2048#Argo-Shadowsocks
*******************************************
Clash:
----------------------------
- {name: Argo-Vless, type: vless, server: icook.hk, port: 443, uuid: ${UUID}, tls: true, servername: \${ARGO_DOMAIN}, skip-cert-verify: false, network: ws, ws-opts: {path: /${WSPATH}-vless?ed=2048, headers: { Host: \${ARGO_DOMAIN}}}, udp: true}
----------------------------
- {name: Argo-Vmess, type: vmess, server: icook.hk, port: 443, uuid: ${UUID}, alterId: 0, cipher: none, tls: true, skip-cert-verify: true, network: ws, ws-opts: {path: /${WSPATH}-vmess?ed=2048, headers: {Host: \${ARGO_DOMAIN}}}, udp: true}
----------------------------
- {name: Argo-Trojan, type: trojan, server: icook.hk, port: 443, password: ${UUID}, udp: true, tls: true, sni: \${ARGO_DOMAIN}, skip-cert-verify: false, network: ws, ws-opts: { path: /${WSPATH}-trojan?ed=2048, headers: { Host: \${ARGO_DOMAIN} } } }
----------------------------
- {name: Argo-Shadowsocks, type: ss, server: icook.hk, port: 443, cipher: chacha20-ietf-poly1305, password: ${UUID}, plugin: v2ray-plugin, plugin-opts: { mode: websocket, host: \${ARGO_DOMAIN}, path: /${WSPATH}-shadowsocks?ed=2048, tls: true, skip-cert-verify: false, mux: false } }
*******************************************
EOF
cat list
}
check_file
run
export_list
ABC
}
generate_nezha() {
cat > nezha.sh << EOF
#!/usr/bin/env bash
# 哪吒的4个参数
NEZHA_SERVER="$NEZHA_SERVER"
NEZHA_PORT="$NEZHA_PORT"
NEZHA_KEY="$NEZHA_KEY"
NEZHA_TLS="$NEZHA_TLS"
# 检测是否已运行
check_run() {
[[ \$(pgrep -laf nezha-agent) ]] && echo "哪吒客户端正在运行中!" && exit
}
# 三个变量不全则不安装哪吒客户端
check_variable() {
[[ -z "\${NEZHA_SERVER}" || -z "\${NEZHA_PORT}" || -z "\${NEZHA_KEY}" ]] && exit
}
# 下载最新版本 Nezha Agent
download_agent() {
if [ ! -e nezha-agent ]; then
URL=\$(wget -qO- -4 "https://api.github.com/repos/nezhahq/agent/releases/latest" | grep -o "https.*linux_amd64.zip")
URL=\${URL:-https://github.com/nezhahq/agent/releases/download/v0.15.6/nezha-agent_linux_amd64.zip}
wget -t 2 -T 10 -N \${URL}
unzip -qod ./ nezha-agent_linux_amd64.zip && rm -f nezha-agent_linux_amd64.zip
fi
}
# 运行客户端
run() {
TLS=\${NEZHA_TLS:+'--tls'}
[[ ! \$PROCESS =~ nezha-agent && -e nezha-agent ]] && ./nezha-agent -s \${NEZHA_SERVER}:\${NEZHA_PORT} -p \${NEZHA_KEY} \${TLS} 2>&1 &
}
check_run
check_variable
download_agent
run
EOF
}
generate_ttyd() {
cat > ttyd.sh << EOF
#!/usr/bin/env bash
# ttyd 三个参数
WEB_USERNAME=${WEB_USERNAME}
WEB_PASSWORD=${WEB_PASSWORD}
SSH_DOMAIN=${SSH_DOMAIN}
# 检测是否已运行
check_run() {
[[ \$(pgrep -lafx ttyd) ]] && echo "ttyd 正在运行中" && exit
}
# ssh argo 域名不设置,则不安装 ttyd 服务端
check_variable() {
[ -z "\${SSH_DOMAIN}" ] && exit
}
# 下载最新版本 ttyd
download_ttyd() {
if [ ! -e ttyd ]; then
URL=\$(wget -qO- "https://api.github.com/repos/tsl0922/ttyd/releases/latest" | grep -o "https.*x86_64")
URL=\${URL:-https://github.com/tsl0922/ttyd/releases/download/1.7.3/ttyd.x86_64}
wget -O ttyd \${URL}
chmod +x ttyd
fi
}
# 运行 ttyd 服务端
run() {
[ -e ttyd ] && nohup ./ttyd -c \${WEB_USERNAME}:\${WEB_PASSWORD} -p 2222 bash >/dev/null 2>&1 &
}
check_run
check_variable
download_ttyd
run
EOF
}
generate_filebrowser () {
cat > filebrowser.sh << EOF
#!/usr/bin/env bash
# filebrowser 三个参数
WEB_USERNAME=${WEB_USERNAME}
WEB_PASSWORD=${WEB_PASSWORD}
FTP_DOMAIN=${FTP_DOMAIN}
# 检测是否已运行
check_run() {
[[ \$(pgrep -lafx filebrowser) ]] && echo "filebrowser 正在运行中" && exit
}
# 若 ftp argo 域名不设置,则不安装 filebrowser
check_variable() {
[ -z "\${FTP_DOMAIN}" ] && exit
}
# 下载最新版本 filebrowser
download_filebrowser() {
if [ ! -e filebrowser ]; then
URL=\$(wget -qO- "https://api.github.com/repos/filebrowser/filebrowser/releases/latest" | grep -o "https.*linux-amd64.*gz")
URL=\${URL:-https://github.com/filebrowser/filebrowser/releases/download/v2.23.0/linux-amd64-filebrowser.tar.gz}
wget -O filebrowser.tar.gz \${URL}
tar xzvf filebrowser.tar.gz filebrowser
rm -f filebrowser.tar.gz
chmod +x filebrowser
fi
}
# 运行 filebrowser 服务端
run() {
PASSWORD_HASH=\$(./filebrowser hash \$WEB_PASSWORD)
[ -e filebrowser ] && nohup ./filebrowser --port 3333 --username \${WEB_USERNAME} --password "\${PASSWORD_HASH}" >/dev/null 2>&1 &
}
check_run
check_variable
download_filebrowser
run
EOF
}
generate_config
generate_argo
generate_nezha
generate_ttyd
generate_filebrowser
[ -e nezha.sh ] && bash nezha.sh
[ -e argo.sh ] && bash argo.sh
[ -e ttyd.sh ] && bash ttyd.sh
[ -e filebrowser.sh ] && bash filebrowser.sh
================================================
FILE: index.js
================================================
const username = process.env.WEB_USERNAME || "admin";
const password = process.env.WEB_PASSWORD || "password";
const url = "http://127.0.0.1";
const port = process.env.PORT || 3000; /* 当容器平台分配不规则端口时,此处需修改为分配端口 */
const express = require("express");
const app = express();
var exec = require("child_process").exec;
const os = require("os");
const { legacyCreateProxyMiddleware } = require("http-proxy-middleware");
var request = require("request");
var fs = require("fs");
var path = require("path");
const auth = require("basic-auth");
app.get("/", function (req, res) {
res.send("hello world");
});
// 页面访问密码
app.use((req, res, next) => {
const user = auth(req);
if (user && user.name === username && user.pass === password) {
return next();
}
res.set("WWW-Authenticate", 'Basic realm="Node"');
return res.status(401).send();
});
//获取系统进程表
app.get("/status", function (req, res) {
let cmdStr = "ps -ef";
exec(cmdStr, function (err, stdout, stderr) {
if (err) {
res.type("html").send("
## 鸣谢下列作者的文章和项目:
* 前端 JS 在大佬 Nike Jeff 的项目 基础上,为了通用性和扩展功能作修改,https://github.com/hrzyang/glitch-trojan
* 后端全部原创,如转载须注明来源。
## 免责声明:
* 本程序仅供学习了解, 非盈利目的,请于下载后 24 小时内删除, 不得用作任何商业用途, 文字、数据及图片均有所属版权, 如转载须注明来源。
* 使用本程序必循遵守部署免责声明。使用本程序必循遵守部署服务器所在地、所在国家和用户所在国家的法律法规, 程序作者不对使用者任何不当行为负责。
================================================
FILE: entrypoint.sh
================================================
#!/usr/bin/env bash
# 设置各变量,WS 路径前缀。(注意:伪装路径不需要 / 符号开始,为避免不必要的麻烦,请不要使用特殊符号.)
WSPATH=${WSPATH:-'argo'}
UUID=${UUID:-'de04add9-5c68-8bab-950c-08cd5320df18'}
WEB_USERNAME=${WEB_USERNAME:-'admin'}
WEB_PASSWORD=${WEB_PASSWORD:-'password'}
# 哪吒4个参数,ssl/tls 看是否需要,不需要的话可以留空,删除或在这4行最前面加 # 以注释
NEZHA_SERVER="$NEZHA_SERVER"
NEZHA_PORT="$NEZHA_PORT"
NEZHA_KEY="$NEZHA_KEY"
NEZHA_TLS="$NEZHA_TLS"
# Argo 固定域名隧道的两个参数,这个可以填 Json 内容或 Token 内容,不需要的话可以留空,删除或在这三行最前面加 # 以注释
ARGO_AUTH=''
ARGO_DOMAIN="$ARGO_DOMAIN"
# ttyd / filebrowser argo 域名
SSH_DOMAIN="$SSH_AUTH"
FTP_DOMAIN="$FTP_AUTH"
# 安装系统依赖
check_dependencies() {
DEPS_CHECK=("wget" "unzip" "ss" "tar")
DEPS_INSTALL=(" wget" " unzip" " iproute2" "tar")
for ((i=0;i<${#DEPS_CHECK[@]};i++)); do [[ ! $(type -p ${DEPS_CHECK[i]}) ]] && DEPS+=${DEPS_INSTALL[i]}; done
[ -n "$DEPS" ] && { apt-get update >/dev/null 2>&1; apt-get install -y $DEPS >/dev/null 2>&1; }
}
# 生成 X 配置文件
generate_config() {
cat > config.json << EOF
{
"log":{
"access":"/dev/null",
"error":"/dev/null",
"loglevel":"none"
},
"inbounds":[
{
"port":8080,
"protocol":"vless",
"settings":{
"clients":[
{
"id":"${UUID}",
"flow":"xtls-rprx-vision"
}
],
"decryption":"none",
"fallbacks":[
{
"dest":3001
},
{
"path":"/${WSPATH}-vless",
"dest":3002
},
{
"path":"/${WSPATH}-vmess",
"dest":3003
},
{
"path":"/${WSPATH}-trojan",
"dest":3004
},
{
"path":"/${WSPATH}-shadowsocks",
"dest":3005
}
]
},
"streamSettings":{
"network":"tcp"
}
},
{
"port":3001,
"listen":"127.0.0.1",
"protocol":"vless",
"settings":{
"clients":[
{
"id":"${UUID}"
}
],
"decryption":"none"
},
"streamSettings":{
"network":"ws",
"security":"none"
}
},
{
"port":3002,
"listen":"127.0.0.1",
"protocol":"vless",
"settings":{
"clients":[
{
"id":"${UUID}",
"level":0
}
],
"decryption":"none"
},
"streamSettings":{
"network":"ws",
"security":"none",
"wsSettings":{
"path":"/${WSPATH}-vless"
}
},
"sniffing":{
"enabled":true,
"destOverride":[
"http",
"tls",
"quic"
],
"metadataOnly":false
}
},
{
"port":3003,
"listen":"127.0.0.1",
"protocol":"vmess",
"settings":{
"clients":[
{
"id":"${UUID}",
"alterId":0
}
]
},
"streamSettings":{
"network":"ws",
"wsSettings":{
"path":"/${WSPATH}-vmess"
}
},
"sniffing":{
"enabled":true,
"destOverride":[
"http",
"tls",
"quic"
],
"metadataOnly":false
}
},
{
"port":3004,
"listen":"127.0.0.1",
"protocol":"trojan",
"settings":{
"clients":[
{
"password":"${UUID}"
}
]
},
"streamSettings":{
"network":"ws",
"security":"none",
"wsSettings":{
"path":"/${WSPATH}-trojan"
}
},
"sniffing":{
"enabled":true,
"destOverride":[
"http",
"tls",
"quic"
],
"metadataOnly":false
}
},
{
"port":3005,
"listen":"127.0.0.1",
"protocol":"shadowsocks",
"settings":{
"clients":[
{
"method":"chacha20-ietf-poly1305",
"password":"${UUID}"
}
],
"decryption":"none"
},
"streamSettings":{
"network":"ws",
"wsSettings":{
"path":"/${WSPATH}-shadowsocks"
}
},
"sniffing":{
"enabled":true,
"destOverride":[
"http",
"tls",
"quic"
],
"metadataOnly":false
}
}
],
"dns":{
"servers":[
"https+local://8.8.8.8/dns-query"
]
},
"outbounds":[
{
"protocol":"freedom"
},
{
"tag":"WARP",
"protocol":"wireguard",
"settings":{
"secretKey":"YFYOAdbw1bKTHlNNi+aEjBM3BO7unuFC5rOkMRAz9XY=",
"address":[
"172.16.0.2/32",
"2606:4700:110:8a36:df92:102a:9602:fa18/128"
],
"peers":[
{
"publicKey":"bmXOC+F1FxEMF9dyiK2H5/1SUtzH0JuVo51h2wPfgyo=",
"allowedIPs":[
"0.0.0.0/0",
"::/0"
],
"endpoint":"162.159.193.10:2408"
}
],
"reserved":[78, 135, 76],
"mtu":1280
}
}
],
"routing":{
"domainStrategy":"AsIs",
"rules":[
{
"type":"field",
"domain":[
"domain:openai.com",
"domain:ai.com"
],
"outboundTag":"WARP"
}
]
}
}
EOF
}
generate_argo() {
cat > argo.sh << ABC
#!/usr/bin/env bash
ARGO_AUTH=${ARGO_AUTH}
ARGO_DOMAIN=${ARGO_DOMAIN}
SSH_DOMAIN=${SSH_DOMAIN}
FTP_DOMAIN=${FTP_DOMAIN}
# 下载并运行 Argo
check_file() {
[ ! -e cloudflared ] && wget -O cloudflared https://github.com/cloudflare/cloudflared/releases/latest/download/cloudflared-linux-amd64 && chmod +x cloudflared
}
run() {
if [[ -n "\${ARGO_AUTH}" && -n "\${ARGO_DOMAIN}" ]]; then
if [[ "\$ARGO_AUTH" =~ TunnelSecret ]]; then
echo "\$ARGO_AUTH" | sed 's@{@{"@g;s@[,:]@"\0"@g;s@}@"}@g' > tunnel.json
cat > tunnel.yml << EOF
tunnel: \$(sed "s@.*TunnelID:\(.*\)}@\1@g" <<< "\$ARGO_AUTH")
credentials-file: $(pwd)/tunnel.json
protocol: http2
ingress:
- hostname: \$ARGO_DOMAIN
service: http://localhost:8080
EOF
[ -n "\${SSH_DOMAIN}" ] && cat >> tunnel.yml << EOF
- hostname: \$SSH_DOMAIN
service: http://localhost:2222
EOF
[ -n "\${FTP_DOMAIN}" ] && cat >> tunnel.yml << EOF
- hostname: \$FTP_DOMAIN
service: http://localhost:3333
EOF
cat >> tunnel.yml << EOF
- service: http_status:404
EOF
nohup ./cloudflared tunnel --edge-ip-version auto --config tunnel.yml run 2>/dev/null 2>&1 &
elif [[ \$ARGO_AUTH =~ ^[A-Z0-9a-z=]{120,250}$ ]]; then
nohup ./cloudflared tunnel --edge-ip-version auto --protocol http2 run --token ${ARGO_AUTH} 2>/dev/null 2>&1 &
fi
else
nohup ./cloudflared tunnel --edge-ip-version auto --protocol http2 --no-autoupdate --url http://localhost:8080 2>/dev/null 2>&1 &
sleep 5
local LOCALHOST=\$(ss -nltp | grep '"cloudflared"' | awk '{print \$4}')
ARGO_DOMAIN=\$(wget -qO- http://\$LOCALHOST/quicktunnel | cut -d\" -f4)
fi
}
export_list() {
VMESS="{ \"v\": \"2\", \"ps\": \"Argo-Vmess\", \"add\": \"icook.hk\", \"port\": \"443\", \"id\": \"${UUID}\", \"aid\": \"0\", \"scy\": \"none\", \"net\": \"ws\", \"type\": \"none\", \"host\": \"\${ARGO_DOMAIN}\", \"path\": \"/${WSPATH}-vmess?ed=2048\", \"tls\": \"tls\", \"sni\": \"\${ARGO_DOMAIN}\", \"alpn\": \"\" }"
cat > list << EOF
*******************************************
V2-rayN:
----------------------------
vless://${UUID}@icook.hk:443?encryption=none&security=tls&sni=\${ARGO_DOMAIN}&type=ws&host=\${ARGO_DOMAIN}&path=%2F${WSPATH}-vless?ed=2048#Argo-Vless
----------------------------
vmess://\$(echo \$VMESS | base64 -w0)
----------------------------
trojan://${UUID}@icook.hk:443?security=tls&sni=\${ARGO_DOMAIN}&type=ws&host=\${ARGO_DOMAIN}&path=%2F${WSPATH}-trojan?ed=2048#Argo-Trojan
----------------------------
ss://$(echo "chacha20-ietf-poly1305:${UUID}@icook.hk:443" | base64 -w0)@icook.hk:443#Argo-Shadowsocks
由于该软件导出的链接不全,请自行处理如下: 传输协议: WS , 伪装域名: \${ARGO_DOMAIN} ,路径: /${WSPATH}-shadowsocks?ed=2048 , 传输层安全: tls , sni: \${ARGO_DOMAIN}
*******************************************
小火箭:
----------------------------
vless://${UUID}@icook.hk:443?encryption=none&security=tls&type=ws&host=\${ARGO_DOMAIN}&path=/${WSPATH}-vless?ed=2048&sni=\${ARGO_DOMAIN}#Argo-Vless
----------------------------
vmess://$(echo "none:${UUID}@icook.hk:443" | base64 -w0)?remarks=Argo-Vmess&obfsParam=\${ARGO_DOMAIN}&path=/${WSPATH}-vmess?ed=2048&obfs=websocket&tls=1&peer=\${ARGO_DOMAIN}&alterId=0
----------------------------
trojan://${UUID}@icook.hk:443?peer=\${ARGO_DOMAIN}&plugin=obfs-local;obfs=websocket;obfs-host=\${ARGO_DOMAIN};obfs-uri=/${WSPATH}-trojan?ed=2048#Argo-Trojan
----------------------------
ss://$(echo "chacha20-ietf-poly1305:${UUID}@icook.hk:443" | base64 -w0)?obfs=wss&obfsParam=\${ARGO_DOMAIN}&path=/${WSPATH}-shadowsocks?ed=2048#Argo-Shadowsocks
*******************************************
Clash:
----------------------------
- {name: Argo-Vless, type: vless, server: icook.hk, port: 443, uuid: ${UUID}, tls: true, servername: \${ARGO_DOMAIN}, skip-cert-verify: false, network: ws, ws-opts: {path: /${WSPATH}-vless?ed=2048, headers: { Host: \${ARGO_DOMAIN}}}, udp: true}
----------------------------
- {name: Argo-Vmess, type: vmess, server: icook.hk, port: 443, uuid: ${UUID}, alterId: 0, cipher: none, tls: true, skip-cert-verify: true, network: ws, ws-opts: {path: /${WSPATH}-vmess?ed=2048, headers: {Host: \${ARGO_DOMAIN}}}, udp: true}
----------------------------
- {name: Argo-Trojan, type: trojan, server: icook.hk, port: 443, password: ${UUID}, udp: true, tls: true, sni: \${ARGO_DOMAIN}, skip-cert-verify: false, network: ws, ws-opts: { path: /${WSPATH}-trojan?ed=2048, headers: { Host: \${ARGO_DOMAIN} } } }
----------------------------
- {name: Argo-Shadowsocks, type: ss, server: icook.hk, port: 443, cipher: chacha20-ietf-poly1305, password: ${UUID}, plugin: v2ray-plugin, plugin-opts: { mode: websocket, host: \${ARGO_DOMAIN}, path: /${WSPATH}-shadowsocks?ed=2048, tls: true, skip-cert-verify: false, mux: false } }
*******************************************
EOF
cat list
}
check_file
run
export_list
ABC
}
generate_nezha() {
cat > nezha.sh << EOF
#!/usr/bin/env bash
# 哪吒的4个参数
NEZHA_SERVER="$NEZHA_SERVER"
NEZHA_PORT="$NEZHA_PORT"
NEZHA_KEY="$NEZHA_KEY"
NEZHA_TLS="$NEZHA_TLS"
# 检测是否已运行
check_run() {
[[ \$(pgrep -laf nezha-agent) ]] && echo "哪吒客户端正在运行中!" && exit
}
# 三个变量不全则不安装哪吒客户端
check_variable() {
[[ -z "\${NEZHA_SERVER}" || -z "\${NEZHA_PORT}" || -z "\${NEZHA_KEY}" ]] && exit
}
# 下载最新版本 Nezha Agent
download_agent() {
if [ ! -e nezha-agent ]; then
URL=\$(wget -qO- -4 "https://api.github.com/repos/nezhahq/agent/releases/latest" | grep -o "https.*linux_amd64.zip")
URL=\${URL:-https://github.com/nezhahq/agent/releases/download/v0.15.6/nezha-agent_linux_amd64.zip}
wget -t 2 -T 10 -N \${URL}
unzip -qod ./ nezha-agent_linux_amd64.zip && rm -f nezha-agent_linux_amd64.zip
fi
}
# 运行客户端
run() {
TLS=\${NEZHA_TLS:+'--tls'}
[[ ! \$PROCESS =~ nezha-agent && -e nezha-agent ]] && ./nezha-agent -s \${NEZHA_SERVER}:\${NEZHA_PORT} -p \${NEZHA_KEY} \${TLS} 2>&1 &
}
check_run
check_variable
download_agent
run
EOF
}
generate_ttyd() {
cat > ttyd.sh << EOF
#!/usr/bin/env bash
# ttyd 三个参数
WEB_USERNAME=${WEB_USERNAME}
WEB_PASSWORD=${WEB_PASSWORD}
SSH_DOMAIN=${SSH_DOMAIN}
# 检测是否已运行
check_run() {
[[ \$(pgrep -lafx ttyd) ]] && echo "ttyd 正在运行中" && exit
}
# ssh argo 域名不设置,则不安装 ttyd 服务端
check_variable() {
[ -z "\${SSH_DOMAIN}" ] && exit
}
# 下载最新版本 ttyd
download_ttyd() {
if [ ! -e ttyd ]; then
URL=\$(wget -qO- "https://api.github.com/repos/tsl0922/ttyd/releases/latest" | grep -o "https.*x86_64")
URL=\${URL:-https://github.com/tsl0922/ttyd/releases/download/1.7.3/ttyd.x86_64}
wget -O ttyd \${URL}
chmod +x ttyd
fi
}
# 运行 ttyd 服务端
run() {
[ -e ttyd ] && nohup ./ttyd -c \${WEB_USERNAME}:\${WEB_PASSWORD} -p 2222 bash >/dev/null 2>&1 &
}
check_run
check_variable
download_ttyd
run
EOF
}
generate_filebrowser () {
cat > filebrowser.sh << EOF
#!/usr/bin/env bash
# filebrowser 三个参数
WEB_USERNAME=${WEB_USERNAME}
WEB_PASSWORD=${WEB_PASSWORD}
FTP_DOMAIN=${FTP_DOMAIN}
# 检测是否已运行
check_run() {
[[ \$(pgrep -lafx filebrowser) ]] && echo "filebrowser 正在运行中" && exit
}
# 若 ftp argo 域名不设置,则不安装 filebrowser
check_variable() {
[ -z "\${FTP_DOMAIN}" ] && exit
}
# 下载最新版本 filebrowser
download_filebrowser() {
if [ ! -e filebrowser ]; then
URL=\$(wget -qO- "https://api.github.com/repos/filebrowser/filebrowser/releases/latest" | grep -o "https.*linux-amd64.*gz")
URL=\${URL:-https://github.com/filebrowser/filebrowser/releases/download/v2.23.0/linux-amd64-filebrowser.tar.gz}
wget -O filebrowser.tar.gz \${URL}
tar xzvf filebrowser.tar.gz filebrowser
rm -f filebrowser.tar.gz
chmod +x filebrowser
fi
}
# 运行 filebrowser 服务端
run() {
PASSWORD_HASH=\$(./filebrowser hash \$WEB_PASSWORD)
[ -e filebrowser ] && nohup ./filebrowser --port 3333 --username \${WEB_USERNAME} --password "\${PASSWORD_HASH}" >/dev/null 2>&1 &
}
check_run
check_variable
download_filebrowser
run
EOF
}
generate_config
generate_argo
generate_nezha
generate_ttyd
generate_filebrowser
[ -e nezha.sh ] && bash nezha.sh
[ -e argo.sh ] && bash argo.sh
[ -e ttyd.sh ] && bash ttyd.sh
[ -e filebrowser.sh ] && bash filebrowser.sh
================================================
FILE: index.js
================================================
const username = process.env.WEB_USERNAME || "admin";
const password = process.env.WEB_PASSWORD || "password";
const url = "http://127.0.0.1";
const port = process.env.PORT || 3000; /* 当容器平台分配不规则端口时,此处需修改为分配端口 */
const express = require("express");
const app = express();
var exec = require("child_process").exec;
const os = require("os");
const { legacyCreateProxyMiddleware } = require("http-proxy-middleware");
var request = require("request");
var fs = require("fs");
var path = require("path");
const auth = require("basic-auth");
app.get("/", function (req, res) {
res.send("hello world");
});
// 页面访问密码
app.use((req, res, next) => {
const user = auth(req);
if (user && user.name === username && user.pass === password) {
return next();
}
res.set("WWW-Authenticate", 'Basic realm="Node"');
return res.status(401).send();
});
//获取系统进程表
app.get("/status", function (req, res) {
let cmdStr = "ps -ef";
exec(cmdStr, function (err, stdout, stderr) {
if (err) {
res.type("html").send("命令行执行错误:\n" + err + "
");
}
else {
res.type("html").send("获取系统进程表:\n" + stdout + "
");
}
});
});
//获取系统监听端口
app.get("/listen", function (req, res) {
let cmdStr = "ss -nltp";
exec(cmdStr, function (err, stdout, stderr) {
if (err) {
res.type("html").send("命令行执行错误:\n" + err + "
");
}
else {
res.type("html").send("获取系统监听端口:\n" + stdout + "
");
}
});
});
//获取节点数据
app.get("/list", function (req, res) {
let cmdStr = "cat list";
exec(cmdStr, function (err, stdout, stderr) {
if (err) {
res.type("html").send("命令行执行错误:\n" + err + "
");
}
else {
res.type("html").send("节点数据:\n\n" + stdout + "
");
}
});
});
//获取系统版本、内存信息
app.get("/info", function (req, res) {
let cmdStr = "cat /etc/*release | grep -E ^NAME";
exec(cmdStr, function (err, stdout, stderr) {
if (err) {
res.send("命令行执行错误:" + err);
}
else {
res.send(
"命令行执行结果:\n" +
"Linux System:" +
stdout +
"\nRAM:" +
os.totalmem() / 1000 / 1000 +
"MB"
);
}
});
});
//文件系统只读测试
app.get("/test", function (req, res) {
let cmdStr = 'mount | grep " / " | grep "(ro," >/dev/null';
exec(cmdStr, function (error, stdout, stderr) {
if (error !== null) {
res.send("系统权限为---非只读");
} else {
res.send("系统权限为---只读");
}
});
});
// keepalive begin
//web保活
function keep_web_alive() {
// 1.请求主页,保持唤醒
exec("curl -m8 " + url + ":" + port, function (err, stdout, stderr) {
if (err) {
console.log("保活-请求主页-命令行执行错误:" + err);
} else {
console.log("保活-请求主页-命令行执行成功,响应报文:" + stdout);
}
});
// 2.请求服务器进程状态列表,若web没在运行,则调起
exec("pgrep -laf web.js", function (err, stdout, stderr) {
// 1.查后台系统进程,保持唤醒
if (stdout.includes("./web.js -c ./config.json")) {
console.log("web 正在运行");
}
else {
//web 未运行,命令行调起
exec(
"chmod +x web.js && ./web.js -c ./config.json >/dev/null 2>&1 &", function (err, stdout, stderr) {
if (err) {
console.log("保活-调起web-命令行执行错误:" + err);
}
else {
console.log("保活-调起web-命令行执行成功!");
}
}
);
}
});
}
setInterval(keep_web_alive, 10 * 1000);
//Argo保活
function keep_argo_alive() {
exec("pgrep -laf cloudflared", function (err, stdout, stderr) {
// 1.查后台系统进程,保持唤醒
if (stdout.includes("./cloudflared")) {
console.log("Argo 正在运行");
}
else {
//Argo 未运行,命令行调起
exec(
"bash argo.sh 2>&1 &", function (err, stdout, stderr) {
if (err) {
console.log("保活-调起Argo-命令行执行错误:" + err);
}
else {
console.log("保活-调起Argo-命令行执行成功!");
}
}
);
}
});
}
setInterval(keep_argo_alive, 30 * 1000);
//哪吒保活
function keep_nezha_alive() {
exec("pgrep -laf nezha-agent", function (err, stdout, stderr) {
// 1.查后台系统进程,保持唤醒
if (stdout.includes("./nezha-agent")) {
console.log("哪吒正在运行");
}
else {
//哪吒未运行,命令行调起
exec(
"bash nezha.sh 2>&1 &", function (err, stdout, stderr) {
if (err) {
console.log("保活-调起哪吒-命令行执行错误:" + err);
}
else {
console.log("保活-调起哪吒-命令行执行成功!");
}
}
);
}
});
}
setInterval(keep_nezha_alive, 45 * 1000);
// keepalive end
//下载web可执行文件
app.get("/download", function (req, res) {
download_web((err) => {
if (err) {
res.send("下载文件失败");
}
else {
res.send("下载文件成功");
}
});
});
app.use( /* 具体配置项迁移参见 https://github.com/chimurai/http-proxy-middleware/blob/master/MIGRATION.md */
legacyCreateProxyMiddleware({
target: 'http://127.0.0.1:8080/', /* 需要跨域处理的请求地址 */
ws: true, /* 是否代理websocket */
changeOrigin: true, /* 是否需要改变原始主机头为目标URL,默认false */
on: { /* http代理事件集 */
proxyRes: function proxyRes(proxyRes, req, res) { /* 处理代理请求 */
// console.log('RAW Response from the target', JSON.stringify(proxyRes.headers, true, 2)); //for debug
// console.log(req) //for debug
// console.log(res) //for debug
},
proxyReq: function proxyReq(proxyReq, req, res) { /* 处理代理响应 */
// console.log(proxyReq); //for debug
// console.log(req) //for debug
// console.log(res) //for debug
},
error: function error(err, req, res) { /* 处理异常 */
console.warn('websocket error.', err);
}
},
pathRewrite: {
'^/': '/', /* 去除请求中的斜线号 */
},
// logger: console /* 是否打开log日志 */
})
);
//初始化,下载web
function download_web(callback) {
let fileName = "web.js";
let web_url =
"https://github.com/fscarmen2/Argo-X-Container-PaaS/raw/main/files/web.js";
let stream = fs.createWriteStream(path.join("./", fileName));
request(web_url)
.pipe(stream)
.on("close", function (err) {
if (err) {
callback("下载文件失败");
}
else {
callback(null);
}
});
}
download_web((err) => {
if (err) {
console.log("初始化-下载web文件失败");
}
else {
console.log("初始化-下载web文件成功");
}
});
//启动核心脚本运行web,哪吒和argo
exec("bash entrypoint.sh", function (err, stdout, stderr) {
if (err) {
console.error(err);
return;
}
console.log(stdout);
});
console.log(`Username is: ${username}`);
console.log(`Password is: ${password}`);
app.listen(port, () => console.log(`Example app listening on port ${port}!`));
================================================
FILE: package.json
================================================
{
"name": "express-hello-world",
"version": "1.0.0",
"description": "Express Hello World",
"main": "index.js",
"repository": "https://github.com/fscarmen2/Argo-X-JS-PaaS",
"author": "fscarmen",
"license": "MIT",
"private": false,
"scripts": {
"start": "node index.js"
},
"dependencies": {
"express": "^4.18.2",
"http-proxy-middleware": "^3.0.0-beta.0",
"request": "^2.88.2",
"basic-auth": "^2.0.1"
},
"engines": {
"node": ">=14"
}
} * 需要应用的 js
| 命令 | 说明 |
| ---- |------ |
|
* 需要应用的 js
| 命令 | 说明 |
| ---- |------ |
| 

 ## 在 Daki 部署重点
## 在 Daki 部署重点






 ## ttyd webssh / filebrowser webftp 的部署
* 原理
```
+---------+ argo +---------+ http +--------+ ssh +-----------+
| browser | <==========> | CF edge | <==========> | ttyd | <=======> | ssh server|
+---------+ argo +---------+ websocket +--------+ ssh +-----------+
+---------+ argo +---------+ http +--------------+ ftp +-----------+
| browser | <==========> | CF edge | <==========> | filebrowser | <=======> | ftp server|
+---------+ argo +---------+ websocket +--------------+ ftp +-----------+
```
* 使用 Json 方式建的隧道
## ttyd webssh / filebrowser webftp 的部署
* 原理
```
+---------+ argo +---------+ http +--------+ ssh +-----------+
| browser | <==========> | CF edge | <==========> | ttyd | <=======> | ssh server|
+---------+ argo +---------+ websocket +--------+ ssh +-----------+
+---------+ argo +---------+ http +--------------+ ftp +-----------+
| browser | <==========> | CF edge | <==========> | filebrowser | <=======> | ftp server|
+---------+ argo +---------+ websocket +--------------+ ftp +-----------+
```
* 使用 Json 方式建的隧道

 ## 部署:
### PaaS 平台用到的变量:
* 在 `server.js` 文件的第1、2行修改查询网页的用户名和密码
| 变量名 | 是否必须 | 默认值 | 备注 |
| ------------ | ------ | ------ | ------ |
| WEB_USERNAME | 是 | admin | 网页的用户名 |
| WEB_PASSWORD | 是 | password | 网页的密码 |
## 部署:
### PaaS 平台用到的变量:
* 在 `server.js` 文件的第1、2行修改查询网页的用户名和密码
| 变量名 | 是否必须 | 默认值 | 备注 |
| ------------ | ------ | ------ | ------ |
| WEB_USERNAME | 是 | admin | 网页的用户名 |
| WEB_PASSWORD | 是 | password | 网页的密码 |
 * 在 `entrypoint.sh` 文件的前面 4-15 行修改;访问页面的认证在 `server.js` 文件的第1、2行修改必填
| 变量名 | 是否必须 | 默认值 | 备注 |
| ------------ | ------ | ------ | ------ |
| UUID | 否 | de04add9-5c68-8bab-950c-08cd5320df18 | 可在线生成 https://www.zxgj.cn/g/uuid |
| WSPATH | 否 | argo | 勿以 / 开头,各协议路径为 `/WSPATH-协议`,如 `/argo-vless`,`/argo-vmess`,`/argo-trojan`,`/argo-shadowsocks` |
| NEZHA_SERVER | 否 | | 哪吒探针服务端的 IP 或域名 |
| NEZHA_PORT | 否 | | 哪吒探针服务端的端口 |
| NEZHA_KEY | 否 | | 哪吒探针客户端专用 Key |
| NEZHA_TLS | 否 | | 哪吒探针是否启用 SSL/TLS 加密 ,如不启用请删除,如要启用填"1" |
| ARGO_AUTH | 否 | | Argo 的 Token 或者 json 值,其中 json 可以通过以下网站,在不需绑卡的情况下轻松获取: https://fscarmen.cloudflare.now.cc/ |
| ARGO_DOMAIN | 否 | | Argo 的域名,须与 ARGO_DOMAIN 必需一起填了才能生效 |
| SSH_DOMAIN | 否 | | webssh 的域名,用户名和密码就是
* 在 `entrypoint.sh` 文件的前面 4-15 行修改;访问页面的认证在 `server.js` 文件的第1、2行修改必填
| 变量名 | 是否必须 | 默认值 | 备注 |
| ------------ | ------ | ------ | ------ |
| UUID | 否 | de04add9-5c68-8bab-950c-08cd5320df18 | 可在线生成 https://www.zxgj.cn/g/uuid |
| WSPATH | 否 | argo | 勿以 / 开头,各协议路径为 `/WSPATH-协议`,如 `/argo-vless`,`/argo-vmess`,`/argo-trojan`,`/argo-shadowsocks` |
| NEZHA_SERVER | 否 | | 哪吒探针服务端的 IP 或域名 |
| NEZHA_PORT | 否 | | 哪吒探针服务端的端口 |
| NEZHA_KEY | 否 | | 哪吒探针客户端专用 Key |
| NEZHA_TLS | 否 | | 哪吒探针是否启用 SSL/TLS 加密 ,如不启用请删除,如要启用填"1" |
| ARGO_AUTH | 否 | | Argo 的 Token 或者 json 值,其中 json 可以通过以下网站,在不需绑卡的情况下轻松获取: https://fscarmen.cloudflare.now.cc/ |
| ARGO_DOMAIN | 否 | | Argo 的域名,须与 ARGO_DOMAIN 必需一起填了才能生效 |
| SSH_DOMAIN | 否 | | webssh 的域名,用户名和密码就是