 
# Version
**Version-2.0**
- Changelog:
- Changed the method of deployment. Deprecation of virtual machines as a worker engine to deployments in k8s. Thanks to "Hilbert Team" for contribution

# Version
**Version-2.0**
- Changelog:
- Changed the method of deployment. Deprecation of virtual machines as a worker engine to deployments in k8s. Thanks to "Hilbert Team" for contribution
 - Docker images:
- `cr.yandex/sol/k8s-events-siem-worker:2.0.0`.
**Version-2.0**
- Changelog:
- Added support for automatic Kyverno installation with policies in the audit mode.
- Docker images:
- `cr.yandex/sol/k8s-events-siem-worker:1.1.0`.
# Table of contents
- [Description](#description)
- [Link to the solution "Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"](#link-to-solution-"Collecting-monitoring-and-analyzing-audit-logs-in-Yandex-Managed-Service-for-Elasticsearch-(ELK)")
- [Generic diagram](#generic-diagram)
- [Terraform description](#terraform-description)
- [Content update process](#content-update-process)
- [Optional manual actions](#optional-manual-actions)
## Description
Here are the out-of-the-box features of the solution:
☑️ Collect [K8s audit logs](https://kubernetes.io/docs/tasks/debug-application-cluster/audit/) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/).
- ☑️ Install [Falco](https://falco.org/) and collect its [Alerts](https://falco.org/docs/alerts/) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/).
- ☑️ Install [Kyverno](https://kyverno.io/) with the [Pod Security Standards (Restricted)](https://kyverno.io/policies/?policytypes=Pod%2520Security%2520Standards%2520%28Restricted%29) policies in the audit mode and collect its [Alerts (Policy Reports)](https://kyverno.io/docs/policy-reports/) using [Policy Reporter](https://github.com/kyverno/policy-reporter).
- ☑️ Import Security Content: dashboards, detection rules, and so on (see the Security Content section) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/) to enable analysis and response to information security events.
- ☑️ This also includes importing Security Content for [OPA Gatekeeper](https://open-policy-agent.github.io/gatekeeper/website/docs/) (in the enforce mode). You can install OPA Gatekeeper manually if needed.
- ☑️ Create indexes in two replicas, set up the basic rollover policy (creating of new indexes every thirty days or when 50 GB are reached) to enable provisioning of high data availability and to set up data snapshots in S3, see [recommendations](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md).
## Link to the solution "Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"
The solution ["Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main) contains information on how to install Yandex Managed Service for Elasticsearch (ELK) and collect logs from Audit Trails in it.
## Generic diagram

## Description of imported ELK (Security Content) object
See a detailed description of the objects [here](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf).
## Terraform description
The solution consist of terraform module:
- It accepts the following input:
- `folder_id`: The ID of the folder where the cluster is hosted.
- `cloud_id`: The ID of the cloud where the cluster is hosted.
- `cluster_name`: The name of the Kubernetes cluster.
- `elastic_server`: The FQDN address of the ELK installation
- `elastic_pw` and `elastic_user`: The ELK user credentials for event import
- `service_account_id`: The ID of the service account that can write to the bucket and has the *ymq.admin* role.
- `log_bucket_name`: The name of the bucket that will create module to save logs to.
- `auditlog_enabled`: *true* or *false* (enables/disables sending of K8s audit logs to ELK).
- `falco_enabled`: *true* or *false* (enables/disables sending of Falco alerts to ELK).
- `kyverno_enabled`: *true* or *false* — (enables/disables sending of Kyverno alerts to ELK).
- Functionality:
- Create a static key for the service account.
- Create a function and a trigger for writing cluster logs to S3.
- Install Falco and pre-configured falcosidekick that will send logs to S3.
- Install Kyverno and pre-configured [Policy Reporter](https://github.com/kyverno/policy-reporter) that will send logs to S3.
- Create YMQ queues with log file names in S3.
- Create functions to push file names from S3 to YMQ.
- Create triggers for interaction between queues and functions.
- Create deployments in k8s with worker containers that import events from S3 to ELK.
#### Prerequisites:
- :white_check_mark: Cluster Managed K8s.
- :white_check_mark: Managed ELK.
- :white_check_mark: A service account that can write to the bucket and has the *ymq.admin* role.
#### Example of calling modules:
See the example of calling modules in [/examples/README.md](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_k8s/examples/README.md)
## Content update process
We recommend subscribing to this repository to receive update notifications.
For content updates, make sure that you are running the latest available image version:
`cr.yandex/sol/k8s-events-siem-worker:latest`
You can update the container as follows:
You can re-create the deployments in k8s via Terraform (change worker_docker_image env in tfvars and run `terraform apply`).
## Optional manual actions
#### Installing OPA Gatekeeper (Helm)
If you prefer OPA Gatekeeper to Kyverno, set the value `kyverno_enabled` to *false* when calling the module, then run the manual installation:
- Install OPA Gatekeeper [using Helm](https://open-policy-agent.github.io/gatekeeper/website/docs/install/#deploying-via-helm).
- Select and install the required constraint template and constraint from [gatekeeper-library](https://github.com/open-policy-agent/gatekeeper-library/tree/master/library/pod-security-policy).
- [Installation example](https://github.com/open-policy-agent/gatekeeper-library#usage).
## Recommendations for setting up retention, rollover, and snapshots:
[Recommendations for setting up retention, rollover, and snapshots](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/README.md
================================================
## Terraform test script
Prerequisites:
- ✅ Cluster of Managed K8s.
- ✅ Managed ELK.
- ✅ A service account that can write to the bucket and has the *ymq.admin* role.
##
1) If you doing this from Russia just create the file and fill it out like this to use yandex network mirror:
```
cat ~/.terraformrc
provider_installation {
network_mirror {
url = "https://terraform-network-mirror.storage.yandexcloud.net/"
}
}
```
2) Fill out the fields in the provider.tf file.
3) Fill out the fields in the terraform.tfvars.example file. (example below)
4) Delete <.example> from the end of the file - terraform.tfvars
5) Run:
```
terraform init
terraform apply
```
Example of terraform.tfvars.example file:
```
folder_id = "example"
cloud_id = "example"
cluster_name = "example-cluster"
elastic_server = "https://example-es.rw.mdb.yandexcloud.net"
elastic_pw = "str0ng_password"
elastic_user = "example_user"
service_account_id = "k8s-audit-logs-example"
log_bucket_name = "k8s-audit-logs-example" #name of cluster that will be create
worker_docker_image = "cr.yandex/sol/k8s-events-siem-worker:2.0.0"
create_namespace = true
auditlog_enabled = true
auditlogs_prefix = "AUDIT/"
auditlog_worker_chart_name = "auditlog-worker-example"
auditlog_worker_namespace = "infra-auditlog-example"
auditlog_worker_replicas_count = 1
falco_enabled = true
falco_prefix = "FALCO/"
falco_worker_chart_name = "falco-worker-example"
falco_worker_namespace = "infra-auditlog-example"
falco_worker_replicas_count = 3
falco_helm_namespace = "falco-example"
falco_version = "1.17.0"
falcosidekick_version = "0.4.4"
kyverno_enabled = true
kyverno_prefix = "KYVERNO/"
kyverno_worker_chart_name = "kyverno-worker-example"
kyverno_worker_namespace = "infra-auditlog-example"
kyverno_worker_replicas_count = 1
kyverno_helm_namespace = "kyverno-example"
kyverno_version = "2.1.10"
kyverno_policies_version = "2.1.10"
policy_reporter_version = "2.2.3"
fakeeventgenerator_enabled = false
```
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/main.tf
================================================
module "security-events-to-siem-importer" {
source = "../modules"
folder_id = var.folder_id
cloud_id = var.cloud_id
cluster_name = var.cluster_name
elastic_server = var.elastic_server
elastic_pw = var.elastic_pw
elastic_user = var.elastic_user
service_account_id = var.service_account_id
log_bucket_name = var.log_bucket_name
create_namespace = var.create_namespace
worker_docker_image = var.worker_docker_image
auditlog_enabled = var.auditlog_enabled
auditlogs_prefix = var.auditlogs_prefix
auditlog_worker_chart_name = var.auditlog_worker_chart_name
auditlog_worker_namespace = var.auditlog_worker_namespace
auditlog_worker_replicas_count = var.auditlog_worker_replicas_count
falco_enabled = var.falco_enabled
falco_prefix = var.falco_prefix
falco_worker_chart_name = var.falco_worker_chart_name
falco_worker_namespace = var.falco_worker_namespace
falco_worker_replicas_count = var.falco_worker_replicas_count
falco_helm_namespace = var.falco_helm_namespace
falco_version = var.falco_version
falcosidekick_version = var.falcosidekick_version
kyverno_enabled = var.kyverno_enabled
kyverno_prefix = var.kyverno_prefix
kyverno_version = var.kyverno_version
kyverno_worker_chart_name = var.kyverno_worker_chart_name
kyverno_worker_namespace = var.kyverno_worker_namespace
kyverno_worker_replicas_count = var.kyverno_worker_replicas_count
kyverno_helm_namespace = var.kyverno_helm_namespace
kyverno_policies_version = var.kyverno_policies_version
policy_reporter_version = var.policy_reporter_version
fakeeventgenerator_enabled = var.fakeeventgenerator_enabled
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/provider.tf
================================================
terraform {
required_version = ">= 0.14"
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = ">= 0.72.0"
}
kustomization = {
source = "kbst/kustomization"
version = ">= 0.5.0"
}
}
}
provider "yandex" {
folder_id = var.folder_id
#token = "example"
service_account_key_file = "./key.json"
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/terraform.tfvars.example
================================================
folder_id = "example"
cloud_id = "example"
cluster_name = "example-cluster"
elastic_server = "https://example-es.rw.mdb.yandexcloud.net"
elastic_pw = "str0ng_password"
elastic_user = "example_user"
service_account_id = "k8s-audit-logs-example"
log_bucket_name = "k8s-audit-logs-example"
worker_docker_image = "cr.yandex/sol/k8s-events-siem-worker:2.0.0"
create_namespace = true
auditlog_enabled = true
auditlogs_prefix = "AUDIT/"
auditlog_worker_chart_name = "auditlog-worker-example"
auditlog_worker_namespace = "infra-auditlog-example"
auditlog_worker_replicas_count = 1
falco_enabled = true
falco_prefix = "FALCO/"
falco_worker_chart_name = "falco-worker-example"
falco_worker_namespace = "infra-auditlog-example"
falco_worker_replicas_count = 3
falco_helm_namespace = "falco-example"
falco_version = "1.17.0"
falcosidekick_version = "0.4.4"
kyverno_enabled = true
kyverno_prefix = "KYVERNO/"
kyverno_worker_chart_name = "kyverno-worker-example"
kyverno_worker_namespace = "infra-auditlog-example"
kyverno_worker_replicas_count = 1
kyverno_helm_namespace = "kyverno-example"
kyverno_version = "2.1.10"
kyverno_policies_version = "2.1.10"
policy_reporter_version = "2.2.3"
fakeeventgenerator_enabled = true
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/variables.tf
================================================
# Variables for Import
# Initial variables
variable "folder_id" {
description = "The Yandex.Cloud folder id."
type = string
}
variable "cloud_id" {
description = "The Yandex.Cloud cloud id."
type = string
}
variable "region_name" {
description = "The Yandex.Cloud Cloud Region name."
type = string
default = "ru-central1"
}
variable "cluster_name" {
description = "The Yandex.Cloud K8s cluster name."
type = string
}
variable "service_account_id" {
type = string
description = "functions.invoker, storage.editor, ymq.editor"
}
# S3 Bucket Variables
variable "log_bucket_name" {
type = string
}
variable "s3_expiration" {
type = map(string)
default = {
"enabled" = true
"days" = 10
}
description = "Enable or disable delete indicies backup from bucket after days"
}
# Yandex Message Queue Variables
variable "timer_for_mq" {
description = "Timer for add permission for create mq"
type = string
default = "10s"
}
# Elastic Server
variable "elastic_pw" {
type = string
}
variable "elastic_user" {
type = string
}
variable "elastic_server" {
type = string
}
# Common Variables for Chart
variable "create_namespace" {
description = "Create the namespace if it does not yet exists."
type = bool
}
variable "value" {
description = "Values for the chart."
default = ""
}
variable "set" {
type = map(any)
default = {}
description = "Additional values set"
}
variable "set_sensitive" {
type = map(any)
default = {}
description = "Additional sensitive values set"
}
# Worker Settings
variable "worker_docker_image" {
type = string
}
# AUDIT LOG
variable "auditlog_enabled" {
type = bool
}
variable "auditlogs_prefix" {
type = string
}
variable "auditlog_worker_chart_name" {
description = "The name of the auditlog worker helm release"
type = string
}
variable "auditlog_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "auditlog_worker_replicas_count" {
description = "Count of replicas for audit worker."
type = number
}
# FALCO
variable "falco_enabled" {
type = bool
}
variable "falco_prefix" {
type = string
}
variable "falco_worker_chart_name" {
description = "The name of the falco worker helm release"
type = string
}
variable "falco_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "falco_worker_replicas_count" {
description = "Count of replicas for falco worker."
type = number
}
variable "falco_helm_namespace" {
description = "The namespace in which the helm will be deployed."
type = string
}
# KYVERNO
variable "kyverno_enabled" {
type = bool
}
variable "kyverno_prefix" {
type = string
}
variable "kyverno_worker_chart_name" {
description = "The name of the kyverno worker helm release"
type = string
}
variable "kyverno_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "kyverno_worker_replicas_count" {
description = "Count of replicas for kyverno worker."
type = number
}
variable "kyverno_helm_namespace" {
description = "The namespace in which the helm will be deployed."
type = string
}
# Variables for Export
variable "fakeeventgenerator_enabled" {
type = bool
}
variable "podSecurityStandard" {
type = string
default = "restricted"
}
variable "validationFailureAction" {
type = string
default = "audit"
}
# FALCO Helm
variable "falco_version" {
type = string
}
variable "falcosidekick_version" {
type = string
}
# KYVERNO Helm
variable "kyverno_version" {
type = string
}
variable "kyverno_policies_version" {
type = string
}
variable "policy_reporter_version" {
type = string
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/images/Logo-scheme.drawio
================================================
- Docker images:
- `cr.yandex/sol/k8s-events-siem-worker:2.0.0`.
**Version-2.0**
- Changelog:
- Added support for automatic Kyverno installation with policies in the audit mode.
- Docker images:
- `cr.yandex/sol/k8s-events-siem-worker:1.1.0`.
# Table of contents
- [Description](#description)
- [Link to the solution "Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"](#link-to-solution-"Collecting-monitoring-and-analyzing-audit-logs-in-Yandex-Managed-Service-for-Elasticsearch-(ELK)")
- [Generic diagram](#generic-diagram)
- [Terraform description](#terraform-description)
- [Content update process](#content-update-process)
- [Optional manual actions](#optional-manual-actions)
## Description
Here are the out-of-the-box features of the solution:
☑️ Collect [K8s audit logs](https://kubernetes.io/docs/tasks/debug-application-cluster/audit/) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/).
- ☑️ Install [Falco](https://falco.org/) and collect its [Alerts](https://falco.org/docs/alerts/) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/).
- ☑️ Install [Kyverno](https://kyverno.io/) with the [Pod Security Standards (Restricted)](https://kyverno.io/policies/?policytypes=Pod%2520Security%2520Standards%2520%28Restricted%29) policies in the audit mode and collect its [Alerts (Policy Reports)](https://kyverno.io/docs/policy-reports/) using [Policy Reporter](https://github.com/kyverno/policy-reporter).
- ☑️ Import Security Content: dashboards, detection rules, and so on (see the Security Content section) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/) to enable analysis and response to information security events.
- ☑️ This also includes importing Security Content for [OPA Gatekeeper](https://open-policy-agent.github.io/gatekeeper/website/docs/) (in the enforce mode). You can install OPA Gatekeeper manually if needed.
- ☑️ Create indexes in two replicas, set up the basic rollover policy (creating of new indexes every thirty days or when 50 GB are reached) to enable provisioning of high data availability and to set up data snapshots in S3, see [recommendations](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md).
## Link to the solution "Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"
The solution ["Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main) contains information on how to install Yandex Managed Service for Elasticsearch (ELK) and collect logs from Audit Trails in it.
## Generic diagram

## Description of imported ELK (Security Content) object
See a detailed description of the objects [here](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf).
## Terraform description
The solution consist of terraform module:
- It accepts the following input:
- `folder_id`: The ID of the folder where the cluster is hosted.
- `cloud_id`: The ID of the cloud where the cluster is hosted.
- `cluster_name`: The name of the Kubernetes cluster.
- `elastic_server`: The FQDN address of the ELK installation
- `elastic_pw` and `elastic_user`: The ELK user credentials for event import
- `service_account_id`: The ID of the service account that can write to the bucket and has the *ymq.admin* role.
- `log_bucket_name`: The name of the bucket that will create module to save logs to.
- `auditlog_enabled`: *true* or *false* (enables/disables sending of K8s audit logs to ELK).
- `falco_enabled`: *true* or *false* (enables/disables sending of Falco alerts to ELK).
- `kyverno_enabled`: *true* or *false* — (enables/disables sending of Kyverno alerts to ELK).
- Functionality:
- Create a static key for the service account.
- Create a function and a trigger for writing cluster logs to S3.
- Install Falco and pre-configured falcosidekick that will send logs to S3.
- Install Kyverno and pre-configured [Policy Reporter](https://github.com/kyverno/policy-reporter) that will send logs to S3.
- Create YMQ queues with log file names in S3.
- Create functions to push file names from S3 to YMQ.
- Create triggers for interaction between queues and functions.
- Create deployments in k8s with worker containers that import events from S3 to ELK.
#### Prerequisites:
- :white_check_mark: Cluster Managed K8s.
- :white_check_mark: Managed ELK.
- :white_check_mark: A service account that can write to the bucket and has the *ymq.admin* role.
#### Example of calling modules:
See the example of calling modules in [/examples/README.md](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_k8s/examples/README.md)
## Content update process
We recommend subscribing to this repository to receive update notifications.
For content updates, make sure that you are running the latest available image version:
`cr.yandex/sol/k8s-events-siem-worker:latest`
You can update the container as follows:
You can re-create the deployments in k8s via Terraform (change worker_docker_image env in tfvars and run `terraform apply`).
## Optional manual actions
#### Installing OPA Gatekeeper (Helm)
If you prefer OPA Gatekeeper to Kyverno, set the value `kyverno_enabled` to *false* when calling the module, then run the manual installation:
- Install OPA Gatekeeper [using Helm](https://open-policy-agent.github.io/gatekeeper/website/docs/install/#deploying-via-helm).
- Select and install the required constraint template and constraint from [gatekeeper-library](https://github.com/open-policy-agent/gatekeeper-library/tree/master/library/pod-security-policy).
- [Installation example](https://github.com/open-policy-agent/gatekeeper-library#usage).
## Recommendations for setting up retention, rollover, and snapshots:
[Recommendations for setting up retention, rollover, and snapshots](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/README.md
================================================
## Terraform test script
Prerequisites:
- ✅ Cluster of Managed K8s.
- ✅ Managed ELK.
- ✅ A service account that can write to the bucket and has the *ymq.admin* role.
##
1) If you doing this from Russia just create the file and fill it out like this to use yandex network mirror:
```
cat ~/.terraformrc
provider_installation {
network_mirror {
url = "https://terraform-network-mirror.storage.yandexcloud.net/"
}
}
```
2) Fill out the fields in the provider.tf file.
3) Fill out the fields in the terraform.tfvars.example file. (example below)
4) Delete <.example> from the end of the file - terraform.tfvars
5) Run:
```
terraform init
terraform apply
```
Example of terraform.tfvars.example file:
```
folder_id = "example"
cloud_id = "example"
cluster_name = "example-cluster"
elastic_server = "https://example-es.rw.mdb.yandexcloud.net"
elastic_pw = "str0ng_password"
elastic_user = "example_user"
service_account_id = "k8s-audit-logs-example"
log_bucket_name = "k8s-audit-logs-example" #name of cluster that will be create
worker_docker_image = "cr.yandex/sol/k8s-events-siem-worker:2.0.0"
create_namespace = true
auditlog_enabled = true
auditlogs_prefix = "AUDIT/"
auditlog_worker_chart_name = "auditlog-worker-example"
auditlog_worker_namespace = "infra-auditlog-example"
auditlog_worker_replicas_count = 1
falco_enabled = true
falco_prefix = "FALCO/"
falco_worker_chart_name = "falco-worker-example"
falco_worker_namespace = "infra-auditlog-example"
falco_worker_replicas_count = 3
falco_helm_namespace = "falco-example"
falco_version = "1.17.0"
falcosidekick_version = "0.4.4"
kyverno_enabled = true
kyverno_prefix = "KYVERNO/"
kyverno_worker_chart_name = "kyverno-worker-example"
kyverno_worker_namespace = "infra-auditlog-example"
kyverno_worker_replicas_count = 1
kyverno_helm_namespace = "kyverno-example"
kyverno_version = "2.1.10"
kyverno_policies_version = "2.1.10"
policy_reporter_version = "2.2.3"
fakeeventgenerator_enabled = false
```
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/main.tf
================================================
module "security-events-to-siem-importer" {
source = "../modules"
folder_id = var.folder_id
cloud_id = var.cloud_id
cluster_name = var.cluster_name
elastic_server = var.elastic_server
elastic_pw = var.elastic_pw
elastic_user = var.elastic_user
service_account_id = var.service_account_id
log_bucket_name = var.log_bucket_name
create_namespace = var.create_namespace
worker_docker_image = var.worker_docker_image
auditlog_enabled = var.auditlog_enabled
auditlogs_prefix = var.auditlogs_prefix
auditlog_worker_chart_name = var.auditlog_worker_chart_name
auditlog_worker_namespace = var.auditlog_worker_namespace
auditlog_worker_replicas_count = var.auditlog_worker_replicas_count
falco_enabled = var.falco_enabled
falco_prefix = var.falco_prefix
falco_worker_chart_name = var.falco_worker_chart_name
falco_worker_namespace = var.falco_worker_namespace
falco_worker_replicas_count = var.falco_worker_replicas_count
falco_helm_namespace = var.falco_helm_namespace
falco_version = var.falco_version
falcosidekick_version = var.falcosidekick_version
kyverno_enabled = var.kyverno_enabled
kyverno_prefix = var.kyverno_prefix
kyverno_version = var.kyverno_version
kyverno_worker_chart_name = var.kyverno_worker_chart_name
kyverno_worker_namespace = var.kyverno_worker_namespace
kyverno_worker_replicas_count = var.kyverno_worker_replicas_count
kyverno_helm_namespace = var.kyverno_helm_namespace
kyverno_policies_version = var.kyverno_policies_version
policy_reporter_version = var.policy_reporter_version
fakeeventgenerator_enabled = var.fakeeventgenerator_enabled
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/provider.tf
================================================
terraform {
required_version = ">= 0.14"
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = ">= 0.72.0"
}
kustomization = {
source = "kbst/kustomization"
version = ">= 0.5.0"
}
}
}
provider "yandex" {
folder_id = var.folder_id
#token = "example"
service_account_key_file = "./key.json"
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/terraform.tfvars.example
================================================
folder_id = "example"
cloud_id = "example"
cluster_name = "example-cluster"
elastic_server = "https://example-es.rw.mdb.yandexcloud.net"
elastic_pw = "str0ng_password"
elastic_user = "example_user"
service_account_id = "k8s-audit-logs-example"
log_bucket_name = "k8s-audit-logs-example"
worker_docker_image = "cr.yandex/sol/k8s-events-siem-worker:2.0.0"
create_namespace = true
auditlog_enabled = true
auditlogs_prefix = "AUDIT/"
auditlog_worker_chart_name = "auditlog-worker-example"
auditlog_worker_namespace = "infra-auditlog-example"
auditlog_worker_replicas_count = 1
falco_enabled = true
falco_prefix = "FALCO/"
falco_worker_chart_name = "falco-worker-example"
falco_worker_namespace = "infra-auditlog-example"
falco_worker_replicas_count = 3
falco_helm_namespace = "falco-example"
falco_version = "1.17.0"
falcosidekick_version = "0.4.4"
kyverno_enabled = true
kyverno_prefix = "KYVERNO/"
kyverno_worker_chart_name = "kyverno-worker-example"
kyverno_worker_namespace = "infra-auditlog-example"
kyverno_worker_replicas_count = 1
kyverno_helm_namespace = "kyverno-example"
kyverno_version = "2.1.10"
kyverno_policies_version = "2.1.10"
policy_reporter_version = "2.2.3"
fakeeventgenerator_enabled = true
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/examples/variables.tf
================================================
# Variables for Import
# Initial variables
variable "folder_id" {
description = "The Yandex.Cloud folder id."
type = string
}
variable "cloud_id" {
description = "The Yandex.Cloud cloud id."
type = string
}
variable "region_name" {
description = "The Yandex.Cloud Cloud Region name."
type = string
default = "ru-central1"
}
variable "cluster_name" {
description = "The Yandex.Cloud K8s cluster name."
type = string
}
variable "service_account_id" {
type = string
description = "functions.invoker, storage.editor, ymq.editor"
}
# S3 Bucket Variables
variable "log_bucket_name" {
type = string
}
variable "s3_expiration" {
type = map(string)
default = {
"enabled" = true
"days" = 10
}
description = "Enable or disable delete indicies backup from bucket after days"
}
# Yandex Message Queue Variables
variable "timer_for_mq" {
description = "Timer for add permission for create mq"
type = string
default = "10s"
}
# Elastic Server
variable "elastic_pw" {
type = string
}
variable "elastic_user" {
type = string
}
variable "elastic_server" {
type = string
}
# Common Variables for Chart
variable "create_namespace" {
description = "Create the namespace if it does not yet exists."
type = bool
}
variable "value" {
description = "Values for the chart."
default = ""
}
variable "set" {
type = map(any)
default = {}
description = "Additional values set"
}
variable "set_sensitive" {
type = map(any)
default = {}
description = "Additional sensitive values set"
}
# Worker Settings
variable "worker_docker_image" {
type = string
}
# AUDIT LOG
variable "auditlog_enabled" {
type = bool
}
variable "auditlogs_prefix" {
type = string
}
variable "auditlog_worker_chart_name" {
description = "The name of the auditlog worker helm release"
type = string
}
variable "auditlog_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "auditlog_worker_replicas_count" {
description = "Count of replicas for audit worker."
type = number
}
# FALCO
variable "falco_enabled" {
type = bool
}
variable "falco_prefix" {
type = string
}
variable "falco_worker_chart_name" {
description = "The name of the falco worker helm release"
type = string
}
variable "falco_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "falco_worker_replicas_count" {
description = "Count of replicas for falco worker."
type = number
}
variable "falco_helm_namespace" {
description = "The namespace in which the helm will be deployed."
type = string
}
# KYVERNO
variable "kyverno_enabled" {
type = bool
}
variable "kyverno_prefix" {
type = string
}
variable "kyverno_worker_chart_name" {
description = "The name of the kyverno worker helm release"
type = string
}
variable "kyverno_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "kyverno_worker_replicas_count" {
description = "Count of replicas for kyverno worker."
type = number
}
variable "kyverno_helm_namespace" {
description = "The namespace in which the helm will be deployed."
type = string
}
# Variables for Export
variable "fakeeventgenerator_enabled" {
type = bool
}
variable "podSecurityStandard" {
type = string
default = "restricted"
}
variable "validationFailureAction" {
type = string
default = "audit"
}
# FALCO Helm
variable "falco_version" {
type = string
}
variable "falcosidekick_version" {
type = string
}
# KYVERNO Helm
variable "kyverno_version" {
type = string
}
variable "kyverno_policies_version" {
type = string
}
variable "policy_reporter_version" {
type = string
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/images/Logo-scheme.drawio
================================================
{
"days": 10,
"enabled": true
} | no |
| [service\_account\_id](#input\_service\_account\_id) | functions.invoker, storage.editor, ymq.editor | `string` | n/a | yes |
| [set](#input\_set) | Additional values set | `map(any)` | `{}` | no |
| [set\_sensitive](#input\_set\_sensitive) | Additional sensitive values set | `map(any)` | `{}` | no |
| [timer\_for\_mq](#input\_timer\_for\_mq) | Timer for add permission for create mq | `string` | `"10s"` | no |
| [validationFailureAction](#input\_validationFailureAction) | n/a | `string` | `"audit"` | no |
| [value](#input\_value) | Values for the chart. | `string` | `""` | no |
| [worker\_docker\_image](#input\_worker\_docker\_image) | Worker Settings | `string` | n/a | yes |
## Outputs
| Name | Description |
|------|-------------|
| [folder\_id](#output\_folder\_id) | n/a |
| [log\_bucket\_name](#output\_log\_bucket\_name) | n/a |
| [service\_account\_id](#output\_service\_account\_id) | n/a |
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/chart/.helmignore
================================================
# Patterns to ignore when building packages.
# This supports shell glob matching, relative path matching, and
# negation (prefixed with !). Only one pattern per line.
.DS_Store
# Common VCS dirs
.git/
.gitignore
.bzr/
.bzrignore
.hg/
.hgignore
.svn/
# Common backup files
*.swp
*.bak
*.tmp
*.orig
*~
# Various IDEs
.project
.idea/
*.tmproj
.vscode/
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/chart/Chart.yaml
================================================
apiVersion: v2
appVersion: 0.2.0
description: A Helm chart for Kubernetes
name: worker
type: application
version: 0.2.2
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/chart/templates/_helpers.tpl
================================================
{{/* Sanitizes given string. */}}
{{- define "sanitize" -}}
{{- $name := regexReplaceAll "[[:^alnum:]]" . "-" -}}
{{- regexReplaceAll "-+" $name "-" | lower | trunc 63 | trimAll "-" -}}
{{- end -}}
{{/* Quotes values of the given object. */}}
{{- define "quote.object" -}}
{{- range $key, $value := . }}
{{ $key }}: {{ $value | quote }}
{{- end -}}
{{- end -}}
{{/* Quotes items of the given list. */}}
{{- define "quote.list" -}}
{{- range $item := . }}
- {{ $item | quote }}
{{- end -}}
{{- end -}}
{{/* Expands the name of the chart. */}}
{{- define "chart.name" -}}
{{- include "sanitize" .Chart.Name -}}
{{- end -}}
{{/* Expands a fully qualified name of the chart. */}}
{{- define "chart.fullname" -}}
{{- $chart := include "chart.name" . -}}
{{- $release := include "sanitize" .Release.Name -}}
{{- if contains $chart $release -}}
{{- $release -}}
{{- else -}}
{{- include "sanitize" (cat $chart $release) -}}
{{- end -}}
{{- end -}}
{{/* Expands selector labels of the chart. */}}
{{- define "chart.selector" -}}
app.kubernetes.io/name: {{ include "chart.name" . | quote }}
app.kubernetes.io/instance: {{ include "chart.fullname" . | quote }}
{{- end -}}
{{/* Expands labels of the chart. */}}
{{- define "chart.labels" -}}
helm.sh/chart: {{ printf "%s-%s" (include "chart.name" .) .Chart.Version | quote }}
{{- if .Chart.AppVersion }}
app.kubernetes.io/version: {{ .Chart.AppVersion | quote }}
{{- end -}}
{{- if .Values.repo }}
{{- with .Values.repo }}
app.kubernetes.io/repo-name: {{ .name | default "unknown" | quote }}
app.kubernetes.io/repo-branch: {{ .branch | default "unknown" | quote }}
app.kubernetes.io/repo-maintainer: {{ .maintainer | default "unknown" | replace " " "_" | quote }}
app.kubernetes.io/repo-last-commit: {{ .lastCommitHash | default "unknown" | quote }}
{{- end -}}
{{- end -}}
{{- if .Values.alerts.slackChannel }}
app.kubernetes.io/slack-channel: {{ .Values.alerts.slackChannel }}
{{- end -}}
{{- end -}}
{{/* Expand annotation labels of the chart. */}}
{{- define "chart.annotations" -}}
{{- with .Values.annotations }}
annotations: {{ include "quote.object" . | indent 2 -}}
{{- end -}}
{{- end -}}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/chart/templates/_server.tpl
================================================
{{/* Expands the name of the server. */}}
{{- define "server.name" -}}
{{- if .Values.server.nameOverride }}
{{- include "sanitize" .Values.server.nameOverride }}
{{- else }}
{{- include "sanitize" (cat (include "chart.fullname" .) "server" ) -}}
{{- end }}
{{- end -}}
{{/* Expands selector labels of the server. */}}
{{- define "server.selector" -}}
{{ include "chart.selector" . }}
app.kubernetes.io/component: "server"
app: "{{ include "server.name" . }}"
{{- end -}}
{{/* Expand common labels of the server. */}}
{{- define "server.labels" -}}
{{ include "chart.labels" . }}
{{ include "server.selector" . }}
{{- end -}}
{{/* Expand annotation labels of the server. */}}
{{- define "server.annotations" -}}
{{- $annotations := merge .Values.server.annotations .Values.annotations -}}
{{- with $annotations }}
{{ include "quote.object" -}}
{{- end -}}
{{- end -}}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/chart/templates/server-cm.yaml
================================================
apiVersion: v1
kind: ConfigMap
metadata:
name: {{ include "server.name" . | quote }}
labels:
{{- include "server.labels" . | nindent 4 }}
annotations:
{{- include "server.annotations" . | nindent 4 }}
data:
{{- if .Values.server.envVars.logPrefix.audit }}
AUDIT_LOG_PREFIX : {{ .Values.server.envVars.logPrefix.audit | quote }}
{{- else if .Values.server.envVars.logPrefix.falco }}
FALCO_LOG_PREFIX : {{ .Values.server.envVars.logPrefix.falco | quote }}
{{- else if .Values.server.envVars.logPrefix.kyverno }}
KYVERNO_LOG_PREFIX : {{ .Values.server.envVars.logPrefix.kyverno | quote }}
{{- end }}
CLOUD_ID : {{ .Values.server.envVars.yandex.cloud.id | quote }}
CLUSTER_ID : {{ .Values.server.envVars.yandex.cluster.id | quote }}
ELASTIC_AUTH_USER : {{ .Values.server.envVars.elastic.authUser | quote }}
ELASTIC_SERVER : {{ .Values.server.envVars.elastic.server | quote }}
ELK_PASS_ENCR : {{ .Values.server.envVars.elastic.passEncr | quote }}
FOLDER_ID : {{ .Values.server.envVars.yandex.folder.id | quote }}
KIBANA_SERVER : {{ .Values.server.envVars.elastic.kibanaServer | quote }}
KMS_KEY_ID : {{ .Values.server.envVars.yandex.kms.key.id | quote }}
S3_BUCKET : {{ .Values.server.envVars.yandex.s3.bucket.name | quote }}
S3_KEY_ENCR : {{ .Values.server.envVars.yandex.s3.bucket.keyEncr | quote }}
S3_SECRET_ENCR : {{ .Values.server.envVars.yandex.s3.bucket.secretEncr | quote }}
SA_ID : {{ .Values.server.envVars.yandex.serviceAccount.id | quote }}
SA_KEY_ID : {{ .Values.server.envVars.yandex.serviceAccount.authKey.id | quote }}
SLEEP_TIME : {{ .Values.server.envVars.sleepTime | quote }}
YMQ_URL : {{ .Values.server.envVars.yandex.messageQueue.url | quote }}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/chart/templates/server-deploy.yaml
================================================
apiVersion: apps/v1
kind: Deployment
metadata:
name: {{ include "server.name" . | quote }}
labels:
{{- include "server.labels" . | nindent 4 }}
annotations:
{{- if .Values.server.tracing.jaeger.enabled }}
sidecar.jaegertracing.io/inject: "true"
{{- end }}
{{- include "server.annotations" . | nindent 4 }}
spec:
selector:
matchLabels:
{{- include "server.selector" . | nindent 6 }}
replicas: {{ .Values.server.replicas }}
template:
metadata:
labels:
{{- include "server.labels" . | nindent 8 }}
annotations:
{{- include "server.annotations" . | nindent 8 }}
spec:
{{- if .Values.pullSecret }}
imagePullSecrets:
- name: {{ .Values.pullSecret }}
{{- end }}
containers:
- name: server
image: {{ .Values.server.image | quote }}
imagePullPolicy: {{ .Values.pullPolicy | quote }}
resources: {{- toYaml .Values.server.resources | nindent 12 }}
env:
- name: PYTHONUNBUFFERED
value: "1"
envFrom:
- configMapRef:
name: {{ include "server.name" . | quote }}
- secretRef:
name: {{ include "server.name" . | quote }}
{{- if .Values.server.probes.readiness }}
readinessProbe: {{- toYaml .Values.server.probes.readiness | nindent 12 }}
{{- end }}
{{- if .Values.server.probes.liveness }}
livenessProbe: {{- toYaml .Values.server.probes.liveness | nindent 12 }}
{{- end }}
{{- if .Values.server.tracing.jaeger.enabled }}
- name: jaeger-agent
image: {{ .Values.jaeger.agent.image }}
imagePullPolicy: {{ .Values.pullPolicy }}
resources: {{- toYaml .Values.server.tracing.jaeger.resources | nindent 14 }}
ports:
- containerPort: 5775
name: zk-compact-trft
protocol: UDP
- containerPort: 5778
name: config-rest
protocol: TCP
- containerPort: 6831
name: jg-compact-trft
protocol: UDP
- containerPort: 6832
name: jg-binary-trft
protocol: UDP
- containerPort: 14271
name: admin-http
protocol: TCP
args:
- --reporter.grpc.host-port={{ .Values.jaeger.collector.endpoint }}
- --reporter.type=grpc
{{- end }}
{{- if .Values.server.nodeSelector }}
nodeSelector: {{ toYaml .Values.server.nodeSelector | nindent 8 }}
{{- end }}
{{- if .Values.server.affinity }}
affinity: {{ toYaml .Values.server.affinity | nindent 8 }}
{{- else }}
affinity:
podAntiAffinity:
preferredDuringSchedulingIgnoredDuringExecution:
- weight: 100
podAffinityTerm:
labelSelector:
matchExpressions:
- key: app
operator: In
values:
- {{ include "server.name" . | quote }}
topologyKey: kubernetes.io/hostname
{{- end }}
{{- if .Values.server.tolerations }}
tolerations: {{ toYaml .Values.server.tolerations | nindent 8 }}
{{- end }}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/chart/templates/server-secret.yaml
================================================
apiVersion: v1
kind: Secret
metadata:
name: {{ include "server.name" . | quote }}
labels:
{{- include "server.labels" . | nindent 4 }}
annotations:
{{- include "server.annotations" . | nindent 4 }}
type: Opaque
stringData:
KEY_PRIV_PEM : {{ .Values.server.envVars.yandex.serviceAccount.authKey.privPem | quote }}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/chart/values.yaml
================================================
# Image pull policy. Possible values: Always, Never, IfNotPresent.
pullPolicy: IfNotPresent
# Image pull secret name.
pullSecret: ""
# Alerts configuration.
alerts:
# Slack channel for alerts.
slackChannel: ""
# Jaeger configuration.
jaeger:
agent:
image: jaegertracing/jaeger-agent:latest
collector:
endpoint: dns:///jaeger-collector.ke.internal:14250
# Server configuration.
server:
# override full name of server
nameOverride: ""
# Docker image of the server application.
image: ""
# The minimum number of replicas.
replicas: ""
envVars:
logPrefix:
audit: ""
falco: ""
kyverno: ""
elastic:
authUser: ""
server: ""
passEncr: ""
kibanaServer: ""
sleepTime: ""
yandex:
cloud:
id: ""
cluster:
id: ""
kms:
key:
id: ""
folder:
id: ""
messageQueue:
url: ""
s3:
bucket:
name: ""
keyEncr: ""
secretEncr: ""
serviceAccount:
id: ""
authKey:
id: ""
privPem: ""
# The resources allocated for each replica, both requests and limits.
resources:
requests:
memory: 512Mi
cpu: 500m
limits:
memory: 1Gi
cpu: 1
# Probes configuration.
probes:
readiness: {}
# initialDelaySeconds: 10
# httpGet:
# port: 8081
# path: "/readiness"
liveness: {}
# initialDelaySeconds: 10
# httpGet:
# port: 8081
# path: "/healthz"
# Tracing configuration.
tracing:
# Jaeger configuration.
jaeger:
# Inject Jaeger Agent sidecar?
enabled: false
# The resources allocated for each replica, both requests and limits.
resources:
requests:
memory: 128Mi
cpu: 100m
limits:
memory: 128Mi
cpu: 100m
# NodeSelector configuration of the validators.
nodeSelector: { }
# Deployment affinity configuration. If not set the default one will be used.
affinity: { }
# Tolerations of the validators pods.
tolerations: [ ]
# Annotations used in the server resources.
annotations: { }
# Annotations used in all application resources.
annotations: { }
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/function/Makefile
================================================
all: clean dependencies package
clean:
rm -rf dist/
dirs:
mkdir -p dist/
dependencies: dirs
docker run --rm \
-v $(shell pwd)/dist:/dist -v $(shell pwd):/app \
-w /app \
python:3.7-stretch \
pip3 install -r /app/requirements.txt --target /dist/
install-code: dirs
cp main.py dist/main.py
cp s3.py dist/s3.py
package: dirs install-code
rm -f dist.zip
cd dist && zip --exclude '*.pyc' -r ../dist.zip ./*
.PHONY: clean dirs dependencies install-code package all
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/function/main.py
================================================
import json
import os
import sys
import uuid
import boto3
import string
import random
from datetime import datetime
def get_random_alphanumeric_string(length):
letters_and_digits = string.ascii_letters + string.digits
result_str = ''.join((random.choice(letters_and_digits) for i in range(length)))
return result_str
client = boto3.client(
service_name='s3',
endpoint_url='https://storage.yandexcloud.net',
region_name='ru-central1'
)
def handler(event, context):
for log_data in event['messages']:
full_log = []
for log_entry in log_data['details']['messages']:
kubernetes_log = json.loads(log_entry['message'])
full_log.append(json.dumps(kubernetes_log))
bucket_name = os.environ.get('BUCKET_NAME')
# object_key = os.environ.get('LOG_PREFIX')+'/'+datetime.now().strftime('%Y-%m-%d-%H:%M:%S')+'-'+get_random_alphanumeric_string(5)
object_key = 'AUDIT/'+os.environ.get('CLUSTER_ID')+'/'+datetime.now().strftime('%Y-%m-%d-%H:%M:%S')+'-'+get_random_alphanumeric_string(5)
object_value = '\n'.join(full_log)
client.put_object(Bucket=bucket_name, Key=object_key, Body=object_value, StorageClass='COLD')
print(object_value)
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/function/requirements.txt
================================================
botocore
boto3
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/function/test.py
================================================
def test(a):
pass
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/outputs.tf
================================================
output "service_account_id" {
value = data.yandex_iam_service_account.bucket_sa.id
sensitive = true
}
output "folder_id" {
value = data.yandex_resourcemanager_folder.my_folder.id
sensitive = true
}
output "log_bucket_name" {
value = var.log_bucket_name
sensitive = true
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/pusher/Makefile
================================================
all: clean dependencies package
clean:
rm -rf dist/
dirs:
mkdir -p dist/
dependencies: dirs
docker run --rm \
-v $(shell pwd)/dist:/dist -v $(shell pwd):/app \
-w /app \
python:3.7-stretch \
pip3 install -r /app/requirements.txt --target /dist/
install-code: dirs
cp main.py dist/main.py
cp s3.py dist/s3.py
package: dirs install-code
rm -f dist.zip
cd dist && zip --exclude '*.pyc' -r ../dist.zip ./*
.PHONY: clean dirs dependencies install-code package all
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/pusher/main.py
================================================
import boto3
import json
import os
client = boto3.client(
service_name='sqs',
endpoint_url='https://message-queue.api.cloud.yandex.net',
region_name='ru-central1'
)
s3_client = boto3.client(
service_name='s3',
endpoint_url='https://storage.yandexcloud.net',
region_name='ru-central1',
)
def handler(event, context):
queue_url = os.environ.get('YMQ_URL')
folder_id = os.environ.get('FOLDER_ID')
cluster_id = os.environ.get('CLUSTER_ID')
for message in event['messages']:
if os.environ.get('AUDIT_LOG_PREFIX') is not None and message['details']['object_id'].startswith(os.environ.get('AUDIT_LOG_PREFIX')):
log_type = 'AUDIT'
elif os.environ.get('FALCO_LOG_PREFIX') is not None and message['details']['object_id'].startswith(os.environ.get('FALCO_LOG_PREFIX')):
log_type = 'FALCO'
elif os.environ.get('KYVERNO_LOG_PREFIX') is not None and message['details']['object_id'].startswith(os.environ.get('KYVERNO_LOG_PREFIX')):
log_type = 'KYVERNO'
else:
log_type = 'UNKNOWN'
metadata_list = message['details']['object_id'].split("/")
data = {
'log_type': log_type,
'bucket_id': message['details']['bucket_id'],
'object_id': message['details']['object_id'],
'cloud_id': os.environ.get('CLOUD_ID'),
'folder_id': os.environ.get('FOLDER_ID'),
'cluster_id': os.environ.get('CLUSTER_ID'),
'cluster_url': "https://console.cloud.yandex.ru/folders/" + str(folder_id) + "/managed-kubernetes/cluster/" + str(cluster_id)
}
print(data)
log_obj = s3_client.get_object(Bucket=message['details']['bucket_id'], Key=message['details']['object_id'])
file_content = log_obj['Body'].read()
print(file_content)
client.send_message(
QueueUrl=queue_url,
MessageBody=json.dumps(data),
MessageGroupId = "%s\%s" % (message['details']['bucket_id'],log_type)
)
print('Successfully sent message to queue')
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/pusher/requirements.txt
================================================
botocore
boto3
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/pusher/test.py
================================================
def test(a):
pass
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/auditlog-worker-limits.yaml
================================================
resources:
requests:
memory: 512Mi
cpu: 500m
limits:
memory: 1Gi
cpu: 1
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/falco-base.yaml
================================================
image:
registry: docker.io
repository: falcosecurity/falco
pullPolicy: IfNotPresent
docker:
enabled: true
socket: /var/run/docker.sock
containerd:
enabled: true
socket: /run/containerd/containerd.sock
falco:
jsonOutput: true
jsonIncludeOutputProperty: true
httpOutput:
enabled: true
url: http://falcosidekick:2801/
resources:
requests:
cpu: 100m
memory: 256Mi
limits:
memory: 1Gi
customRules:
rules-cilium.yaml: |-
# disabling cilium false positives
- rule: Packet socket created in container
desc: Detect new packet socket at the device driver (OSI Layer 2) level in a container. Packet socket could be used for ARP Spoofing and privilege escalation(CVE-2020-14386) by attacker.
condition: evt.type=socket and evt.arg[0]=AF_PACKET and consider_packet_socket_communication and container and not proc.name in (user_known_packet_socket_binaries) and not container.image.repository=cr.yandex/crpsjg1coh47p81vh2lc/k8s-addons/cilium/cilium
output: Packet socket was created in a container (user=%user.name user_loginuid=%user.loginuid command=%proc.cmdline socket_info=%evt.args container_id=%container.id container_name=%container.name image=%container.image.repository:%container.image.tag)
priority: NOTICE
tags: [network, mitre_discovery]
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/falco-worker-limits.yaml
================================================
resources:
requests:
memory: 512Mi
cpu: 500m
limits:
memory: 1Gi
cpu: 1
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/falcosidekick-base.yaml
================================================
# enable falcosidekick deployment
image:
tag: 2.24.0
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/kubeconfig-template.yaml.tpl
================================================
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: ${cluster_ca_certificate}
server: ${endpoint}
name: ${context}
contexts:
- context:
cluster: ${context}
user: ${context}
name: ${context}
current-context: ${context}
kind: Config
preferences: {}
users:
- name: ${context}
user:
token: ${token}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/kyverno-base.yaml
================================================
resources:
requests:
cpu: 100m
memory: 256Mi
limits:
memory: 1Gi
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/kyverno-worker-limits.yaml
================================================
resources:
requests:
memory: 512Mi
cpu: 500m
limits:
memory: 1Gi
cpu: 1
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/policy-reporter-base.yaml
================================================
resources:
requests:
cpu: 100m
memory: 256Mi
limits:
memory: 1Gi
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/templates/yc-mk8s.ca
================================================
LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUM1ekNDQWMrZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBREFWTVJNd0VRWURWUVFERXdwcmRXSmwKY201bGRHVnpNQjRYRFRJeE1EWXhNREE0TlRBMU0xb1hEVE14TURZd09EQTROVEExTTFvd0ZURVRNQkVHQTFVRQpBeE1LYTNWaVpYSnVaWFJsY3pDQ0FTSXdEUVlKS29aSWh2Y05BUUVCQlFBRGdnRVBBRENDQVFvQ2dnRUJBTXNDCnhocFpIQTB0b096RVRFV05CbGJremljTUg0NTdhK0ltajExc1ZweHlRYnM1U1B6cXdkRUVTMVN3MHpxZnAvbTQKYi9LSDVmNVY4MEFBekdnY2RqUXBYREQ2VFYzeThDSmdzbTE0TjllZzQxWHF2MUZFOTV5U0tpeFhHQjlkbk01Kwp5N0V1SXY1Z1FoZTBCMWUvRmRtM0h1QWNUblJkbzdLdEV6bGI4c3luSVVVNnRZaUVYNVd2cFBsaDRlcHo1eHo4ClBFd2xyZWJsaDRNaE85OWE3bmswYXd5RGV5OFdmNkM0eXdadHUrUG5XNGw1UzVjTnF6Wi9pcWJnN0pmeFZVU3EKYTBzWHJoNzRPMDI3SStlQ3dOVGxCYU5lVUNJY3owYm9nQ3o3dkh6ZnNkODhIdXJ2RnphSTRURGtyMHd4dkNkdApRQVFUUDdPVmp1d2hISXpteE9FQ0F3RUFBYU5DTUVBd0RnWURWUjBQQVFIL0JBUURBZ0trTUE4R0ExVWRFd0VCCi93UUZNQU1CQWY4d0hRWURWUjBPQkJZRUZOUTlmQWNBemowd2FHS3NXdFU5bWpkeDdXQXFNQTBHQ1NxR1NJYjMKRFFFQkN3VUFBNElCQVFBR3V5cFFaMDM0RzQ4RHhtVzl1MFFFZ0pNNUlRVHYzUnZDNEFnenkxVnlkd0tVNG8zOApheHQrY2RGYWgrTFFoRVd3amErYzhCY1VzU0lGQVRaU2V2a3p6MkVOVVpwNlVHVmY4QjFKNjZEQU5nYXY4cks4ClN3VktSMHFuV2czSHVqZGlpcWZvK3dyQnRRUUk3VUxuU0p6R3RYTjNZMlZPT2tyR1YxVUZOV3NhUzE0aklLRG4KMlMwYmovbVBxN2FnK3M0T0FMb1ltcGRybjNSZGN5RGdJUTE3MkNQM0doZ1hkd2VUYkV4UmtsYzVvUUhOYkV5NAo2b1l3em1FK0tqdG5Kd3FKYTRmRVM3WkExd2dzRW9HQXkzaUx3TlNBdDFEN2RZWGI0RU1reDZ6UTA0d2RIWDNGCnNGWHRJdFY3NjdJSmVEV1BmQjNiMHNxYkpqSE9kZ1pmcnhmTwotLS0tLUVORCBDRVJUSUZJQ0FURS0tLS0tCg==
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/variables.tf
================================================
# Variables for Import
# Initial variables
variable "folder_id" {
description = "The Yandex.Cloud folder id."
type = string
}
variable "cloud_id" {
description = "The Yandex.Cloud cloud id."
type = string
}
variable "region_name" {
description = "The Yandex.Cloud Cloud Region name."
type = string
default = "ru-central1"
}
variable "cluster_name" {
description = "The Yandex.Cloud K8s cluster name."
type = string
}
variable "service_account_id" {
type = string
description = "functions.invoker, storage.editor, ymq.editor"
}
# S3 Bucket Variables
variable "log_bucket_name" {
type = string
}
variable "s3_expiration" {
type = map(string)
default = {
"enabled" = true
"days" = 10
}
description = "Enable or disable delete indicies backup from bucket after days"
}
# Yandex Message Queue Variables
variable "timer_for_mq" {
description = "Timer for add permission for create mq"
type = string
default = "10s"
}
# Elastic Server
variable "elastic_pw" {
type = string
}
variable "elastic_user" {
type = string
}
variable "elastic_server" {
type = string
}
# Common Variables for Chart
variable "create_namespace" {
description = "Create the namespace if it does not yet exists."
type = bool
}
variable "value" {
description = "Values for the chart."
default = ""
}
variable "set" {
type = map(any)
default = {}
description = "Additional values set"
}
variable "set_sensitive" {
type = map(any)
default = {}
description = "Additional sensitive values set"
}
# Worker Settings
variable "worker_docker_image" {
type = string
}
# AUDIT LOG
variable "auditlog_enabled" {
type = bool
}
variable "auditlogs_prefix" {
type = string
}
variable "auditlog_worker_chart_name" {
description = "The name of the auditlog worker helm release"
type = string
}
variable "auditlog_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "auditlog_worker_replicas_count" {
description = "Count of replicas for audit worker."
type = number
}
# FALCO
variable "falco_enabled" {
type = bool
}
variable "falco_prefix" {
type = string
}
variable "falco_worker_chart_name" {
description = "The name of the falco worker helm release"
type = string
}
variable "falco_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "falco_worker_replicas_count" {
description = "Count of replicas for falco worker."
type = number
}
variable "falco_helm_namespace" {
description = "The namespace in which the helm will be deployed."
type = string
}
# KYVERNO
variable "kyverno_enabled" {
type = bool
}
variable "kyverno_prefix" {
type = string
}
variable "kyverno_worker_chart_name" {
description = "The name of the kyverno worker helm release"
type = string
}
variable "kyverno_worker_namespace" {
description = "The namespace in which the worker chart will be deployed."
type = string
}
variable "kyverno_worker_replicas_count" {
description = "Count of replicas for kyverno worker."
type = number
}
variable "kyverno_helm_namespace" {
description = "The namespace in which the helm will be deployed."
type = string
}
# Variables for Export
variable "fakeeventgenerator_enabled" {
type = bool
}
variable "podSecurityStandard" {
type = string
default = "restricted"
}
variable "validationFailureAction" {
type = string
default = "audit"
}
# FALCO Helm
variable "falco_version" {
type = string
}
variable "falcosidekick_version" {
type = string
}
# KYVERNO Helm
variable "kyverno_version" {
type = string
}
variable "kyverno_policies_version" {
type = string
}
variable "policy_reporter_version" {
type = string
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s/modules/versions.tf
================================================
terraform {
required_version = ">= 0.14"
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = ">= 0.72.0"
}
kustomization = {
source = "kbst/kustomization"
version = ">= 0.5.0"
}
}
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_k8s_old/README.md
================================================
## Yandex.Cloud: Analyzing K8s security logs in ELK: audit logs, Policy Engine, Falco


 
# Version
**Version-2.0**
- Changelog:
- Added support for automatic Kyverno installation with policies in the audit mode.
- Docker images:
- `cr.yandex/crpjfmfou6gflobbfvfv/k8s-events-siem-worker:1.1.0`.
# Table of contents
- [Description](#description)
- [Link to the solution "Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"](#link-to-solution-"Collecting-monitoring-and-analyzing-audit-logs-in-Yandex-Managed-Service-for-Elasticsearch-(ELK)")
- [Generic diagram](#generic-diagram)
- [Description of imported ELK (Security Content) objects](#description of-imported-ELK-(Security-Content)-objects)
- [Terraform description](#terraform-description)
- [Content update process](#content-update-process)
- [Optional manual actions](#optional-manual-actions)
## Description
Here are the out-of-the-box features of the solution:
☑️ Collect [K8s audit logs](https://kubernetes.io/docs/tasks/debug-application-cluster/audit/) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/).
- ☑️ Install [Falco](https://falco.org/) and collect its [Alerts](https://falco.org/docs/alerts/) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/).
- ☑️ Install [Kyverno](https://kyverno.io/) with the [Pod Security Standards (Restricted)](https://kyverno.io/policies/?policytypes=Pod%2520Security%2520Standards%2520%28Restricted%29) policies in the audit mode and collect its [Alerts (Policy Reports)](https://kyverno.io/docs/policy-reports/) using [Policy Reporter](https://github.com/kyverno/policy-reporter).
- ☑️ Import Security Content: dashboards, detection rules, and so on (see the Security Content section) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/) to enable analysis and response to information security events.
- ☑️ This also includes importing Security Content for [OPA Gatekeeper](https://open-policy-agent.github.io/gatekeeper/website/docs/) (in the enforce mode). You can install OPA Gatekeeper manually if needed.
- ☑️ Create indexes in two replicas, set up the basic rollover policy (creating of new indexes every thirty days or when 50 GB are reached) to enable provisioning of high data availability and to set up data snapshots in S3, see [recommendations](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md).
## Link to the solution "Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"
The solution ["Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main) contains information on how to install Yandex Managed Service for Elasticsearch (ELK) and collect logs from Audit Trails in it.
## Generic diagram

## Description of imported ELK (Security Content) object
See a detailed description of the objects [here](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf).
## Terraform description
The solution consists of two Terraform modules:
1) [security-events-to-storage-exporter](./security-events-to-storage-exporter) exports logs to S3.
- It accepts the following input:
- `folder_id`: The ID of the folder where the cluster is hosted.
- `cluster_name`: The name of the Kubernetes cluster.
- `log_bucket_service_account_id`: The ID of the service account that can write to the bucket and has the *ymq.admin* role.
- `log_bucket_name`: The name of the bucket to save logs to.
- `function_service_account_id`: The ID of the service account that will run the function (optional). If omitted, `log_bucket_service_account_id` is used.
- Functionality:
- Create a static key for the service account.
- Create a function and a trigger for writing cluster logs to S3.
- Install Falco and pre-configured falcosidekick that will send logs to S3.
- Install Kyverno and pre-configured [Policy Reporter](https://github.com/kyverno/policy-reporter) that will send logs to S3.
2) [security-events-to-siem-importer](./security-events-to-siem-importer) imports logs into ELK.
- It accepts the following input:
- Several parameters from the module (`security-events-to-storage-exporter`) module.
- `auditlog_enabled`: *true* or *false* (enables/disables sending of K8s audit logs to ELK).
- 'falco_enabled`: *true* or *false* (enables/disables sending of Falco alerts to ELK).
- 'kyverno_enabled`: *true* or *false* — (enables/disables sending of Kyverno alerts to ELK).
- The FQDN address of the ELK installation.
- The ID of the subnet where the VM instance with the importer container is being created.
- The ELK user credentials for event import.
- Functionality:
- Create YMQ queues with log file names in S3.
- Create functions to push file names from S3 to YMQ.
- Create triggers for interaction between queues and functions.
- Generate and write SSH keys to a file and to a VM.
- Create VM instances based on COI ([Container Optimized Image](https://cloud.yandex.ru/docs/cos/concepts/)) with worker containers that import events from S3 to ELK.
#### Prerequisites:
- :white_check_mark: Cluster Managed K8s.
- :white_check_mark: Managed ELK.
- :white_check_mark: A service account that can write to the bucket and has the *ymq.admin* role.
- :white_check_mark: Object Storage Bucket.
- :white_check_mark: A subnet for deploying a VM with NAT enabled.
#### Example of calling modules:
See the example of calling modules in /example/main.tf
```Python
//Calling the security-events-to-storage-exporter module
module "security-events-to-storage-exporter" {
source = "../security-events-to-storage-exporter/" # path to the module
folder_id = "xxxxxx" // The folder ID of the K8s cluster yc managed-kubernetes cluster get --id

# Version
**Version-2.0**
- Changelog:
- Added support for automatic Kyverno installation with policies in the audit mode.
- Docker images:
- `cr.yandex/crpjfmfou6gflobbfvfv/k8s-events-siem-worker:1.1.0`.
# Table of contents
- [Description](#description)
- [Link to the solution "Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"](#link-to-solution-"Collecting-monitoring-and-analyzing-audit-logs-in-Yandex-Managed-Service-for-Elasticsearch-(ELK)")
- [Generic diagram](#generic-diagram)
- [Description of imported ELK (Security Content) objects](#description of-imported-ELK-(Security-Content)-objects)
- [Terraform description](#terraform-description)
- [Content update process](#content-update-process)
- [Optional manual actions](#optional-manual-actions)
## Description
Here are the out-of-the-box features of the solution:
☑️ Collect [K8s audit logs](https://kubernetes.io/docs/tasks/debug-application-cluster/audit/) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/).
- ☑️ Install [Falco](https://falco.org/) and collect its [Alerts](https://falco.org/docs/alerts/) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/).
- ☑️ Install [Kyverno](https://kyverno.io/) with the [Pod Security Standards (Restricted)](https://kyverno.io/policies/?policytypes=Pod%2520Security%2520Standards%2520%28Restricted%29) policies in the audit mode and collect its [Alerts (Policy Reports)](https://kyverno.io/docs/policy-reports/) using [Policy Reporter](https://github.com/kyverno/policy-reporter).
- ☑️ Import Security Content: dashboards, detection rules, and so on (see the Security Content section) in [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/) to enable analysis and response to information security events.
- ☑️ This also includes importing Security Content for [OPA Gatekeeper](https://open-policy-agent.github.io/gatekeeper/website/docs/) (in the enforce mode). You can install OPA Gatekeeper manually if needed.
- ☑️ Create indexes in two replicas, set up the basic rollover policy (creating of new indexes every thirty days or when 50 GB are reached) to enable provisioning of high data availability and to set up data snapshots in S3, see [recommendations](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md).
## Link to the solution "Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"
The solution ["Collecting, monitoring, and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)"](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main) contains information on how to install Yandex Managed Service for Elasticsearch (ELK) and collect logs from Audit Trails in it.
## Generic diagram

## Description of imported ELK (Security Content) object
See a detailed description of the objects [here](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf).
## Terraform description
The solution consists of two Terraform modules:
1) [security-events-to-storage-exporter](./security-events-to-storage-exporter) exports logs to S3.
- It accepts the following input:
- `folder_id`: The ID of the folder where the cluster is hosted.
- `cluster_name`: The name of the Kubernetes cluster.
- `log_bucket_service_account_id`: The ID of the service account that can write to the bucket and has the *ymq.admin* role.
- `log_bucket_name`: The name of the bucket to save logs to.
- `function_service_account_id`: The ID of the service account that will run the function (optional). If omitted, `log_bucket_service_account_id` is used.
- Functionality:
- Create a static key for the service account.
- Create a function and a trigger for writing cluster logs to S3.
- Install Falco and pre-configured falcosidekick that will send logs to S3.
- Install Kyverno and pre-configured [Policy Reporter](https://github.com/kyverno/policy-reporter) that will send logs to S3.
2) [security-events-to-siem-importer](./security-events-to-siem-importer) imports logs into ELK.
- It accepts the following input:
- Several parameters from the module (`security-events-to-storage-exporter`) module.
- `auditlog_enabled`: *true* or *false* (enables/disables sending of K8s audit logs to ELK).
- 'falco_enabled`: *true* or *false* (enables/disables sending of Falco alerts to ELK).
- 'kyverno_enabled`: *true* or *false* — (enables/disables sending of Kyverno alerts to ELK).
- The FQDN address of the ELK installation.
- The ID of the subnet where the VM instance with the importer container is being created.
- The ELK user credentials for event import.
- Functionality:
- Create YMQ queues with log file names in S3.
- Create functions to push file names from S3 to YMQ.
- Create triggers for interaction between queues and functions.
- Generate and write SSH keys to a file and to a VM.
- Create VM instances based on COI ([Container Optimized Image](https://cloud.yandex.ru/docs/cos/concepts/)) with worker containers that import events from S3 to ELK.
#### Prerequisites:
- :white_check_mark: Cluster Managed K8s.
- :white_check_mark: Managed ELK.
- :white_check_mark: A service account that can write to the bucket and has the *ymq.admin* role.
- :white_check_mark: Object Storage Bucket.
- :white_check_mark: A subnet for deploying a VM with NAT enabled.
#### Example of calling modules:
See the example of calling modules in /example/main.tf
```Python
//Calling the security-events-to-storage-exporter module
module "security-events-to-storage-exporter" {
source = "../security-events-to-storage-exporter/" # path to the module
folder_id = "xxxxxx" // The folder ID of the K8s cluster yc managed-kubernetes cluster get --id  
# Version
**Version-2.0**
- Changelog:
- добавлена поддержка авто-установки kyverno с политиками в режиме audit
- Docker images:
- `cr.yandex/sol/k8s-events-siem-worker:1.1.0`
# Оглавление
- [Описание](#описание)
- [Связь с решением "Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"](#связь-с-решением-"Сбор-мониторинг-и-анализ-аудит-логов-в-Yandex-Managed-Service-for-Elasticsearch-(ELK)")
- [Общая схема](#общая-схема)
- [Описание импортируемых объектов ELK (Security Content)](#описание-импортируемых-объектов-ELK-(Security-Content))
- [Описание terraform](#описание-terraform)
- [Процесс обновления контента](#процесс-обновления-контента)
- [Опционально ручные действие](#опционально-ручные-действие)
## Описание
Решение из "коробки" выполняет следующее:
- ☑️ собирает [k8s AUDIT-LOGS](https://kubernetes.io/docs/tasks/debug-application-cluster/audit/) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/)
- ☑️ устанавливает [FALCO](https://falco.org/) и собирает его [ALERTS](https://falco.org/docs/alerts/) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/)
- ☑️ устанавливает [Kyverno](https://kyverno.io/) c политиками категории [Pod Security Standards (Restricted)](https://kyverno.io/policies/?policytypes=Pod%2520Security%2520Standards%2520%28Restricted%29) в режиме audit и собирает его [ALERTS (PolicyReports)](https://kyverno.io/docs/policy-reports/) (при помощи [Policy Reporter](https://github.com/kyverno/policy-reporter))
- ☑️ импортирует Security Content (dashboards, detection rules и др.)(см. в секции Security Content) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/) для анализа и реагирования на события ИБ.
- ✔️ *В том числе импортирует Security Content для [OPA Gatekeeper](https://open-policy-agent.github.io/gatekeeper/website/docs/) (в режиме enforce). (сам OPA Gatekeeper может быть установлен вручную дополнительно)
- ☑️ Создает индексы в двух репликах, настраивает базовую политику rollover (создания новых индексов каждые тридцать дней или по достижению 50ГБ), для дальнейшей настройки в части высокой доступности данных и для настройки снимков данных в S3 - см. [рекомендации](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md).
## Связь с решением "Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"
Решение ["Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main) содержит информацию о том, как установить Yandex Managed Service for Elasticsearch (ELK) и собирать в него логи Audit Trails
## Общая схема

## Описание импортируемых объектов ELK (Security Content)
Подробное описание объектов по [ссылке](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf)
## Описание terraform
Решение состоит из 2-х модулей Terraform:
1) [security-events-to-storage-exporter](./security-events-to-storage-exporter) (экспортирует логи в s3)
- Принимает на вход:
- `folder_id` - id каталога, в котором расположен кластер
- `cluster_name` - имя кластера Kubernetes
- `log_bucket_service_account_id` - id сервисного аккаунта, который может писать в бакет и имеет роль *ymq.admin*
- `log_bucket_name` - имя бакета, куда нужно сохранять логи
- `function_service_account_id` - (опционально) id сервисного аккаунта, который будет запускать фукнцию, если не указан, то используется `log_bucket_service_account_id`
- Выполняет:
- создание статического ключа для сервисного аккаунта
- создание функции и тригера для записи логов кластера в s3
- установку falco и настроенного falcosidekick, который отправит логи в s3
- установку Kyverno и настроенного [Policy Reporter](https://github.com/kyverno/policy-reporter), который отправит логи в s3
2) [security-events-to-siem-importer](./security-events-to-siem-importer) (импортирует логи в ELK)
- Принимает на вход:
- ряд параметров из модуля (`security-events-to-storage-exporter`)
- `auditlog_enabled` - *true* или *false* (отправлять ли аудит логи k8s в ELK)
- `falco_enabled` - *true* или *false* (отправлять ли алерты falco в ELK)
- `kyverno_enabled` - *true* или *false* (отправлять ли алерты kyverno в ELK)
- адрес FQDN инсталляции ELK
- id подсети, в которой создается ВМ с контейнером импортера
- credentials ELK пользователя для импорта событий
- Выполняет:
- создание YMQ очередей с именами файлов логов в S3
- создание функций для push имен файлов из S3 в YMQ
- создание тригеров для взаимодействия очередей и функций
- генерацию и запись в файл и на ВМ ключей SSH
- создание ВМ на базе COI ([container optimised image](https://cloud.yandex.ru/docs/cos/concepts/)) с контейнерами workers, которые импортируют событий из s3 в ELK
#### Пререквизиты
- :white_check_mark: Cluster Managed k8s
- :white_check_mark: Managed ELK
- :white_check_mark: Сервисный аккаунт, который может писать в бакет и имеет роль *ymq.admin*
- :white_check_mark: Object Storage Bucket
- :white_check_mark: Subnet для развертывания ВМ с включенным NAT
#### Пример вызова модулей:
См. Пример вызова модулей в /example/main.tf
```Python
//Вызов модуля security-events-to-storage-exporter
module "security-events-to-storage-exporter" {
source = "../security-events-to-storage-exporter/" # путь до модуля
folder_id = "xxxxxx" // folder-id кластера k8s yc managed-kubernetes cluster get --id

# Version
**Version-2.0**
- Changelog:
- добавлена поддержка авто-установки kyverno с политиками в режиме audit
- Docker images:
- `cr.yandex/sol/k8s-events-siem-worker:1.1.0`
# Оглавление
- [Описание](#описание)
- [Связь с решением "Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"](#связь-с-решением-"Сбор-мониторинг-и-анализ-аудит-логов-в-Yandex-Managed-Service-for-Elasticsearch-(ELK)")
- [Общая схема](#общая-схема)
- [Описание импортируемых объектов ELK (Security Content)](#описание-импортируемых-объектов-ELK-(Security-Content))
- [Описание terraform](#описание-terraform)
- [Процесс обновления контента](#процесс-обновления-контента)
- [Опционально ручные действие](#опционально-ручные-действие)
## Описание
Решение из "коробки" выполняет следующее:
- ☑️ собирает [k8s AUDIT-LOGS](https://kubernetes.io/docs/tasks/debug-application-cluster/audit/) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/)
- ☑️ устанавливает [FALCO](https://falco.org/) и собирает его [ALERTS](https://falco.org/docs/alerts/) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/)
- ☑️ устанавливает [Kyverno](https://kyverno.io/) c политиками категории [Pod Security Standards (Restricted)](https://kyverno.io/policies/?policytypes=Pod%2520Security%2520Standards%2520%28Restricted%29) в режиме audit и собирает его [ALERTS (PolicyReports)](https://kyverno.io/docs/policy-reports/) (при помощи [Policy Reporter](https://github.com/kyverno/policy-reporter))
- ☑️ импортирует Security Content (dashboards, detection rules и др.)(см. в секции Security Content) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/) для анализа и реагирования на события ИБ.
- ✔️ *В том числе импортирует Security Content для [OPA Gatekeeper](https://open-policy-agent.github.io/gatekeeper/website/docs/) (в режиме enforce). (сам OPA Gatekeeper может быть установлен вручную дополнительно)
- ☑️ Создает индексы в двух репликах, настраивает базовую политику rollover (создания новых индексов каждые тридцать дней или по достижению 50ГБ), для дальнейшей настройки в части высокой доступности данных и для настройки снимков данных в S3 - см. [рекомендации](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md).
## Связь с решением "Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"
Решение ["Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main) содержит информацию о том, как установить Yandex Managed Service for Elasticsearch (ELK) и собирать в него логи Audit Trails
## Общая схема

## Описание импортируемых объектов ELK (Security Content)
Подробное описание объектов по [ссылке](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf)
## Описание terraform
Решение состоит из 2-х модулей Terraform:
1) [security-events-to-storage-exporter](./security-events-to-storage-exporter) (экспортирует логи в s3)
- Принимает на вход:
- `folder_id` - id каталога, в котором расположен кластер
- `cluster_name` - имя кластера Kubernetes
- `log_bucket_service_account_id` - id сервисного аккаунта, который может писать в бакет и имеет роль *ymq.admin*
- `log_bucket_name` - имя бакета, куда нужно сохранять логи
- `function_service_account_id` - (опционально) id сервисного аккаунта, который будет запускать фукнцию, если не указан, то используется `log_bucket_service_account_id`
- Выполняет:
- создание статического ключа для сервисного аккаунта
- создание функции и тригера для записи логов кластера в s3
- установку falco и настроенного falcosidekick, который отправит логи в s3
- установку Kyverno и настроенного [Policy Reporter](https://github.com/kyverno/policy-reporter), который отправит логи в s3
2) [security-events-to-siem-importer](./security-events-to-siem-importer) (импортирует логи в ELK)
- Принимает на вход:
- ряд параметров из модуля (`security-events-to-storage-exporter`)
- `auditlog_enabled` - *true* или *false* (отправлять ли аудит логи k8s в ELK)
- `falco_enabled` - *true* или *false* (отправлять ли алерты falco в ELK)
- `kyverno_enabled` - *true* или *false* (отправлять ли алерты kyverno в ELK)
- адрес FQDN инсталляции ELK
- id подсети, в которой создается ВМ с контейнером импортера
- credentials ELK пользователя для импорта событий
- Выполняет:
- создание YMQ очередей с именами файлов логов в S3
- создание функций для push имен файлов из S3 в YMQ
- создание тригеров для взаимодействия очередей и функций
- генерацию и запись в файл и на ВМ ключей SSH
- создание ВМ на базе COI ([container optimised image](https://cloud.yandex.ru/docs/cos/concepts/)) с контейнерами workers, которые импортируют событий из s3 в ELK
#### Пререквизиты
- :white_check_mark: Cluster Managed k8s
- :white_check_mark: Managed ELK
- :white_check_mark: Сервисный аккаунт, который может писать в бакет и имеет роль *ymq.admin*
- :white_check_mark: Object Storage Bucket
- :white_check_mark: Subnet для развертывания ВМ с включенным NAT
#### Пример вызова модулей:
См. Пример вызова модулей в /example/main.tf
```Python
//Вызов модуля security-events-to-storage-exporter
module "security-events-to-storage-exporter" {
source = "../security-events-to-storage-exporter/" # путь до модуля
folder_id = "xxxxxx" // folder-id кластера k8s yc managed-kubernetes cluster get --id 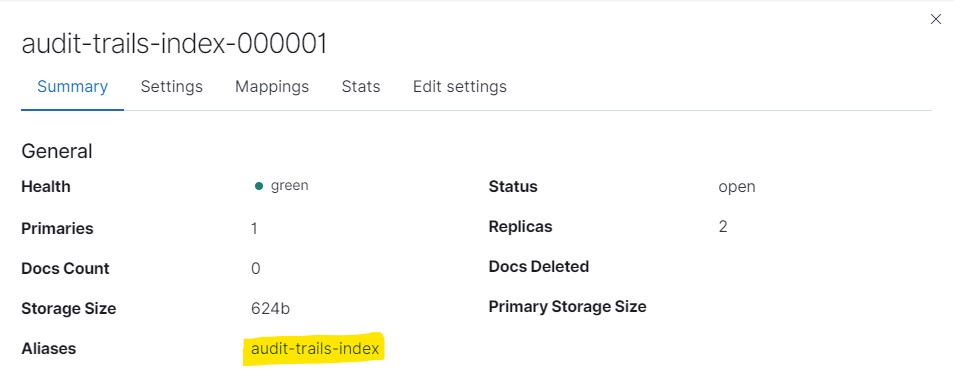 ## Index template
## Index template
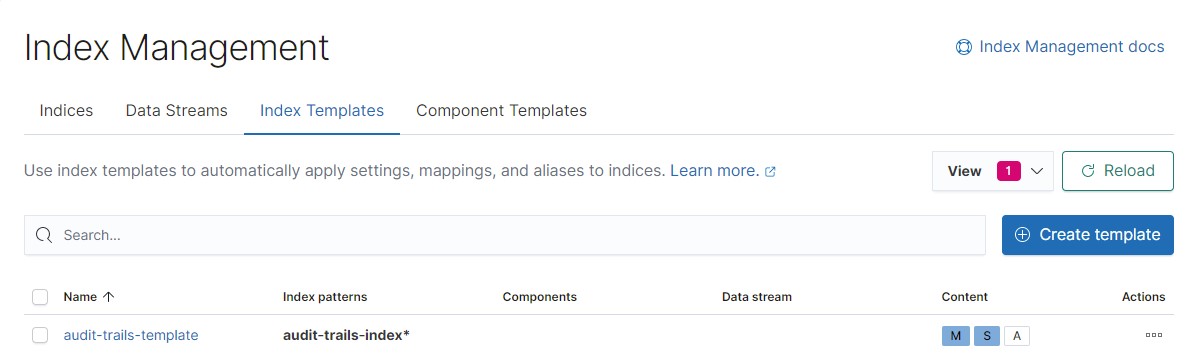 An index template contains all the necessary parameters to create a new index as a result of the rollover:
- Index pattern. Newly created indexes that meet the pattern are automatically created with the template parameters.
- Index settings. In our case, this is the name of the index rollover policy, the number of data replicas, and the `rollover_alias`, that is, the alias that will be moved to the new index.
```
{
"index": {
"lifecycle": {
"name": "audit-trails-ilm",
"rollover_alias": "audit-trails-index"
},
"number_of_replicas": "2"
}
}
```
- Mapping parameters.
## Index lifecycle policy
The index lifecycle policy tracks the lifecycle of our data.
As the data becomes older, you can move it to lower-end servers or disks, and, finally, delete them, after a certain period.
An index template contains all the necessary parameters to create a new index as a result of the rollover:
- Index pattern. Newly created indexes that meet the pattern are automatically created with the template parameters.
- Index settings. In our case, this is the name of the index rollover policy, the number of data replicas, and the `rollover_alias`, that is, the alias that will be moved to the new index.
```
{
"index": {
"lifecycle": {
"name": "audit-trails-ilm",
"rollover_alias": "audit-trails-index"
},
"number_of_replicas": "2"
}
}
```
- Mapping parameters.
## Index lifecycle policy
The index lifecycle policy tracks the lifecycle of our data.
As the data becomes older, you can move it to lower-end servers or disks, and, finally, delete them, after a certain period.
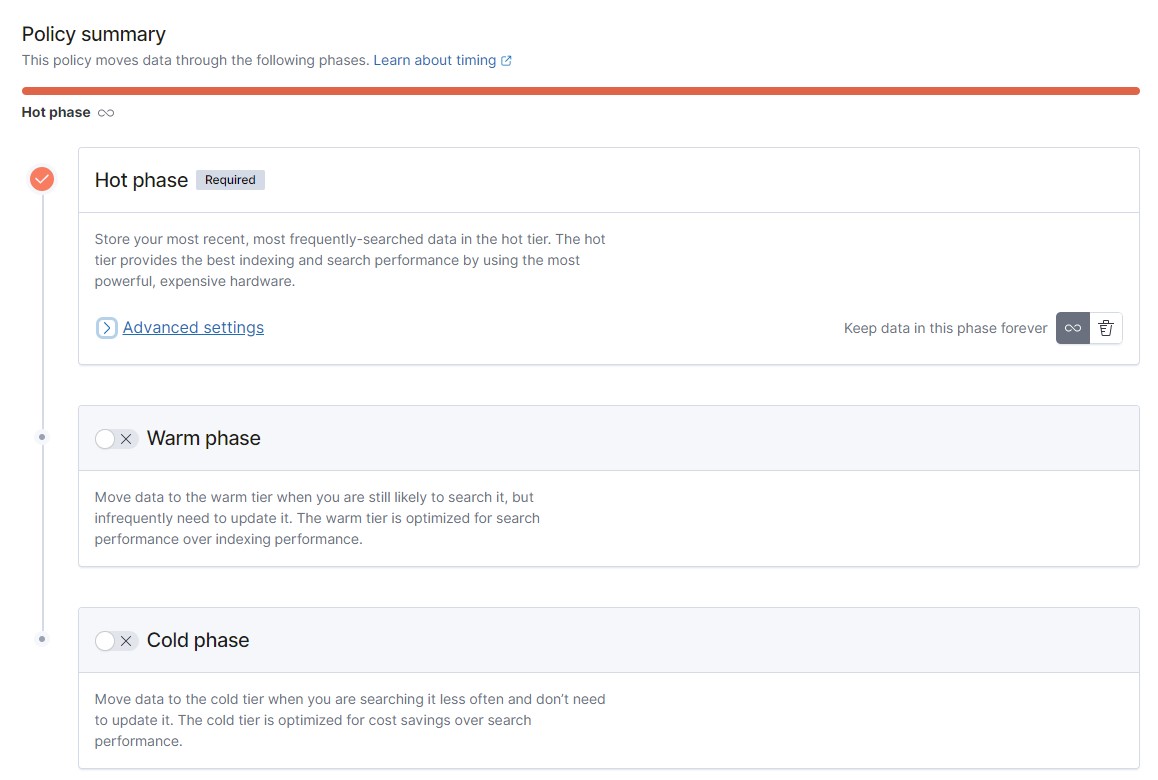 In our example, we configured only the hot phase, with only default metrics for the rollover procedure enabled.
In our example, we configured only the hot phase, with only default metrics for the rollover procedure enabled.
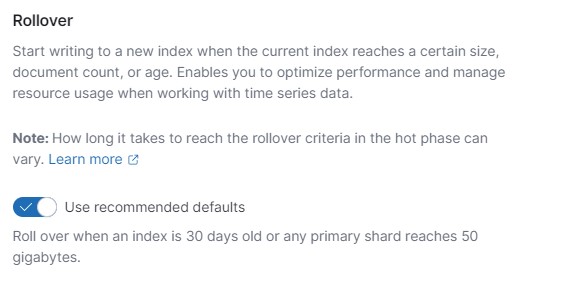 But for production deployment, we recommended to plan for the process of data obsolescence (that is, moving it to "slow" nodes), and deletion.
It is recommended to enable data deletion when you have no other phase but the hot one.
But for production deployment, we recommended to plan for the process of data obsolescence (that is, moving it to "slow" nodes), and deletion.
It is recommended to enable data deletion when you have no other phase but the hot one.
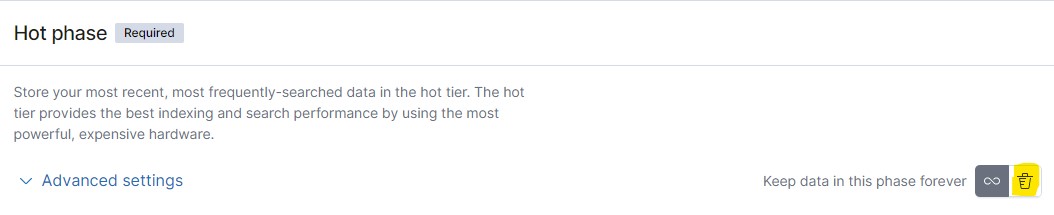 After a certain period, indexes with obsolete data will be deleted.
If you have set up data snapshots, you can enable the delete option only if a snapshot is present. In this case, specify the name of the snapshot policy.
After a certain period, indexes with obsolete data will be deleted.
If you have set up data snapshots, you can enable the delete option only if a snapshot is present. In this case, specify the name of the snapshot policy.
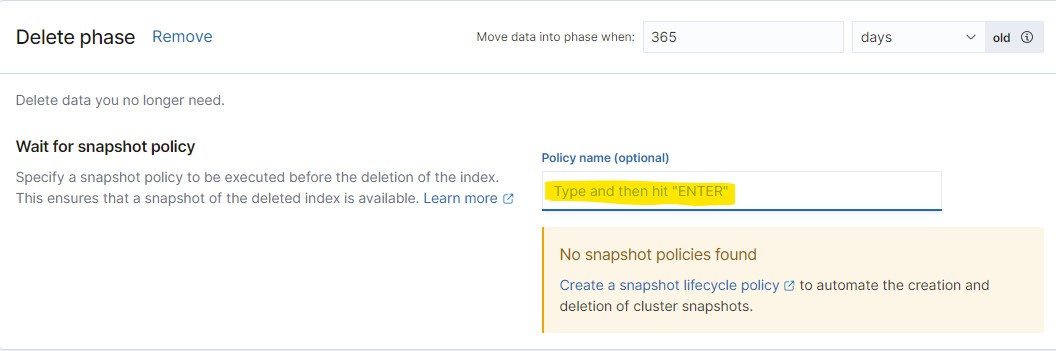 Setting up the snapshot creation policy is described below.
## Snapshot creation policy
Data snapshots are used for backing up data at certain time points. We recommend setting up a snapshot creation policy for your production environment. The snapshots created can be stored in Yandex.Cloud S3 storage. The procedure for setting up the policy with an S3 storage is described below. Snapshots are created incrementally and consume a minimum space in the long run, because only changes are added.
To store snapshots in an S3 storage, you need:
1. Set up a service account to work with S3 and connect it to the Elasticsearch cluster.
2. Configure access rights.
3. Connect the repository to Elasticsearch.
These steps are described in the [documentation](https://cloud.yandex.ru/docs/managed-elasticsearch/operations/s3-access) for Managed Service for Elasticsearch.
Example of a created snapshot repository:
Setting up the snapshot creation policy is described below.
## Snapshot creation policy
Data snapshots are used for backing up data at certain time points. We recommend setting up a snapshot creation policy for your production environment. The snapshots created can be stored in Yandex.Cloud S3 storage. The procedure for setting up the policy with an S3 storage is described below. Snapshots are created incrementally and consume a minimum space in the long run, because only changes are added.
To store snapshots in an S3 storage, you need:
1. Set up a service account to work with S3 and connect it to the Elasticsearch cluster.
2. Configure access rights.
3. Connect the repository to Elasticsearch.
These steps are described in the [documentation](https://cloud.yandex.ru/docs/managed-elasticsearch/operations/s3-access) for Managed Service for Elasticsearch.
Example of a created snapshot repository:
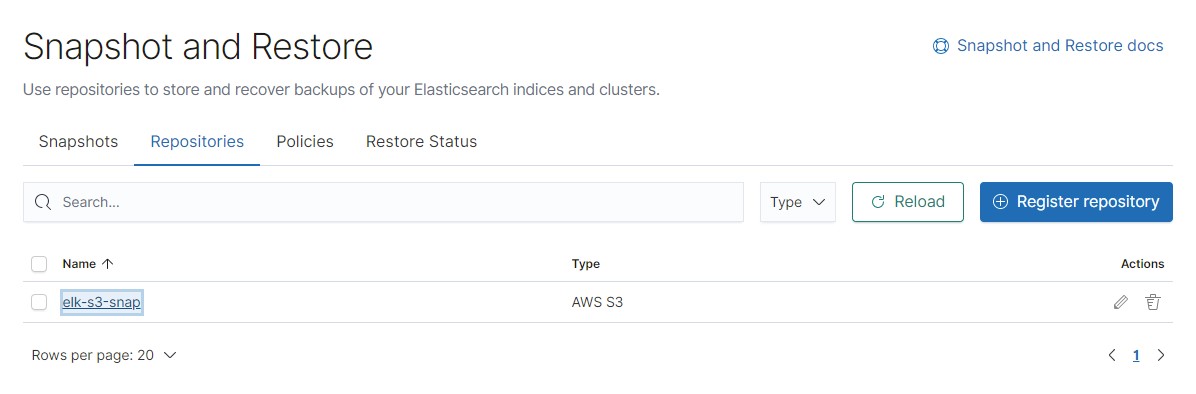 After the repository has been connected to Elasticsearch, you can configure your first snapshot creation policy.
After the repository has been connected to Elasticsearch, you can configure your first snapshot creation policy.
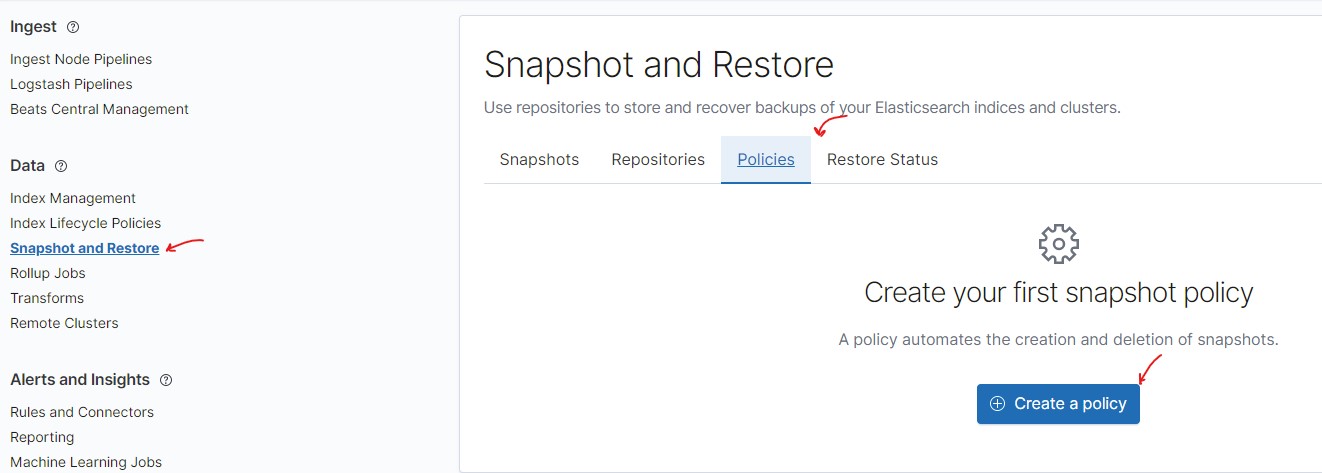 Then use a simple setup wizard to specify:
- The name of the snapshot policy.
- Pattern for the snapshot names.
- A repository for snapshots that your created previously.
- A schedule for creating snapshots (for example, every hour).
- Snapshot parameters: take snapshots for all or specific indexes, retain cluster state in the snapshot, and others.
- Snapshot retention parameters.
The created snapshot policy may look as follows:
Then use a simple setup wizard to specify:
- The name of the snapshot policy.
- Pattern for the snapshot names.
- A repository for snapshots that your created previously.
- A schedule for creating snapshots (for example, every hour).
- Snapshot parameters: take snapshots for all or specific indexes, retain cluster state in the snapshot, and others.
- Snapshot retention parameters.
The created snapshot policy may look as follows:
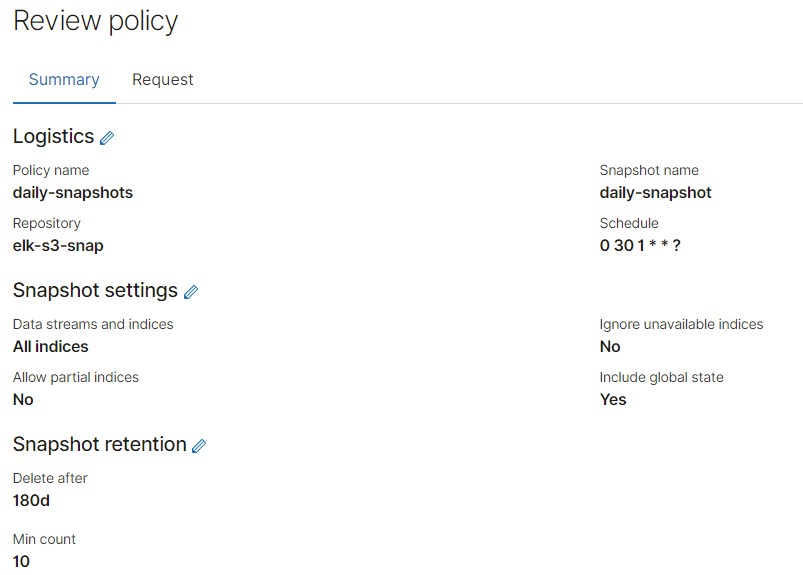 After the policy is created, you can see it in the list of all policies wherefrom you can run it and check straight away.
After the policy is created, you can see it in the list of all policies wherefrom you can run it and check straight away.
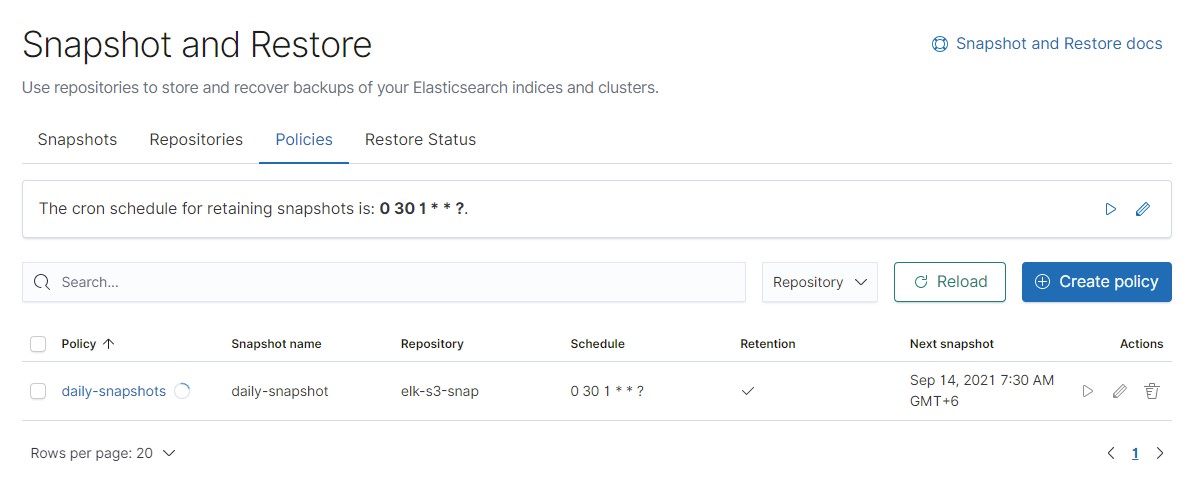 When you run the policy, a new snapshot is created and shown in the list.
When you run the policy, a new snapshot is created and shown in the list.
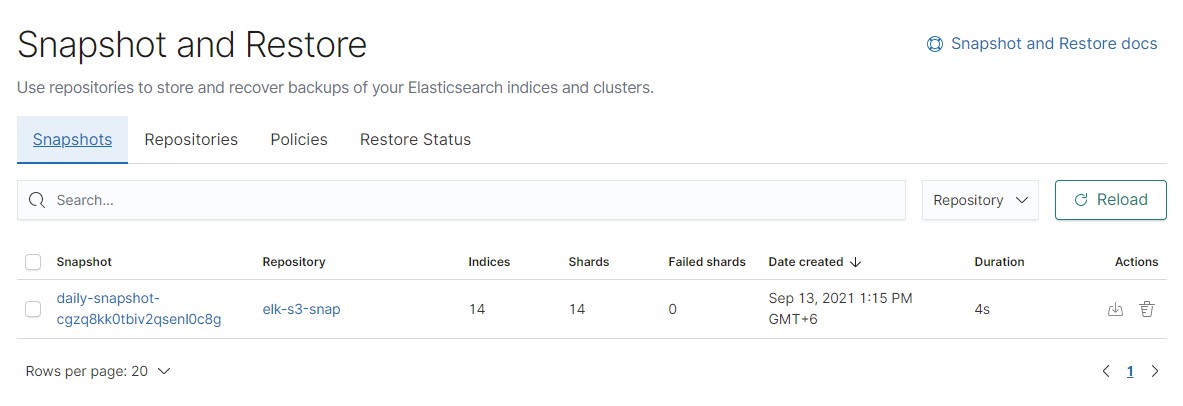 The data also appears in the object storage:
The data also appears in the object storage:
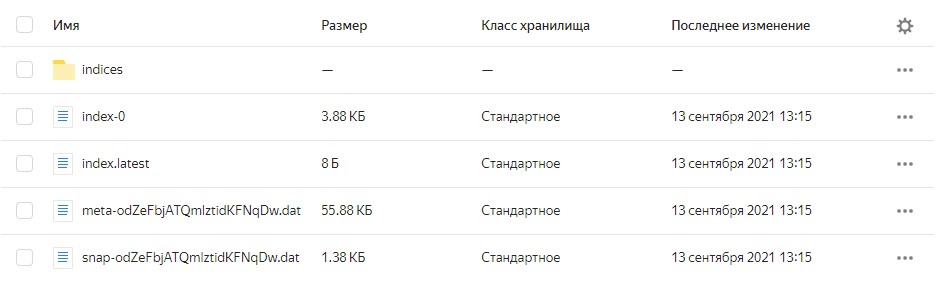 The snapshot policy can be used in the index lifecycle policy created previously.
The snapshot policy can be used in the index lifecycle policy created previously.
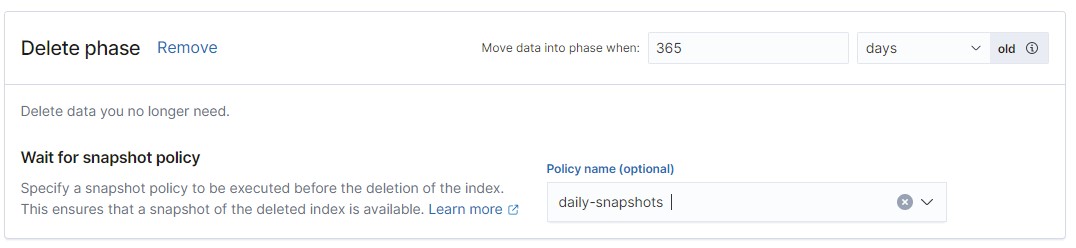 ================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/CONFIGURE-HA_RU.md
================================================
# Рекомендации для высокой доступности данных
Наш пример ElasticSearch устанавливается в базовой конфигурации.
В части высокой доступности данных применены следующие механизмы:
- Несколько нод для данных
- Несколько реплик для индексов
- Индексы ротируются (`rollover`) по рекомендованной схеме, а именно:
- По достижению индексом размера в 50ГБ, создается новый индекс, или
- Каждый тридцать дней, создается новый индекс
- Данные отправляются в алиас (`alias`), который привязан к активному индексу, то есть ротация индекса не должна повлиять на работу схемы в примере
## Ротация индекса
Ротация индекса использует следующие сущности в ElasticSearch:
- Индексы и алиас (`alias`) индекса
- Шаблона индекса (`index template`)
- Политика жизненного цикла индекса (`index lifecycle policy`)
Первый индекс в примере создается с цифровым суффиксом — это необходимо, чтобы в результате ротации создался новый индекс с измененным суффиксом.
На созданный индекс назначается алиас, который в процессе ротации переносится на новый индекс.
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/CONFIGURE-HA_RU.md
================================================
# Рекомендации для высокой доступности данных
Наш пример ElasticSearch устанавливается в базовой конфигурации.
В части высокой доступности данных применены следующие механизмы:
- Несколько нод для данных
- Несколько реплик для индексов
- Индексы ротируются (`rollover`) по рекомендованной схеме, а именно:
- По достижению индексом размера в 50ГБ, создается новый индекс, или
- Каждый тридцать дней, создается новый индекс
- Данные отправляются в алиас (`alias`), который привязан к активному индексу, то есть ротация индекса не должна повлиять на работу схемы в примере
## Ротация индекса
Ротация индекса использует следующие сущности в ElasticSearch:
- Индексы и алиас (`alias`) индекса
- Шаблона индекса (`index template`)
- Политика жизненного цикла индекса (`index lifecycle policy`)
Первый индекс в примере создается с цифровым суффиксом — это необходимо, чтобы в результате ротации создался новый индекс с измененным суффиксом.
На созданный индекс назначается алиас, который в процессе ротации переносится на новый индекс.
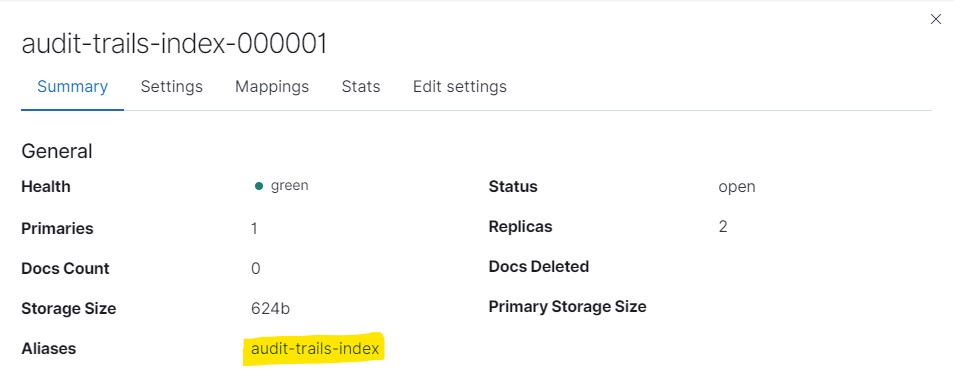 ## Шаблон индекса
## Шаблон индекса
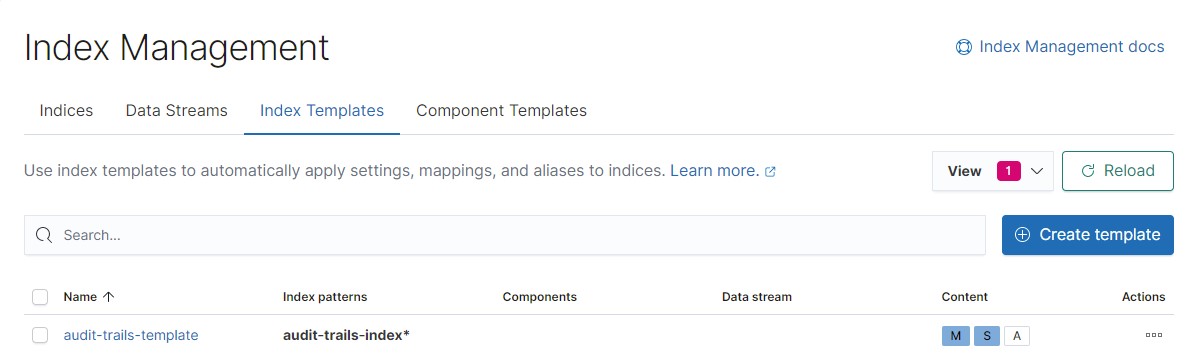 Шаблон индекса содержит все необходимые параметры для создания нового индекса в результате ротации:
- Паттерн индекса (`index pattern`). Новосозданные индексы, подпадающие под паттерн, будут автоматически созданы с параметрами шаблона.
- Настройки индекса. В нашем случае, это имя политики ротации (`index rollover policy`), количество реплик данных и `rollover_alias` - алиас, который будет перенесен на новый индекс.
```
{
"index": {
"lifecycle": {
"name": "audit-trails-ilm",
"rollover_alias": "audit-trails-index"
},
"number_of_replicas": "2"
}
}
```
- Параметры сопоставления (`mapping`).
## Политика ротации
Политика ротации (`index lifecycle policy`) отслеживает "жизненный путь" наших данных.
По мере устаревания данных, данные можно переносить на менее производительные серверы или диски, а по истечении определенного времени — и, вовсе, удалить.
Шаблон индекса содержит все необходимые параметры для создания нового индекса в результате ротации:
- Паттерн индекса (`index pattern`). Новосозданные индексы, подпадающие под паттерн, будут автоматически созданы с параметрами шаблона.
- Настройки индекса. В нашем случае, это имя политики ротации (`index rollover policy`), количество реплик данных и `rollover_alias` - алиас, который будет перенесен на новый индекс.
```
{
"index": {
"lifecycle": {
"name": "audit-trails-ilm",
"rollover_alias": "audit-trails-index"
},
"number_of_replicas": "2"
}
}
```
- Параметры сопоставления (`mapping`).
## Политика ротации
Политика ротации (`index lifecycle policy`) отслеживает "жизненный путь" наших данных.
По мере устаревания данных, данные можно переносить на менее производительные серверы или диски, а по истечении определенного времени — и, вовсе, удалить.
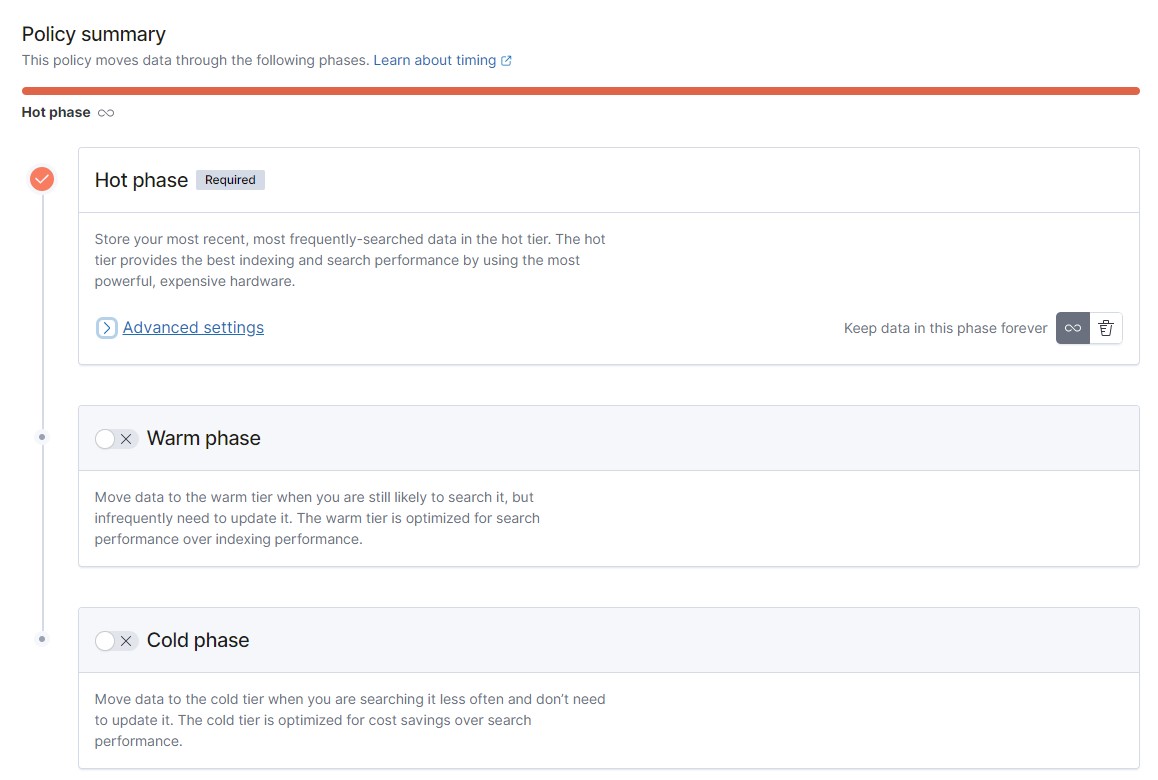 В нашем примере настроена только горячая фаза (`hot phase`) и была включена рекомендованный по умолчанию метрики для процедуры rollover.
В нашем примере настроена только горячая фаза (`hot phase`) и была включена рекомендованный по умолчанию метрики для процедуры rollover.
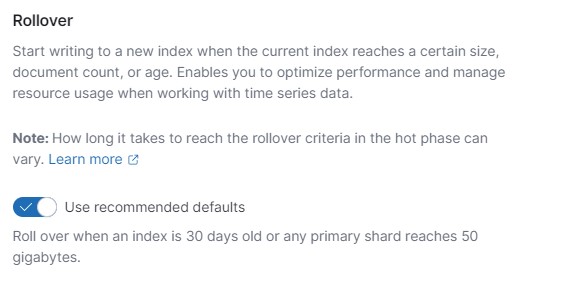 Но в продуктивном развертывании рекомендуется спланировать, как процесс устаревания данных (перенос на "медленные" ноды), так и их удаление.
Удаление данных рекомендуется включить и при отсутствии других фаз, только для горячей фазы.
Но в продуктивном развертывании рекомендуется спланировать, как процесс устаревания данных (перенос на "медленные" ноды), так и их удаление.
Удаление данных рекомендуется включить и при отсутствии других фаз, только для горячей фазы.
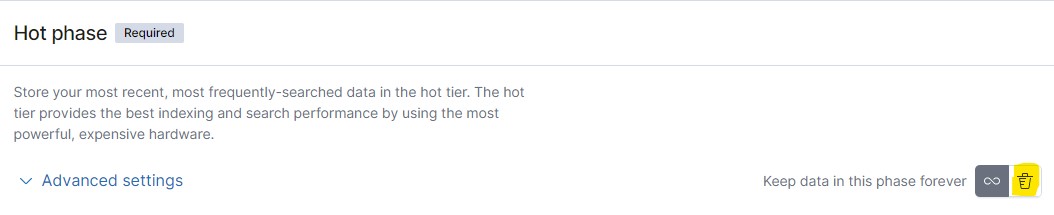 По истечении определенного времени, индексы с устаревшими данными будут удалены.
Если настроены снимки данных (`snapshots`) — можно включить опцию удаления только при наличии снимка.
В этом случае, необходимо указать имя политики создания снимков (`snapshot policy`).
По истечении определенного времени, индексы с устаревшими данными будут удалены.
Если настроены снимки данных (`snapshots`) — можно включить опцию удаления только при наличии снимка.
В этом случае, необходимо указать имя политики создания снимков (`snapshot policy`).
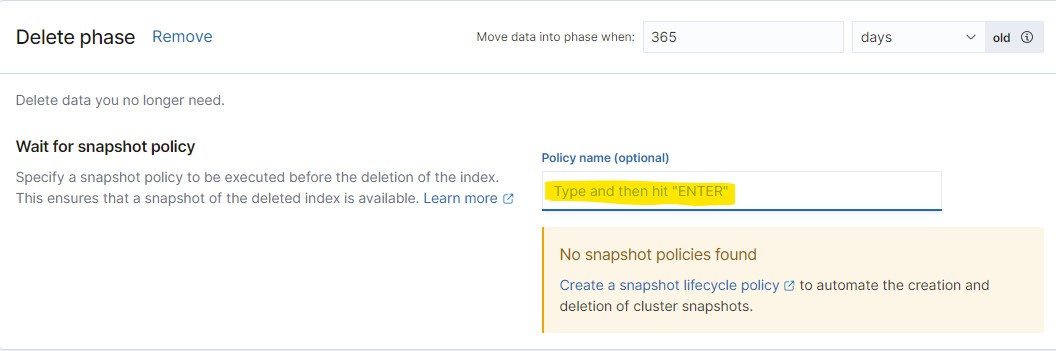 Настройка политики создания снимков описана ниже.
## Политика создания снимков
Снимки данных (`snapshots`) необходимы для создания резервных копий данных на определенный момент времени.
Рекомендуется настроить политику создания снимков в продуктивной среде.
Созданные снимки данных можно хранить в S3 хранилище Yandex.Cloud — ниже описана процедура настройки политики с использованием хранилища S3.
Снимки создаются инкрементально и не занимают много пространства в долгосрочной перспективе, так как добавляются только изменения.
Для хранения снимков в S3 хранилище необходимо:
1. Настроить сервисный аккаунт для работы с S3 и подключить его к кластеру ElasticSearch
2. Настроить права доступа
3. Подключить репозиторий к ElasticSearch
Эти шаги описаны в [документации](https://cloud.yandex.ru/docs/managed-elasticsearch/operations/s3-access) к Managed Service for ElasticSearch.
Пример созданного репозитория снимков:
Настройка политики создания снимков описана ниже.
## Политика создания снимков
Снимки данных (`snapshots`) необходимы для создания резервных копий данных на определенный момент времени.
Рекомендуется настроить политику создания снимков в продуктивной среде.
Созданные снимки данных можно хранить в S3 хранилище Yandex.Cloud — ниже описана процедура настройки политики с использованием хранилища S3.
Снимки создаются инкрементально и не занимают много пространства в долгосрочной перспективе, так как добавляются только изменения.
Для хранения снимков в S3 хранилище необходимо:
1. Настроить сервисный аккаунт для работы с S3 и подключить его к кластеру ElasticSearch
2. Настроить права доступа
3. Подключить репозиторий к ElasticSearch
Эти шаги описаны в [документации](https://cloud.yandex.ru/docs/managed-elasticsearch/operations/s3-access) к Managed Service for ElasticSearch.
Пример созданного репозитория снимков:
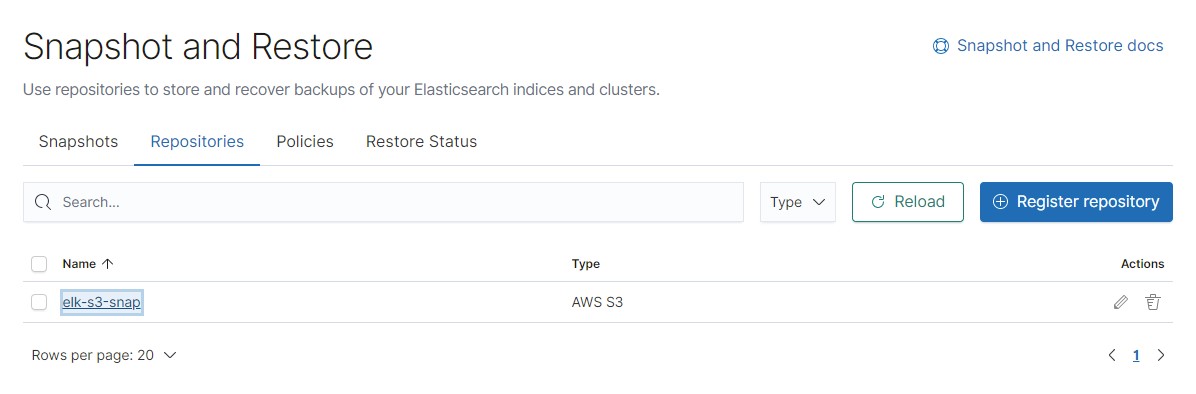 После того, как репозиторий был подключен к ElasticSearch, можно выполнить настройку первой политики для создания снимков.
После того, как репозиторий был подключен к ElasticSearch, можно выполнить настройку первой политики для создания снимков.
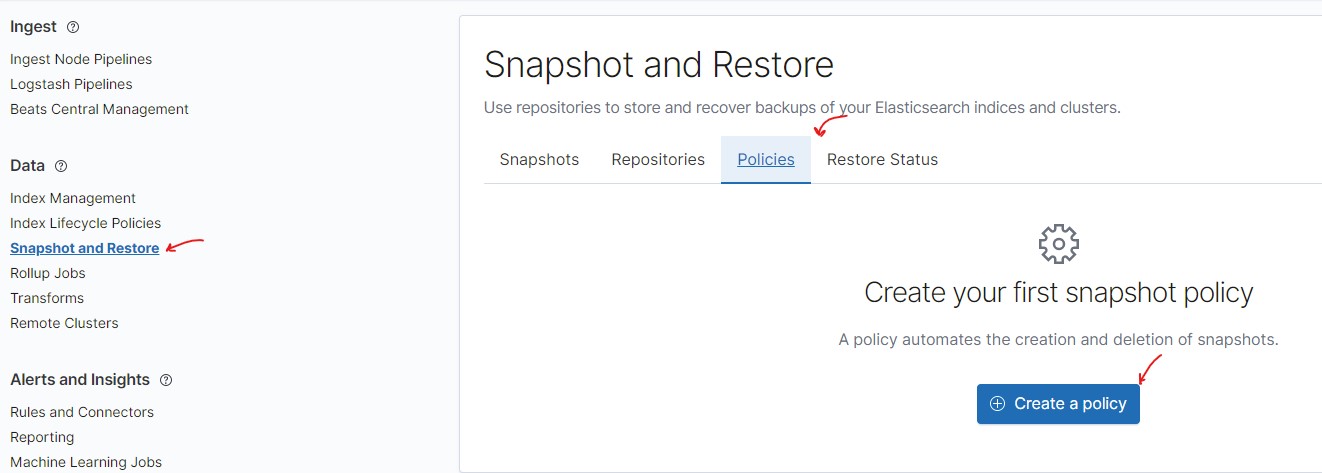 Далее, через простой мастер настройки, необходимо указать:
- Имя политики снимков
- Паттерн для имен, созданных снимков
- Репозиторий снимков, который был создан ранее
- График создания снимков (например, каждый час)
- Параметры снимков: делать снимки для всех или определенных индексов, хранить в снимке состояние кластера, и др.
- Параметры хранения снимков (`retention`)
Созданная политика снимков может выглядеть следующим образом:
Далее, через простой мастер настройки, необходимо указать:
- Имя политики снимков
- Паттерн для имен, созданных снимков
- Репозиторий снимков, который был создан ранее
- График создания снимков (например, каждый час)
- Параметры снимков: делать снимки для всех или определенных индексов, хранить в снимке состояние кластера, и др.
- Параметры хранения снимков (`retention`)
Созданная политика снимков может выглядеть следующим образом:
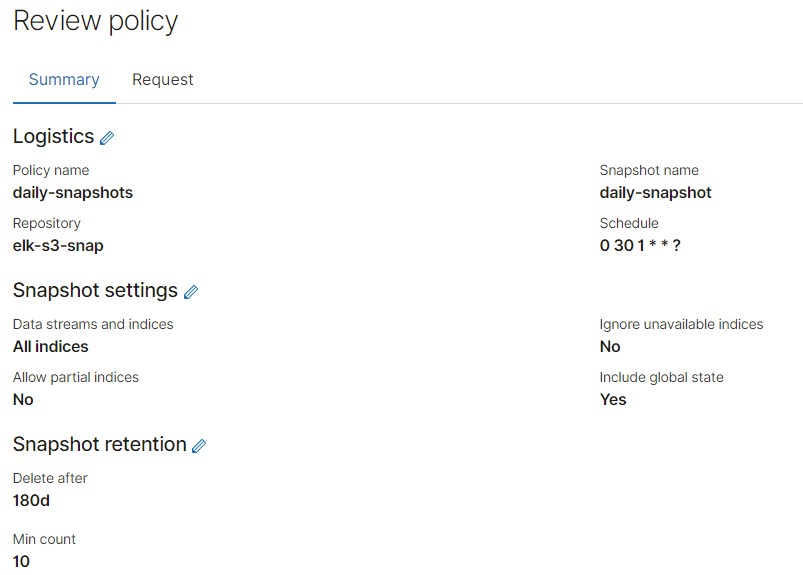 После создания политики, она будет видна в общем списке политик, где её можно сразу же запустить и проверить.
После создания политики, она будет видна в общем списке политик, где её можно сразу же запустить и проверить.
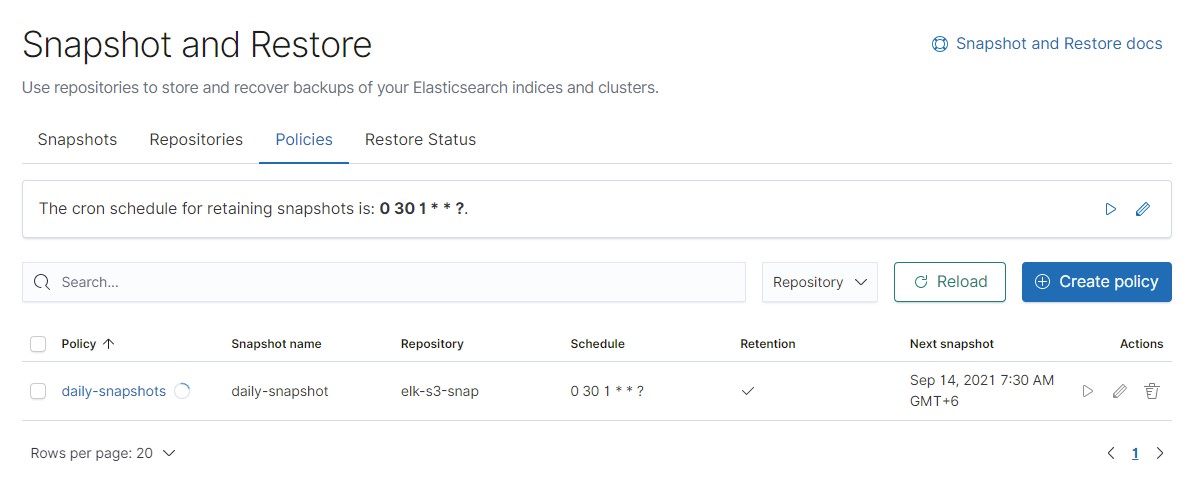 В результате запуска, создан новый снимок, который отображается в списке.
В результате запуска, создан новый снимок, который отображается в списке.
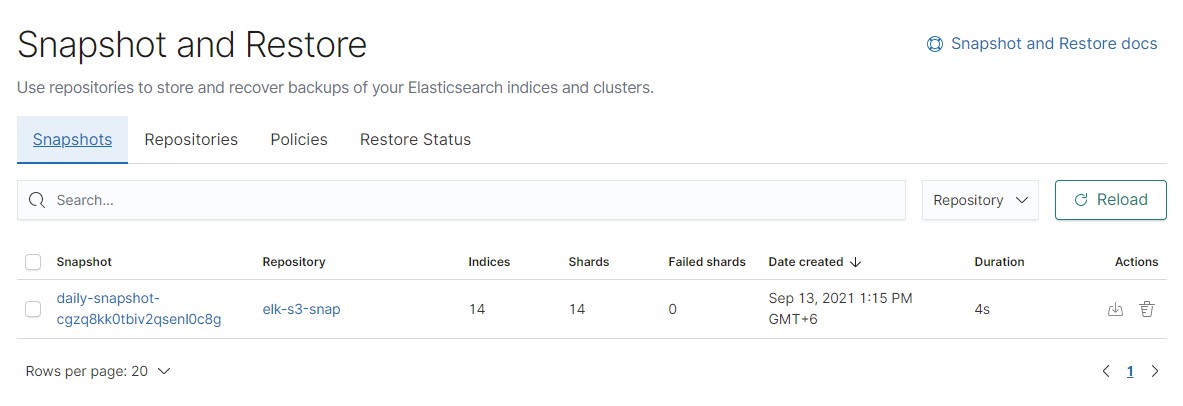 А также, данные появились и в самом объектном хранилище:
А также, данные появились и в самом объектном хранилище:
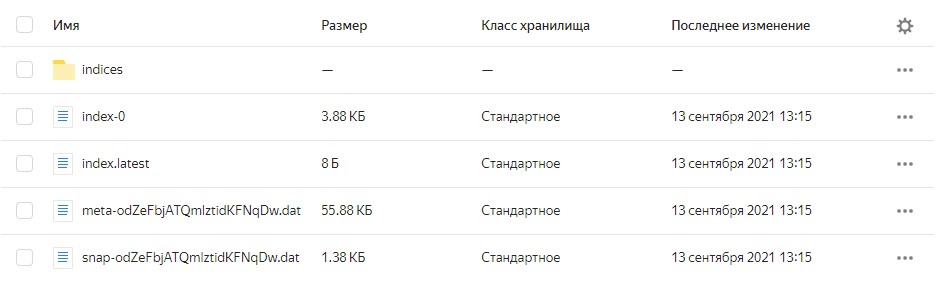 Созданную политику снимков можно задействовать в политике ротации индексов, которая была создана ранее.
Созданную политику снимков можно задействовать в политике ротации индексов, которая была создана ранее.
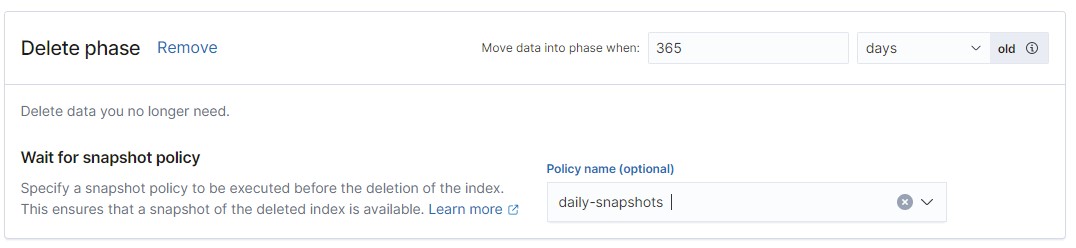 ================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/LICENSE
================================================
Copyright 2021 YANDEX LLC
Licensed under the Apache License, Version 2.0 (the "License");
you may not use this file except in compliance with the License.
You may obtain a copy of the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software
distributed under the License is distributed on an "AS IS" BASIS,
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
See the License for the specific language governing permissions and
limitations under the License.
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/README.md
================================================
# Collecting, monitoring and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)

# Version
**Version-2.1**
- Changelog:
- Added new use cases from [Use cases and important security events in audit logs](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches#use-cases-%D0%B8-%D0%B2%D0%B0%D0%B6%D0%BD%D1%8B%D0%B5-%D1%81%D0%BE%D0%B1%D1%8B%D1%82%D0%B8%D1%8F-%D0%B1%D0%B5%D0%B7%D0%BE%D0%BF%D0%B0%D1%81%D0%BD%D0%BE%D1%81%D1%82%D0%B8-%D0%B2-%D0%B0%D1%83%D0%B4%D0%B8%D1%82-%D0%BB%D0%BE%D0%B3%D0%B0%D1%85)"
- Docker images:
- `cr.yandex/sol/s3-elk-importer:2.1`
- `cr.yandex/sol/elk-updater:1.0.4`
**Version-2.0**
- Changelog:
- Добавлен фильтр по Folder name
- Docker images:
- `cr.yandex/sol/s3-elk-importer:1.0.6`
# Table of contents
- [Solution description](#solution-description)
- [Solution features](#solution-features)
- [Solution diagram](#solution-diagram)
- [Security Content](#security-content)
- [License restrictions](#license-restrictions)
- [Content update process](#content-update-process)
- [Deployment using Terraform](#deployment-using-Terraform)
- [Deployment of a solution to supply K8s logs] (#deployment-of-a-solution-to-supply-k8s-logs)
- [Recommendations for setting up retention, rollover, and snapshots](#recommendations-for-setting-retention-rollover-and-snapshots)
## Solution description
The solution lets you collect, monitor, and analyze audit logs in Yandex Managed Service for Elasticsearch (ELK) from the following sources:
- [Yandex Audit Trails](https://cloud.yandex.ru/docs/audit-trails/)
- [Yandex Managed Service for Kubernetes](https://cloud.yandex.ru/docs/managed-kubernetes/): audit logs, Falco alerts, and Policy Engine (OPA Gatekeeper) ([setup description](../export-auditlogs-to-ELK_k8s))
> The solution is constantly updated and maintained by the Yandex.Cloud Security team.
## Solution features
- ☑️ Deploy a Managed ELK cluster in the Yandex.Cloud infrastructure via Terraform. In the default configuration, see Deployment using Terraform. Calculate the relevant configuration for your infrastructure together with your cloud architect.
- ☑️ Deploy a COI Instance with container based on the s3-elk-importer image (`cr.yandex/crpjfmfou6gflobbfvfv/s3-elk-importer:latest`).
- ☑️ Upload Security Content to ELK: Dashboards, Detection Rules with alerts, etc.
- ☑️ Enable continuous delivery of JSON files with audit logs from Yandex Object Storage to ELK.
- ☑️ Create indexes in two replicas, configure the basic rollover policy (create new indexes every thirty days or after reaching 50 GB). For further provisioning for high data availability and setting up data snapshots in S3, see [recommendations](./CONFIGURE-HA.md).
## Solution diagram

[Diagram of the solution to supply K8s logs](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_k8s)
## Security Content
**Security Content** are ELK objects automatically loaded by the solution. All the content leverages the long-term expertise of the Yandex.Cloud Security team and our cloud customers.
The solution contains the following Security Content:
- Dashboard that reflects all use cases and useful statistics.
- A set of Saved Queries for easy search of Security events.
- A set of Detection Rules: the correlation rules for which alerts are configured (the client should specify the alert destination).
All relevant event fields have been converted to the [Elastic Common Schema (ECS)] (https://www.elastic.co/guide/en/ecs/current/index.html) format, the full mapping table is in the [file with object description](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf).
A detailed description is in the [ECS-mapping.docx](./papers/ECS-mapping_new.pdf) file
## License restrictions


[Subscription options on ELK site](https://www.elastic.co/subscriptions)
## Content update process
We recommend subscribing to this repository to receive update notifications.
To get the latest content version, do the following:
- Keep the sync container up-to-date.
- Keep the Security content imported to Elasticsearch in the updated state.
For content updates, make sure that you are running the latest available image version: `cr.yandex/crpjfmfou6gflobbfvfv/s3-elk-importer:latest`.
You can update the container as follows:
- You can re-create the deployed COI Instance with the container via Terraform (delete the COI Instance and run: `terraform apply`).
- You can stop and delete the `audit-trail-worker-*` container, delete the `s3-elk-importer` image, and restart COI Instance. After the launch, a new image will be downloaded and a new container will be created.
You can update the Security content in Kibana (dashboards, detection rules, searches) by launching the elk-updater container:
```
docker run -it --rm -e ELASTIC_AUTH_USER='admin' -e ELASTIC_AUTH_PW='password' -e KIBANA_SERVER='https://xxx.rw.mdb.yandexcloud.net' --name elk-updater cr.yandex/crpjfmfou6gflobbfvfv/elk-updater:latest
```
## Deployment using Terraform
#### Description
#### Prerequisites:
- :white_check_mark: Object Storage Bucket for Audit Trails.
- :white_check_mark: [Audit Trails service enabled](https://cloud.yandex.ru/docs/audit-trails/quickstart) in the UI.
- :white_check_mark: VPC network.
- :white_check_mark: Subnets in three availability zones.
- :white_check_mark: COI Instance has access to the internet to download the container image.
- :white_check_mark: ServiceAccount with the *storage.editor* role for actions in Object Storage.
See the example of configuring prerequisites and calling modules in [/example/main.tf](./terraform/example)
##
The solution consists of two Terraform modules [/terraform/modules/](./terraform/modules):
- yc-managed-elk creates a cluster [Yandex Managed Service for Elasticsearch](https://cloud.yandex.ru/services/managed-elasticsearch):
- With three nodes (one for each availability zone).
- With a Gold license.
- Characteristics: s2-medium (8 vCPU, 32GB RAM), HDD: 1TB.
- A password to the ELK admin account.
- yc-elastic-trail:
- Creates static keys for the SA (for working with JSON objects in a bucket and encrypting/decrypting secrets).
- Creates a COI VM with a Docker Container specification using a script.
- Creates an SSH key pair and saves the private part to the disk and the public part to the VM.
- Creates a KMS key.
- Assigns the kms.keys.encrypterDecrypter rights to the key for SA to encrypt secrets.
- Encrypts secrets and passes them to Docker Container.
#### Example of calling modules:
```Python
module "yc-managed-elk" {
source = "../modules/yc-managed-elk" # path to module yc-managed-elk
folder_id = var.folder_id
subnet_ids = yandex_vpc_subnet.elk-subnet[*].id # Subnets in three availability zones for ELK deployment
network_id = yandex_vpc_network.vpc-elk.id # The ID of the network where ELK will be deployed
elk_edition = "gold"
elk_datanode_preset = "s2.medium"
elk_datanode_disk_size = 1000
elk_public_ip = false # true if you need a public access to Elasticsearch
}
module "yc-elastic-trail" {
source = "../modules/yc-elastic-trail/" # path to module yc-elastic-trail
folder_id = var.folder_id
elk_credentials = module.yc-managed-elk.elk-pass
elk_address = module.yc-managed-elk.elk_fqdn
bucket_name = yandex_storage_bucket.trail-bucket.bucket
bucket_folder = "" # Specify the name of the prefix where trails writes logs to the bucket, for example prefix-trails (if it's root, then leave empty at default)
sa_id = yandex_iam_service_account.sa-bucket-editor.id
coi_subnet_id = yandex_vpc_subnet.elk-subnet[0].id
}
output "elk-pass" {
value = module.yc-managed-elk.elk-pass
sensitive = true
} // View the ELK password: terraform output elk-pass
output "elk_fqdn" {
value = module.yc-managed-elk.elk_fqdn
} // Outputs the ELK URL that can be accessed, for example, through the browser
output "elk-user" {
value = "admin"
}
```
## Deployment of a solution to supply K8s logs
[Deployment of the K8s log delivery solution](../export-auditlogs-to-ELK_k8s)
## Recommendations for setting up retention, rollover, and snapshots
[Recommendations for setting up retention, rollover, and snapshots](./CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/README_RU.md
================================================
# Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)

# Version
**Version-2.1**
- Changelog:
- Добавлены новые detection rules из [Use cases и важные события безопасности в аудит логах](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches#use-cases-%D0%B8-%D0%B2%D0%B0%D0%B6%D0%BD%D1%8B%D0%B5-%D1%81%D0%BE%D0%B1%D1%8B%D1%82%D0%B8%D1%8F-%D0%B1%D0%B5%D0%B7%D0%BE%D0%BF%D0%B0%D1%81%D0%BD%D0%BE%D1%81%D1%82%D0%B8-%D0%B2-%D0%B0%D1%83%D0%B4%D0%B8%D1%82-%D0%BB%D0%BE%D0%B3%D0%B0%D1%85)"
- Docker images:
- `cr.yandex/sol/s3-elk-importer:2.1`
- `cr.yandex/sol/elk-updater:1.0.4`
**Version-2.0**
- Changelog:
- Добавлен фильтр по Folder name
- Docker images:
- `cr.yandex/sol/s3-elk-importer:1.0.6`
# Оглавление
- [Описание решения](#описание-решения)
- [Что делает решение](#что-делает-решение)
- [Схема решения](#схема-решения)
- [Security Content](#security-content)
- [Лицензионные ограничения](#лицензионные-ограничения)
- [Процесс обновления контента](#процесс-обновления-контента)
- [Развертывание с помощью Terraform](#развертывание-с-помощью-Terraform)
- [Развертывание решения для поставки логов k8s](#развертывание-решения-для-поставки-логов-k8s)
- [Рекомендации по настройке retention, rollover и snapshots:](#рекомендации-по-настройке-retention-rollover-и-snapshots)
## Описание решения
Решение позволяет собирать, мониторить и анализировать аудит логи в Yandex.Cloud Managed Service for Elasticsearch (ELK) из следующих источников:
- [Yandex Audit Trails](https://cloud.yandex.ru/docs/audit-trails/)
- [Yandex Managed Service for Kubernetes](https://cloud.yandex.ru/docs/managed-kubernetes/): аудит логи, алерты falco и Policy Engine (OPA Gatekeeper) ([описание настройки](../export-auditlogs-to-ELK_k8s))
> Решение является постоянно обновляемым и поддерживаемым Security-командой Yandex.Cloud.
> Важно! По умолчанию данная конструкция предлагает удалять файлы после вычитывания из бакета, но вы можете одновременно хранить аудит логи Audit Trails в S3 на долгосрочной основе и отсылать в Elastic. Для этого необходимо создать два Audit Trails в разных S3 бакетах:
- Первый бакет будет использоваться только для хранения
- Второй бакет будет использоваться для интеграции с ArcSight
## Что делает решение
- ☑️ Разворачивает в инфраструктуре Yandex.Cloud кластер Managed ELK (через Terraform) (в default конфигурации см. п. Terraform)(рассчитать необходимую конфигурацию для вашей инфраструктуры необходимо совместно с Cloud Архитектором)
- ☑️ Разворачивает COI Instance с контейнером на базе образа s3-elk-importer (`cr.yandex/sol/s3-elk-importer:latest`)
- ☑️ Загружает Security Content в ELK (Dashboards, Detection Rules (с alerts), etc.)
- ☑️ Обеспечивает непрерывную доставку json файлов с аудит логами из Yandex Object Storage в ELK
- ☑️ Создает индексы в двух репликах, настраивает базовую политику rollover (создания новых индексов каждые тридцать дней или по достижению 50ГБ), для дальнейшей настройки в части высокой доступности данных и для настройки снимков данных в S3 - см. [рекомендации](./CONFIGURE-HA.md).
## Схема решения

[Схема решения для поставки логов k8s](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_k8s)
## Security Content
**Security Content** — объекты ELK, которые автоматически загружаются решением. Весь контент разработан с учетом многолетнего опыта Security команды Yandex.Cloud и на основе опыта Клиентов облака.
Содержит следующий Security Content:
- Dashboard, на котором отражены все use cases и полезная статистика
- Набор Saved Queries для удобного поиска Security событий
- Набор Detection Rules (правила корреляции) на которые настроены оповещения (Клиенту самостоятельно необходимо указать назначение уведомлений)
- Все интересные поля событий преобразованы в формат [Elastic Common Schema (ECS)](https://www.elastic.co/guide/en/ecs/current/index.html), полная табличка маппинга в файле [Описание объектов](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf)
Подробное описание в файле [ECS-mapping.docx](./papers/ECS-mapping_new.pdf)
## Лицензионные ограничения


[Описание различий с сайта ELK](https://www.elastic.co/subscriptions)
## Процесс обновления контента
Рекомендуем подписаться на данный репозиторий для получения уведомлений об обновлениях.
Для того, чтобы использовать самую актуальную версию контента, необходимо
- Поддерживать в актуальной версии контейнер, выполняющий синхронизацию
- Поддерживать в актуальном состоянии Security контент, который импортируется в ElasticSearch
В части обновления контента, необходимо убедиться, что вы используете последнюю доступную версию образа:
`cr.yandex/sol/s3-elk-importer:latest`
Обновление контейнера можно выполнить следующим образом:
- Можно пересоздать развернутый COI Instance с контейнером через Terraform (удалить COI Instance, выполнить `terraform apply`)
- Можно остановить и удалить сам контейнер (`audit-trail-worker-*`), удалить образ `s3-elk-importer`, перезапустить COI Instance — после запуска будет скачан новый образ и создан новый контейнер
Обновление Security контента в Kibana (dashboards, detection rules, searches) — можно выполнить через запуск контейнера `elk-updater`:
```
docker run -it --rm -e ELASTIC_AUTH_USER='admin' -e ELASTIC_AUTH_PW='password' -e KIBANA_SERVER='https://xxx.rw.mdb.yandexcloud.net' --name elk-updater cr.yandex/sol/elk-updater:latest
```
## Развертывание с помощью Terraform
#### Описание
#### Пререквизиты
- :white_check_mark: Object Storage Bucket для Audit Trails
- :white_check_mark: [Включенный сервис Audit Trails](https://cloud.yandex.ru/docs/audit-trails/quickstart) в UI
- :white_check_mark: Сеть VPC
- :white_check_mark: Подсети в 3-х зонах доступности
- :white_check_mark: Наличие доступа в интернет с COI Instance для скачивания образа контейнера
- :white_check_mark: ServiceAccount с ролью *storage.editor* для действий в Object Storage
См. Пример конфигурации пререквизитов и вызова модулей в [/example/main.tf](./terraform/example)
##
Решение состоит из 2-х модулей Terraform [/terraform/modules/](./terraform/modules) :
1) yc-managed-elk:
- создает cluster [Yandex Managed Service for Elasticsearch](https://cloud.yandex.ru/services/managed-elasticsearch)
- с тремя нодами (по одной на каждую зону доступности)
- с лицензией Gold
- характеристики: s2-medium (8 vCPU, 32Gb Memory)
- HDD: 1TB
- назначает пароль на аккаунт admin в ELK
2) yc-elastic-trail:
- создает static keys для sa (для работы с объектами JSON в бакете и шифрования/расшифрования секретов)
- создает ВМ COI со спецификацией Docker Container со скриптом
- создает ssh пару ключей и сохраняет приватную часть на диск, публичную в ВМ
- создает KMS ключ
- назначает права kms.keys.encrypterDecrypter на ключ для sa для шифрование секретов
- шифрует секреты и передает их в Docker Container
#### Пример вызова модулей:
```Python
module "yc-managed-elk" {
source = "../modules/yc-managed-elk" # path to module yc-managed-elk
folder_id = var.folder_id
subnet_ids = yandex_vpc_subnet.elk-subnet[*].id # subnets в 3-х зонах доступности для развертывания ELK
network_id = yandex_vpc_network.vpc-elk.id # network id в которой будет развернут ELK
elk_edition = "gold"
elk_datanode_preset = "s2.medium"
elk_datanode_disk_size = 1000
elk_public_ip = false # true, если нужен публичный доступ к ElasticSearch
}
module "yc-elastic-trail" {
source = "../modules/yc-elastic-trail/" # path to module yc-elastic-trail
folder_id = var.folder_id
elk_credentials = module.yc-managed-elk.elk-pass
elk_address = module.yc-managed-elk.elk_fqdn
bucket_name = yandex_storage_bucket.trail-bucket.bucket
bucket_folder = "" # указать название префикса куда trails пишет логи в бакет, например "prefix-trails", если в корень то оставить по умолчанию пустым
sa_id = yandex_iam_service_account.sa-bucket-editor.id
coi_subnet_id = yandex_vpc_subnet.elk-subnet[0].id
}
output "elk-pass" {
value = module.yc-managed-elk.elk-pass
sensitive = true
} // Чтобы посмотреть пароль ELK: terraform output elk-pass
output "elk_fqdn" {
value = module.yc-managed-elk.elk_fqdn
} // Выводит адрес ELK на который можно обращаться, например через браузер
output "elk-user" {
value = "admin"
}
```
## Развертывание решения для поставки логов k8s:
[Развертывание решения для поставки логов k8s](../export-auditlogs-to-ELK_k8s)
## Рекомендации по настройке retention, rollover и snapshots:
[Рекомендации по настройке retention, rollover и snapshots](./CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/curl_play with elk.sh
================================================
Описание всего:>>>
Описание разовой загрузки объектов данных в ELK (bash скрипт либо питон) >>>
Создаем сам индекс
curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X PUT "https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net:9200/audit-trails-index/?pretty" -H 'Content-Type: application/json' -d @/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/mapping6.json
загрузка ingest pipeline curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X PUT "https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net:9200/_ingest/pipeline/audit-trails-pipeline?pretty" -H 'Content-Type: application/json' -d @/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/pipeline3.json
import kibana index pattern с нужным нашим id
curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/saved_objects/_import --form file=@/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/kibana_index_pattern.ndjson -H 'kbn-xsrf: true'
загрузка filters curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/saved_objects/_import --form file=@/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/filters.ndjson -H 'kbn-xsrf: true'
загрузка search curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/saved_objects/_import --form file=@/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/kibana_search2.ndjson -H 'kbn-xsrf: true'
загрузка dashboards curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/saved_objects/_import --form file=@/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/dashboard_very_new.ndjson -H 'kbn-xsrf: true'
Файл json необходимо преобразовать перед загрузкой в качестве bulk в elk
jq -c -r ".[]" /Users/mirtov8/Documents/CloudTrail/ArcSight\ Connector/gg/155732665.json | while read line; do echo '{"index":{}}'; echo $line; done > bulk.json
python пример ( пример - https://gist.github.com/icamys/4287ae49d20ff2add3db86e2b2053977#file-elastic_import_data_bulk-py-L51 )
Отправка bulk
curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST "https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net:9200/audit-trails-index/_bulk?pipeline=audit-trails-pipeline" -H 'Content-Type: application/json' --data-binary "@./bulk3.json"
python пример ( https://elasticsearch-py.readthedocs.io/en/master/helpers.html ) (https://gist.github.com/icamys/4287ae49d20ff2add3db86e2b2053977#file-elastic_import_data_bulk-py-L51)
загрузка detections curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/detection_engine/rules/_import --form file=@./detections.ndjson -H 'kbn-xsrf: true'
______
k8s
curl --user beat:beat123 --cacert ~/.elasticsearch/root.crt -X GET "https://c-c9qps9eabd0ok4haehjq.rw.mdb.yandexcloud.net:9200/k8s-index?pretty"
curl --user beat:beat123 --cacert ~/.elasticsearch/root.crt -X PUT "https://c-c9qps9eabd0ok4haehjq.rw.mdb.yandexcloud.net:9200/k8s-index/?pretty" -H 'Content-Type: application/json' -d @//Users/mirtov8/Documents/GitHub/yc-solution-library-for-security/auditlogs/export-auditlogs-to-ELK/include/k8s/mapping_k8s.json
curl --user beat:beat123 --cacert ~/.elasticsearch/root.crt -X POST "https://c-c9qps9eabd0ok4haehjq.rw.mdb.yandexcloud.net:9200/k8s-index/_bulk?pipeline=k8s_audit-pipeline" -H 'Content-Type: application/json' --data-binary "@./bulk2.json"
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/kms_decrypt_cmds.sh
================================================
Получить токен:
TOKEN=$(curl -H Metadata-Flavor:Google 169.254.169.254/computeMetadata/v1/instance/service-accounts/default/token | jq -r '.access_token')
Зашифровать данные
curl -vX POST https://kms.yandex/kms/v1/keys/abjulftcuh1p66lfdmpg:encrypt -d '{"versionId": "abj24us9a9gl3d28f8kt","plaintext": "password"}' --header "Accept: application/json" --header "Authorization: Bearer ${TOKEN}"
Расшифровать данные
curl -X POST https://kms.yandex/kms/v1/keys/abjulftcuh1p66lfdmpg:decrypt -d '{"ciphertext": "AAAAAQAAABRhYmoyNHVzOWE5Z2wzZDI4ZjhrdAAAABCs8pwmY0EXt4Z93jl2bXyKAAAADNsHbqFdoUZZG6hx38ES7Jal90aYsxU1VZUPP3309i1/Bf4="}' --header "Accept: application/json" --header "Authorization: Bearer ${TOKEN}" | jq '.plaintext' | sed 's/"//g'
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/last_backup/falco_pipeline_backup.json
================================================
{
"description": "k8s pipeline",
"processors": [
{
"set": {
"field": "event.kind",
"value": "event",
"ignore_failure": true
}
},
{
"set": {
"field": "event.category",
"value": ["configuration", "iam"],
"ignore_failure": true
}
},
{
"set": {
"field": "event.dataset",
"value": "yandexcloud.k8s_falco",
"ignore_failure": true
}
},
{
"set": {
"field": "cloud.provider",
"value": "yandexcloud",
"ignore_failure": true
}
},
{
"set": {
"field": "@timestamp",
"value": "{{{time}}}",
"ignore_failure": true
}
},
{
"set": {
"field": "cloud.service.name",
"value": "falco",
"ignore_failure": true
}
}
]
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/last_backup/k8s-mapping-ba.json
================================================
{
"settings" : {
"number_of_replicas" : 2
},
"mappings": {
"properties": {
"source" : {
"properties" : {
"address" : {
"type" : "text",
"fields" : {
"keyword" : {
"type" : "keyword",
"ignore_above" : 256
}
}
},
"ip" : {
"type" : "ip"
}
}
},
"sourceIPs" : {
"type" : "ip"
},
"@timestamp": {
"type": "date"
},
"geoip.location": {
"type": "geo_point"
}
}
}
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/last_backup/k8s_audit_dashboard-back.ndjson
================================================
{"attributes":{"description":"","hits":0,"kibanaSavedObjectMeta":{"searchSourceJSON":"{\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filter\":[]}"},"optionsJSON":"{\"hidePanelTitles\":false,\"useMargins\":true}","panelsJSON":"[{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":0,\"w\":24,\"h\":6,\"i\":\"df4da863-2133-4560-82f3-5c126ac27f14\"},\"panelIndex\":\"df4da863-2133-4560-82f3-5c126ac27f14\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1628927100713\",\"fieldName\":\"cluster_id.keyword\",\"parent\":\"\",\"label\":\"k8s-cluster_id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_df4da863-2133-4560-82f3-5c126ac27f14_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Cluster filter\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":24,\"y\":0,\"w\":24,\"h\":6,\"i\":\"58adfaa4-02bd-4b64-89cc-395d6ee0f968\"},\"panelIndex\":\"58adfaa4-02bd-4b64-89cc-395d6ee0f968\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1628927314788\",\"fieldName\":\"cloud_id.keyword\",\"parent\":\"\",\"label\":\"k8s-cloud-id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_58adfaa4-02bd-4b64-89cc-395d6ee0f968_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Cloud filter\"},{\"version\":\"7.13.4\",\"type\":\"map\",\"gridData\":{\"x\":0,\"y\":6,\"w\":24,\"h\":15,\"i\":\"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2\"},\"panelIndex\":\"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"description\":\"\",\"layerListJSON\":\"[{\\\"sourceDescriptor\\\":{\\\"type\\\":\\\"EMS_TMS\\\",\\\"isAutoSelect\\\":true},\\\"id\\\":\\\"99115329-feb3-42c6-b426-dff8bd1e1b3a\\\",\\\"label\\\":null,\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":1,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"TILE\\\"},\\\"type\\\":\\\"VECTOR_TILE\\\"},{\\\"sourceDescriptor\\\":{\\\"indexPatternId\\\":\\\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\\\",\\\"geoField\\\":\\\"geoip.location\\\",\\\"filterByMapBounds\\\":true,\\\"scalingType\\\":\\\"CLUSTERS\\\",\\\"id\\\":\\\"5728ef62-6dc0-4b27-b048-7ffda088d201\\\",\\\"type\\\":\\\"ES_SEARCH\\\",\\\"applyGlobalQuery\\\":true,\\\"applyGlobalTime\\\":true,\\\"tooltipProperties\\\":[],\\\"sortField\\\":\\\"\\\",\\\"sortOrder\\\":\\\"desc\\\",\\\"topHitsSplitField\\\":\\\"\\\",\\\"topHitsSize\\\":1},\\\"id\\\":\\\"04fbaa00-b4ba-40db-b46e-8a6dd6d12d04\\\",\\\"label\\\":\\\"success-connect-from-ip\\\",\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":0.91,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"VECTOR\\\",\\\"properties\\\":{\\\"icon\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"value\\\":\\\"marker\\\"}},\\\"fillColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#54B399\\\"}},\\\"lineColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#41937c\\\"}},\\\"lineWidth\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":1}},\\\"iconSize\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":6}},\\\"iconOrientation\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"orientation\\\":0}},\\\"labelText\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"value\\\":\\\"\\\"}},\\\"labelColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#000000\\\"}},\\\"labelSize\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":14}},\\\"labelBorderColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#FFFFFF\\\"}},\\\"symbolizeAs\\\":{\\\"options\\\":{\\\"value\\\":\\\"circle\\\"}},\\\"labelBorderSize\\\":{\\\"options\\\":{\\\"size\\\":\\\"SMALL\\\"}}},\\\"isTimeAware\\\":true},\\\"type\\\":\\\"BLENDED_VECTOR\\\",\\\"joins\\\":[],\\\"query\\\":{\\\"query\\\":\\\"not responseStatus.status : Failure\\\",\\\"language\\\":\\\"kuery\\\"}}]\",\"mapStateJSON\":\"{\\\"zoom\\\":1.41,\\\"center\\\":{\\\"lon\\\":64.80962,\\\"lat\\\":57.04692},\\\"timeFilters\\\":{\\\"from\\\":\\\"now-15d\\\",\\\"to\\\":\\\"now\\\"},\\\"refreshConfig\\\":{\\\"isPaused\\\":true,\\\"interval\\\":0},\\\"query\\\":{\\\"query\\\":\\\"event.dataset : yandexcloud.k8s_audit_logs and source.ip : * and not responseStatus.status : Failure\\\",\\\"language\\\":\\\"kuery\\\"},\\\"filters\\\":[],\\\"settings\\\":{\\\"autoFitToDataBounds\\\":false,\\\"backgroundColor\\\":\\\"#ffffff\\\",\\\"disableInteractive\\\":false,\\\"disableTooltipControl\\\":false,\\\"hideToolbarOverlay\\\":false,\\\"hideLayerControl\\\":false,\\\"hideViewControl\\\":false,\\\"initialLocation\\\":\\\"LAST_SAVED_LOCATION\\\",\\\"fixedLocation\\\":{\\\"lat\\\":0,\\\"lon\\\":0,\\\"zoom\\\":2},\\\"browserLocation\\\":{\\\"zoom\\\":2},\\\"maxZoom\\\":24,\\\"minZoom\\\":0,\\\"showScaleControl\\\":false,\\\"showSpatialFilters\\\":true,\\\"spatialFiltersAlpa\\\":0.3,\\\"spatialFiltersFillColor\\\":\\\"#DA8B45\\\",\\\"spatialFiltersLineColor\\\":\\\"#DA8B45\\\"}}\",\"uiStateJSON\":\"{\\\"isLayerTOCOpen\\\":true,\\\"openTOCDetails\\\":[]}\"},\"mapCenter\":{\"lat\":57.21062,\"lon\":78.63166,\"zoom\":1.41},\"mapBuffer\":{\"minLon\":-141.24608,\"minLat\":-9.879624999999994,\"maxLon\":298.50939999999997,\"maxLat\":104.90343499999999},\"isLayerTOCOpen\":false,\"openTOCDetails\":[],\"hiddenLayers\":[],\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"Connect from ip\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":6,\"w\":24,\"h\":15,\"i\":\"913c8496-3a96-4fa5-b029-20b53d929446\"},\"panelIndex\":\"913c8496-3a96-4fa5-b029-20b53d929446\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"201765c7-9d49-4931-954d-047211d60c67\":{\"columns\":{\"cb3cdcfa-2372-4b24-a37d-b7594d6ac42f\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"485e13ff-3e64-4c34-ac75-e421aa3cc191\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"485e13ff-3e64-4c34-ac75-e421aa3cc191\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"},\"2cdf7d8d-6a13-4283-a596-68e7230c6bad\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"485e13ff-3e64-4c34-ac75-e421aa3cc191\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}}},\"columnOrder\":[\"cb3cdcfa-2372-4b24-a37d-b7594d6ac42f\",\"2cdf7d8d-6a13-4283-a596-68e7230c6bad\",\"485e13ff-3e64-4c34-ac75-e421aa3cc191\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_horizontal\",\"layers\":[{\"layerId\":\"201765c7-9d49-4931-954d-047211d60c67\",\"seriesType\":\"bar_horizontal\",\"xAccessor\":\"2cdf7d8d-6a13-4283-a596-68e7230c6bad\",\"splitAccessor\":\"cb3cdcfa-2372-4b24-a37d-b7594d6ac42f\",\"accessors\":[\"485e13ff-3e64-4c34-ac75-e421aa3cc191\"]}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-201765c7-9d49-4931-954d-047211d60c67\"}]},\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"OPA-gatekeeper-detections(only enforce)\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":21,\"w\":13,\"h\":9,\"i\":\"bb843cd6-969c-4aae-a37c-978d2fe0bbef\"},\"panelIndex\":\"bb843cd6-969c-4aae-a37c-978d2fe0bbef\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"d401535b-665e-442b-a312-9edd3c1ebcc0\":{\"columns\":{\"61acda83-5d64-453e-9ca1-16b129cc2b42\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"fac0953d-82d6-4ef6-955a-8bc79bccf002\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"ece5248d-0578-44e8-b245-bc2de86f37f4\":{\"label\":\"Top values of verb.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"verb.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"fac0953d-82d6-4ef6-955a-8bc79bccf002\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"fac0953d-82d6-4ef6-955a-8bc79bccf002\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"61acda83-5d64-453e-9ca1-16b129cc2b42\",\"ece5248d-0578-44e8-b245-bc2de86f37f4\",\"fac0953d-82d6-4ef6-955a-8bc79bccf002\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\",\"showSingleSeries\":false},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_horizontal_stacked\",\"layers\":[{\"palette\":{\"type\":\"palette\",\"name\":\"default\"},\"layerId\":\"d401535b-665e-442b-a312-9edd3c1ebcc0\",\"seriesType\":\"bar_horizontal_stacked\",\"xAccessor\":\"ece5248d-0578-44e8-b245-bc2de86f37f4\",\"splitAccessor\":\"61acda83-5d64-453e-9ca1-16b129cc2b42\",\"accessors\":[\"fac0953d-82d6-4ef6-955a-8bc79bccf002\"]}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseStatus.reason : Forbidden and not user.name : (system*node* or *gatekeeper* or *kyverno* or *proxy* or *scheduler* or *anonymous* or *csi* or *controller*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-d401535b-665e-442b-a312-9edd3c1ebcc0\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Unauthorized events\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":13,\"y\":21,\"w\":11,\"h\":9,\"i\":\"4d0ab419-47d3-48bd-9e5e-93a563e20aee\"},\"panelIndex\":\"4d0ab419-47d3-48bd-9e5e-93a563e20aee\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"b5bee140-5f01-4de3-9395-d279acb203dc\":{\"columns\":{\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"4eda6d99-05c3-4ab8-a294-4632c9442157\":{\"label\":\"Top values of requestObject.kind.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"requestObject.kind.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\",\"4eda6d99-05c3-4ab8-a294-4632c9442157\",\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":false,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"layerId\":\"b5bee140-5f01-4de3-9395-d279acb203dc\",\"accessors\":[\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"],\"position\":\"top\",\"seriesType\":\"bar_stacked\",\"showGridlines\":false,\"xAccessor\":\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\",\"splitAccessor\":\"4eda6d99-05c3-4ab8-a294-4632c9442157\"}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and requestObject.roleRef.name.keyword:(cluster-admin or admin) and objectRef.resource.keyword: (clusterrolebindings or rolebinding) and verb : create and not responseObject.reason : AlreadyExists\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-b5bee140-5f01-4de3-9395-d279acb203dc\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Assign Cluster-admin/admin\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":21,\"w\":13,\"h\":17,\"i\":\"bbfefc52-8578-4755-84b5-1f18783f51d4\"},\"panelIndex\":\"bbfefc52-8578-4755-84b5-1f18783f51d4\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"fd0565e3-d5dd-490a-bd9d-2c0cd901a5c3\":{\"columns\":{\"80c15f05-a37b-4c19-a89b-0be5c9847ae0\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"},\"4a5a33db-17c3-4477-a71d-05620894f6f9\":{\"label\":\"Top values of folder_id.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"folder_id.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"80c15f05-a37b-4c19-a89b-0be5c9847ae0\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}}},\"columnOrder\":[\"4a5a33db-17c3-4477-a71d-05620894f6f9\",\"80c15f05-a37b-4c19-a89b-0be5c9847ae0\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"fd0565e3-d5dd-490a-bd9d-2c0cd901a5c3\",\"groups\":[\"4a5a33db-17c3-4477-a71d-05620894f6f9\",\"4a5a33db-17c3-4477-a71d-05620894f6f9\",\"4a5a33db-17c3-4477-a71d-05620894f6f9\",\"4a5a33db-17c3-4477-a71d-05620894f6f9\"],\"metric\":\"80c15f05-a37b-4c19-a89b-0be5c9847ae0\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2,\"legendPosition\":\"right\"}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-fd0565e3-d5dd-490a-bd9d-2c0cd901a5c3\"}]},\"enhancements\":{\"dynamicActions\":{\"events\":[{\"eventId\":\"e254cc8a-f8d7-45b5-8f64-d2f448a0af10\",\"triggers\":[\"VALUE_CLICK_TRIGGER\"],\"action\":{\"factoryId\":\"URL_DRILLDOWN\",\"name\":\"Look at yandex-cloud console\",\"config\":{\"url\":{\"template\":\"https://console.cloud.yandex.ru/folders/{{event.value}}\"},\"openInNewTab\":true,\"encodeUrl\":true}}}]}},\"hidePanelTitles\":false},\"title\":\"OPA-detections by Folder_id\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":37,\"y\":21,\"w\":5,\"h\":9,\"i\":\"e1d27ba4-c45c-431e-933b-0a174c71d48c\"},\"panelIndex\":\"e1d27ba4-c45c-431e-933b-0a174c71d48c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"metric\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"type\":\"metric\",\"metric\":{\"percentageMode\":false,\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"metricColorMode\":\"Labels\",\"colorsRange\":[{\"from\":0,\"to\":1},{\"from\":1,\"to\":100000}],\"labels\":{\"show\":true},\"invertColors\":false,\"style\":{\"bgFill\":\"#000\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":76}}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"OPA-Gatekeeper-Detections\"},\"schema\":\"metric\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":42,\"y\":21,\"w\":6,\"h\":9,\"i\":\"93384633-a71f-4441-8beb-cbb5cab7c514\"},\"panelIndex\":\"93384633-a71f-4441-8beb-cbb5cab7c514\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"goal\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"isDisplayWarning\":true,\"type\":\"gauge\",\"gauge\":{\"verticalSplit\":false,\"autoExtend\":false,\"percentageMode\":false,\"gaugeType\":\"Arc\",\"gaugeStyle\":\"Full\",\"backStyle\":\"Full\",\"orientation\":\"vertical\",\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"gaugeColorMode\":\"None\",\"colorsRange\":[{\"from\":0,\"to\":1}],\"invertColors\":false,\"labels\":{\"show\":false,\"color\":\"black\"},\"scale\":{\"show\":false,\"labels\":false,\"color\":\"rgba(105,112,125,0.2)\",\"width\":2},\"type\":\"meter\",\"style\":{\"bgFill\":\"rgba(105,112,125,0.2)\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":60}}},\"uiState\":{\"vis\":{\"defaultColors\":{\"0 - 1\":\"rgb(0,104,55)\"}}},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Delete-OPA-Gatekeeper \"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"verb.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"group\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.name.keyword: gatekeeper-validating-webhook-configuration and verb : delete\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":30,\"w\":17,\"h\":8,\"i\":\"9e45767a-451f-48a1-b421-17738c299cd9\"},\"panelIndex\":\"9e45767a-451f-48a1-b421-17738c299cd9\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"pie\",\"params\":{\"type\":\"pie\",\"addTooltip\":true,\"addLegend\":true,\"legendPosition\":\"left\",\"isDonut\":true,\"labels\":{\"show\":true,\"values\":false,\"last_level\":true,\"truncate\":100}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"NetworkPolicy:create/delete/update\"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"responseObject.metadata.selfLink.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"segment\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and requestObject.kind.keyword: (NetworkPolicy or CiliumNetworkPolicy) and verb : (create or update or delete)\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"NetworkPolicy:create/delete/update\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":17,\"y\":30,\"w\":7,\"h\":8,\"i\":\"398a8ba3-0ffc-40ee-90e1-c1547938d171\"},\"panelIndex\":\"398a8ba3-0ffc-40ee-90e1-c1547938d171\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"c76f346d-f6d6-4f9e-acb8-f5dde656e783\":{\"columns\":{\"b659aca0-0f1f-4408-8cea-1eea232bfe93\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"b659aca0-0f1f-4408-8cea-1eea232bfe93\",\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"c76f346d-f6d6-4f9e-acb8-f5dde656e783\",\"groups\":[\"b659aca0-0f1f-4408-8cea-1eea232bfe93\"],\"metric\":\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"default\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.namespace.keyword: kube-system and verb : create and objectRef.resource.keyword: pods and objectRef.name : * and not objectRef.name : (*calico* or *dns* or *npd* or *proxy* or *metrics* or *csi* or *masq*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-c76f346d-f6d6-4f9e-acb8-f5dde656e783\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Create pod in kube-system\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":37,\"y\":30,\"w\":11,\"h\":8,\"i\":\"ad54fa9e-40c4-4c74-85c2-543efeef1004\"},\"panelIndex\":\"ad54fa9e-40c4-4c74-85c2-543efeef1004\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"07f20f17-d0d3-4d63-b030-7980f218c412\":{\"columns\":{\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\":{\"label\":\"Top values of objectRef.resource.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.resource.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\",\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"palette\":{\"type\":\"palette\",\"name\":\"negative\"},\"layers\":[{\"layerId\":\"07f20f17-d0d3-4d63-b030-7980f218c412\",\"groups\":[\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\"],\"metric\":\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.apiGroup.keyword: constraints.gatekeeper.sh and (verb : delete or update) and not user.name : \\\"system:serviceaccount:gatekeeper-system:gatekeeper-admin\\\"\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-07f20f17-d0d3-4d63-b030-7980f218c412\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"OPA-constraint-delete/update\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":38,\"w\":17,\"h\":7,\"i\":\"7a0555be-d5f3-4aeb-9159-f48d7264d40c\"},\"panelIndex\":\"7a0555be-d5f3-4aeb-9159-f48d7264d40c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"pie\",\"params\":{\"type\":\"pie\",\"addTooltip\":true,\"addLegend\":true,\"legendPosition\":\"left\",\"isDonut\":true,\"labels\":{\"show\":true,\"values\":false,\"last_level\":true,\"truncate\":100}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Exec to container\"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"objectRef.name.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"segment\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.subresource.keyword: exec\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{},\"vis\":{\"legendOpen\":true}},\"title\":\"Exec to container\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":17,\"y\":38,\"w\":16,\"h\":7,\"i\":\"b6d054cd-bca1-49a6-affb-7b115b76af5a\"},\"panelIndex\":\"b6d054cd-bca1-49a6-affb-7b115b76af5a\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsDatatable\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"18ea127c-2267-4d24-9893-d3ef85942514\":{\"columns\":{\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\":{\"label\":\"Unique count of user.name.keyword\",\"dataType\":\"number\",\"operationType\":\"unique_count\",\"scale\":\"ratio\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":false},\"c94a437d-970d-4c55-89a7-499d47032bc8\":{\"label\":\"ServiceAccounts\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":15,\"orderBy\":{\"type\":\"column\",\"columnId\":\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false},\"customLabel\":true}},\"columnOrder\":[\"c94a437d-970d-4c55-89a7-499d47032bc8\",\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"layerId\":\"18ea127c-2267-4d24-9893-d3ef85942514\",\"columns\":[{\"isTransposed\":false,\"columnId\":\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\",\"hidden\":true},{\"columnId\":\"c94a437d-970d-4c55-89a7-499d47032bc8\",\"isTransposed\":false,\"alignment\":\"left\"}]},\"query\":{\"query\":\"user.name : *serviceaccount*\",\"language\":\"kuery\"},\"filters\":[{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:certificate-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-0\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:certificate-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:coredns\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-1\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:coredns\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:cronjob-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-2\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:cronjob-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:generic-garbage-collector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-3\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:generic-garbage-collector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:job-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-4\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:job-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:endpointslice-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-5\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:endpointslice-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:endpoint-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-6\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:endpoint-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:calico-node\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-7\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:calico-node\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:kube-proxy\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-8\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:kube-proxy\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"alias\":null,\"negate\":true,\"disabled\":false,\"type\":\"phrase\",\"key\":\"objectRef.namespace\",\"params\":{\"query\":\"kube-system\"},\"indexRefName\":\"filter-index-pattern-9\"},\"query\":{\"match_phrase\":{\"objectRef.namespace\":\"kube-system\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:kube-dns-autoscaler\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-10\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:kube-dns-autoscaler\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:daemon-set-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-11\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:daemon-set-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:metrics-server\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-12\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:metrics-server\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:pod-garbage-collector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-13\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:pod-garbage-collector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:node-problem-detector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-14\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:node-problem-detector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:typha-cpha\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-15\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:typha-cpha\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:service-account-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-16\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:service-account-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:resourcequota-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-17\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:resourcequota-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:replicaset-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-18\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:replicaset-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:namespace-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-19\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:namespace-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:typha-cpva\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-20\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:typha-cpva\"}},\"$state\":{\"store\":\"appState\"}}]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-18ea127c-2267-4d24-9893-d3ef85942514\"},{\"name\":\"filter-index-pattern-0\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-1\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-2\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-3\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-4\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-5\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-6\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-7\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-8\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-9\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-10\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-11\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-12\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-13\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-14\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-15\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-16\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-17\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-18\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-19\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-20\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"}]},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":33,\"y\":38,\"w\":15,\"h\":7,\"i\":\"1d2c60a9-c570-45b0-8f49-e577c74e9ce3\"},\"panelIndex\":\"1d2c60a9-c570-45b0-8f49-e577c74e9ce3\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsDatatable\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"8e37793f-a2a3-48b0-a4b5-dda752e958b9\":{\"columns\":{\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\":{\"label\":\"YC Admins\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false},\"customLabel\":true},\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\",\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"columns\":[{\"isTransposed\":false,\"columnId\":\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\"},{\"isTransposed\":false,\"columnId\":\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\",\"hidden\":true}],\"layerId\":\"8e37793f-a2a3-48b0-a4b5-dda752e958b9\"},\"query\":{\"query\":\"user.groups.keyword: *admin*\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-8e37793f-a2a3-48b0-a4b5-dda752e958b9\"}]},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":45,\"w\":17,\"h\":11,\"i\":\"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb\"},\"panelIndex\":\"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\":{\"columns\":{\"71c8af00-7864-4ca6-a20d-0e43a80da354\":{\"label\":\"Top values of requestObject.status.containerStatuses.image.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"requestObject.status.containerStatuses.image.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"71c8af00-7864-4ca6-a20d-0e43a80da354\",\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\",\"groups\":[\"71c8af00-7864-4ca6-a20d-0e43a80da354\"],\"metric\":\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and not requestObject.status.containerStatuses.image.keyword: *cr.yandex/* and requestObject.status.containerStatuses.containerID : *docker* and verb : patch and not requestObject.status.containerStatuses.image.keyword: (*falco* or *openpolicyagent* or *kyverno* or *k8s.gcr.io*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Images not from YC CR\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":17,\"y\":45,\"w\":16,\"h\":11,\"i\":\"611221c8-59e6-4ea2-bfdb-bbb53f646772\"},\"panelIndex\":\"611221c8-59e6-4ea2-bfdb-bbb53f646772\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"d7984002-15d6-4e61-b30e-d34bc0a066ea\":{\"columns\":{\"0c0b50e4-e53e-4ef3-a0d2-ee5cc416762f\":{\"label\":\"Top values of objectRef.namespace.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.namespace.keyword\",\"isBucketed\":true,\"params\":{\"size\":10,\"orderBy\":{\"type\":\"column\",\"columnId\":\"3b8ab08b-e01f-407b-976f-4f073207dde4\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"3b8ab08b-e01f-407b-976f-4f073207dde4\":{\"label\":\"Unique count of objectRef.namespace.keyword\",\"dataType\":\"number\",\"operationType\":\"unique_count\",\"scale\":\"ratio\",\"sourceField\":\"objectRef.namespace.keyword\",\"isBucketed\":false}},\"columnOrder\":[\"0c0b50e4-e53e-4ef3-a0d2-ee5cc416762f\",\"3b8ab08b-e01f-407b-976f-4f073207dde4\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"palette\":{\"type\":\"palette\",\"name\":\"cool\"},\"layers\":[{\"layerId\":\"d7984002-15d6-4e61-b30e-d34bc0a066ea\",\"groups\":[\"0c0b50e4-e53e-4ef3-a0d2-ee5cc416762f\",\"0c0b50e4-e53e-4ef3-a0d2-ee5cc416762f\"],\"metric\":\"3b8ab08b-e01f-407b-976f-4f073207dde4\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"default\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-d7984002-15d6-4e61-b30e-d34bc0a066ea\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Namespaces\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":33,\"y\":45,\"w\":15,\"h\":11,\"i\":\"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c\"},\"panelIndex\":\"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"b770c4de-625b-4d6b-9cd2-caf7372d5d6a\":{\"columns\":{\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\":{\"label\":\"Top values of event.dataset.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"event.dataset.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"8a74805c-8582-46c0-8d53-920a919f9b59\":{\"label\":\"stageTimestamp\",\"dataType\":\"date\",\"operationType\":\"date_histogram\",\"sourceField\":\"stageTimestamp\",\"isBucketed\":true,\"scale\":\"interval\",\"params\":{\"interval\":\"auto\"}},\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\",\"8a74805c-8582-46c0-8d53-920a919f9b59\",\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"top\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"layerId\":\"b770c4de-625b-4d6b-9cd2-caf7372d5d6a\",\"accessors\":[\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"],\"position\":\"top\",\"seriesType\":\"bar_stacked\",\"showGridlines\":false,\"xAccessor\":\"8a74805c-8582-46c0-8d53-920a919f9b59\",\"palette\":{\"type\":\"palette\",\"name\":\"temperature\"},\"splitAccessor\":\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\"}]},\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-b770c4de-625b-4d6b-9cd2-caf7372d5d6a\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Events-by-time\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":56,\"w\":48,\"h\":12,\"i\":\"46f514cc-dac0-4727-9416-ea72ea7a7ed6\"},\"panelIndex\":\"46f514cc-dac0-4727-9416-ea72ea7a7ed6\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"f30699c9-d583-4db7-a489-b1e1ff2b86fe\":{\"columns\":{\"0ebea67a-d401-40b8-8e82-535c4849014e\":{\"label\":\"Top values of rule.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"rule.keyword\",\"isBucketed\":true,\"params\":{\"size\":15,\"orderBy\":{\"type\":\"column\",\"columnId\":\"a51a05c8-5849-473d-b77c-2fb8eb4cc331\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"a51a05c8-5849-473d-b77c-2fb8eb4cc331\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"0ebea67a-d401-40b8-8e82-535c4849014e\",\"a51a05c8-5849-473d-b77c-2fb8eb4cc331\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"f30699c9-d583-4db7-a489-b1e1ff2b86fe\",\"groups\":[\"0ebea67a-d401-40b8-8e82-535c4849014e\"],\"metric\":\"a51a05c8-5849-473d-b77c-2fb8eb4cc331\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_falco\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"4c290ba0-fdad-11eb-b912-d99e9986f72b\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"4c290ba0-fdad-11eb-b912-d99e9986f72b\",\"name\":\"indexpattern-datasource-layer-f30699c9-d583-4db7-a489-b1e1ff2b86fe\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Falco alerts\"},{\"version\":\"7.13.4\",\"type\":\"search\",\"gridData\":{\"x\":0,\"y\":68,\"w\":48,\"h\":17,\"i\":\"ed79a50e-9a59-475a-8e0c-d41b0cb84acd\"},\"panelIndex\":\"ed79a50e-9a59-475a-8e0c-d41b0cb84acd\",\"embeddableConfig\":{\"enhancements\":{}},\"panelRefName\":\"panel_ed79a50e-9a59-475a-8e0c-d41b0cb84acd\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":25,\"y\":85,\"w\":23,\"h\":9,\"i\":\"0492dbd1-815d-46f2-82b9-1917fddcd8a7\"},\"panelIndex\":\"0492dbd1-815d-46f2-82b9-1917fddcd8a7\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"889ef61e-c27c-49b4-97b5-0bcad36eb8c3\":{\"columns\":{\"6f154ebc-1387-4dd2-a440-5760b39ee994\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"8d5794d3-a850-4779-b32f-3dc2edfa855a\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"93aed031-2523-40b2-a8ae-ec6fe6b06c8f\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"8d5794d3-a850-4779-b32f-3dc2edfa855a\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"8d5794d3-a850-4779-b32f-3dc2edfa855a\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"6f154ebc-1387-4dd2-a440-5760b39ee994\",\"93aed031-2523-40b2-a8ae-ec6fe6b06c8f\",\"8d5794d3-a850-4779-b32f-3dc2edfa855a\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_horizontal\",\"layers\":[{\"layerId\":\"889ef61e-c27c-49b4-97b5-0bcad36eb8c3\",\"accessors\":[\"8d5794d3-a850-4779-b32f-3dc2edfa855a\"],\"position\":\"top\",\"seriesType\":\"bar_horizontal\",\"showGridlines\":false,\"xAccessor\":\"6f154ebc-1387-4dd2-a440-5760b39ee994\",\"splitAccessor\":\"93aed031-2523-40b2-a8ae-ec6fe6b06c8f\"}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validate.kyverno.svc\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-889ef61e-c27c-49b4-97b5-0bcad36eb8c3\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"kyverno-detections(only enforce)\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":25,\"y\":94,\"w\":12,\"h\":10,\"i\":\"c0743ff5-8470-469a-86cf-5d33d45deb34\"},\"panelIndex\":\"c0743ff5-8470-469a-86cf-5d33d45deb34\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"411026a7-eff6-47fa-9e93-bff4143c7544\":{\"columns\":{\"2858fd65-2d0f-4550-8c3c-52fdbc2209fe\":{\"label\":\"Top values of cluster_id.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"cluster_id.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"b448e6ad-2ac4-459a-a76f-a505f6c9fbe3\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"b448e6ad-2ac4-459a-a76f-a505f6c9fbe3\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"2858fd65-2d0f-4550-8c3c-52fdbc2209fe\",\"b448e6ad-2ac4-459a-a76f-a505f6c9fbe3\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"411026a7-eff6-47fa-9e93-bff4143c7544\",\"groups\":[\"2858fd65-2d0f-4550-8c3c-52fdbc2209fe\"],\"metric\":\"b448e6ad-2ac4-459a-a76f-a505f6c9fbe3\",\"numberDisplay\":\"percent\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validate.kyverno.svc\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-411026a7-eff6-47fa-9e93-bff4143c7544\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"kyverno-detections by Cluster_id\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":37,\"y\":94,\"w\":5,\"h\":10,\"i\":\"557d758a-f0b2-4d4f-aebd-a32f8cf70b9c\"},\"panelIndex\":\"557d758a-f0b2-4d4f-aebd-a32f8cf70b9c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"metric\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"type\":\"metric\",\"metric\":{\"percentageMode\":false,\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"metricColorMode\":\"Labels\",\"colorsRange\":[{\"from\":0,\"to\":1},{\"from\":1,\"to\":100000}],\"labels\":{\"show\":true},\"invertColors\":false,\"style\":{\"bgFill\":\"#000\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":76}}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Kyverno-Detections\"},\"schema\":\"metric\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validate.kyverno.svc\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":42,\"y\":94,\"w\":6,\"h\":10,\"i\":\"42a0de3a-e9c3-4f34-bf5a-82244b6cf497\"},\"panelIndex\":\"42a0de3a-e9c3-4f34-bf5a-82244b6cf497\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"goal\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"isDisplayWarning\":true,\"type\":\"gauge\",\"gauge\":{\"verticalSplit\":false,\"autoExtend\":false,\"percentageMode\":false,\"gaugeType\":\"Arc\",\"gaugeStyle\":\"Full\",\"backStyle\":\"Full\",\"orientation\":\"vertical\",\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"gaugeColorMode\":\"None\",\"colorsRange\":[{\"from\":0,\"to\":1}],\"invertColors\":false,\"labels\":{\"show\":false,\"color\":\"black\"},\"scale\":{\"show\":false,\"labels\":false,\"color\":\"rgba(105,112,125,0.2)\",\"width\":2},\"type\":\"meter\",\"style\":{\"bgFill\":\"rgba(105,112,125,0.2)\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":60}}},\"uiState\":{\"vis\":{\"defaultColors\":{\"0 - 1\":\"rgb(0,104,55)\"}}},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Delete-Kyverno\"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"verb.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"group\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.name.keyword: kyverno-resource-validating-webhook-cfg and verb : delete \",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":37,\"y\":104,\"w\":11,\"h\":8,\"i\":\"a79397e8-8420-4be0-903e-23c664992a25\"},\"panelIndex\":\"a79397e8-8420-4be0-903e-23c664992a25\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"07f20f17-d0d3-4d63-b030-7980f218c412\":{\"columns\":{\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"},\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}}},\"columnOrder\":[\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\",\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"palette\":{\"type\":\"palette\",\"name\":\"negative\"},\"layers\":[{\"layerId\":\"07f20f17-d0d3-4d63-b030-7980f218c412\",\"groups\":[\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\",\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\"],\"metric\":\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.apiGroup.keyword: kyverno.io and (verb : delete or update) and objectRef.resource.keyword: *policies\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-07f20f17-d0d3-4d63-b030-7980f218c412\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Kyverno-delete/update\"}]","timeRestore":false,"title":"k8s-dashboard-and-opa","version":1},"coreMigrationVersion":"7.13.4","id":"642ffd90-fcbc-11eb-b912-d99e9986f72b","migrationVersion":{"dashboard":"7.13.1"},"references":[{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"df4da863-2133-4560-82f3-5c126ac27f14:control_df4da863-2133-4560-82f3-5c126ac27f14_0_index_pattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"58adfaa4-02bd-4b64-89cc-395d6ee0f968:control_58adfaa4-02bd-4b64-89cc-395d6ee0f968_0_index_pattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2:layer_1_source_index_pattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"913c8496-3a96-4fa5-b029-20b53d929446:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"913c8496-3a96-4fa5-b029-20b53d929446:indexpattern-datasource-layer-201765c7-9d49-4931-954d-047211d60c67","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"bb843cd6-969c-4aae-a37c-978d2fe0bbef:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"bb843cd6-969c-4aae-a37c-978d2fe0bbef:indexpattern-datasource-layer-d401535b-665e-442b-a312-9edd3c1ebcc0","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"4d0ab419-47d3-48bd-9e5e-93a563e20aee:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"4d0ab419-47d3-48bd-9e5e-93a563e20aee:indexpattern-datasource-layer-b5bee140-5f01-4de3-9395-d279acb203dc","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"bbfefc52-8578-4755-84b5-1f18783f51d4:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"bbfefc52-8578-4755-84b5-1f18783f51d4:indexpattern-datasource-layer-fd0565e3-d5dd-490a-bd9d-2c0cd901a5c3","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"e1d27ba4-c45c-431e-933b-0a174c71d48c:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"93384633-a71f-4441-8beb-cbb5cab7c514:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"9e45767a-451f-48a1-b421-17738c299cd9:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"398a8ba3-0ffc-40ee-90e1-c1547938d171:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"398a8ba3-0ffc-40ee-90e1-c1547938d171:indexpattern-datasource-layer-c76f346d-f6d6-4f9e-acb8-f5dde656e783","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"ad54fa9e-40c4-4c74-85c2-543efeef1004:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"ad54fa9e-40c4-4c74-85c2-543efeef1004:indexpattern-datasource-layer-07f20f17-d0d3-4d63-b030-7980f218c412","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"7a0555be-d5f3-4aeb-9159-f48d7264d40c:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:indexpattern-datasource-layer-18ea127c-2267-4d24-9893-d3ef85942514","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-0","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-1","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-2","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-3","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-4","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-5","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-6","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-7","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-8","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-9","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-10","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-11","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-12","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-13","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-14","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-15","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-16","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-17","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-18","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-19","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-20","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"1d2c60a9-c570-45b0-8f49-e577c74e9ce3:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"1d2c60a9-c570-45b0-8f49-e577c74e9ce3:indexpattern-datasource-layer-8e37793f-a2a3-48b0-a4b5-dda752e958b9","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb:indexpattern-datasource-layer-f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"611221c8-59e6-4ea2-bfdb-bbb53f646772:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"611221c8-59e6-4ea2-bfdb-bbb53f646772:indexpattern-datasource-layer-d7984002-15d6-4e61-b30e-d34bc0a066ea","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c:indexpattern-datasource-layer-b770c4de-625b-4d6b-9cd2-caf7372d5d6a","type":"index-pattern"},{"id":"4c290ba0-fdad-11eb-b912-d99e9986f72b","name":"46f514cc-dac0-4727-9416-ea72ea7a7ed6:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"4c290ba0-fdad-11eb-b912-d99e9986f72b","name":"46f514cc-dac0-4727-9416-ea72ea7a7ed6:indexpattern-datasource-layer-f30699c9-d583-4db7-a489-b1e1ff2b86fe","type":"index-pattern"},{"id":"0a358990-fcd0-11eb-b912-d99e9986f72b","name":"ed79a50e-9a59-475a-8e0c-d41b0cb84acd:panel_ed79a50e-9a59-475a-8e0c-d41b0cb84acd","type":"search"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"0492dbd1-815d-46f2-82b9-1917fddcd8a7:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"0492dbd1-815d-46f2-82b9-1917fddcd8a7:indexpattern-datasource-layer-889ef61e-c27c-49b4-97b5-0bcad36eb8c3","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"c0743ff5-8470-469a-86cf-5d33d45deb34:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"c0743ff5-8470-469a-86cf-5d33d45deb34:indexpattern-datasource-layer-411026a7-eff6-47fa-9e93-bff4143c7544","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"557d758a-f0b2-4d4f-aebd-a32f8cf70b9c:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"42a0de3a-e9c3-4f34-bf5a-82244b6cf497:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"a79397e8-8420-4be0-903e-23c664992a25:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"a79397e8-8420-4be0-903e-23c664992a25:indexpattern-datasource-layer-07f20f17-d0d3-4d63-b030-7980f218c412","type":"index-pattern"}],"type":"dashboard","updated_at":"2021-08-15T11:01:33.321Z","version":"WzU5NDU4LDJd"}
{"exportedCount":1,"missingRefCount":0,"missingReferences":[]}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/last_backup/k8s_audit_dashboard-future.ndjson
================================================
{"attributes":{"description":"","hits":0,"kibanaSavedObjectMeta":{"searchSourceJSON":"{\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filter\":[]}"},"optionsJSON":"{\"hidePanelTitles\":false,\"syncColors\":true,\"useMargins\":true}","panelsJSON":"[{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":0,\"w\":48,\"h\":4,\"i\":\"ac6581bb-3b07-45af-b3d6-3c3e30b7fa0e\"},\"panelIndex\":\"ac6581bb-3b07-45af-b3d6-3c3e30b7fa0e\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"markdown\",\"params\":{\"fontSize\":21,\"openLinksInNewTab\":false,\"markdown\":\"Filters\"},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":true,\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":4,\"w\":12,\"h\":6,\"i\":\"df4da863-2133-4560-82f3-5c126ac27f14\"},\"panelIndex\":\"df4da863-2133-4560-82f3-5c126ac27f14\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1628927100713\",\"fieldName\":\"cluster_id.keyword\",\"parent\":\"\",\"label\":\"k8s-cluster_id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_df4da863-2133-4560-82f3-5c126ac27f14_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Cluster filter\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":12,\"y\":4,\"w\":12,\"h\":6,\"i\":\"58adfaa4-02bd-4b64-89cc-395d6ee0f968\"},\"panelIndex\":\"58adfaa4-02bd-4b64-89cc-395d6ee0f968\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1628927314788\",\"fieldName\":\"cloud_id.keyword\",\"parent\":\"\",\"label\":\"k8s-cloud_id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_58adfaa4-02bd-4b64-89cc-395d6ee0f968_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Cloud filter\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":24,\"y\":4,\"w\":12,\"h\":6,\"i\":\"7bd8bc93-77ba-4de0-a3ff-46dfb58b9109\"},\"panelIndex\":\"7bd8bc93-77ba-4de0-a3ff-46dfb58b9109\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1629308709541\",\"fieldName\":\"folder_id.keyword\",\"parent\":\"\",\"label\":\"k8s-folder_id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_7bd8bc93-77ba-4de0-a3ff-46dfb58b9109_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"Folder filter\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":36,\"y\":4,\"w\":12,\"h\":6,\"i\":\"ff5a5c53-c294-4c2b-ad00-3011d042dbcb\"},\"panelIndex\":\"ff5a5c53-c294-4c2b-ad00-3011d042dbcb\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1629308369258\",\"fieldName\":\"objectRef.namespace.keyword\",\"parent\":\"\",\"label\":\"k8s-namespace\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_ff5a5c53-c294-4c2b-ad00-3011d042dbcb_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"Namespace filter\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":10,\"w\":12,\"h\":4,\"i\":\"5c09dead-7faf-4100-8f5a-7dec81dfcae3\"},\"panelIndex\":\"5c09dead-7faf-4100-8f5a-7dec81dfcae3\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\":{\"columns\":{\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\":{\"label\":\"Top values of cluster_url.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"cluster_url.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"76b4703c-15ec-48d9-a55f-4f8b9ad61473\":{\"label\":\"Top values of cluster_id.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"cluster_id.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"95107cd5-d71c-446d-be12-9ebe860cca6c\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"76b4703c-15ec-48d9-a55f-4f8b9ad61473\",\"95107cd5-d71c-446d-be12-9ebe860cca6c\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"treemap\",\"palette\":{\"type\":\"palette\",\"name\":\"cool\"},\"layers\":[{\"layerId\":\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\",\"groups\":[\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"76b4703c-15ec-48d9-a55f-4f8b9ad61473\"],\"metric\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"hide\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\"}]},\"enhancements\":{\"dynamicActions\":{\"events\":[{\"eventId\":\"e2434170-8807-4c59-823d-345d4f235e8d\",\"triggers\":[\"VALUE_CLICK_TRIGGER\"],\"action\":{\"factoryId\":\"URL_DRILLDOWN\",\"name\":\"Go to URL\",\"config\":{\"url\":{\"template\":\"{{event.value}}\"},\"openInNewTab\":true,\"encodeUrl\":true}}}]}},\"hidePanelTitles\":false},\"title\":\"Click on Cluster - go to YC concole\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":12,\"y\":10,\"w\":12,\"h\":4,\"i\":\"ba1c70dc-01c5-4fe3-8920-0dc8b0285e9f\"},\"panelIndex\":\"ba1c70dc-01c5-4fe3-8920-0dc8b0285e9f\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\":{\"columns\":{\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\":{\"label\":\"Top values of cloud.service.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"cloud.service.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"95107cd5-d71c-446d-be12-9ebe860cca6c\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"95107cd5-d71c-446d-be12-9ebe860cca6c\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"treemap\",\"palette\":{\"type\":\"palette\",\"name\":\"cool\"},\"layers\":[{\"layerId\":\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\",\"groups\":[\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\"],\"metric\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"hide\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\"}]},\"enhancements\":{\"dynamicActions\":{\"events\":[{\"eventId\":\"e2434170-8807-4c59-823d-345d4f235e8d\",\"triggers\":[\"VALUE_CLICK_TRIGGER\"],\"action\":{\"factoryId\":\"URL_DRILLDOWN\",\"name\":\"Go to URL\",\"config\":{\"url\":{\"template\":\"https://console.cloud.yandex.ru/\"},\"openInNewTab\":true,\"encodeUrl\":true}}}]}},\"hidePanelTitles\":false},\"title\":\"Click on Cloud - go to YC concole\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":10,\"w\":12,\"h\":4,\"i\":\"14c3ebb9-6592-4fb5-ab34-2a8ab1e0ab04\"},\"panelIndex\":\"14c3ebb9-6592-4fb5-ab34-2a8ab1e0ab04\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\":{\"columns\":{\"57147c6c-713f-4793-865a-1d671e3f141c\":{\"label\":\"Top values of folder_id.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"folder_id.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"95107cd5-d71c-446d-be12-9ebe860cca6c\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"57147c6c-713f-4793-865a-1d671e3f141c\",\"95107cd5-d71c-446d-be12-9ebe860cca6c\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"treemap\",\"palette\":{\"type\":\"palette\",\"name\":\"cool\"},\"layers\":[{\"layerId\":\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\",\"groups\":[\"57147c6c-713f-4793-865a-1d671e3f141c\"],\"metric\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"hide\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\"}]},\"enhancements\":{\"dynamicActions\":{\"events\":[{\"eventId\":\"e2434170-8807-4c59-823d-345d4f235e8d\",\"triggers\":[\"VALUE_CLICK_TRIGGER\"],\"action\":{\"factoryId\":\"URL_DRILLDOWN\",\"name\":\"Go to URL\",\"config\":{\"url\":{\"template\":\"https://console.cloud.yandex.ru/folders/{{event.value}}\"},\"openInNewTab\":true,\"encodeUrl\":true}}}]}},\"hidePanelTitles\":false},\"title\":\"Click on Folder - go to YC concole\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":14,\"w\":48,\"h\":4,\"i\":\"7a112312-c097-4205-9f74-38913eae2169\"},\"panelIndex\":\"7a112312-c097-4205-9f74-38913eae2169\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"markdown\",\"params\":{\"fontSize\":21,\"openLinksInNewTab\":true,\"markdown\":\"Main k8s audit Events\"},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":true,\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"map\",\"gridData\":{\"x\":0,\"y\":18,\"w\":24,\"h\":15,\"i\":\"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2\"},\"panelIndex\":\"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"description\":\"\",\"layerListJSON\":\"[{\\\"sourceDescriptor\\\":{\\\"type\\\":\\\"EMS_TMS\\\",\\\"isAutoSelect\\\":false,\\\"id\\\":\\\"road_map\\\"},\\\"id\\\":\\\"99115329-feb3-42c6-b426-dff8bd1e1b3a\\\",\\\"label\\\":null,\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":1,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"TILE\\\"},\\\"type\\\":\\\"VECTOR_TILE\\\",\\\"areLabelsOnTop\\\":false},{\\\"sourceDescriptor\\\":{\\\"indexPatternId\\\":\\\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\\\",\\\"geoField\\\":\\\"geoip.location\\\",\\\"filterByMapBounds\\\":true,\\\"scalingType\\\":\\\"CLUSTERS\\\",\\\"id\\\":\\\"5728ef62-6dc0-4b27-b048-7ffda088d201\\\",\\\"type\\\":\\\"ES_SEARCH\\\",\\\"applyGlobalQuery\\\":true,\\\"applyGlobalTime\\\":true,\\\"tooltipProperties\\\":[],\\\"sortField\\\":\\\"\\\",\\\"sortOrder\\\":\\\"desc\\\",\\\"topHitsSplitField\\\":\\\"\\\",\\\"topHitsSize\\\":1},\\\"id\\\":\\\"04fbaa00-b4ba-40db-b46e-8a6dd6d12d04\\\",\\\"label\\\":\\\"success-connect-from-ip\\\",\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":0.91,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"VECTOR\\\",\\\"properties\\\":{\\\"icon\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"value\\\":\\\"marker\\\"}},\\\"fillColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#54B399\\\"}},\\\"lineColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#41937c\\\"}},\\\"lineWidth\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":1}},\\\"iconSize\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":6}},\\\"iconOrientation\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"orientation\\\":0}},\\\"labelText\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"value\\\":\\\"\\\"}},\\\"labelColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#000000\\\"}},\\\"labelSize\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":14}},\\\"labelBorderColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#FFFFFF\\\"}},\\\"symbolizeAs\\\":{\\\"options\\\":{\\\"value\\\":\\\"circle\\\"}},\\\"labelBorderSize\\\":{\\\"options\\\":{\\\"size\\\":\\\"SMALL\\\"}}},\\\"isTimeAware\\\":true},\\\"type\\\":\\\"BLENDED_VECTOR\\\",\\\"joins\\\":[],\\\"query\\\":{\\\"query\\\":\\\"not responseStatus.status : Failure\\\",\\\"language\\\":\\\"kuery\\\"}}]\",\"mapStateJSON\":\"{\\\"zoom\\\":1.41,\\\"center\\\":{\\\"lon\\\":78.63166,\\\"lat\\\":57.21062},\\\"timeFilters\\\":{\\\"from\\\":\\\"now-15d\\\",\\\"to\\\":\\\"now\\\"},\\\"refreshConfig\\\":{\\\"isPaused\\\":true,\\\"interval\\\":0},\\\"query\\\":{\\\"query\\\":\\\"event.dataset : yandexcloud.k8s_audit_logs and source.ip : * and not responseStatus.status : Failure\\\",\\\"language\\\":\\\"kuery\\\"},\\\"filters\\\":[],\\\"settings\\\":{\\\"autoFitToDataBounds\\\":false,\\\"backgroundColor\\\":\\\"#ffffff\\\",\\\"disableInteractive\\\":false,\\\"disableTooltipControl\\\":false,\\\"hideToolbarOverlay\\\":false,\\\"hideLayerControl\\\":false,\\\"hideViewControl\\\":false,\\\"initialLocation\\\":\\\"LAST_SAVED_LOCATION\\\",\\\"fixedLocation\\\":{\\\"lat\\\":0,\\\"lon\\\":0,\\\"zoom\\\":2},\\\"browserLocation\\\":{\\\"zoom\\\":2},\\\"maxZoom\\\":24,\\\"minZoom\\\":0,\\\"showScaleControl\\\":false,\\\"showSpatialFilters\\\":true,\\\"spatialFiltersAlpa\\\":0.3,\\\"spatialFiltersFillColor\\\":\\\"#DA8B45\\\",\\\"spatialFiltersLineColor\\\":\\\"#DA8B45\\\"}}\",\"uiStateJSON\":\"{\\\"isLayerTOCOpen\\\":true,\\\"openTOCDetails\\\":[]}\"},\"mapCenter\":{\"lat\":57.21062,\"lon\":78.63166,\"zoom\":1.41},\"mapBuffer\":{\"minLon\":-155.53415999999999,\"minLat\":-9.879624999999994,\"maxLon\":312.79748,\"maxLat\":104.90343499999999},\"isLayerTOCOpen\":false,\"openTOCDetails\":[],\"hiddenLayers\":[],\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"Connect from ip\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":18,\"w\":24,\"h\":10,\"i\":\"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c\"},\"panelIndex\":\"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"b770c4de-625b-4d6b-9cd2-caf7372d5d6a\":{\"columns\":{\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\":{\"label\":\"Top values of event.dataset.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"event.dataset.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"8a74805c-8582-46c0-8d53-920a919f9b59\":{\"label\":\"stageTimestamp\",\"dataType\":\"date\",\"operationType\":\"date_histogram\",\"sourceField\":\"stageTimestamp\",\"isBucketed\":true,\"scale\":\"interval\",\"params\":{\"interval\":\"auto\"}},\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\",\"8a74805c-8582-46c0-8d53-920a919f9b59\",\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"top\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"layerId\":\"b770c4de-625b-4d6b-9cd2-caf7372d5d6a\",\"accessors\":[\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"],\"position\":\"top\",\"seriesType\":\"bar_stacked\",\"showGridlines\":false,\"xAccessor\":\"8a74805c-8582-46c0-8d53-920a919f9b59\",\"palette\":{\"type\":\"palette\",\"name\":\"temperature\"},\"splitAccessor\":\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\"}]},\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-b770c4de-625b-4d6b-9cd2-caf7372d5d6a\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Events-by-time\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":28,\"w\":12,\"h\":14,\"i\":\"398a8ba3-0ffc-40ee-90e1-c1547938d171\"},\"panelIndex\":\"398a8ba3-0ffc-40ee-90e1-c1547938d171\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"c76f346d-f6d6-4f9e-acb8-f5dde656e783\":{\"columns\":{\"b659aca0-0f1f-4408-8cea-1eea232bfe93\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"b659aca0-0f1f-4408-8cea-1eea232bfe93\",\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"c76f346d-f6d6-4f9e-acb8-f5dde656e783\",\"groups\":[\"b659aca0-0f1f-4408-8cea-1eea232bfe93\"],\"metric\":\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"default\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.namespace.keyword: kube-system and verb : create and objectRef.resource.keyword: pods and objectRef.name : * and not objectRef.name : (*calico* or *dns* or *npd* or *proxy* or *metrics* or *csi* or *masq* or *hubble*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-c76f346d-f6d6-4f9e-acb8-f5dde656e783\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Create pod in kube-system\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":36,\"y\":28,\"w\":12,\"h\":14,\"i\":\"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb\"},\"panelIndex\":\"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\":{\"columns\":{\"71c8af00-7864-4ca6-a20d-0e43a80da354\":{\"label\":\"Top values of requestObject.status.containerStatuses.image.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"requestObject.status.containerStatuses.image.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"71c8af00-7864-4ca6-a20d-0e43a80da354\",\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\",\"groups\":[\"71c8af00-7864-4ca6-a20d-0e43a80da354\"],\"metric\":\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and not requestObject.status.containerStatuses.image.keyword: *cr.yandex/* and requestObject.status.containerStatuses.containerID : *docker* and verb : patch and not requestObject.status.containerStatuses.image.keyword: (*falco* or *openpolicyagent* or *kyverno* or *k8s.gcr.io*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Images not from YC CR\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":33,\"w\":13,\"h\":9,\"i\":\"1d2c60a9-c570-45b0-8f49-e577c74e9ce3\"},\"panelIndex\":\"1d2c60a9-c570-45b0-8f49-e577c74e9ce3\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsDatatable\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"8e37793f-a2a3-48b0-a4b5-dda752e958b9\":{\"columns\":{\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\":{\"label\":\"Current Cluster Admins\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false},\"customLabel\":true},\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\",\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"columns\":[{\"isTransposed\":false,\"columnId\":\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\"},{\"isTransposed\":false,\"columnId\":\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\",\"hidden\":true}],\"layerId\":\"8e37793f-a2a3-48b0-a4b5-dda752e958b9\"},\"query\":{\"query\":\"user.groups.keyword: *admin*\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-8e37793f-a2a3-48b0-a4b5-dda752e958b9\"}]},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":13,\"y\":33,\"w\":11,\"h\":9,\"i\":\"4d0ab419-47d3-48bd-9e5e-93a563e20aee\"},\"panelIndex\":\"4d0ab419-47d3-48bd-9e5e-93a563e20aee\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"b5bee140-5f01-4de3-9395-d279acb203dc\":{\"columns\":{\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\":{\"label\":\"Top values of objectRef.resource.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.resource.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"4eda6d99-05c3-4ab8-a294-4632c9442157\":{\"label\":\"Top values of requestObject.subjects.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"requestObject.subjects.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\",\"4eda6d99-05c3-4ab8-a294-4632c9442157\",\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":false,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"layerId\":\"b5bee140-5f01-4de3-9395-d279acb203dc\",\"accessors\":[\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"],\"position\":\"top\",\"seriesType\":\"bar_stacked\",\"showGridlines\":false,\"xAccessor\":\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\",\"splitAccessor\":\"4eda6d99-05c3-4ab8-a294-4632c9442157\"}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and requestObject.roleRef.name.keyword:(cluster-admin or admin) and objectRef.resource.keyword: (clusterrolebindings or rolebindings) and verb : create and not responseObject.reason : AlreadyExists\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-b5bee140-5f01-4de3-9395-d279acb203dc\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Assign Cluster-admin/admin\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":42,\"w\":17,\"h\":8,\"i\":\"9e45767a-451f-48a1-b421-17738c299cd9\"},\"panelIndex\":\"9e45767a-451f-48a1-b421-17738c299cd9\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"pie\",\"params\":{\"type\":\"pie\",\"addTooltip\":true,\"addLegend\":true,\"legendPosition\":\"left\",\"isDonut\":true,\"labels\":{\"show\":true,\"values\":false,\"last_level\":true,\"truncate\":100},\"row\":false},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"NetworkPolicy:create/delete/update\"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"cluster_id.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"split\"},{\"id\":\"3\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"verb.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"segment\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and requestObject.kind.keyword: (NetworkPolicy or CiliumNetworkPolicy or DeleteOptions) and verb : (create or update or delete) and objectRef.resource : networkpolicies\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"NetworkPolicy:create/delete/update\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":17,\"y\":42,\"w\":17,\"h\":8,\"i\":\"7a0555be-d5f3-4aeb-9159-f48d7264d40c\"},\"panelIndex\":\"7a0555be-d5f3-4aeb-9159-f48d7264d40c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"pie\",\"params\":{\"type\":\"pie\",\"addTooltip\":true,\"addLegend\":true,\"legendPosition\":\"left\",\"isDonut\":true,\"labels\":{\"show\":true,\"values\":false,\"last_level\":true,\"truncate\":100},\"row\":false},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Exec to container\"},\"schema\":\"metric\"},{\"id\":\"3\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"cluster_id.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\",\"customLabel\":\"Cluster_id\"},\"schema\":\"split\"},{\"id\":\"4\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"objectRef.name.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"segment\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.subresource.keyword: exec\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{},\"vis\":{\"legendOpen\":true}},\"title\":\"Exec to container\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":34,\"y\":42,\"w\":14,\"h\":8,\"i\":\"b6d054cd-bca1-49a6-affb-7b115b76af5a\"},\"panelIndex\":\"b6d054cd-bca1-49a6-affb-7b115b76af5a\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsDatatable\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"18ea127c-2267-4d24-9893-d3ef85942514\":{\"columns\":{\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\":{\"label\":\"Unique count of user.name.keyword\",\"dataType\":\"number\",\"operationType\":\"unique_count\",\"scale\":\"ratio\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":false},\"c94a437d-970d-4c55-89a7-499d47032bc8\":{\"label\":\"ServiceAccounts\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":15,\"orderBy\":{\"type\":\"column\",\"columnId\":\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false},\"customLabel\":true}},\"columnOrder\":[\"c94a437d-970d-4c55-89a7-499d47032bc8\",\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"layerId\":\"18ea127c-2267-4d24-9893-d3ef85942514\",\"columns\":[{\"isTransposed\":false,\"columnId\":\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\",\"hidden\":true},{\"columnId\":\"c94a437d-970d-4c55-89a7-499d47032bc8\",\"isTransposed\":false,\"alignment\":\"left\"}]},\"query\":{\"query\":\"user.name : *serviceaccount*\",\"language\":\"kuery\"},\"filters\":[{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:certificate-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-0\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:certificate-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:coredns\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-1\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:coredns\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:cronjob-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-2\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:cronjob-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:generic-garbage-collector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-3\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:generic-garbage-collector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:job-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-4\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:job-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:endpointslice-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-5\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:endpointslice-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:endpoint-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-6\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:endpoint-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:calico-node\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-7\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:calico-node\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:kube-proxy\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-8\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:kube-proxy\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"alias\":null,\"negate\":true,\"disabled\":false,\"type\":\"phrase\",\"key\":\"objectRef.namespace\",\"params\":{\"query\":\"kube-system\"},\"indexRefName\":\"filter-index-pattern-9\"},\"query\":{\"match_phrase\":{\"objectRef.namespace\":\"kube-system\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:kube-dns-autoscaler\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-10\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:kube-dns-autoscaler\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:daemon-set-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-11\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:daemon-set-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:metrics-server\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-12\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:metrics-server\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:pod-garbage-collector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-13\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:pod-garbage-collector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:node-problem-detector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-14\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:node-problem-detector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:typha-cpha\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-15\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:typha-cpha\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:service-account-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-16\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:service-account-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:resourcequota-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-17\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:resourcequota-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:replicaset-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-18\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:replicaset-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:namespace-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-19\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:namespace-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:typha-cpva\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-20\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:typha-cpva\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:gatekeeper-system:gatekeeper-admin\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-21\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:gatekeeper-system:gatekeeper-admin\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:cilium-operator\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-22\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:cilium-operator\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:cilium\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-23\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:cilium\"}},\"$state\":{\"store\":\"appState\"}}]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-18ea127c-2267-4d24-9893-d3ef85942514\"},{\"name\":\"filter-index-pattern-0\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-1\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-2\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-3\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-4\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-5\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-6\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-7\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-8\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-9\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-10\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-11\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-12\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-13\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-14\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-15\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-16\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-17\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-18\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-19\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-20\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-21\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-22\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-23\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"}]},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"map\",\"gridData\":{\"x\":0,\"y\":50,\"w\":34,\"h\":9,\"i\":\"96fdb671-a668-4ffc-9ad1-792d69551764\"},\"panelIndex\":\"96fdb671-a668-4ffc-9ad1-792d69551764\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"description\":\"\",\"layerListJSON\":\"[{\\\"sourceDescriptor\\\":{\\\"type\\\":\\\"EMS_TMS\\\",\\\"id\\\":\\\"dark_map\\\",\\\"isAutoSelect\\\":false},\\\"id\\\":\\\"1a56b9d3-c903-4286-8d75-48b62bf38532\\\",\\\"label\\\":null,\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":1,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"TILE\\\"},\\\"type\\\":\\\"VECTOR_TILE\\\"},{\\\"sourceDescriptor\\\":{\\\"indexPatternId\\\":\\\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\\\",\\\"geoField\\\":\\\"geoip.location\\\",\\\"requestType\\\":\\\"heatmap\\\",\\\"id\\\":\\\"65583363-2a0b-40ce-bf98-40ff54ad224e\\\",\\\"type\\\":\\\"ES_GEO_GRID\\\",\\\"applyGlobalQuery\\\":true,\\\"applyGlobalTime\\\":true,\\\"metrics\\\":[{\\\"type\\\":\\\"count\\\"}],\\\"resolution\\\":\\\"FINE\\\"},\\\"id\\\":\\\"519e1390-4055-4be7-a5bc-537bb78eea07\\\",\\\"label\\\":null,\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":0.58,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"HEATMAP\\\",\\\"colorRampName\\\":\\\"theclassic\\\"},\\\"type\\\":\\\"HEATMAP\\\"}]\",\"mapStateJSON\":\"{\\\"zoom\\\":1.45,\\\"center\\\":{\\\"lon\\\":54.04753,\\\"lat\\\":56.32976},\\\"timeFilters\\\":{\\\"from\\\":\\\"now-15d\\\",\\\"to\\\":\\\"now\\\"},\\\"refreshConfig\\\":{\\\"isPaused\\\":true,\\\"interval\\\":0},\\\"query\\\":{\\\"query\\\":\\\"event.dataset : yandexcloud.k8s_audit_logs and responseStatus.reason : Forbidden and not user.name : (system*node* or *gatekeeper* or *kyverno* or *proxy* or *scheduler* or *anonymous* or *csi* or *controller*)\\\",\\\"language\\\":\\\"kuery\\\"},\\\"filters\\\":[],\\\"settings\\\":{\\\"autoFitToDataBounds\\\":false,\\\"backgroundColor\\\":\\\"#ffffff\\\",\\\"disableInteractive\\\":false,\\\"disableTooltipControl\\\":false,\\\"hideToolbarOverlay\\\":false,\\\"hideLayerControl\\\":false,\\\"hideViewControl\\\":false,\\\"initialLocation\\\":\\\"LAST_SAVED_LOCATION\\\",\\\"fixedLocation\\\":{\\\"lat\\\":0,\\\"lon\\\":0,\\\"zoom\\\":2},\\\"browserLocation\\\":{\\\"zoom\\\":2},\\\"maxZoom\\\":24,\\\"minZoom\\\":0,\\\"showScaleControl\\\":false,\\\"showSpatialFilters\\\":true,\\\"spatialFiltersAlpa\\\":0.3,\\\"spatialFiltersFillColor\\\":\\\"#DA8B45\\\",\\\"spatialFiltersLineColor\\\":\\\"#DA8B45\\\"}}\",\"uiStateJSON\":\"{\\\"isLayerTOCOpen\\\":true,\\\"openTOCDetails\\\":[]}\"},\"mapCenter\":{\"lat\":56.32976,\"lon\":54.04753,\"zoom\":1.45},\"mapBuffer\":{\"minLon\":-269.96721,\"minLat\":21.676450000000003,\"maxLon\":378.06227,\"maxLat\":84.75865},\"isLayerTOCOpen\":false,\"openTOCDetails\":[],\"hiddenLayers\":[],\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":34,\"y\":50,\"w\":14,\"h\":9,\"i\":\"bb843cd6-969c-4aae-a37c-978d2fe0bbef\"},\"panelIndex\":\"bb843cd6-969c-4aae-a37c-978d2fe0bbef\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"d401535b-665e-442b-a312-9edd3c1ebcc0\":{\"columns\":{\"61acda83-5d64-453e-9ca1-16b129cc2b42\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"56667c46-e4e6-4a18-9613-12d027ca7a16\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"ece5248d-0578-44e8-b245-bc2de86f37f4\":{\"label\":\"@timestamp\",\"dataType\":\"date\",\"operationType\":\"date_histogram\",\"sourceField\":\"@timestamp\",\"isBucketed\":true,\"scale\":\"interval\",\"params\":{\"interval\":\"auto\"}},\"56667c46-e4e6-4a18-9613-12d027ca7a16\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"61acda83-5d64-453e-9ca1-16b129cc2b42\",\"ece5248d-0578-44e8-b245-bc2de86f37f4\",\"56667c46-e4e6-4a18-9613-12d027ca7a16\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\",\"showSingleSeries\":false},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"palette\":{\"type\":\"palette\",\"name\":\"gray\"},\"layerId\":\"d401535b-665e-442b-a312-9edd3c1ebcc0\",\"seriesType\":\"bar_stacked\",\"xAccessor\":\"ece5248d-0578-44e8-b245-bc2de86f37f4\",\"splitAccessor\":\"61acda83-5d64-453e-9ca1-16b129cc2b42\",\"accessors\":[\"56667c46-e4e6-4a18-9613-12d027ca7a16\"]}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseStatus.reason : Forbidden and not user.name : (system*node* or *gatekeeper* or *kyverno* or *proxy* or *scheduler* or *anonymous* or *csi* or *controller*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-d401535b-665e-442b-a312-9edd3c1ebcc0\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Unauthorized events\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":59,\"w\":48,\"h\":4,\"i\":\"5abb0208-9bcf-42f2-8376-ee20d8047f2a\"},\"panelIndex\":\"5abb0208-9bcf-42f2-8376-ee20d8047f2a\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"markdown\",\"params\":{\"fontSize\":21,\"openLinksInNewTab\":false,\"markdown\":\"Policy Engine\"},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":true,\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":63,\"w\":5,\"h\":9,\"i\":\"e1d27ba4-c45c-431e-933b-0a174c71d48c\"},\"panelIndex\":\"e1d27ba4-c45c-431e-933b-0a174c71d48c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"metric\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"type\":\"metric\",\"metric\":{\"percentageMode\":false,\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"metricColorMode\":\"Labels\",\"colorsRange\":[{\"from\":0,\"to\":1},{\"from\":1,\"to\":100000}],\"labels\":{\"show\":true},\"invertColors\":false,\"style\":{\"bgFill\":\"#000\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":76}}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"OPA-Gatekeeper-Detections\"},\"schema\":\"metric\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":5,\"y\":63,\"w\":9,\"h\":9,\"i\":\"f9181782-c266-4c44-860e-dc37a48bf08f\"},\"panelIndex\":\"f9181782-c266-4c44-860e-dc37a48bf08f\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"6f2deb01-002f-4a18-bee7-7968ad39a8a7\":{\"columns\":{\"443941ae-37bd-4230-a7c2-3eec6b193f37\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"1708471f-d516-4b55-a792-7263d51215ba\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"1708471f-d516-4b55-a792-7263d51215ba\":{\"label\":\"OPA-Gatekeeper detection\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\",\"customLabel\":true}},\"columnOrder\":[\"443941ae-37bd-4230-a7c2-3eec6b193f37\",\"1708471f-d516-4b55-a792-7263d51215ba\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"6f2deb01-002f-4a18-bee7-7968ad39a8a7\",\"groups\":[\"443941ae-37bd-4230-a7c2-3eec6b193f37\"],\"metric\":\"1708471f-d516-4b55-a792-7263d51215ba\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-6f2deb01-002f-4a18-bee7-7968ad39a8a7\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"opa-by-user(yc iam user get --id
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/LICENSE
================================================
Copyright 2021 YANDEX LLC
Licensed under the Apache License, Version 2.0 (the "License");
you may not use this file except in compliance with the License.
You may obtain a copy of the License at
http://www.apache.org/licenses/LICENSE-2.0
Unless required by applicable law or agreed to in writing, software
distributed under the License is distributed on an "AS IS" BASIS,
WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
See the License for the specific language governing permissions and
limitations under the License.
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/README.md
================================================
# Collecting, monitoring and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)

# Version
**Version-2.1**
- Changelog:
- Added new use cases from [Use cases and important security events in audit logs](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches#use-cases-%D0%B8-%D0%B2%D0%B0%D0%B6%D0%BD%D1%8B%D0%B5-%D1%81%D0%BE%D0%B1%D1%8B%D1%82%D0%B8%D1%8F-%D0%B1%D0%B5%D0%B7%D0%BE%D0%BF%D0%B0%D1%81%D0%BD%D0%BE%D1%81%D1%82%D0%B8-%D0%B2-%D0%B0%D1%83%D0%B4%D0%B8%D1%82-%D0%BB%D0%BE%D0%B3%D0%B0%D1%85)"
- Docker images:
- `cr.yandex/sol/s3-elk-importer:2.1`
- `cr.yandex/sol/elk-updater:1.0.4`
**Version-2.0**
- Changelog:
- Добавлен фильтр по Folder name
- Docker images:
- `cr.yandex/sol/s3-elk-importer:1.0.6`
# Table of contents
- [Solution description](#solution-description)
- [Solution features](#solution-features)
- [Solution diagram](#solution-diagram)
- [Security Content](#security-content)
- [License restrictions](#license-restrictions)
- [Content update process](#content-update-process)
- [Deployment using Terraform](#deployment-using-Terraform)
- [Deployment of a solution to supply K8s logs] (#deployment-of-a-solution-to-supply-k8s-logs)
- [Recommendations for setting up retention, rollover, and snapshots](#recommendations-for-setting-retention-rollover-and-snapshots)
## Solution description
The solution lets you collect, monitor, and analyze audit logs in Yandex Managed Service for Elasticsearch (ELK) from the following sources:
- [Yandex Audit Trails](https://cloud.yandex.ru/docs/audit-trails/)
- [Yandex Managed Service for Kubernetes](https://cloud.yandex.ru/docs/managed-kubernetes/): audit logs, Falco alerts, and Policy Engine (OPA Gatekeeper) ([setup description](../export-auditlogs-to-ELK_k8s))
> The solution is constantly updated and maintained by the Yandex.Cloud Security team.
## Solution features
- ☑️ Deploy a Managed ELK cluster in the Yandex.Cloud infrastructure via Terraform. In the default configuration, see Deployment using Terraform. Calculate the relevant configuration for your infrastructure together with your cloud architect.
- ☑️ Deploy a COI Instance with container based on the s3-elk-importer image (`cr.yandex/crpjfmfou6gflobbfvfv/s3-elk-importer:latest`).
- ☑️ Upload Security Content to ELK: Dashboards, Detection Rules with alerts, etc.
- ☑️ Enable continuous delivery of JSON files with audit logs from Yandex Object Storage to ELK.
- ☑️ Create indexes in two replicas, configure the basic rollover policy (create new indexes every thirty days or after reaching 50 GB). For further provisioning for high data availability and setting up data snapshots in S3, see [recommendations](./CONFIGURE-HA.md).
## Solution diagram

[Diagram of the solution to supply K8s logs](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_k8s)
## Security Content
**Security Content** are ELK objects automatically loaded by the solution. All the content leverages the long-term expertise of the Yandex.Cloud Security team and our cloud customers.
The solution contains the following Security Content:
- Dashboard that reflects all use cases and useful statistics.
- A set of Saved Queries for easy search of Security events.
- A set of Detection Rules: the correlation rules for which alerts are configured (the client should specify the alert destination).
All relevant event fields have been converted to the [Elastic Common Schema (ECS)] (https://www.elastic.co/guide/en/ecs/current/index.html) format, the full mapping table is in the [file with object description](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf).
A detailed description is in the [ECS-mapping.docx](./papers/ECS-mapping_new.pdf) file
## License restrictions


[Subscription options on ELK site](https://www.elastic.co/subscriptions)
## Content update process
We recommend subscribing to this repository to receive update notifications.
To get the latest content version, do the following:
- Keep the sync container up-to-date.
- Keep the Security content imported to Elasticsearch in the updated state.
For content updates, make sure that you are running the latest available image version: `cr.yandex/crpjfmfou6gflobbfvfv/s3-elk-importer:latest`.
You can update the container as follows:
- You can re-create the deployed COI Instance with the container via Terraform (delete the COI Instance and run: `terraform apply`).
- You can stop and delete the `audit-trail-worker-*` container, delete the `s3-elk-importer` image, and restart COI Instance. After the launch, a new image will be downloaded and a new container will be created.
You can update the Security content in Kibana (dashboards, detection rules, searches) by launching the elk-updater container:
```
docker run -it --rm -e ELASTIC_AUTH_USER='admin' -e ELASTIC_AUTH_PW='password' -e KIBANA_SERVER='https://xxx.rw.mdb.yandexcloud.net' --name elk-updater cr.yandex/crpjfmfou6gflobbfvfv/elk-updater:latest
```
## Deployment using Terraform
#### Description
#### Prerequisites:
- :white_check_mark: Object Storage Bucket for Audit Trails.
- :white_check_mark: [Audit Trails service enabled](https://cloud.yandex.ru/docs/audit-trails/quickstart) in the UI.
- :white_check_mark: VPC network.
- :white_check_mark: Subnets in three availability zones.
- :white_check_mark: COI Instance has access to the internet to download the container image.
- :white_check_mark: ServiceAccount with the *storage.editor* role for actions in Object Storage.
See the example of configuring prerequisites and calling modules in [/example/main.tf](./terraform/example)
##
The solution consists of two Terraform modules [/terraform/modules/](./terraform/modules):
- yc-managed-elk creates a cluster [Yandex Managed Service for Elasticsearch](https://cloud.yandex.ru/services/managed-elasticsearch):
- With three nodes (one for each availability zone).
- With a Gold license.
- Characteristics: s2-medium (8 vCPU, 32GB RAM), HDD: 1TB.
- A password to the ELK admin account.
- yc-elastic-trail:
- Creates static keys for the SA (for working with JSON objects in a bucket and encrypting/decrypting secrets).
- Creates a COI VM with a Docker Container specification using a script.
- Creates an SSH key pair and saves the private part to the disk and the public part to the VM.
- Creates a KMS key.
- Assigns the kms.keys.encrypterDecrypter rights to the key for SA to encrypt secrets.
- Encrypts secrets and passes them to Docker Container.
#### Example of calling modules:
```Python
module "yc-managed-elk" {
source = "../modules/yc-managed-elk" # path to module yc-managed-elk
folder_id = var.folder_id
subnet_ids = yandex_vpc_subnet.elk-subnet[*].id # Subnets in three availability zones for ELK deployment
network_id = yandex_vpc_network.vpc-elk.id # The ID of the network where ELK will be deployed
elk_edition = "gold"
elk_datanode_preset = "s2.medium"
elk_datanode_disk_size = 1000
elk_public_ip = false # true if you need a public access to Elasticsearch
}
module "yc-elastic-trail" {
source = "../modules/yc-elastic-trail/" # path to module yc-elastic-trail
folder_id = var.folder_id
elk_credentials = module.yc-managed-elk.elk-pass
elk_address = module.yc-managed-elk.elk_fqdn
bucket_name = yandex_storage_bucket.trail-bucket.bucket
bucket_folder = "" # Specify the name of the prefix where trails writes logs to the bucket, for example prefix-trails (if it's root, then leave empty at default)
sa_id = yandex_iam_service_account.sa-bucket-editor.id
coi_subnet_id = yandex_vpc_subnet.elk-subnet[0].id
}
output "elk-pass" {
value = module.yc-managed-elk.elk-pass
sensitive = true
} // View the ELK password: terraform output elk-pass
output "elk_fqdn" {
value = module.yc-managed-elk.elk_fqdn
} // Outputs the ELK URL that can be accessed, for example, through the browser
output "elk-user" {
value = "admin"
}
```
## Deployment of a solution to supply K8s logs
[Deployment of the K8s log delivery solution](../export-auditlogs-to-ELK_k8s)
## Recommendations for setting up retention, rollover, and snapshots
[Recommendations for setting up retention, rollover, and snapshots](./CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/README_RU.md
================================================
# Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)

# Version
**Version-2.1**
- Changelog:
- Добавлены новые detection rules из [Use cases и важные события безопасности в аудит логах](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches#use-cases-%D0%B8-%D0%B2%D0%B0%D0%B6%D0%BD%D1%8B%D0%B5-%D1%81%D0%BE%D0%B1%D1%8B%D1%82%D0%B8%D1%8F-%D0%B1%D0%B5%D0%B7%D0%BE%D0%BF%D0%B0%D1%81%D0%BD%D0%BE%D1%81%D1%82%D0%B8-%D0%B2-%D0%B0%D1%83%D0%B4%D0%B8%D1%82-%D0%BB%D0%BE%D0%B3%D0%B0%D1%85)"
- Docker images:
- `cr.yandex/sol/s3-elk-importer:2.1`
- `cr.yandex/sol/elk-updater:1.0.4`
**Version-2.0**
- Changelog:
- Добавлен фильтр по Folder name
- Docker images:
- `cr.yandex/sol/s3-elk-importer:1.0.6`
# Оглавление
- [Описание решения](#описание-решения)
- [Что делает решение](#что-делает-решение)
- [Схема решения](#схема-решения)
- [Security Content](#security-content)
- [Лицензионные ограничения](#лицензионные-ограничения)
- [Процесс обновления контента](#процесс-обновления-контента)
- [Развертывание с помощью Terraform](#развертывание-с-помощью-Terraform)
- [Развертывание решения для поставки логов k8s](#развертывание-решения-для-поставки-логов-k8s)
- [Рекомендации по настройке retention, rollover и snapshots:](#рекомендации-по-настройке-retention-rollover-и-snapshots)
## Описание решения
Решение позволяет собирать, мониторить и анализировать аудит логи в Yandex.Cloud Managed Service for Elasticsearch (ELK) из следующих источников:
- [Yandex Audit Trails](https://cloud.yandex.ru/docs/audit-trails/)
- [Yandex Managed Service for Kubernetes](https://cloud.yandex.ru/docs/managed-kubernetes/): аудит логи, алерты falco и Policy Engine (OPA Gatekeeper) ([описание настройки](../export-auditlogs-to-ELK_k8s))
> Решение является постоянно обновляемым и поддерживаемым Security-командой Yandex.Cloud.
> Важно! По умолчанию данная конструкция предлагает удалять файлы после вычитывания из бакета, но вы можете одновременно хранить аудит логи Audit Trails в S3 на долгосрочной основе и отсылать в Elastic. Для этого необходимо создать два Audit Trails в разных S3 бакетах:
- Первый бакет будет использоваться только для хранения
- Второй бакет будет использоваться для интеграции с ArcSight
## Что делает решение
- ☑️ Разворачивает в инфраструктуре Yandex.Cloud кластер Managed ELK (через Terraform) (в default конфигурации см. п. Terraform)(рассчитать необходимую конфигурацию для вашей инфраструктуры необходимо совместно с Cloud Архитектором)
- ☑️ Разворачивает COI Instance с контейнером на базе образа s3-elk-importer (`cr.yandex/sol/s3-elk-importer:latest`)
- ☑️ Загружает Security Content в ELK (Dashboards, Detection Rules (с alerts), etc.)
- ☑️ Обеспечивает непрерывную доставку json файлов с аудит логами из Yandex Object Storage в ELK
- ☑️ Создает индексы в двух репликах, настраивает базовую политику rollover (создания новых индексов каждые тридцать дней или по достижению 50ГБ), для дальнейшей настройки в части высокой доступности данных и для настройки снимков данных в S3 - см. [рекомендации](./CONFIGURE-HA.md).
## Схема решения

[Схема решения для поставки логов k8s](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_k8s)
## Security Content
**Security Content** — объекты ELK, которые автоматически загружаются решением. Весь контент разработан с учетом многолетнего опыта Security команды Yandex.Cloud и на основе опыта Клиентов облака.
Содержит следующий Security Content:
- Dashboard, на котором отражены все use cases и полезная статистика
- Набор Saved Queries для удобного поиска Security событий
- Набор Detection Rules (правила корреляции) на которые настроены оповещения (Клиенту самостоятельно необходимо указать назначение уведомлений)
- Все интересные поля событий преобразованы в формат [Elastic Common Schema (ECS)](https://www.elastic.co/guide/en/ecs/current/index.html), полная табличка маппинга в файле [Описание объектов](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf)
Подробное описание в файле [ECS-mapping.docx](./papers/ECS-mapping_new.pdf)
## Лицензионные ограничения


[Описание различий с сайта ELK](https://www.elastic.co/subscriptions)
## Процесс обновления контента
Рекомендуем подписаться на данный репозиторий для получения уведомлений об обновлениях.
Для того, чтобы использовать самую актуальную версию контента, необходимо
- Поддерживать в актуальной версии контейнер, выполняющий синхронизацию
- Поддерживать в актуальном состоянии Security контент, который импортируется в ElasticSearch
В части обновления контента, необходимо убедиться, что вы используете последнюю доступную версию образа:
`cr.yandex/sol/s3-elk-importer:latest`
Обновление контейнера можно выполнить следующим образом:
- Можно пересоздать развернутый COI Instance с контейнером через Terraform (удалить COI Instance, выполнить `terraform apply`)
- Можно остановить и удалить сам контейнер (`audit-trail-worker-*`), удалить образ `s3-elk-importer`, перезапустить COI Instance — после запуска будет скачан новый образ и создан новый контейнер
Обновление Security контента в Kibana (dashboards, detection rules, searches) — можно выполнить через запуск контейнера `elk-updater`:
```
docker run -it --rm -e ELASTIC_AUTH_USER='admin' -e ELASTIC_AUTH_PW='password' -e KIBANA_SERVER='https://xxx.rw.mdb.yandexcloud.net' --name elk-updater cr.yandex/sol/elk-updater:latest
```
## Развертывание с помощью Terraform
#### Описание
#### Пререквизиты
- :white_check_mark: Object Storage Bucket для Audit Trails
- :white_check_mark: [Включенный сервис Audit Trails](https://cloud.yandex.ru/docs/audit-trails/quickstart) в UI
- :white_check_mark: Сеть VPC
- :white_check_mark: Подсети в 3-х зонах доступности
- :white_check_mark: Наличие доступа в интернет с COI Instance для скачивания образа контейнера
- :white_check_mark: ServiceAccount с ролью *storage.editor* для действий в Object Storage
См. Пример конфигурации пререквизитов и вызова модулей в [/example/main.tf](./terraform/example)
##
Решение состоит из 2-х модулей Terraform [/terraform/modules/](./terraform/modules) :
1) yc-managed-elk:
- создает cluster [Yandex Managed Service for Elasticsearch](https://cloud.yandex.ru/services/managed-elasticsearch)
- с тремя нодами (по одной на каждую зону доступности)
- с лицензией Gold
- характеристики: s2-medium (8 vCPU, 32Gb Memory)
- HDD: 1TB
- назначает пароль на аккаунт admin в ELK
2) yc-elastic-trail:
- создает static keys для sa (для работы с объектами JSON в бакете и шифрования/расшифрования секретов)
- создает ВМ COI со спецификацией Docker Container со скриптом
- создает ssh пару ключей и сохраняет приватную часть на диск, публичную в ВМ
- создает KMS ключ
- назначает права kms.keys.encrypterDecrypter на ключ для sa для шифрование секретов
- шифрует секреты и передает их в Docker Container
#### Пример вызова модулей:
```Python
module "yc-managed-elk" {
source = "../modules/yc-managed-elk" # path to module yc-managed-elk
folder_id = var.folder_id
subnet_ids = yandex_vpc_subnet.elk-subnet[*].id # subnets в 3-х зонах доступности для развертывания ELK
network_id = yandex_vpc_network.vpc-elk.id # network id в которой будет развернут ELK
elk_edition = "gold"
elk_datanode_preset = "s2.medium"
elk_datanode_disk_size = 1000
elk_public_ip = false # true, если нужен публичный доступ к ElasticSearch
}
module "yc-elastic-trail" {
source = "../modules/yc-elastic-trail/" # path to module yc-elastic-trail
folder_id = var.folder_id
elk_credentials = module.yc-managed-elk.elk-pass
elk_address = module.yc-managed-elk.elk_fqdn
bucket_name = yandex_storage_bucket.trail-bucket.bucket
bucket_folder = "" # указать название префикса куда trails пишет логи в бакет, например "prefix-trails", если в корень то оставить по умолчанию пустым
sa_id = yandex_iam_service_account.sa-bucket-editor.id
coi_subnet_id = yandex_vpc_subnet.elk-subnet[0].id
}
output "elk-pass" {
value = module.yc-managed-elk.elk-pass
sensitive = true
} // Чтобы посмотреть пароль ELK: terraform output elk-pass
output "elk_fqdn" {
value = module.yc-managed-elk.elk_fqdn
} // Выводит адрес ELK на который можно обращаться, например через браузер
output "elk-user" {
value = "admin"
}
```
## Развертывание решения для поставки логов k8s:
[Развертывание решения для поставки логов k8s](../export-auditlogs-to-ELK_k8s)
## Рекомендации по настройке retention, rollover и snapshots:
[Рекомендации по настройке retention, rollover и snapshots](./CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/curl_play with elk.sh
================================================
Описание всего:>>>
Описание разовой загрузки объектов данных в ELK (bash скрипт либо питон) >>>
Создаем сам индекс
curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X PUT "https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net:9200/audit-trails-index/?pretty" -H 'Content-Type: application/json' -d @/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/mapping6.json
загрузка ingest pipeline curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X PUT "https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net:9200/_ingest/pipeline/audit-trails-pipeline?pretty" -H 'Content-Type: application/json' -d @/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/pipeline3.json
import kibana index pattern с нужным нашим id
curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/saved_objects/_import --form file=@/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/kibana_index_pattern.ndjson -H 'kbn-xsrf: true'
загрузка filters curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/saved_objects/_import --form file=@/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/filters.ndjson -H 'kbn-xsrf: true'
загрузка search curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/saved_objects/_import --form file=@/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/kibana_search2.ndjson -H 'kbn-xsrf: true'
загрузка dashboards curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/saved_objects/_import --form file=@/Users/mirtov8/Documents/CloudTrail/ELK-new-clean/dashboard_very_new.ndjson -H 'kbn-xsrf: true'
Файл json необходимо преобразовать перед загрузкой в качестве bulk в elk
jq -c -r ".[]" /Users/mirtov8/Documents/CloudTrail/ArcSight\ Connector/gg/155732665.json | while read line; do echo '{"index":{}}'; echo $line; done > bulk.json
python пример ( пример - https://gist.github.com/icamys/4287ae49d20ff2add3db86e2b2053977#file-elastic_import_data_bulk-py-L51 )
Отправка bulk
curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST "https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net:9200/audit-trails-index/_bulk?pipeline=audit-trails-pipeline" -H 'Content-Type: application/json' --data-binary "@./bulk3.json"
python пример ( https://elasticsearch-py.readthedocs.io/en/master/helpers.html ) (https://gist.github.com/icamys/4287ae49d20ff2add3db86e2b2053977#file-elastic_import_data_bulk-py-L51)
загрузка detections curl --user beats:beats123 --cacert ~/.elasticsearch/root.crt -X POST https://c-c9qfr7e8e470ghr1lanf.rw.mdb.yandexcloud.net/api/detection_engine/rules/_import --form file=@./detections.ndjson -H 'kbn-xsrf: true'
______
k8s
curl --user beat:beat123 --cacert ~/.elasticsearch/root.crt -X GET "https://c-c9qps9eabd0ok4haehjq.rw.mdb.yandexcloud.net:9200/k8s-index?pretty"
curl --user beat:beat123 --cacert ~/.elasticsearch/root.crt -X PUT "https://c-c9qps9eabd0ok4haehjq.rw.mdb.yandexcloud.net:9200/k8s-index/?pretty" -H 'Content-Type: application/json' -d @//Users/mirtov8/Documents/GitHub/yc-solution-library-for-security/auditlogs/export-auditlogs-to-ELK/include/k8s/mapping_k8s.json
curl --user beat:beat123 --cacert ~/.elasticsearch/root.crt -X POST "https://c-c9qps9eabd0ok4haehjq.rw.mdb.yandexcloud.net:9200/k8s-index/_bulk?pipeline=k8s_audit-pipeline" -H 'Content-Type: application/json' --data-binary "@./bulk2.json"
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/kms_decrypt_cmds.sh
================================================
Получить токен:
TOKEN=$(curl -H Metadata-Flavor:Google 169.254.169.254/computeMetadata/v1/instance/service-accounts/default/token | jq -r '.access_token')
Зашифровать данные
curl -vX POST https://kms.yandex/kms/v1/keys/abjulftcuh1p66lfdmpg:encrypt -d '{"versionId": "abj24us9a9gl3d28f8kt","plaintext": "password"}' --header "Accept: application/json" --header "Authorization: Bearer ${TOKEN}"
Расшифровать данные
curl -X POST https://kms.yandex/kms/v1/keys/abjulftcuh1p66lfdmpg:decrypt -d '{"ciphertext": "AAAAAQAAABRhYmoyNHVzOWE5Z2wzZDI4ZjhrdAAAABCs8pwmY0EXt4Z93jl2bXyKAAAADNsHbqFdoUZZG6hx38ES7Jal90aYsxU1VZUPP3309i1/Bf4="}' --header "Accept: application/json" --header "Authorization: Bearer ${TOKEN}" | jq '.plaintext' | sed 's/"//g'
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/last_backup/falco_pipeline_backup.json
================================================
{
"description": "k8s pipeline",
"processors": [
{
"set": {
"field": "event.kind",
"value": "event",
"ignore_failure": true
}
},
{
"set": {
"field": "event.category",
"value": ["configuration", "iam"],
"ignore_failure": true
}
},
{
"set": {
"field": "event.dataset",
"value": "yandexcloud.k8s_falco",
"ignore_failure": true
}
},
{
"set": {
"field": "cloud.provider",
"value": "yandexcloud",
"ignore_failure": true
}
},
{
"set": {
"field": "@timestamp",
"value": "{{{time}}}",
"ignore_failure": true
}
},
{
"set": {
"field": "cloud.service.name",
"value": "falco",
"ignore_failure": true
}
}
]
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/last_backup/k8s-mapping-ba.json
================================================
{
"settings" : {
"number_of_replicas" : 2
},
"mappings": {
"properties": {
"source" : {
"properties" : {
"address" : {
"type" : "text",
"fields" : {
"keyword" : {
"type" : "keyword",
"ignore_above" : 256
}
}
},
"ip" : {
"type" : "ip"
}
}
},
"sourceIPs" : {
"type" : "ip"
},
"@timestamp": {
"type": "date"
},
"geoip.location": {
"type": "geo_point"
}
}
}
}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/last_backup/k8s_audit_dashboard-back.ndjson
================================================
{"attributes":{"description":"","hits":0,"kibanaSavedObjectMeta":{"searchSourceJSON":"{\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filter\":[]}"},"optionsJSON":"{\"hidePanelTitles\":false,\"useMargins\":true}","panelsJSON":"[{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":0,\"w\":24,\"h\":6,\"i\":\"df4da863-2133-4560-82f3-5c126ac27f14\"},\"panelIndex\":\"df4da863-2133-4560-82f3-5c126ac27f14\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1628927100713\",\"fieldName\":\"cluster_id.keyword\",\"parent\":\"\",\"label\":\"k8s-cluster_id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_df4da863-2133-4560-82f3-5c126ac27f14_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Cluster filter\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":24,\"y\":0,\"w\":24,\"h\":6,\"i\":\"58adfaa4-02bd-4b64-89cc-395d6ee0f968\"},\"panelIndex\":\"58adfaa4-02bd-4b64-89cc-395d6ee0f968\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1628927314788\",\"fieldName\":\"cloud_id.keyword\",\"parent\":\"\",\"label\":\"k8s-cloud-id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_58adfaa4-02bd-4b64-89cc-395d6ee0f968_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Cloud filter\"},{\"version\":\"7.13.4\",\"type\":\"map\",\"gridData\":{\"x\":0,\"y\":6,\"w\":24,\"h\":15,\"i\":\"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2\"},\"panelIndex\":\"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"description\":\"\",\"layerListJSON\":\"[{\\\"sourceDescriptor\\\":{\\\"type\\\":\\\"EMS_TMS\\\",\\\"isAutoSelect\\\":true},\\\"id\\\":\\\"99115329-feb3-42c6-b426-dff8bd1e1b3a\\\",\\\"label\\\":null,\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":1,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"TILE\\\"},\\\"type\\\":\\\"VECTOR_TILE\\\"},{\\\"sourceDescriptor\\\":{\\\"indexPatternId\\\":\\\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\\\",\\\"geoField\\\":\\\"geoip.location\\\",\\\"filterByMapBounds\\\":true,\\\"scalingType\\\":\\\"CLUSTERS\\\",\\\"id\\\":\\\"5728ef62-6dc0-4b27-b048-7ffda088d201\\\",\\\"type\\\":\\\"ES_SEARCH\\\",\\\"applyGlobalQuery\\\":true,\\\"applyGlobalTime\\\":true,\\\"tooltipProperties\\\":[],\\\"sortField\\\":\\\"\\\",\\\"sortOrder\\\":\\\"desc\\\",\\\"topHitsSplitField\\\":\\\"\\\",\\\"topHitsSize\\\":1},\\\"id\\\":\\\"04fbaa00-b4ba-40db-b46e-8a6dd6d12d04\\\",\\\"label\\\":\\\"success-connect-from-ip\\\",\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":0.91,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"VECTOR\\\",\\\"properties\\\":{\\\"icon\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"value\\\":\\\"marker\\\"}},\\\"fillColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#54B399\\\"}},\\\"lineColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#41937c\\\"}},\\\"lineWidth\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":1}},\\\"iconSize\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":6}},\\\"iconOrientation\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"orientation\\\":0}},\\\"labelText\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"value\\\":\\\"\\\"}},\\\"labelColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#000000\\\"}},\\\"labelSize\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":14}},\\\"labelBorderColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#FFFFFF\\\"}},\\\"symbolizeAs\\\":{\\\"options\\\":{\\\"value\\\":\\\"circle\\\"}},\\\"labelBorderSize\\\":{\\\"options\\\":{\\\"size\\\":\\\"SMALL\\\"}}},\\\"isTimeAware\\\":true},\\\"type\\\":\\\"BLENDED_VECTOR\\\",\\\"joins\\\":[],\\\"query\\\":{\\\"query\\\":\\\"not responseStatus.status : Failure\\\",\\\"language\\\":\\\"kuery\\\"}}]\",\"mapStateJSON\":\"{\\\"zoom\\\":1.41,\\\"center\\\":{\\\"lon\\\":64.80962,\\\"lat\\\":57.04692},\\\"timeFilters\\\":{\\\"from\\\":\\\"now-15d\\\",\\\"to\\\":\\\"now\\\"},\\\"refreshConfig\\\":{\\\"isPaused\\\":true,\\\"interval\\\":0},\\\"query\\\":{\\\"query\\\":\\\"event.dataset : yandexcloud.k8s_audit_logs and source.ip : * and not responseStatus.status : Failure\\\",\\\"language\\\":\\\"kuery\\\"},\\\"filters\\\":[],\\\"settings\\\":{\\\"autoFitToDataBounds\\\":false,\\\"backgroundColor\\\":\\\"#ffffff\\\",\\\"disableInteractive\\\":false,\\\"disableTooltipControl\\\":false,\\\"hideToolbarOverlay\\\":false,\\\"hideLayerControl\\\":false,\\\"hideViewControl\\\":false,\\\"initialLocation\\\":\\\"LAST_SAVED_LOCATION\\\",\\\"fixedLocation\\\":{\\\"lat\\\":0,\\\"lon\\\":0,\\\"zoom\\\":2},\\\"browserLocation\\\":{\\\"zoom\\\":2},\\\"maxZoom\\\":24,\\\"minZoom\\\":0,\\\"showScaleControl\\\":false,\\\"showSpatialFilters\\\":true,\\\"spatialFiltersAlpa\\\":0.3,\\\"spatialFiltersFillColor\\\":\\\"#DA8B45\\\",\\\"spatialFiltersLineColor\\\":\\\"#DA8B45\\\"}}\",\"uiStateJSON\":\"{\\\"isLayerTOCOpen\\\":true,\\\"openTOCDetails\\\":[]}\"},\"mapCenter\":{\"lat\":57.21062,\"lon\":78.63166,\"zoom\":1.41},\"mapBuffer\":{\"minLon\":-141.24608,\"minLat\":-9.879624999999994,\"maxLon\":298.50939999999997,\"maxLat\":104.90343499999999},\"isLayerTOCOpen\":false,\"openTOCDetails\":[],\"hiddenLayers\":[],\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"Connect from ip\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":6,\"w\":24,\"h\":15,\"i\":\"913c8496-3a96-4fa5-b029-20b53d929446\"},\"panelIndex\":\"913c8496-3a96-4fa5-b029-20b53d929446\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"201765c7-9d49-4931-954d-047211d60c67\":{\"columns\":{\"cb3cdcfa-2372-4b24-a37d-b7594d6ac42f\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"485e13ff-3e64-4c34-ac75-e421aa3cc191\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"485e13ff-3e64-4c34-ac75-e421aa3cc191\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"},\"2cdf7d8d-6a13-4283-a596-68e7230c6bad\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"485e13ff-3e64-4c34-ac75-e421aa3cc191\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}}},\"columnOrder\":[\"cb3cdcfa-2372-4b24-a37d-b7594d6ac42f\",\"2cdf7d8d-6a13-4283-a596-68e7230c6bad\",\"485e13ff-3e64-4c34-ac75-e421aa3cc191\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_horizontal\",\"layers\":[{\"layerId\":\"201765c7-9d49-4931-954d-047211d60c67\",\"seriesType\":\"bar_horizontal\",\"xAccessor\":\"2cdf7d8d-6a13-4283-a596-68e7230c6bad\",\"splitAccessor\":\"cb3cdcfa-2372-4b24-a37d-b7594d6ac42f\",\"accessors\":[\"485e13ff-3e64-4c34-ac75-e421aa3cc191\"]}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-201765c7-9d49-4931-954d-047211d60c67\"}]},\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"OPA-gatekeeper-detections(only enforce)\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":21,\"w\":13,\"h\":9,\"i\":\"bb843cd6-969c-4aae-a37c-978d2fe0bbef\"},\"panelIndex\":\"bb843cd6-969c-4aae-a37c-978d2fe0bbef\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"d401535b-665e-442b-a312-9edd3c1ebcc0\":{\"columns\":{\"61acda83-5d64-453e-9ca1-16b129cc2b42\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"fac0953d-82d6-4ef6-955a-8bc79bccf002\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"ece5248d-0578-44e8-b245-bc2de86f37f4\":{\"label\":\"Top values of verb.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"verb.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"fac0953d-82d6-4ef6-955a-8bc79bccf002\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"fac0953d-82d6-4ef6-955a-8bc79bccf002\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"61acda83-5d64-453e-9ca1-16b129cc2b42\",\"ece5248d-0578-44e8-b245-bc2de86f37f4\",\"fac0953d-82d6-4ef6-955a-8bc79bccf002\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\",\"showSingleSeries\":false},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_horizontal_stacked\",\"layers\":[{\"palette\":{\"type\":\"palette\",\"name\":\"default\"},\"layerId\":\"d401535b-665e-442b-a312-9edd3c1ebcc0\",\"seriesType\":\"bar_horizontal_stacked\",\"xAccessor\":\"ece5248d-0578-44e8-b245-bc2de86f37f4\",\"splitAccessor\":\"61acda83-5d64-453e-9ca1-16b129cc2b42\",\"accessors\":[\"fac0953d-82d6-4ef6-955a-8bc79bccf002\"]}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseStatus.reason : Forbidden and not user.name : (system*node* or *gatekeeper* or *kyverno* or *proxy* or *scheduler* or *anonymous* or *csi* or *controller*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-d401535b-665e-442b-a312-9edd3c1ebcc0\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Unauthorized events\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":13,\"y\":21,\"w\":11,\"h\":9,\"i\":\"4d0ab419-47d3-48bd-9e5e-93a563e20aee\"},\"panelIndex\":\"4d0ab419-47d3-48bd-9e5e-93a563e20aee\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"b5bee140-5f01-4de3-9395-d279acb203dc\":{\"columns\":{\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"4eda6d99-05c3-4ab8-a294-4632c9442157\":{\"label\":\"Top values of requestObject.kind.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"requestObject.kind.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\",\"4eda6d99-05c3-4ab8-a294-4632c9442157\",\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":false,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"layerId\":\"b5bee140-5f01-4de3-9395-d279acb203dc\",\"accessors\":[\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"],\"position\":\"top\",\"seriesType\":\"bar_stacked\",\"showGridlines\":false,\"xAccessor\":\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\",\"splitAccessor\":\"4eda6d99-05c3-4ab8-a294-4632c9442157\"}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and requestObject.roleRef.name.keyword:(cluster-admin or admin) and objectRef.resource.keyword: (clusterrolebindings or rolebinding) and verb : create and not responseObject.reason : AlreadyExists\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-b5bee140-5f01-4de3-9395-d279acb203dc\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Assign Cluster-admin/admin\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":21,\"w\":13,\"h\":17,\"i\":\"bbfefc52-8578-4755-84b5-1f18783f51d4\"},\"panelIndex\":\"bbfefc52-8578-4755-84b5-1f18783f51d4\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"fd0565e3-d5dd-490a-bd9d-2c0cd901a5c3\":{\"columns\":{\"80c15f05-a37b-4c19-a89b-0be5c9847ae0\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"},\"4a5a33db-17c3-4477-a71d-05620894f6f9\":{\"label\":\"Top values of folder_id.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"folder_id.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"80c15f05-a37b-4c19-a89b-0be5c9847ae0\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}}},\"columnOrder\":[\"4a5a33db-17c3-4477-a71d-05620894f6f9\",\"80c15f05-a37b-4c19-a89b-0be5c9847ae0\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"fd0565e3-d5dd-490a-bd9d-2c0cd901a5c3\",\"groups\":[\"4a5a33db-17c3-4477-a71d-05620894f6f9\",\"4a5a33db-17c3-4477-a71d-05620894f6f9\",\"4a5a33db-17c3-4477-a71d-05620894f6f9\",\"4a5a33db-17c3-4477-a71d-05620894f6f9\"],\"metric\":\"80c15f05-a37b-4c19-a89b-0be5c9847ae0\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2,\"legendPosition\":\"right\"}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-fd0565e3-d5dd-490a-bd9d-2c0cd901a5c3\"}]},\"enhancements\":{\"dynamicActions\":{\"events\":[{\"eventId\":\"e254cc8a-f8d7-45b5-8f64-d2f448a0af10\",\"triggers\":[\"VALUE_CLICK_TRIGGER\"],\"action\":{\"factoryId\":\"URL_DRILLDOWN\",\"name\":\"Look at yandex-cloud console\",\"config\":{\"url\":{\"template\":\"https://console.cloud.yandex.ru/folders/{{event.value}}\"},\"openInNewTab\":true,\"encodeUrl\":true}}}]}},\"hidePanelTitles\":false},\"title\":\"OPA-detections by Folder_id\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":37,\"y\":21,\"w\":5,\"h\":9,\"i\":\"e1d27ba4-c45c-431e-933b-0a174c71d48c\"},\"panelIndex\":\"e1d27ba4-c45c-431e-933b-0a174c71d48c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"metric\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"type\":\"metric\",\"metric\":{\"percentageMode\":false,\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"metricColorMode\":\"Labels\",\"colorsRange\":[{\"from\":0,\"to\":1},{\"from\":1,\"to\":100000}],\"labels\":{\"show\":true},\"invertColors\":false,\"style\":{\"bgFill\":\"#000\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":76}}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"OPA-Gatekeeper-Detections\"},\"schema\":\"metric\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":42,\"y\":21,\"w\":6,\"h\":9,\"i\":\"93384633-a71f-4441-8beb-cbb5cab7c514\"},\"panelIndex\":\"93384633-a71f-4441-8beb-cbb5cab7c514\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"goal\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"isDisplayWarning\":true,\"type\":\"gauge\",\"gauge\":{\"verticalSplit\":false,\"autoExtend\":false,\"percentageMode\":false,\"gaugeType\":\"Arc\",\"gaugeStyle\":\"Full\",\"backStyle\":\"Full\",\"orientation\":\"vertical\",\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"gaugeColorMode\":\"None\",\"colorsRange\":[{\"from\":0,\"to\":1}],\"invertColors\":false,\"labels\":{\"show\":false,\"color\":\"black\"},\"scale\":{\"show\":false,\"labels\":false,\"color\":\"rgba(105,112,125,0.2)\",\"width\":2},\"type\":\"meter\",\"style\":{\"bgFill\":\"rgba(105,112,125,0.2)\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":60}}},\"uiState\":{\"vis\":{\"defaultColors\":{\"0 - 1\":\"rgb(0,104,55)\"}}},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Delete-OPA-Gatekeeper \"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"verb.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"group\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.name.keyword: gatekeeper-validating-webhook-configuration and verb : delete\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":30,\"w\":17,\"h\":8,\"i\":\"9e45767a-451f-48a1-b421-17738c299cd9\"},\"panelIndex\":\"9e45767a-451f-48a1-b421-17738c299cd9\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"pie\",\"params\":{\"type\":\"pie\",\"addTooltip\":true,\"addLegend\":true,\"legendPosition\":\"left\",\"isDonut\":true,\"labels\":{\"show\":true,\"values\":false,\"last_level\":true,\"truncate\":100}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"NetworkPolicy:create/delete/update\"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"responseObject.metadata.selfLink.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"segment\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and requestObject.kind.keyword: (NetworkPolicy or CiliumNetworkPolicy) and verb : (create or update or delete)\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"NetworkPolicy:create/delete/update\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":17,\"y\":30,\"w\":7,\"h\":8,\"i\":\"398a8ba3-0ffc-40ee-90e1-c1547938d171\"},\"panelIndex\":\"398a8ba3-0ffc-40ee-90e1-c1547938d171\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"c76f346d-f6d6-4f9e-acb8-f5dde656e783\":{\"columns\":{\"b659aca0-0f1f-4408-8cea-1eea232bfe93\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"b659aca0-0f1f-4408-8cea-1eea232bfe93\",\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"c76f346d-f6d6-4f9e-acb8-f5dde656e783\",\"groups\":[\"b659aca0-0f1f-4408-8cea-1eea232bfe93\"],\"metric\":\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"default\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.namespace.keyword: kube-system and verb : create and objectRef.resource.keyword: pods and objectRef.name : * and not objectRef.name : (*calico* or *dns* or *npd* or *proxy* or *metrics* or *csi* or *masq*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-c76f346d-f6d6-4f9e-acb8-f5dde656e783\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Create pod in kube-system\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":37,\"y\":30,\"w\":11,\"h\":8,\"i\":\"ad54fa9e-40c4-4c74-85c2-543efeef1004\"},\"panelIndex\":\"ad54fa9e-40c4-4c74-85c2-543efeef1004\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"07f20f17-d0d3-4d63-b030-7980f218c412\":{\"columns\":{\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\":{\"label\":\"Top values of objectRef.resource.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.resource.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\",\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"palette\":{\"type\":\"palette\",\"name\":\"negative\"},\"layers\":[{\"layerId\":\"07f20f17-d0d3-4d63-b030-7980f218c412\",\"groups\":[\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\"],\"metric\":\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.apiGroup.keyword: constraints.gatekeeper.sh and (verb : delete or update) and not user.name : \\\"system:serviceaccount:gatekeeper-system:gatekeeper-admin\\\"\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-07f20f17-d0d3-4d63-b030-7980f218c412\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"OPA-constraint-delete/update\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":38,\"w\":17,\"h\":7,\"i\":\"7a0555be-d5f3-4aeb-9159-f48d7264d40c\"},\"panelIndex\":\"7a0555be-d5f3-4aeb-9159-f48d7264d40c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"pie\",\"params\":{\"type\":\"pie\",\"addTooltip\":true,\"addLegend\":true,\"legendPosition\":\"left\",\"isDonut\":true,\"labels\":{\"show\":true,\"values\":false,\"last_level\":true,\"truncate\":100}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Exec to container\"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"objectRef.name.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"segment\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.subresource.keyword: exec\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{},\"vis\":{\"legendOpen\":true}},\"title\":\"Exec to container\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":17,\"y\":38,\"w\":16,\"h\":7,\"i\":\"b6d054cd-bca1-49a6-affb-7b115b76af5a\"},\"panelIndex\":\"b6d054cd-bca1-49a6-affb-7b115b76af5a\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsDatatable\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"18ea127c-2267-4d24-9893-d3ef85942514\":{\"columns\":{\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\":{\"label\":\"Unique count of user.name.keyword\",\"dataType\":\"number\",\"operationType\":\"unique_count\",\"scale\":\"ratio\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":false},\"c94a437d-970d-4c55-89a7-499d47032bc8\":{\"label\":\"ServiceAccounts\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":15,\"orderBy\":{\"type\":\"column\",\"columnId\":\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false},\"customLabel\":true}},\"columnOrder\":[\"c94a437d-970d-4c55-89a7-499d47032bc8\",\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"layerId\":\"18ea127c-2267-4d24-9893-d3ef85942514\",\"columns\":[{\"isTransposed\":false,\"columnId\":\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\",\"hidden\":true},{\"columnId\":\"c94a437d-970d-4c55-89a7-499d47032bc8\",\"isTransposed\":false,\"alignment\":\"left\"}]},\"query\":{\"query\":\"user.name : *serviceaccount*\",\"language\":\"kuery\"},\"filters\":[{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:certificate-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-0\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:certificate-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:coredns\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-1\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:coredns\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:cronjob-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-2\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:cronjob-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:generic-garbage-collector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-3\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:generic-garbage-collector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:job-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-4\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:job-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:endpointslice-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-5\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:endpointslice-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:endpoint-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-6\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:endpoint-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:calico-node\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-7\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:calico-node\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:kube-proxy\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-8\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:kube-proxy\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"alias\":null,\"negate\":true,\"disabled\":false,\"type\":\"phrase\",\"key\":\"objectRef.namespace\",\"params\":{\"query\":\"kube-system\"},\"indexRefName\":\"filter-index-pattern-9\"},\"query\":{\"match_phrase\":{\"objectRef.namespace\":\"kube-system\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:kube-dns-autoscaler\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-10\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:kube-dns-autoscaler\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:daemon-set-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-11\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:daemon-set-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:metrics-server\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-12\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:metrics-server\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:pod-garbage-collector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-13\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:pod-garbage-collector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:node-problem-detector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-14\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:node-problem-detector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:typha-cpha\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-15\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:typha-cpha\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:service-account-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-16\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:service-account-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:resourcequota-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-17\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:resourcequota-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:replicaset-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-18\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:replicaset-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:namespace-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-19\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:namespace-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:typha-cpva\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-20\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:typha-cpva\"}},\"$state\":{\"store\":\"appState\"}}]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-18ea127c-2267-4d24-9893-d3ef85942514\"},{\"name\":\"filter-index-pattern-0\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-1\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-2\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-3\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-4\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-5\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-6\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-7\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-8\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-9\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-10\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-11\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-12\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-13\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-14\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-15\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-16\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-17\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-18\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-19\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-20\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"}]},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":33,\"y\":38,\"w\":15,\"h\":7,\"i\":\"1d2c60a9-c570-45b0-8f49-e577c74e9ce3\"},\"panelIndex\":\"1d2c60a9-c570-45b0-8f49-e577c74e9ce3\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsDatatable\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"8e37793f-a2a3-48b0-a4b5-dda752e958b9\":{\"columns\":{\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\":{\"label\":\"YC Admins\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false},\"customLabel\":true},\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\",\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"columns\":[{\"isTransposed\":false,\"columnId\":\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\"},{\"isTransposed\":false,\"columnId\":\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\",\"hidden\":true}],\"layerId\":\"8e37793f-a2a3-48b0-a4b5-dda752e958b9\"},\"query\":{\"query\":\"user.groups.keyword: *admin*\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-8e37793f-a2a3-48b0-a4b5-dda752e958b9\"}]},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":45,\"w\":17,\"h\":11,\"i\":\"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb\"},\"panelIndex\":\"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\":{\"columns\":{\"71c8af00-7864-4ca6-a20d-0e43a80da354\":{\"label\":\"Top values of requestObject.status.containerStatuses.image.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"requestObject.status.containerStatuses.image.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"71c8af00-7864-4ca6-a20d-0e43a80da354\",\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\",\"groups\":[\"71c8af00-7864-4ca6-a20d-0e43a80da354\"],\"metric\":\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and not requestObject.status.containerStatuses.image.keyword: *cr.yandex/* and requestObject.status.containerStatuses.containerID : *docker* and verb : patch and not requestObject.status.containerStatuses.image.keyword: (*falco* or *openpolicyagent* or *kyverno* or *k8s.gcr.io*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Images not from YC CR\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":17,\"y\":45,\"w\":16,\"h\":11,\"i\":\"611221c8-59e6-4ea2-bfdb-bbb53f646772\"},\"panelIndex\":\"611221c8-59e6-4ea2-bfdb-bbb53f646772\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"d7984002-15d6-4e61-b30e-d34bc0a066ea\":{\"columns\":{\"0c0b50e4-e53e-4ef3-a0d2-ee5cc416762f\":{\"label\":\"Top values of objectRef.namespace.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.namespace.keyword\",\"isBucketed\":true,\"params\":{\"size\":10,\"orderBy\":{\"type\":\"column\",\"columnId\":\"3b8ab08b-e01f-407b-976f-4f073207dde4\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"3b8ab08b-e01f-407b-976f-4f073207dde4\":{\"label\":\"Unique count of objectRef.namespace.keyword\",\"dataType\":\"number\",\"operationType\":\"unique_count\",\"scale\":\"ratio\",\"sourceField\":\"objectRef.namespace.keyword\",\"isBucketed\":false}},\"columnOrder\":[\"0c0b50e4-e53e-4ef3-a0d2-ee5cc416762f\",\"3b8ab08b-e01f-407b-976f-4f073207dde4\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"palette\":{\"type\":\"palette\",\"name\":\"cool\"},\"layers\":[{\"layerId\":\"d7984002-15d6-4e61-b30e-d34bc0a066ea\",\"groups\":[\"0c0b50e4-e53e-4ef3-a0d2-ee5cc416762f\",\"0c0b50e4-e53e-4ef3-a0d2-ee5cc416762f\"],\"metric\":\"3b8ab08b-e01f-407b-976f-4f073207dde4\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"default\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-d7984002-15d6-4e61-b30e-d34bc0a066ea\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Namespaces\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":33,\"y\":45,\"w\":15,\"h\":11,\"i\":\"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c\"},\"panelIndex\":\"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"b770c4de-625b-4d6b-9cd2-caf7372d5d6a\":{\"columns\":{\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\":{\"label\":\"Top values of event.dataset.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"event.dataset.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"8a74805c-8582-46c0-8d53-920a919f9b59\":{\"label\":\"stageTimestamp\",\"dataType\":\"date\",\"operationType\":\"date_histogram\",\"sourceField\":\"stageTimestamp\",\"isBucketed\":true,\"scale\":\"interval\",\"params\":{\"interval\":\"auto\"}},\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\",\"8a74805c-8582-46c0-8d53-920a919f9b59\",\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"top\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"layerId\":\"b770c4de-625b-4d6b-9cd2-caf7372d5d6a\",\"accessors\":[\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"],\"position\":\"top\",\"seriesType\":\"bar_stacked\",\"showGridlines\":false,\"xAccessor\":\"8a74805c-8582-46c0-8d53-920a919f9b59\",\"palette\":{\"type\":\"palette\",\"name\":\"temperature\"},\"splitAccessor\":\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\"}]},\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-b770c4de-625b-4d6b-9cd2-caf7372d5d6a\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Events-by-time\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":56,\"w\":48,\"h\":12,\"i\":\"46f514cc-dac0-4727-9416-ea72ea7a7ed6\"},\"panelIndex\":\"46f514cc-dac0-4727-9416-ea72ea7a7ed6\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"f30699c9-d583-4db7-a489-b1e1ff2b86fe\":{\"columns\":{\"0ebea67a-d401-40b8-8e82-535c4849014e\":{\"label\":\"Top values of rule.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"rule.keyword\",\"isBucketed\":true,\"params\":{\"size\":15,\"orderBy\":{\"type\":\"column\",\"columnId\":\"a51a05c8-5849-473d-b77c-2fb8eb4cc331\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"a51a05c8-5849-473d-b77c-2fb8eb4cc331\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"0ebea67a-d401-40b8-8e82-535c4849014e\",\"a51a05c8-5849-473d-b77c-2fb8eb4cc331\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"f30699c9-d583-4db7-a489-b1e1ff2b86fe\",\"groups\":[\"0ebea67a-d401-40b8-8e82-535c4849014e\"],\"metric\":\"a51a05c8-5849-473d-b77c-2fb8eb4cc331\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_falco\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"4c290ba0-fdad-11eb-b912-d99e9986f72b\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"4c290ba0-fdad-11eb-b912-d99e9986f72b\",\"name\":\"indexpattern-datasource-layer-f30699c9-d583-4db7-a489-b1e1ff2b86fe\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Falco alerts\"},{\"version\":\"7.13.4\",\"type\":\"search\",\"gridData\":{\"x\":0,\"y\":68,\"w\":48,\"h\":17,\"i\":\"ed79a50e-9a59-475a-8e0c-d41b0cb84acd\"},\"panelIndex\":\"ed79a50e-9a59-475a-8e0c-d41b0cb84acd\",\"embeddableConfig\":{\"enhancements\":{}},\"panelRefName\":\"panel_ed79a50e-9a59-475a-8e0c-d41b0cb84acd\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":25,\"y\":85,\"w\":23,\"h\":9,\"i\":\"0492dbd1-815d-46f2-82b9-1917fddcd8a7\"},\"panelIndex\":\"0492dbd1-815d-46f2-82b9-1917fddcd8a7\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"889ef61e-c27c-49b4-97b5-0bcad36eb8c3\":{\"columns\":{\"6f154ebc-1387-4dd2-a440-5760b39ee994\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"8d5794d3-a850-4779-b32f-3dc2edfa855a\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"93aed031-2523-40b2-a8ae-ec6fe6b06c8f\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"8d5794d3-a850-4779-b32f-3dc2edfa855a\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"8d5794d3-a850-4779-b32f-3dc2edfa855a\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"6f154ebc-1387-4dd2-a440-5760b39ee994\",\"93aed031-2523-40b2-a8ae-ec6fe6b06c8f\",\"8d5794d3-a850-4779-b32f-3dc2edfa855a\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_horizontal\",\"layers\":[{\"layerId\":\"889ef61e-c27c-49b4-97b5-0bcad36eb8c3\",\"accessors\":[\"8d5794d3-a850-4779-b32f-3dc2edfa855a\"],\"position\":\"top\",\"seriesType\":\"bar_horizontal\",\"showGridlines\":false,\"xAccessor\":\"6f154ebc-1387-4dd2-a440-5760b39ee994\",\"splitAccessor\":\"93aed031-2523-40b2-a8ae-ec6fe6b06c8f\"}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validate.kyverno.svc\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-889ef61e-c27c-49b4-97b5-0bcad36eb8c3\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"kyverno-detections(only enforce)\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":25,\"y\":94,\"w\":12,\"h\":10,\"i\":\"c0743ff5-8470-469a-86cf-5d33d45deb34\"},\"panelIndex\":\"c0743ff5-8470-469a-86cf-5d33d45deb34\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"411026a7-eff6-47fa-9e93-bff4143c7544\":{\"columns\":{\"2858fd65-2d0f-4550-8c3c-52fdbc2209fe\":{\"label\":\"Top values of cluster_id.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"cluster_id.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"b448e6ad-2ac4-459a-a76f-a505f6c9fbe3\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"b448e6ad-2ac4-459a-a76f-a505f6c9fbe3\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"2858fd65-2d0f-4550-8c3c-52fdbc2209fe\",\"b448e6ad-2ac4-459a-a76f-a505f6c9fbe3\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"411026a7-eff6-47fa-9e93-bff4143c7544\",\"groups\":[\"2858fd65-2d0f-4550-8c3c-52fdbc2209fe\"],\"metric\":\"b448e6ad-2ac4-459a-a76f-a505f6c9fbe3\",\"numberDisplay\":\"percent\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validate.kyverno.svc\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-411026a7-eff6-47fa-9e93-bff4143c7544\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"kyverno-detections by Cluster_id\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":37,\"y\":94,\"w\":5,\"h\":10,\"i\":\"557d758a-f0b2-4d4f-aebd-a32f8cf70b9c\"},\"panelIndex\":\"557d758a-f0b2-4d4f-aebd-a32f8cf70b9c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"metric\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"type\":\"metric\",\"metric\":{\"percentageMode\":false,\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"metricColorMode\":\"Labels\",\"colorsRange\":[{\"from\":0,\"to\":1},{\"from\":1,\"to\":100000}],\"labels\":{\"show\":true},\"invertColors\":false,\"style\":{\"bgFill\":\"#000\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":76}}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Kyverno-Detections\"},\"schema\":\"metric\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validate.kyverno.svc\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":42,\"y\":94,\"w\":6,\"h\":10,\"i\":\"42a0de3a-e9c3-4f34-bf5a-82244b6cf497\"},\"panelIndex\":\"42a0de3a-e9c3-4f34-bf5a-82244b6cf497\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"goal\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"isDisplayWarning\":true,\"type\":\"gauge\",\"gauge\":{\"verticalSplit\":false,\"autoExtend\":false,\"percentageMode\":false,\"gaugeType\":\"Arc\",\"gaugeStyle\":\"Full\",\"backStyle\":\"Full\",\"orientation\":\"vertical\",\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"gaugeColorMode\":\"None\",\"colorsRange\":[{\"from\":0,\"to\":1}],\"invertColors\":false,\"labels\":{\"show\":false,\"color\":\"black\"},\"scale\":{\"show\":false,\"labels\":false,\"color\":\"rgba(105,112,125,0.2)\",\"width\":2},\"type\":\"meter\",\"style\":{\"bgFill\":\"rgba(105,112,125,0.2)\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":60}}},\"uiState\":{\"vis\":{\"defaultColors\":{\"0 - 1\":\"rgb(0,104,55)\"}}},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Delete-Kyverno\"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"verb.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"group\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.name.keyword: kyverno-resource-validating-webhook-cfg and verb : delete \",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":37,\"y\":104,\"w\":11,\"h\":8,\"i\":\"a79397e8-8420-4be0-903e-23c664992a25\"},\"panelIndex\":\"a79397e8-8420-4be0-903e-23c664992a25\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"07f20f17-d0d3-4d63-b030-7980f218c412\":{\"columns\":{\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"},\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}}},\"columnOrder\":[\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\",\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"palette\":{\"type\":\"palette\",\"name\":\"negative\"},\"layers\":[{\"layerId\":\"07f20f17-d0d3-4d63-b030-7980f218c412\",\"groups\":[\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\",\"f7cf57b8-95d1-4801-ad75-10569cf4bca4\"],\"metric\":\"a0efc17d-8c48-4bec-83a3-05dbf24449e5\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.apiGroup.keyword: kyverno.io and (verb : delete or update) and objectRef.resource.keyword: *policies\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-07f20f17-d0d3-4d63-b030-7980f218c412\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Kyverno-delete/update\"}]","timeRestore":false,"title":"k8s-dashboard-and-opa","version":1},"coreMigrationVersion":"7.13.4","id":"642ffd90-fcbc-11eb-b912-d99e9986f72b","migrationVersion":{"dashboard":"7.13.1"},"references":[{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"df4da863-2133-4560-82f3-5c126ac27f14:control_df4da863-2133-4560-82f3-5c126ac27f14_0_index_pattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"58adfaa4-02bd-4b64-89cc-395d6ee0f968:control_58adfaa4-02bd-4b64-89cc-395d6ee0f968_0_index_pattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2:layer_1_source_index_pattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"913c8496-3a96-4fa5-b029-20b53d929446:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"913c8496-3a96-4fa5-b029-20b53d929446:indexpattern-datasource-layer-201765c7-9d49-4931-954d-047211d60c67","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"bb843cd6-969c-4aae-a37c-978d2fe0bbef:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"bb843cd6-969c-4aae-a37c-978d2fe0bbef:indexpattern-datasource-layer-d401535b-665e-442b-a312-9edd3c1ebcc0","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"4d0ab419-47d3-48bd-9e5e-93a563e20aee:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"4d0ab419-47d3-48bd-9e5e-93a563e20aee:indexpattern-datasource-layer-b5bee140-5f01-4de3-9395-d279acb203dc","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"bbfefc52-8578-4755-84b5-1f18783f51d4:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"bbfefc52-8578-4755-84b5-1f18783f51d4:indexpattern-datasource-layer-fd0565e3-d5dd-490a-bd9d-2c0cd901a5c3","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"e1d27ba4-c45c-431e-933b-0a174c71d48c:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"93384633-a71f-4441-8beb-cbb5cab7c514:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"9e45767a-451f-48a1-b421-17738c299cd9:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"398a8ba3-0ffc-40ee-90e1-c1547938d171:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"398a8ba3-0ffc-40ee-90e1-c1547938d171:indexpattern-datasource-layer-c76f346d-f6d6-4f9e-acb8-f5dde656e783","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"ad54fa9e-40c4-4c74-85c2-543efeef1004:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"ad54fa9e-40c4-4c74-85c2-543efeef1004:indexpattern-datasource-layer-07f20f17-d0d3-4d63-b030-7980f218c412","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"7a0555be-d5f3-4aeb-9159-f48d7264d40c:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:indexpattern-datasource-layer-18ea127c-2267-4d24-9893-d3ef85942514","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-0","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-1","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-2","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-3","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-4","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-5","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-6","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-7","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-8","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-9","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-10","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-11","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-12","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-13","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-14","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-15","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-16","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-17","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-18","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-19","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"b6d054cd-bca1-49a6-affb-7b115b76af5a:filter-index-pattern-20","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"1d2c60a9-c570-45b0-8f49-e577c74e9ce3:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"1d2c60a9-c570-45b0-8f49-e577c74e9ce3:indexpattern-datasource-layer-8e37793f-a2a3-48b0-a4b5-dda752e958b9","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb:indexpattern-datasource-layer-f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"611221c8-59e6-4ea2-bfdb-bbb53f646772:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"611221c8-59e6-4ea2-bfdb-bbb53f646772:indexpattern-datasource-layer-d7984002-15d6-4e61-b30e-d34bc0a066ea","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c:indexpattern-datasource-layer-b770c4de-625b-4d6b-9cd2-caf7372d5d6a","type":"index-pattern"},{"id":"4c290ba0-fdad-11eb-b912-d99e9986f72b","name":"46f514cc-dac0-4727-9416-ea72ea7a7ed6:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"4c290ba0-fdad-11eb-b912-d99e9986f72b","name":"46f514cc-dac0-4727-9416-ea72ea7a7ed6:indexpattern-datasource-layer-f30699c9-d583-4db7-a489-b1e1ff2b86fe","type":"index-pattern"},{"id":"0a358990-fcd0-11eb-b912-d99e9986f72b","name":"ed79a50e-9a59-475a-8e0c-d41b0cb84acd:panel_ed79a50e-9a59-475a-8e0c-d41b0cb84acd","type":"search"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"0492dbd1-815d-46f2-82b9-1917fddcd8a7:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"0492dbd1-815d-46f2-82b9-1917fddcd8a7:indexpattern-datasource-layer-889ef61e-c27c-49b4-97b5-0bcad36eb8c3","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"c0743ff5-8470-469a-86cf-5d33d45deb34:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"c0743ff5-8470-469a-86cf-5d33d45deb34:indexpattern-datasource-layer-411026a7-eff6-47fa-9e93-bff4143c7544","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"557d758a-f0b2-4d4f-aebd-a32f8cf70b9c:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"42a0de3a-e9c3-4f34-bf5a-82244b6cf497:kibanaSavedObjectMeta.searchSourceJSON.index","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"a79397e8-8420-4be0-903e-23c664992a25:indexpattern-datasource-current-indexpattern","type":"index-pattern"},{"id":"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5","name":"a79397e8-8420-4be0-903e-23c664992a25:indexpattern-datasource-layer-07f20f17-d0d3-4d63-b030-7980f218c412","type":"index-pattern"}],"type":"dashboard","updated_at":"2021-08-15T11:01:33.321Z","version":"WzU5NDU4LDJd"}
{"exportedCount":1,"missingRefCount":0,"missingReferences":[]}
================================================
FILE: auditlogs/export-auditlogs-to-ELK_main/backup/last_backup/k8s_audit_dashboard-future.ndjson
================================================
{"attributes":{"description":"","hits":0,"kibanaSavedObjectMeta":{"searchSourceJSON":"{\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filter\":[]}"},"optionsJSON":"{\"hidePanelTitles\":false,\"syncColors\":true,\"useMargins\":true}","panelsJSON":"[{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":0,\"w\":48,\"h\":4,\"i\":\"ac6581bb-3b07-45af-b3d6-3c3e30b7fa0e\"},\"panelIndex\":\"ac6581bb-3b07-45af-b3d6-3c3e30b7fa0e\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"markdown\",\"params\":{\"fontSize\":21,\"openLinksInNewTab\":false,\"markdown\":\"Filters\"},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":true,\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":4,\"w\":12,\"h\":6,\"i\":\"df4da863-2133-4560-82f3-5c126ac27f14\"},\"panelIndex\":\"df4da863-2133-4560-82f3-5c126ac27f14\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1628927100713\",\"fieldName\":\"cluster_id.keyword\",\"parent\":\"\",\"label\":\"k8s-cluster_id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_df4da863-2133-4560-82f3-5c126ac27f14_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Cluster filter\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":12,\"y\":4,\"w\":12,\"h\":6,\"i\":\"58adfaa4-02bd-4b64-89cc-395d6ee0f968\"},\"panelIndex\":\"58adfaa4-02bd-4b64-89cc-395d6ee0f968\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1628927314788\",\"fieldName\":\"cloud_id.keyword\",\"parent\":\"\",\"label\":\"k8s-cloud_id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_58adfaa4-02bd-4b64-89cc-395d6ee0f968_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Cloud filter\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":24,\"y\":4,\"w\":12,\"h\":6,\"i\":\"7bd8bc93-77ba-4de0-a3ff-46dfb58b9109\"},\"panelIndex\":\"7bd8bc93-77ba-4de0-a3ff-46dfb58b9109\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1629308709541\",\"fieldName\":\"folder_id.keyword\",\"parent\":\"\",\"label\":\"k8s-folder_id\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_7bd8bc93-77ba-4de0-a3ff-46dfb58b9109_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"Folder filter\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":36,\"y\":4,\"w\":12,\"h\":6,\"i\":\"ff5a5c53-c294-4c2b-ad00-3011d042dbcb\"},\"panelIndex\":\"ff5a5c53-c294-4c2b-ad00-3011d042dbcb\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"input_control_vis\",\"params\":{\"controls\":[{\"id\":\"1629308369258\",\"fieldName\":\"objectRef.namespace.keyword\",\"parent\":\"\",\"label\":\"k8s-namespace\",\"type\":\"list\",\"options\":{\"type\":\"terms\",\"multiselect\":true,\"dynamicOptions\":true,\"size\":5,\"order\":\"desc\"},\"indexPatternRefName\":\"control_ff5a5c53-c294-4c2b-ad00-3011d042dbcb_0_index_pattern\"}],\"updateFiltersOnChange\":false,\"useTimeFilter\":false,\"pinFilters\":false},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"Namespace filter\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":10,\"w\":12,\"h\":4,\"i\":\"5c09dead-7faf-4100-8f5a-7dec81dfcae3\"},\"panelIndex\":\"5c09dead-7faf-4100-8f5a-7dec81dfcae3\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\":{\"columns\":{\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\":{\"label\":\"Top values of cluster_url.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"cluster_url.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"76b4703c-15ec-48d9-a55f-4f8b9ad61473\":{\"label\":\"Top values of cluster_id.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"cluster_id.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"95107cd5-d71c-446d-be12-9ebe860cca6c\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"76b4703c-15ec-48d9-a55f-4f8b9ad61473\",\"95107cd5-d71c-446d-be12-9ebe860cca6c\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"treemap\",\"palette\":{\"type\":\"palette\",\"name\":\"cool\"},\"layers\":[{\"layerId\":\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\",\"groups\":[\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"76b4703c-15ec-48d9-a55f-4f8b9ad61473\"],\"metric\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"hide\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\"}]},\"enhancements\":{\"dynamicActions\":{\"events\":[{\"eventId\":\"e2434170-8807-4c59-823d-345d4f235e8d\",\"triggers\":[\"VALUE_CLICK_TRIGGER\"],\"action\":{\"factoryId\":\"URL_DRILLDOWN\",\"name\":\"Go to URL\",\"config\":{\"url\":{\"template\":\"{{event.value}}\"},\"openInNewTab\":true,\"encodeUrl\":true}}}]}},\"hidePanelTitles\":false},\"title\":\"Click on Cluster - go to YC concole\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":12,\"y\":10,\"w\":12,\"h\":4,\"i\":\"ba1c70dc-01c5-4fe3-8920-0dc8b0285e9f\"},\"panelIndex\":\"ba1c70dc-01c5-4fe3-8920-0dc8b0285e9f\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\":{\"columns\":{\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\":{\"label\":\"Top values of cloud.service.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"cloud.service.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"95107cd5-d71c-446d-be12-9ebe860cca6c\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"95107cd5-d71c-446d-be12-9ebe860cca6c\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"treemap\",\"palette\":{\"type\":\"palette\",\"name\":\"cool\"},\"layers\":[{\"layerId\":\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\",\"groups\":[\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\",\"2b8d71c3-ca49-4ab2-9315-33c0f7f9c79e\"],\"metric\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"hide\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\"}]},\"enhancements\":{\"dynamicActions\":{\"events\":[{\"eventId\":\"e2434170-8807-4c59-823d-345d4f235e8d\",\"triggers\":[\"VALUE_CLICK_TRIGGER\"],\"action\":{\"factoryId\":\"URL_DRILLDOWN\",\"name\":\"Go to URL\",\"config\":{\"url\":{\"template\":\"https://console.cloud.yandex.ru/\"},\"openInNewTab\":true,\"encodeUrl\":true}}}]}},\"hidePanelTitles\":false},\"title\":\"Click on Cloud - go to YC concole\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":10,\"w\":12,\"h\":4,\"i\":\"14c3ebb9-6592-4fb5-ab34-2a8ab1e0ab04\"},\"panelIndex\":\"14c3ebb9-6592-4fb5-ab34-2a8ab1e0ab04\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\":{\"columns\":{\"57147c6c-713f-4793-865a-1d671e3f141c\":{\"label\":\"Top values of folder_id.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"folder_id.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"95107cd5-d71c-446d-be12-9ebe860cca6c\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"57147c6c-713f-4793-865a-1d671e3f141c\",\"95107cd5-d71c-446d-be12-9ebe860cca6c\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"treemap\",\"palette\":{\"type\":\"palette\",\"name\":\"cool\"},\"layers\":[{\"layerId\":\"a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\",\"groups\":[\"57147c6c-713f-4793-865a-1d671e3f141c\"],\"metric\":\"95107cd5-d71c-446d-be12-9ebe860cca6c\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"hide\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-a9cdd464-b2ee-4c71-978e-8dc871e9a4f4\"}]},\"enhancements\":{\"dynamicActions\":{\"events\":[{\"eventId\":\"e2434170-8807-4c59-823d-345d4f235e8d\",\"triggers\":[\"VALUE_CLICK_TRIGGER\"],\"action\":{\"factoryId\":\"URL_DRILLDOWN\",\"name\":\"Go to URL\",\"config\":{\"url\":{\"template\":\"https://console.cloud.yandex.ru/folders/{{event.value}}\"},\"openInNewTab\":true,\"encodeUrl\":true}}}]}},\"hidePanelTitles\":false},\"title\":\"Click on Folder - go to YC concole\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":14,\"w\":48,\"h\":4,\"i\":\"7a112312-c097-4205-9f74-38913eae2169\"},\"panelIndex\":\"7a112312-c097-4205-9f74-38913eae2169\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"markdown\",\"params\":{\"fontSize\":21,\"openLinksInNewTab\":true,\"markdown\":\"Main k8s audit Events\"},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":true,\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"map\",\"gridData\":{\"x\":0,\"y\":18,\"w\":24,\"h\":15,\"i\":\"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2\"},\"panelIndex\":\"8fbf0969-9a83-426c-b42a-0e8d2a8f10c2\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"description\":\"\",\"layerListJSON\":\"[{\\\"sourceDescriptor\\\":{\\\"type\\\":\\\"EMS_TMS\\\",\\\"isAutoSelect\\\":false,\\\"id\\\":\\\"road_map\\\"},\\\"id\\\":\\\"99115329-feb3-42c6-b426-dff8bd1e1b3a\\\",\\\"label\\\":null,\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":1,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"TILE\\\"},\\\"type\\\":\\\"VECTOR_TILE\\\",\\\"areLabelsOnTop\\\":false},{\\\"sourceDescriptor\\\":{\\\"indexPatternId\\\":\\\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\\\",\\\"geoField\\\":\\\"geoip.location\\\",\\\"filterByMapBounds\\\":true,\\\"scalingType\\\":\\\"CLUSTERS\\\",\\\"id\\\":\\\"5728ef62-6dc0-4b27-b048-7ffda088d201\\\",\\\"type\\\":\\\"ES_SEARCH\\\",\\\"applyGlobalQuery\\\":true,\\\"applyGlobalTime\\\":true,\\\"tooltipProperties\\\":[],\\\"sortField\\\":\\\"\\\",\\\"sortOrder\\\":\\\"desc\\\",\\\"topHitsSplitField\\\":\\\"\\\",\\\"topHitsSize\\\":1},\\\"id\\\":\\\"04fbaa00-b4ba-40db-b46e-8a6dd6d12d04\\\",\\\"label\\\":\\\"success-connect-from-ip\\\",\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":0.91,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"VECTOR\\\",\\\"properties\\\":{\\\"icon\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"value\\\":\\\"marker\\\"}},\\\"fillColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#54B399\\\"}},\\\"lineColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#41937c\\\"}},\\\"lineWidth\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":1}},\\\"iconSize\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":6}},\\\"iconOrientation\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"orientation\\\":0}},\\\"labelText\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"value\\\":\\\"\\\"}},\\\"labelColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#000000\\\"}},\\\"labelSize\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"size\\\":14}},\\\"labelBorderColor\\\":{\\\"type\\\":\\\"STATIC\\\",\\\"options\\\":{\\\"color\\\":\\\"#FFFFFF\\\"}},\\\"symbolizeAs\\\":{\\\"options\\\":{\\\"value\\\":\\\"circle\\\"}},\\\"labelBorderSize\\\":{\\\"options\\\":{\\\"size\\\":\\\"SMALL\\\"}}},\\\"isTimeAware\\\":true},\\\"type\\\":\\\"BLENDED_VECTOR\\\",\\\"joins\\\":[],\\\"query\\\":{\\\"query\\\":\\\"not responseStatus.status : Failure\\\",\\\"language\\\":\\\"kuery\\\"}}]\",\"mapStateJSON\":\"{\\\"zoom\\\":1.41,\\\"center\\\":{\\\"lon\\\":78.63166,\\\"lat\\\":57.21062},\\\"timeFilters\\\":{\\\"from\\\":\\\"now-15d\\\",\\\"to\\\":\\\"now\\\"},\\\"refreshConfig\\\":{\\\"isPaused\\\":true,\\\"interval\\\":0},\\\"query\\\":{\\\"query\\\":\\\"event.dataset : yandexcloud.k8s_audit_logs and source.ip : * and not responseStatus.status : Failure\\\",\\\"language\\\":\\\"kuery\\\"},\\\"filters\\\":[],\\\"settings\\\":{\\\"autoFitToDataBounds\\\":false,\\\"backgroundColor\\\":\\\"#ffffff\\\",\\\"disableInteractive\\\":false,\\\"disableTooltipControl\\\":false,\\\"hideToolbarOverlay\\\":false,\\\"hideLayerControl\\\":false,\\\"hideViewControl\\\":false,\\\"initialLocation\\\":\\\"LAST_SAVED_LOCATION\\\",\\\"fixedLocation\\\":{\\\"lat\\\":0,\\\"lon\\\":0,\\\"zoom\\\":2},\\\"browserLocation\\\":{\\\"zoom\\\":2},\\\"maxZoom\\\":24,\\\"minZoom\\\":0,\\\"showScaleControl\\\":false,\\\"showSpatialFilters\\\":true,\\\"spatialFiltersAlpa\\\":0.3,\\\"spatialFiltersFillColor\\\":\\\"#DA8B45\\\",\\\"spatialFiltersLineColor\\\":\\\"#DA8B45\\\"}}\",\"uiStateJSON\":\"{\\\"isLayerTOCOpen\\\":true,\\\"openTOCDetails\\\":[]}\"},\"mapCenter\":{\"lat\":57.21062,\"lon\":78.63166,\"zoom\":1.41},\"mapBuffer\":{\"minLon\":-155.53415999999999,\"minLat\":-9.879624999999994,\"maxLon\":312.79748,\"maxLat\":104.90343499999999},\"isLayerTOCOpen\":false,\"openTOCDetails\":[],\"hiddenLayers\":[],\"enhancements\":{},\"hidePanelTitles\":false},\"title\":\"Connect from ip\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":18,\"w\":24,\"h\":10,\"i\":\"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c\"},\"panelIndex\":\"d36f938f-5c6a-4fa4-bc28-812f4bf74f9c\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"b770c4de-625b-4d6b-9cd2-caf7372d5d6a\":{\"columns\":{\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\":{\"label\":\"Top values of event.dataset.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"event.dataset.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"8a74805c-8582-46c0-8d53-920a919f9b59\":{\"label\":\"stageTimestamp\",\"dataType\":\"date\",\"operationType\":\"date_histogram\",\"sourceField\":\"stageTimestamp\",\"isBucketed\":true,\"scale\":\"interval\",\"params\":{\"interval\":\"auto\"}},\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\",\"8a74805c-8582-46c0-8d53-920a919f9b59\",\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"top\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"layerId\":\"b770c4de-625b-4d6b-9cd2-caf7372d5d6a\",\"accessors\":[\"075661dc-8a85-4c07-b7c7-2a6bb6745c70\"],\"position\":\"top\",\"seriesType\":\"bar_stacked\",\"showGridlines\":false,\"xAccessor\":\"8a74805c-8582-46c0-8d53-920a919f9b59\",\"palette\":{\"type\":\"palette\",\"name\":\"temperature\"},\"splitAccessor\":\"e0074aab-0bf9-478b-94c1-f607c5dbf1be\"}]},\"query\":{\"language\":\"kuery\",\"query\":\"\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-b770c4de-625b-4d6b-9cd2-caf7372d5d6a\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Events-by-time\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":24,\"y\":28,\"w\":12,\"h\":14,\"i\":\"398a8ba3-0ffc-40ee-90e1-c1547938d171\"},\"panelIndex\":\"398a8ba3-0ffc-40ee-90e1-c1547938d171\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"c76f346d-f6d6-4f9e-acb8-f5dde656e783\":{\"columns\":{\"b659aca0-0f1f-4408-8cea-1eea232bfe93\":{\"label\":\"Top values of objectRef.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"b659aca0-0f1f-4408-8cea-1eea232bfe93\",\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"c76f346d-f6d6-4f9e-acb8-f5dde656e783\",\"groups\":[\"b659aca0-0f1f-4408-8cea-1eea232bfe93\"],\"metric\":\"e4cb6a49-c1ea-4257-aeae-d65d1aed62f7\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"default\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.namespace.keyword: kube-system and verb : create and objectRef.resource.keyword: pods and objectRef.name : * and not objectRef.name : (*calico* or *dns* or *npd* or *proxy* or *metrics* or *csi* or *masq* or *hubble*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-c76f346d-f6d6-4f9e-acb8-f5dde656e783\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Create pod in kube-system\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":36,\"y\":28,\"w\":12,\"h\":14,\"i\":\"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb\"},\"panelIndex\":\"3e2f27b5-f148-4c2b-9c36-ccdb2b49bbcb\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\":{\"columns\":{\"71c8af00-7864-4ca6-a20d-0e43a80da354\":{\"label\":\"Top values of requestObject.status.containerStatuses.image.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"requestObject.status.containerStatuses.image.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"71c8af00-7864-4ca6-a20d-0e43a80da354\",\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\",\"groups\":[\"71c8af00-7864-4ca6-a20d-0e43a80da354\"],\"metric\":\"1f45b75e-0ec2-4159-97e2-dd1f4f0aaf84\",\"numberDisplay\":\"hidden\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and not requestObject.status.containerStatuses.image.keyword: *cr.yandex/* and requestObject.status.containerStatuses.containerID : *docker* and verb : patch and not requestObject.status.containerStatuses.image.keyword: (*falco* or *openpolicyagent* or *kyverno* or *k8s.gcr.io*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-f72786b2-64b8-4e0e-a0c9-5c1c2e2ba3d5\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Images not from YC CR\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":0,\"y\":33,\"w\":13,\"h\":9,\"i\":\"1d2c60a9-c570-45b0-8f49-e577c74e9ce3\"},\"panelIndex\":\"1d2c60a9-c570-45b0-8f49-e577c74e9ce3\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsDatatable\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"8e37793f-a2a3-48b0-a4b5-dda752e958b9\":{\"columns\":{\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\":{\"label\":\"Current Cluster Admins\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false},\"customLabel\":true},\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\",\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"columns\":[{\"isTransposed\":false,\"columnId\":\"239f6c81-2f8e-43e6-94ce-e92b61c1a91a\"},{\"isTransposed\":false,\"columnId\":\"7759b675-c0f2-450e-b8d5-06e2a2c230a2\",\"hidden\":true}],\"layerId\":\"8e37793f-a2a3-48b0-a4b5-dda752e958b9\"},\"query\":{\"query\":\"user.groups.keyword: *admin*\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-8e37793f-a2a3-48b0-a4b5-dda752e958b9\"}]},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":13,\"y\":33,\"w\":11,\"h\":9,\"i\":\"4d0ab419-47d3-48bd-9e5e-93a563e20aee\"},\"panelIndex\":\"4d0ab419-47d3-48bd-9e5e-93a563e20aee\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"b5bee140-5f01-4de3-9395-d279acb203dc\":{\"columns\":{\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\":{\"label\":\"Top values of objectRef.resource.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"objectRef.resource.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"4eda6d99-05c3-4ab8-a294-4632c9442157\":{\"label\":\"Top values of requestObject.subjects.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"requestObject.subjects.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":3,\"orderBy\":{\"type\":\"column\",\"columnId\":\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\",\"4eda6d99-05c3-4ab8-a294-4632c9442157\",\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\"},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":false,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"layerId\":\"b5bee140-5f01-4de3-9395-d279acb203dc\",\"accessors\":[\"6dc3784e-658d-4b02-b8f6-a64e170b46f9\"],\"position\":\"top\",\"seriesType\":\"bar_stacked\",\"showGridlines\":false,\"xAccessor\":\"48e660f4-62fa-4dfa-a1b4-670c9af71d59\",\"splitAccessor\":\"4eda6d99-05c3-4ab8-a294-4632c9442157\"}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and requestObject.roleRef.name.keyword:(cluster-admin or admin) and objectRef.resource.keyword: (clusterrolebindings or rolebindings) and verb : create and not responseObject.reason : AlreadyExists\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-b5bee140-5f01-4de3-9395-d279acb203dc\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Assign Cluster-admin/admin\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":42,\"w\":17,\"h\":8,\"i\":\"9e45767a-451f-48a1-b421-17738c299cd9\"},\"panelIndex\":\"9e45767a-451f-48a1-b421-17738c299cd9\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"pie\",\"params\":{\"type\":\"pie\",\"addTooltip\":true,\"addLegend\":true,\"legendPosition\":\"left\",\"isDonut\":true,\"labels\":{\"show\":true,\"values\":false,\"last_level\":true,\"truncate\":100},\"row\":false},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"NetworkPolicy:create/delete/update\"},\"schema\":\"metric\"},{\"id\":\"2\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"cluster_id.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"split\"},{\"id\":\"3\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"verb.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"segment\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and requestObject.kind.keyword: (NetworkPolicy or CiliumNetworkPolicy or DeleteOptions) and verb : (create or update or delete) and objectRef.resource : networkpolicies\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"NetworkPolicy:create/delete/update\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":17,\"y\":42,\"w\":17,\"h\":8,\"i\":\"7a0555be-d5f3-4aeb-9159-f48d7264d40c\"},\"panelIndex\":\"7a0555be-d5f3-4aeb-9159-f48d7264d40c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"pie\",\"params\":{\"type\":\"pie\",\"addTooltip\":true,\"addLegend\":true,\"legendPosition\":\"left\",\"isDonut\":true,\"labels\":{\"show\":true,\"values\":false,\"last_level\":true,\"truncate\":100},\"row\":false},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"Exec to container\"},\"schema\":\"metric\"},{\"id\":\"3\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"cluster_id.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\",\"customLabel\":\"Cluster_id\"},\"schema\":\"split\"},{\"id\":\"4\",\"enabled\":true,\"type\":\"terms\",\"params\":{\"field\":\"objectRef.name.keyword\",\"orderBy\":\"1\",\"order\":\"desc\",\"size\":5,\"otherBucket\":false,\"otherBucketLabel\":\"Other\",\"missingBucket\":false,\"missingBucketLabel\":\"Missing\"},\"schema\":\"segment\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and objectRef.subresource.keyword: exec\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":false,\"enhancements\":{},\"vis\":{\"legendOpen\":true}},\"title\":\"Exec to container\"},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":34,\"y\":42,\"w\":14,\"h\":8,\"i\":\"b6d054cd-bca1-49a6-affb-7b115b76af5a\"},\"panelIndex\":\"b6d054cd-bca1-49a6-affb-7b115b76af5a\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsDatatable\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"18ea127c-2267-4d24-9893-d3ef85942514\":{\"columns\":{\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\":{\"label\":\"Unique count of user.name.keyword\",\"dataType\":\"number\",\"operationType\":\"unique_count\",\"scale\":\"ratio\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":false},\"c94a437d-970d-4c55-89a7-499d47032bc8\":{\"label\":\"ServiceAccounts\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":15,\"orderBy\":{\"type\":\"column\",\"columnId\":\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false},\"customLabel\":true}},\"columnOrder\":[\"c94a437d-970d-4c55-89a7-499d47032bc8\",\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"layerId\":\"18ea127c-2267-4d24-9893-d3ef85942514\",\"columns\":[{\"isTransposed\":false,\"columnId\":\"c4f2ec69-90f8-42ff-9f24-48fc0fa87a45\",\"hidden\":true},{\"columnId\":\"c94a437d-970d-4c55-89a7-499d47032bc8\",\"isTransposed\":false,\"alignment\":\"left\"}]},\"query\":{\"query\":\"user.name : *serviceaccount*\",\"language\":\"kuery\"},\"filters\":[{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:certificate-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-0\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:certificate-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:coredns\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-1\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:coredns\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:cronjob-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-2\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:cronjob-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:generic-garbage-collector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-3\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:generic-garbage-collector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:job-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-4\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:job-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:endpointslice-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-5\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:endpointslice-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:endpoint-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-6\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:endpoint-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:calico-node\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-7\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:calico-node\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:kube-proxy\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-8\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:kube-proxy\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"alias\":null,\"negate\":true,\"disabled\":false,\"type\":\"phrase\",\"key\":\"objectRef.namespace\",\"params\":{\"query\":\"kube-system\"},\"indexRefName\":\"filter-index-pattern-9\"},\"query\":{\"match_phrase\":{\"objectRef.namespace\":\"kube-system\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:kube-dns-autoscaler\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-10\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:kube-dns-autoscaler\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:daemon-set-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-11\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:daemon-set-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:metrics-server\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-12\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:metrics-server\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:pod-garbage-collector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-13\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:pod-garbage-collector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:node-problem-detector\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-14\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:node-problem-detector\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:typha-cpha\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-15\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:typha-cpha\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:service-account-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-16\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:service-account-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:resourcequota-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-17\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:resourcequota-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:replicaset-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-18\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:replicaset-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:namespace-controller\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-19\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:namespace-controller\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:typha-cpva\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-20\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:typha-cpva\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:gatekeeper-system:gatekeeper-admin\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-21\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:gatekeeper-system:gatekeeper-admin\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:cilium-operator\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-22\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:cilium-operator\"}},\"$state\":{\"store\":\"appState\"}},{\"meta\":{\"negate\":true,\"type\":\"phrase\",\"key\":\"user.name.keyword\",\"params\":{\"query\":\"system:serviceaccount:kube-system:cilium\"},\"disabled\":false,\"alias\":null,\"indexRefName\":\"filter-index-pattern-23\"},\"query\":{\"match_phrase\":{\"user.name.keyword\":\"system:serviceaccount:kube-system:cilium\"}},\"$state\":{\"store\":\"appState\"}}]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-18ea127c-2267-4d24-9893-d3ef85942514\"},{\"name\":\"filter-index-pattern-0\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-1\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-2\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-3\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-4\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-5\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-6\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-7\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-8\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-9\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-10\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-11\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-12\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-13\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-14\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-15\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-16\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-17\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-18\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-19\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-20\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-21\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-22\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"},{\"name\":\"filter-index-pattern-23\",\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\"}]},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"map\",\"gridData\":{\"x\":0,\"y\":50,\"w\":34,\"h\":9,\"i\":\"96fdb671-a668-4ffc-9ad1-792d69551764\"},\"panelIndex\":\"96fdb671-a668-4ffc-9ad1-792d69551764\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"description\":\"\",\"layerListJSON\":\"[{\\\"sourceDescriptor\\\":{\\\"type\\\":\\\"EMS_TMS\\\",\\\"id\\\":\\\"dark_map\\\",\\\"isAutoSelect\\\":false},\\\"id\\\":\\\"1a56b9d3-c903-4286-8d75-48b62bf38532\\\",\\\"label\\\":null,\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":1,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"TILE\\\"},\\\"type\\\":\\\"VECTOR_TILE\\\"},{\\\"sourceDescriptor\\\":{\\\"indexPatternId\\\":\\\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\\\",\\\"geoField\\\":\\\"geoip.location\\\",\\\"requestType\\\":\\\"heatmap\\\",\\\"id\\\":\\\"65583363-2a0b-40ce-bf98-40ff54ad224e\\\",\\\"type\\\":\\\"ES_GEO_GRID\\\",\\\"applyGlobalQuery\\\":true,\\\"applyGlobalTime\\\":true,\\\"metrics\\\":[{\\\"type\\\":\\\"count\\\"}],\\\"resolution\\\":\\\"FINE\\\"},\\\"id\\\":\\\"519e1390-4055-4be7-a5bc-537bb78eea07\\\",\\\"label\\\":null,\\\"minZoom\\\":0,\\\"maxZoom\\\":24,\\\"alpha\\\":0.58,\\\"visible\\\":true,\\\"style\\\":{\\\"type\\\":\\\"HEATMAP\\\",\\\"colorRampName\\\":\\\"theclassic\\\"},\\\"type\\\":\\\"HEATMAP\\\"}]\",\"mapStateJSON\":\"{\\\"zoom\\\":1.45,\\\"center\\\":{\\\"lon\\\":54.04753,\\\"lat\\\":56.32976},\\\"timeFilters\\\":{\\\"from\\\":\\\"now-15d\\\",\\\"to\\\":\\\"now\\\"},\\\"refreshConfig\\\":{\\\"isPaused\\\":true,\\\"interval\\\":0},\\\"query\\\":{\\\"query\\\":\\\"event.dataset : yandexcloud.k8s_audit_logs and responseStatus.reason : Forbidden and not user.name : (system*node* or *gatekeeper* or *kyverno* or *proxy* or *scheduler* or *anonymous* or *csi* or *controller*)\\\",\\\"language\\\":\\\"kuery\\\"},\\\"filters\\\":[],\\\"settings\\\":{\\\"autoFitToDataBounds\\\":false,\\\"backgroundColor\\\":\\\"#ffffff\\\",\\\"disableInteractive\\\":false,\\\"disableTooltipControl\\\":false,\\\"hideToolbarOverlay\\\":false,\\\"hideLayerControl\\\":false,\\\"hideViewControl\\\":false,\\\"initialLocation\\\":\\\"LAST_SAVED_LOCATION\\\",\\\"fixedLocation\\\":{\\\"lat\\\":0,\\\"lon\\\":0,\\\"zoom\\\":2},\\\"browserLocation\\\":{\\\"zoom\\\":2},\\\"maxZoom\\\":24,\\\"minZoom\\\":0,\\\"showScaleControl\\\":false,\\\"showSpatialFilters\\\":true,\\\"spatialFiltersAlpa\\\":0.3,\\\"spatialFiltersFillColor\\\":\\\"#DA8B45\\\",\\\"spatialFiltersLineColor\\\":\\\"#DA8B45\\\"}}\",\"uiStateJSON\":\"{\\\"isLayerTOCOpen\\\":true,\\\"openTOCDetails\\\":[]}\"},\"mapCenter\":{\"lat\":56.32976,\"lon\":54.04753,\"zoom\":1.45},\"mapBuffer\":{\"minLon\":-269.96721,\"minLat\":21.676450000000003,\"maxLon\":378.06227,\"maxLat\":84.75865},\"isLayerTOCOpen\":false,\"openTOCDetails\":[],\"hiddenLayers\":[],\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":34,\"y\":50,\"w\":14,\"h\":9,\"i\":\"bb843cd6-969c-4aae-a37c-978d2fe0bbef\"},\"panelIndex\":\"bb843cd6-969c-4aae-a37c-978d2fe0bbef\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsXY\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"d401535b-665e-442b-a312-9edd3c1ebcc0\":{\"columns\":{\"61acda83-5d64-453e-9ca1-16b129cc2b42\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"56667c46-e4e6-4a18-9613-12d027ca7a16\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"ece5248d-0578-44e8-b245-bc2de86f37f4\":{\"label\":\"@timestamp\",\"dataType\":\"date\",\"operationType\":\"date_histogram\",\"sourceField\":\"@timestamp\",\"isBucketed\":true,\"scale\":\"interval\",\"params\":{\"interval\":\"auto\"}},\"56667c46-e4e6-4a18-9613-12d027ca7a16\":{\"label\":\"Count of records\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\"}},\"columnOrder\":[\"61acda83-5d64-453e-9ca1-16b129cc2b42\",\"ece5248d-0578-44e8-b245-bc2de86f37f4\",\"56667c46-e4e6-4a18-9613-12d027ca7a16\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"legend\":{\"isVisible\":true,\"position\":\"right\",\"showSingleSeries\":false},\"valueLabels\":\"hide\",\"fittingFunction\":\"None\",\"axisTitlesVisibilitySettings\":{\"x\":false,\"yLeft\":false,\"yRight\":true},\"tickLabelsVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"gridlinesVisibilitySettings\":{\"x\":true,\"yLeft\":true,\"yRight\":true},\"preferredSeriesType\":\"bar_stacked\",\"layers\":[{\"palette\":{\"type\":\"palette\",\"name\":\"gray\"},\"layerId\":\"d401535b-665e-442b-a312-9edd3c1ebcc0\",\"seriesType\":\"bar_stacked\",\"xAccessor\":\"ece5248d-0578-44e8-b245-bc2de86f37f4\",\"splitAccessor\":\"61acda83-5d64-453e-9ca1-16b129cc2b42\",\"accessors\":[\"56667c46-e4e6-4a18-9613-12d027ca7a16\"]}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseStatus.reason : Forbidden and not user.name : (system*node* or *gatekeeper* or *kyverno* or *proxy* or *scheduler* or *anonymous* or *csi* or *controller*)\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-d401535b-665e-442b-a312-9edd3c1ebcc0\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"Unauthorized events\"},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":59,\"w\":48,\"h\":4,\"i\":\"5abb0208-9bcf-42f2-8376-ee20d8047f2a\"},\"panelIndex\":\"5abb0208-9bcf-42f2-8376-ee20d8047f2a\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"markdown\",\"params\":{\"fontSize\":21,\"openLinksInNewTab\":false,\"markdown\":\"Policy Engine\"},\"uiState\":{},\"data\":{\"aggs\":[],\"searchSource\":{\"query\":{\"query\":\"\",\"language\":\"kuery\"},\"filter\":[]}}},\"hidePanelTitles\":true,\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"visualization\",\"gridData\":{\"x\":0,\"y\":63,\"w\":5,\"h\":9,\"i\":\"e1d27ba4-c45c-431e-933b-0a174c71d48c\"},\"panelIndex\":\"e1d27ba4-c45c-431e-933b-0a174c71d48c\",\"embeddableConfig\":{\"savedVis\":{\"title\":\"\",\"description\":\"\",\"type\":\"metric\",\"params\":{\"addTooltip\":true,\"addLegend\":false,\"type\":\"metric\",\"metric\":{\"percentageMode\":false,\"useRanges\":false,\"colorSchema\":\"Green to Red\",\"metricColorMode\":\"Labels\",\"colorsRange\":[{\"from\":0,\"to\":1},{\"from\":1,\"to\":100000}],\"labels\":{\"show\":true},\"invertColors\":false,\"style\":{\"bgFill\":\"#000\",\"bgColor\":false,\"labelColor\":false,\"subText\":\"\",\"fontSize\":76}}},\"uiState\":{},\"data\":{\"aggs\":[{\"id\":\"1\",\"enabled\":true,\"type\":\"count\",\"params\":{\"customLabel\":\"OPA-Gatekeeper-Detections\"},\"schema\":\"metric\"}],\"searchSource\":{\"index\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filter\":[]}}},\"enhancements\":{}}},{\"version\":\"7.13.4\",\"type\":\"lens\",\"gridData\":{\"x\":5,\"y\":63,\"w\":9,\"h\":9,\"i\":\"f9181782-c266-4c44-860e-dc37a48bf08f\"},\"panelIndex\":\"f9181782-c266-4c44-860e-dc37a48bf08f\",\"embeddableConfig\":{\"attributes\":{\"title\":\"\",\"type\":\"lens\",\"visualizationType\":\"lnsPie\",\"state\":{\"datasourceStates\":{\"indexpattern\":{\"layers\":{\"6f2deb01-002f-4a18-bee7-7968ad39a8a7\":{\"columns\":{\"443941ae-37bd-4230-a7c2-3eec6b193f37\":{\"label\":\"Top values of user.name.keyword\",\"dataType\":\"string\",\"operationType\":\"terms\",\"scale\":\"ordinal\",\"sourceField\":\"user.name.keyword\",\"isBucketed\":true,\"params\":{\"size\":5,\"orderBy\":{\"type\":\"column\",\"columnId\":\"1708471f-d516-4b55-a792-7263d51215ba\"},\"orderDirection\":\"desc\",\"otherBucket\":true,\"missingBucket\":false}},\"1708471f-d516-4b55-a792-7263d51215ba\":{\"label\":\"OPA-Gatekeeper detection\",\"dataType\":\"number\",\"operationType\":\"count\",\"isBucketed\":false,\"scale\":\"ratio\",\"sourceField\":\"Records\",\"customLabel\":true}},\"columnOrder\":[\"443941ae-37bd-4230-a7c2-3eec6b193f37\",\"1708471f-d516-4b55-a792-7263d51215ba\"],\"incompleteColumns\":{}}}}},\"visualization\":{\"shape\":\"donut\",\"layers\":[{\"layerId\":\"6f2deb01-002f-4a18-bee7-7968ad39a8a7\",\"groups\":[\"443941ae-37bd-4230-a7c2-3eec6b193f37\"],\"metric\":\"1708471f-d516-4b55-a792-7263d51215ba\",\"numberDisplay\":\"value\",\"categoryDisplay\":\"default\",\"legendDisplay\":\"show\",\"nestedLegend\":false,\"percentDecimals\":2}]},\"query\":{\"query\":\"event.dataset : yandexcloud.k8s_audit_logs and responseObject.status.keyword: Failure and responseObject.message :\\\" admission webhook \\\\\\\\\\\\\\\"validation.gatekeeper.sh\\\\\\\\\\\\\\\" denied the request\\\" and not objectRef.namespace : falco and not user.name : system\\\\\\\\\\\\:serviceaccount\\\\\\\\\\\\:kube-system\\\\\\\\\\\\:daemon-set-controller\",\"language\":\"kuery\"},\"filters\":[]},\"references\":[{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-current-indexpattern\"},{\"type\":\"index-pattern\",\"id\":\"0c4550b0-f8f4-11eb-bf38-9dbfd3ede2c5\",\"name\":\"indexpattern-datasource-layer-6f2deb01-002f-4a18-bee7-7968ad39a8a7\"}]},\"hidePanelTitles\":false,\"enhancements\":{}},\"title\":\"opa-by-user(yc iam user get --id  
# Version
**Version-2.0**
- Changelog:
- добавлена поддержка авто-установки kyverno с политиками в режиме audit
- Docker images:
- `cr.yandex/crpjfmfou6gflobbfvfv/k8s-events-siem-worker:1.1.0`
# Оглавление
- [Описание](#описание)
- [Связь с решением "Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"](#связь-с-решением-"Сбор-мониторинг-и-анализ-аудит-логов-в-Yandex-Managed-Service-for-Elasticsearch-(ELK)")
- [Общая схема](#общая-схема)
- [Описание импортируемых объектов ELK (Security Content)](#описание-импортируемых-объектов-ELK-(Security-Content))
- [Описание terraform](#описание-terraform)
- [Процесс обновления контента](#процесс-обновления-контента)
- [Опционально ручные действие](#опционально-ручные-действие)
## Описание
Решение из "коробки" выполняет следующее:
- ☑️ собирает [k8s AUDIT-LOGS](https://kubernetes.io/docs/tasks/debug-application-cluster/audit/) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/)
- ☑️ устанавливает [FALCO](https://falco.org/) и собирает его [ALERTS](https://falco.org/docs/alerts/) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/)
- ☑️ устанавливает [Kyverno](https://kyverno.io/) c политиками категории [Pod Security Policy(Restricted)](https://kyverno.io/policies/?policytypes=Pod%2520Security%2520Standards%2520%28Restricted%29) в режиме audit и собирает его [ALERTS (PolicyReports)](https://kyverno.io/docs/policy-reports/) (при помощи [Policy Reporter](https://github.com/kyverno/policy-reporter))
- ☑️ импортирует Security Content (dashboards, detection rules и др.)(см. в секции Security Content) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/) для анализа и реагирования на события ИБ.
- ✔️ *В том числе импортирует Security Content для [OPA Gatekeeper](https://open-policy-agent.github.io/gatekeeper/website/docs/) (в режиме enforce). (сам OPA Gatekeeper может быть установлен вручную дополнительно)
- ☑️ Создает индексы в двух репликах, настраивает базовую политику rollover (создания новых индексов каждые тридцать дней или по достижению 50ГБ), для дальнейшей настройки в части высокой доступности данных и для настройки снимков данных в S3 - см. [рекомендации](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md).
## Связь с решением "Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"
Решение ["Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main) содержит информацию о том, как установить Yandex Managed Service for Elasticsearch (ELK) и собирать в него логи Audit Trails
## Общая схема
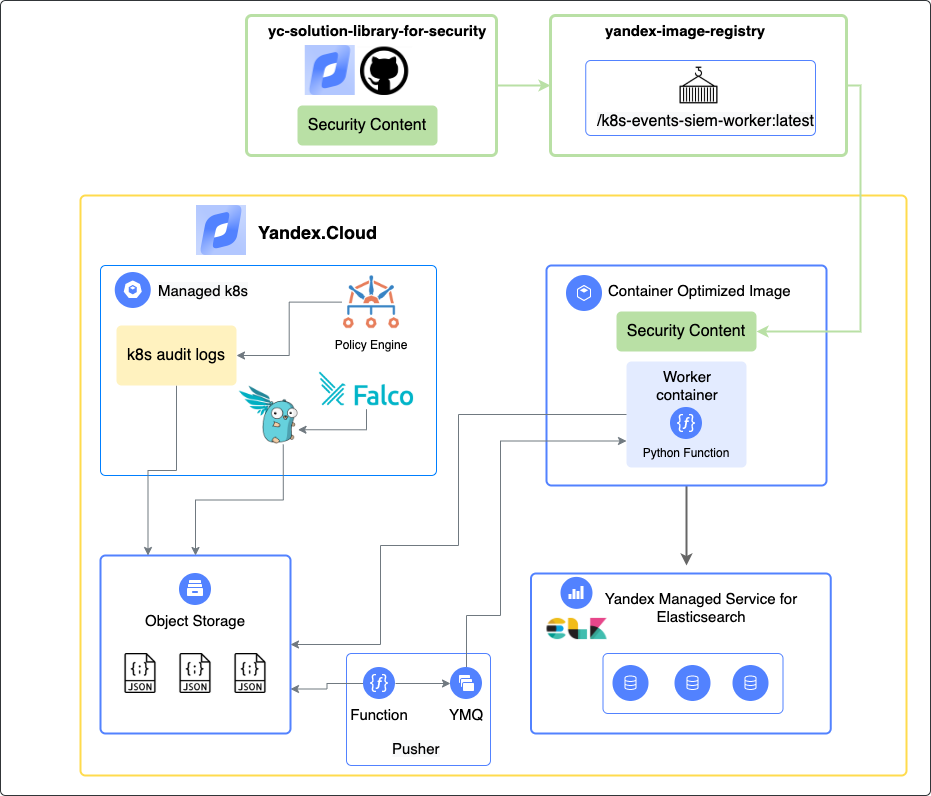
## Описание импортируемых объектов ELK (Security Content)
Подробное описание объектов по [ссылке](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf)
## Описание terraform
Решение состоит из 2-х модулей Terraform:
1) [security-events-to-storage-exporter](./security-events-to-storage-exporter) (экспортирует логи в s3)
- Принимает на вход:
- `folder_id` - id каталога, в котором расположен кластер
- `cluster_name` - имя кластера Kubernetes
- `log_bucket_service_account_id` - id сервисного аккаунта, который может писать в бакет и имеет роль *ymq.admin*
- `log_bucket_name` - имя бакета, куда нужно сохранять логи
- `function_service_account_id` - (опционально) id сервисного аккаунта, который будет запускать фукнцию, если не указан, то используется `log_bucket_service_account_id`
- Выполняет:
- создание статического ключа для сервисного аккаунта
- создание функции и тригера для записи логов кластера в s3
- установку falco и настроенного falcosidekick, который отправит логи в s3
- установку Kyverno и настроенного [Policy Reporter](https://github.com/kyverno/policy-reporter), который отправит логи в s3
2) [security-events-to-siem-importer](./security-events-to-siem-importer) (импортирует логи в ELK)
- Принимает на вход:
- ряд параметров из модуля (`security-events-to-storage-exporter`)
- `auditlog_enabled` - *true* или *false* (отправлять ли аудит логи k8s в ELK)
- `falco_enabled` - *true* или *false* (отправлять ли алерты falco в ELK)
- `kyverno_enabled` - *true* или *false* (отправлять ли алерты kyverno в ELK)
- адрес FQDN инсталляции ELK
- id подсети, в которой создается ВМ с контейнером импортера
- credentials ELK пользователя для импорта событий
- Выполняет:
- создание YMQ очередей с именами файлов логов в S3
- создание функций для push имен файлов из S3 в YMQ
- создание тригеров для взаимодействия очередей и функций
- генерацию и запись в файл и на ВМ ключей SSH
- создание ВМ на базе COI ([container optimised image](https://cloud.yandex.ru/docs/cos/concepts/)) с контейнерами workers, которые импортируют событий из s3 в ELK
#### Пререквизиты
- :white_check_mark: Cluster Managed k8s
- :white_check_mark: Managed ELK
- :white_check_mark: Сервисный аккаунт, который может писать в бакет и имеет роль *ymq.admin*
- :white_check_mark: Object Storage Bucket
- :white_check_mark: Subnet для развертывания ВМ с включенным NAT
#### Пример вызова модулей:
См. Пример вызова модулей в /example/main.tf
```Python
//Вызов модуля security-events-to-storage-exporter
module "security-events-to-storage-exporter" {
source = "../security-events-to-storage-exporter/" # путь до модуля
folder_id = "xxxxxx" // folder-id кластера k8s yc managed-kubernetes cluster get --id

# Version
**Version-2.0**
- Changelog:
- добавлена поддержка авто-установки kyverno с политиками в режиме audit
- Docker images:
- `cr.yandex/crpjfmfou6gflobbfvfv/k8s-events-siem-worker:1.1.0`
# Оглавление
- [Описание](#описание)
- [Связь с решением "Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"](#связь-с-решением-"Сбор-мониторинг-и-анализ-аудит-логов-в-Yandex-Managed-Service-for-Elasticsearch-(ELK)")
- [Общая схема](#общая-схема)
- [Описание импортируемых объектов ELK (Security Content)](#описание-импортируемых-объектов-ELK-(Security-Content))
- [Описание terraform](#описание-terraform)
- [Процесс обновления контента](#процесс-обновления-контента)
- [Опционально ручные действие](#опционально-ручные-действие)
## Описание
Решение из "коробки" выполняет следующее:
- ☑️ собирает [k8s AUDIT-LOGS](https://kubernetes.io/docs/tasks/debug-application-cluster/audit/) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/)
- ☑️ устанавливает [FALCO](https://falco.org/) и собирает его [ALERTS](https://falco.org/docs/alerts/) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/)
- ☑️ устанавливает [Kyverno](https://kyverno.io/) c политиками категории [Pod Security Policy(Restricted)](https://kyverno.io/policies/?policytypes=Pod%2520Security%2520Standards%2520%28Restricted%29) в режиме audit и собирает его [ALERTS (PolicyReports)](https://kyverno.io/docs/policy-reports/) (при помощи [Policy Reporter](https://github.com/kyverno/policy-reporter))
- ☑️ импортирует Security Content (dashboards, detection rules и др.)(см. в секции Security Content) в [Managed ELK SIEM](https://cloud.yandex.ru/docs/managed-elasticsearch/) для анализа и реагирования на события ИБ.
- ✔️ *В том числе импортирует Security Content для [OPA Gatekeeper](https://open-policy-agent.github.io/gatekeeper/website/docs/) (в режиме enforce). (сам OPA Gatekeeper может быть установлен вручную дополнительно)
- ☑️ Создает индексы в двух репликах, настраивает базовую политику rollover (создания новых индексов каждые тридцать дней или по достижению 50ГБ), для дальнейшей настройки в части высокой доступности данных и для настройки снимков данных в S3 - см. [рекомендации](../export-auditlogs-to-ELK_main/CONFIGURE-HA.md).
## Связь с решением "Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"
Решение ["Сбор, мониторинг и анализ аудит логов в Yandex Managed Service for Elasticsearch (ELK)"](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main) содержит информацию о том, как установить Yandex Managed Service for Elasticsearch (ELK) и собирать в него логи Audit Trails
## Общая схема
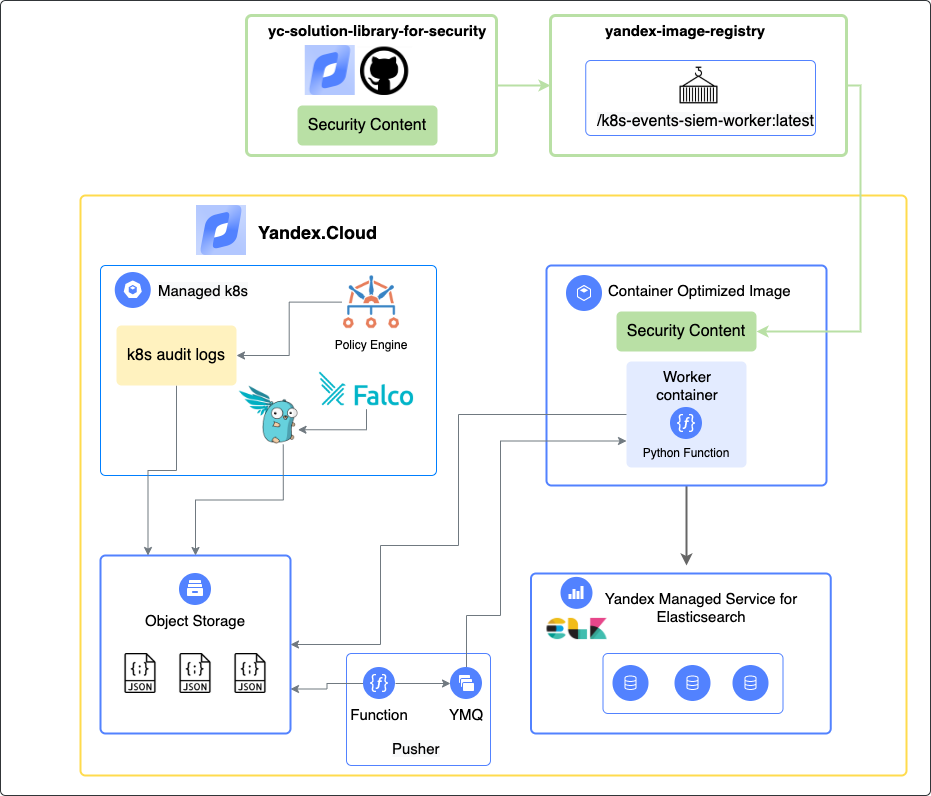
## Описание импортируемых объектов ELK (Security Content)
Подробное описание объектов по [ссылке](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf)
## Описание terraform
Решение состоит из 2-х модулей Terraform:
1) [security-events-to-storage-exporter](./security-events-to-storage-exporter) (экспортирует логи в s3)
- Принимает на вход:
- `folder_id` - id каталога, в котором расположен кластер
- `cluster_name` - имя кластера Kubernetes
- `log_bucket_service_account_id` - id сервисного аккаунта, который может писать в бакет и имеет роль *ymq.admin*
- `log_bucket_name` - имя бакета, куда нужно сохранять логи
- `function_service_account_id` - (опционально) id сервисного аккаунта, который будет запускать фукнцию, если не указан, то используется `log_bucket_service_account_id`
- Выполняет:
- создание статического ключа для сервисного аккаунта
- создание функции и тригера для записи логов кластера в s3
- установку falco и настроенного falcosidekick, который отправит логи в s3
- установку Kyverno и настроенного [Policy Reporter](https://github.com/kyverno/policy-reporter), который отправит логи в s3
2) [security-events-to-siem-importer](./security-events-to-siem-importer) (импортирует логи в ELK)
- Принимает на вход:
- ряд параметров из модуля (`security-events-to-storage-exporter`)
- `auditlog_enabled` - *true* или *false* (отправлять ли аудит логи k8s в ELK)
- `falco_enabled` - *true* или *false* (отправлять ли алерты falco в ELK)
- `kyverno_enabled` - *true* или *false* (отправлять ли алерты kyverno в ELK)
- адрес FQDN инсталляции ELK
- id подсети, в которой создается ВМ с контейнером импортера
- credentials ELK пользователя для импорта событий
- Выполняет:
- создание YMQ очередей с именами файлов логов в S3
- создание функций для push имен файлов из S3 в YMQ
- создание тригеров для взаимодействия очередей и функций
- генерацию и запись в файл и на ВМ ключей SSH
- создание ВМ на базе COI ([container optimised image](https://cloud.yandex.ru/docs/cos/concepts/)) с контейнерами workers, которые импортируют событий из s3 в ELK
#### Пререквизиты
- :white_check_mark: Cluster Managed k8s
- :white_check_mark: Managed ELK
- :white_check_mark: Сервисный аккаунт, который может писать в бакет и имеет роль *ymq.admin*
- :white_check_mark: Object Storage Bucket
- :white_check_mark: Subnet для развертывания ВМ с включенным NAT
#### Пример вызова модулей:
См. Пример вызова модулей в /example/main.tf
```Python
//Вызов модуля security-events-to-storage-exporter
module "security-events-to-storage-exporter" {
source = "../security-events-to-storage-exporter/" # путь до модуля
folder_id = "xxxxxx" // folder-id кластера k8s yc managed-kubernetes cluster get --id  ## Security Content
**Security Content** — объекты OpenSearch , которые автоматически загружаются решением. Весь контент разработан с учетом опыта Security команды Yandex.Cloud и на основе опыта Клиентов облака.
Содержит следующий Security Content:
- Dashboard, на котором отражены все use cases и полезная статистика
- Набор Saved Queries для удобного поиска Security событий
- Пример Alert на которые настроены оповещения (Клиенту самостоятельно необходимо указать назначение уведомлений)
- Все интересные поля событий преобразованы в формат [Elastic Common Schema (ECS)](https://www.elastic.co/guide/en/ecs/current/index.html), полная табличка маппинга в файле [Описание объектов](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf)
Подробное описание в файле [ECS-mapping.docx](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/ECS-mapping_new.pdf)
## Процесс обновления контента
Скоро..к следующей версии
## Установка отказоустойчивого OpenSearch Yandex Managed Service for OpenSearch
https://cloud.yandex.ru/docs/managed-opensearch/quickstart
## Установка решения с помощью Terraform
Для установки с помощью terraform перейдите в раздел [terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/add-opensearch-solution/auditlogs/export-auditlogs-to-Opensearch/terraform)
По результатам выполнения tf скрипта и ручных действий указанных ниже, в указанный вами OpenSearch будут загружаться события audit trails из облака и будет загружен security content (dashboard, filters, mapping etc.) для работы с ними
По итогу установки у вас будет создан tenant "at-tenant", в котором находятся все объекты
## Настройка Alerts и Destination
Алертинг и правила реагирования в OpenSearch выполняется с помощью механизма [Alerting](https://opensearch.org/docs/latest/monitoring-plugins/alerting/index/)
Наше решение уже загружает пример monitor, вы можете взять его как пример для старта и сделать алерты по аналогии. Перейдите во вкладку Alerting - Monitors и найдите там "test". Нажмите кнопку edit, промотайте вниз и раскройте вкладку triggers и в ней укажите action. Выберите там заранее созданный канал [нотификации](https://opensearch.org/docs/latest/notifications-plugin/index/) (например slack)
## Самостоятельная Установка all-in-one Openasearch на ВМ
Для устновки opensearch можно воспользоваться оффициальной документацией. Например [установка с помощью docker](https://opensearch.org/docs/2.1/opensearch/install/index/)
Для настройки TLS в opensearch dashboard используйте [инструкцию](https://opensearch.org/docs/2.1/dashboards/install/tls/)
Для генерации самоподпсанного SSL сертификата используйте [инстуркцию](https://opensearch.org/docs/2.1/security-plugin/configuration/generate-certificates/)
Либо загружите ваш собственный сертификат
Здесь представлены тестовые примеры файлов для установки opensearch в разделе [deploy-of-opensearch](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/add-opensearch-solution/auditlogs/export-auditlogs-to-Opensearch/deploy-of-opensearch)
p.s: не забудьте предоставить необходимые права доступа на файлы с сертификатом и ключем
## Рекомендации по настройке retention, rollover и snapshots:
[Рекомендации по настройке retention, rollover и snapshots](./CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/README_EN.md
================================================
# Collection, monitoring and analysis of Yandex Cloud audit logs in Opensearch

## Version
**Version-1.1**
- Changelog:
- Docker images:
- `cr.yandex/sol/s3-opensearch-importer:1.1`
## Solution Description
The solution allows you to collect, monitor and analyze Yandex.Cloud audit logs (Audit Trails) in Opensearch from the following sources:
- [Yandex Audit Trails](https://cloud.yandex.ru/docs/audit-trails/)
> The solution is constantly updated and maintained by the Yandex.Cloud Security team.
> Important! By default, this construct suggests deleting files after being subtracted from the bucket, but you can simultaneously store Audit Trails audit logs in S3 on a long-term basis and send them to Elastic. To do this, you need to create two Audit Trails in different S3 buckets:. The first bucket will be used for storage only. The second bucket will be used for integration with Opensearch
## What the solution does
- ☑️ Sends data to an existing Opensearch cluster (if you don't have an Opensearch cluster, use the installation instructions at the end of the page)
- ☑️ Deploys COI Instance with container based on s3-elk-importer image (`cr.yandex/sol/s3-opensearch-importer:latest`)
- ☑️ Upload Security Content to Opensearch (Dashboards, Detection Rules (with alerts), etc.)
- ☑️ Provides continuous delivery of json files with audit logs from Yandex Object Storage (Audit Trails) to Opensearch
- ☑️ Creates indexes on two replicas, configures a basic rollover policy (create new indexes every thirty days or when 50GB is reached), for further tuning in terms of data high availability and for configuring data snapshots in S3 - see [recommendations] (./CONFIGURE -HA.md).
## Solution diagram
## Security Content
**Security Content** — объекты OpenSearch , которые автоматически загружаются решением. Весь контент разработан с учетом опыта Security команды Yandex.Cloud и на основе опыта Клиентов облака.
Содержит следующий Security Content:
- Dashboard, на котором отражены все use cases и полезная статистика
- Набор Saved Queries для удобного поиска Security событий
- Пример Alert на которые настроены оповещения (Клиенту самостоятельно необходимо указать назначение уведомлений)
- Все интересные поля событий преобразованы в формат [Elastic Common Schema (ECS)](https://www.elastic.co/guide/en/ecs/current/index.html), полная табличка маппинга в файле [Описание объектов](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов.pdf)
Подробное описание в файле [ECS-mapping.docx](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/ECS-mapping_new.pdf)
## Процесс обновления контента
Скоро..к следующей версии
## Установка отказоустойчивого OpenSearch Yandex Managed Service for OpenSearch
https://cloud.yandex.ru/docs/managed-opensearch/quickstart
## Установка решения с помощью Terraform
Для установки с помощью terraform перейдите в раздел [terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/add-opensearch-solution/auditlogs/export-auditlogs-to-Opensearch/terraform)
По результатам выполнения tf скрипта и ручных действий указанных ниже, в указанный вами OpenSearch будут загружаться события audit trails из облака и будет загружен security content (dashboard, filters, mapping etc.) для работы с ними
По итогу установки у вас будет создан tenant "at-tenant", в котором находятся все объекты
## Настройка Alerts и Destination
Алертинг и правила реагирования в OpenSearch выполняется с помощью механизма [Alerting](https://opensearch.org/docs/latest/monitoring-plugins/alerting/index/)
Наше решение уже загружает пример monitor, вы можете взять его как пример для старта и сделать алерты по аналогии. Перейдите во вкладку Alerting - Monitors и найдите там "test". Нажмите кнопку edit, промотайте вниз и раскройте вкладку triggers и в ней укажите action. Выберите там заранее созданный канал [нотификации](https://opensearch.org/docs/latest/notifications-plugin/index/) (например slack)
## Самостоятельная Установка all-in-one Openasearch на ВМ
Для устновки opensearch можно воспользоваться оффициальной документацией. Например [установка с помощью docker](https://opensearch.org/docs/2.1/opensearch/install/index/)
Для настройки TLS в opensearch dashboard используйте [инструкцию](https://opensearch.org/docs/2.1/dashboards/install/tls/)
Для генерации самоподпсанного SSL сертификата используйте [инстуркцию](https://opensearch.org/docs/2.1/security-plugin/configuration/generate-certificates/)
Либо загружите ваш собственный сертификат
Здесь представлены тестовые примеры файлов для установки opensearch в разделе [deploy-of-opensearch](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/add-opensearch-solution/auditlogs/export-auditlogs-to-Opensearch/deploy-of-opensearch)
p.s: не забудьте предоставить необходимые права доступа на файлы с сертификатом и ключем
## Рекомендации по настройке retention, rollover и snapshots:
[Рекомендации по настройке retention, rollover и snapshots](./CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/README_EN.md
================================================
# Collection, monitoring and analysis of Yandex Cloud audit logs in Opensearch

## Version
**Version-1.1**
- Changelog:
- Docker images:
- `cr.yandex/sol/s3-opensearch-importer:1.1`
## Solution Description
The solution allows you to collect, monitor and analyze Yandex.Cloud audit logs (Audit Trails) in Opensearch from the following sources:
- [Yandex Audit Trails](https://cloud.yandex.ru/docs/audit-trails/)
> The solution is constantly updated and maintained by the Yandex.Cloud Security team.
> Important! By default, this construct suggests deleting files after being subtracted from the bucket, but you can simultaneously store Audit Trails audit logs in S3 on a long-term basis and send them to Elastic. To do this, you need to create two Audit Trails in different S3 buckets:. The first bucket will be used for storage only. The second bucket will be used for integration with Opensearch
## What the solution does
- ☑️ Sends data to an existing Opensearch cluster (if you don't have an Opensearch cluster, use the installation instructions at the end of the page)
- ☑️ Deploys COI Instance with container based on s3-elk-importer image (`cr.yandex/sol/s3-opensearch-importer:latest`)
- ☑️ Upload Security Content to Opensearch (Dashboards, Detection Rules (with alerts), etc.)
- ☑️ Provides continuous delivery of json files with audit logs from Yandex Object Storage (Audit Trails) to Opensearch
- ☑️ Creates indexes on two replicas, configures a basic rollover policy (create new indexes every thirty days or when 50GB is reached), for further tuning in terms of data high availability and for configuring data snapshots in S3 - see [recommendations] (./CONFIGURE -HA.md).
## Solution diagram
 ## Security Content
**Security Content** - Opensearch objects that are automatically loaded by the solution. All content is developed taking into account the experience of the Yandex.Cloud Security team and based on the experience of Cloud Clients.
Contains the following Security Content:
- Dashboard showing all use cases and useful statistics
- A set of Saved Queries for easy search of Security events
- An example of Alert for which alerts are configured (The client himself needs to specify the purpose of notifications)
- All interesting event fields are converted to the [Elastic Common Schema (ECS)] format (https://www.elastic.co/guide/en/ecs/current/index.html), full mapping table in the [Object description](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов%20eng.docx)
Detailed description in the file [ECS-mapping.docx](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/ ECS-mapping_new.pdf)
## Content update process
Coming soon..to the next version
## Installing the solution with Terraform
To install using terraform, go to the [terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/add-opensearch-solution/auditlogs/export-auditlogs-to- opensearch/terraform)
Based on the results of executing the tf script and the manual actions indicated below, audit trails events from the cloud will be loaded into the opensearch specified by you and security content (dashboard, filters, mapping etc.) will be loaded to work with them
As a result of the installation, you will have a tenant "at-tenant", in which all objects are located
## Set up Alerts and Destination
Alerting and response rules in Opensearch is done using the [Alerting mechanism](https://opensearch.org/docs/latest/monitoring-plugins/alerting/index/)
Our solution already loads the monitor example, you can take it as an example to start and make alerts by analogy. Go to the Alerting - Monitors tab and find "test" there. Press the edit button, scroll down and expand the triggers tab and enter an action in it. Select a pre-created [notification] channel there (https://opensearch.org/docs/latest/notifications-plugin/index/) (for example, slack)
## Install Openasearch
To install opensearch, you can use the official documentation. For example [install with docker](https://opensearch.org/docs/2.1/opensearch/install/index/)
To set up TLS in opensearch dashboard, use [instruction](https://opensearch.org/docs/2.1/dashboards/install/tls/)
To generate a self-signed SSL certificate, use [instruction](https://opensearch.org/docs/2.1/security-plugin/configuration/generate-certificates/)
Or upload your own certificate
Here are test files for installing opensearch in the [deploy-of-opensearch] section(https://github.com/yandex-cloud/yc-solution-library-for-security/tree/add-opensearch-solution/auditlogs/ export-auditlogs-to-opensearch/deploy-of-opensearch)
p.s: don't forget to give the necessary file permissions with the certificate and key
## Recommendations for configuring retention, rollover and snapshots:
[Recommendations for configuring retention, rollover and snapshots](./CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/deploy-of-opensearch/docker-compose.yaml
================================================
version: '3'
services:
opensearch-node1:
#image: opensearchproject/opensearch:2.0.1
image: opensearchproject/opensearch:2.1.0
container_name: opensearch-node1
environment:
- cluster.name=opensearch-cluster
- node.name=opensearch-node1
- bootstrap.memory_lock=true # along with the memlock settings below, disables swapping
- "OPENSEARCH_JAVA_OPTS=-Xms512m -Xmx512m" # minimum and maximum Java heap size, recommend setting both to 50% of system RAM
- "DISABLE_INSTALL_DEMO_CONFIG=false" # disables execution of install_demo_configuration.sh bundled with security plugin, which installs demo certificates and security configurations to OpenSearch
- "DISABLE_SECURITY_PLUGIN=false" # disables security plugin entirely in OpenSearch by setting plugins.security.disabled: true in opensearch.yml
- "discovery.type=single-node" # disables bootstrap checks that are enabled when network.host is set to a non-loopback address
ulimits:
memlock:
soft: -1
hard: -1
nofile:
soft: 65536 # maximum number of open files for the OpenSearch user, set to at least 65536 on modern systems
hard: 65536
volumes:
- opensearch-data1:/usr/share/opensearch/data
ports:
- 9200:9200
- 9600:9600 # required for Performance Analyzer
networks:
- opensearch-net
opensearch-dashboards:
volumes:
- /usr/share/opensearch-dashboards/config/opensearch_dashboards.yml:/usr/share/opensearch-dashboards/config/opensearch_dashboards.yml #add config
- /usr/share/opensearch-dashboards/config/client-cert.pem:/usr/share/opensearch-dashboards/config/client-cert.pem
- /usr/share/opensearch-dashboards/config/client-cert-key.pem:/usr/share/opensearch-dashboards/config/client-cert-key.pem
- /usr/share/opensearch-dashboards/config/root-ca.pem:/usr/share/opensearch-dashboards/config/root-ca.pem
#image: opensearchproject/opensearch-dashboards:2.0.1
image: opensearchproject/opensearch-dashboards:2.1.0
container_name: opensearch-dashboards
ports:
- 5601:5601
expose:
- "5601"
environment:
#- 'OPENSEARCH_HOSTS=["https://opensearch-node1:9200"]'
- "DISABLE_SECURITY_DASHBOARDS_PLUGIN=false" # disables security dashboards plugin in OpenSearch Dashboards
networks:
- opensearch-net
volumes:
opensearch-data1:
networks:
opensearch-net:
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/deploy-of-opensearch/opensearch_dashboards.yml
================================================
server.host: "0.0.0.0"
opensearch.hosts: ["https://opensearch-node1:9200"]
opensearch.ssl.verificationMode: none
opensearch.username: "kibanaserver"
opensearch.password: "kibanaserver"
opensearch.requestHeadersAllowlist: [ authorization,securitytenant ]
server.ssl.enabled: true
server.ssl.certificate: /usr/share/opensearch-dashboards/config/client-cert.pem
server.ssl.key: /usr/share/opensearch-dashboards/config/client-cert-key.pem
opensearch.ssl.certificateAuthorities: [ "/usr/share/opensearch-dashboards/config/root-ca.pem" ]
opensearch_security.multitenancy.enabled: true
opensearch_security.multitenancy.tenants.preferred: ["Private", "Global"]
opensearch_security.readonly_mode.roles: ["kibana_read_only"]
opensearch_security.cookie.secure: true
#disable_security_dashboards_plugin: false
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/functions/Dockerfile
================================================
FROM python:3.9.1-slim
RUN apt-get update
# docker build нужно запускать из папки export-auditlogs-to-Opensearch чтобы был правильный контекст при подборе include файлов
# пример docker build команды:
# docker build -t s3-opensearch-importer:latest -f ./functions/Dockerfile .
COPY /functions /app/functions
COPY /update-opensearch-scheme/include /app/include
WORKDIR /app
RUN pip install --upgrade pip
RUN pip install -r functions/requirements.txt
CMD ["python3", "functions/main.py"]
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/functions/main.py
================================================
import requests
import json
import os
import boto3
import time
import base64
# Function - Get token
def get_token():
response = requests.get('http://169.254.169.254/computeMetadata/v1/instance/service-accounts/default/token', headers={"Metadata-Flavor":"Google"})
return response.json().get('access_token')
# Function - Decrypt data with KMS key
def decrypt_secret_kms(secret):
token = get_token()
request_suffix = f"{kms_key_id}:decrypt"
request_json_data = {'ciphertext': secret}
response = requests.post('https://kms.yandex/kms/v1/keys/'+request_suffix, data=json.dumps(request_json_data), headers={"Accept":"application/json", "Authorization": "Bearer "+token})
b64_data = response.json().get('plaintext')
return base64.b64decode(b64_data).decode()
# # Configuration - Get ElasticSearch CA.pem
# def get_elastic_cert():
# file = '/app/include/CA.pem'
# if os.path.isfile(file):
# return file
# else:
# url = 'https://storage.yandexcloud.net/cloud-certs/CA.pem'
# response = requests.get(url)
# with open('/app/include/CA.pem', 'wb') as f:
# f.write(response.content)
# return file
# Configuration - Keys
kms_key_id = os.environ['KMS_KEY_ID']
elastic_auth_pw_encr = os.environ['ELK_PASS_ENCR']
s3_key_encr = os.environ['S3_KEY_ENCR']
s3_secret_encr = os.environ['S3_SECRET_ENCR']
# Configuration - Setting up variables for ElasticSearch
elastic_server = os.environ['ELASTIC_SERVER']
elastic_auth_user = os.environ['ELASTIC_AUTH_USER']
elastic_auth_pw = decrypt_secret_kms(elastic_auth_pw_encr)
elastic_index_name = f"{os.environ['ELASTIC_INDEX_NAME']}-000001"
elastic_index_alias = "audit-trails-index"
elastic_index_template = "audit-trails-template"
elastic_index_ilm = "audit-trails-ilm"
elastic_index_pipeline = "audit-trails-pipeline"
kibana_server = os.environ['KIBANA_SERVER']
fals = False #tls validation disable (please enable it when you use valid certificate)
#elastic_cert = get_elastic_cert()
# Configuration - Setting up variables for S3
s3_key = decrypt_secret_kms(s3_key_encr)
s3_secret = decrypt_secret_kms(s3_secret_encr)
s3_bucket = os.environ['S3_BUCKET']
s3_folder = os.environ['S3_FOLDER']
s3_local = '/tmp/s3'
# Configuration - Sleep time
if(os.getenv('SLEEP_TIME') is not None):
sleep_time = int(os.environ['SLEEP_TIME'])
else:
sleep_time = 240
# State - Setting up S3 client
s3 = boto3.resource('s3',
endpoint_url = 'https://storage.yandexcloud.net',
aws_access_key_id = s3_key,
aws_secret_access_key = s3_secret
)
# Create tenant
def create_tenant():
request_suffix = "/_plugins/_security/api/tenants/at-tenant"
request_json = """{
"description": "A tenant for the yandex cloud audit trails events."
}"""
response = requests.put(elastic_server+request_suffix, data=request_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json"})
if(response.status_code == 200):
print('Tenant -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Create config index in ElasticSearch
def create_config_index():
request_suffix = f"/.state-{elastic_index_alias}"
response = requests.get(elastic_server+request_suffix, verify=fals, auth=(elastic_auth_user, elastic_auth_pw))
if(response.status_code == 404):
request_suffix = f"/.state-{elastic_index_alias}/_doc/1"
request_json = """{
"is_configured": true
}"""
response = requests.post(elastic_server+request_suffix, data=request_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json"})
print('Config index -- CREATED')
else:
print('Config index -- EXISTS')
print(f"{response.status_code} - {response.text}")
# Function - Get config index state
def get_config_index_state():
request_suffix = f"/.state-{elastic_index_alias}/_doc/1"
response = requests.get(elastic_server+request_suffix, verify=fals, auth=(elastic_auth_user, elastic_auth_pw))
if(response.status_code != 200):
return False
print(f"{response.status_code} - {response.text}")
return True
# Function - Create ingest pipeline
def create_ingest_pipeline():
request_suffix = f"/_ingest/pipeline/{elastic_index_pipeline}"
data_file = open('/app/include/audit-trail/pipeline.json')
data_json = json.load(data_file)
data_file.close()
response = requests.put(elastic_server+request_suffix, json=data_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Ingest pipeline -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Create an index lifecycle policy
def create_lifecycle_policy():
request_suffix = f"/_plugins/_ism/policies/{elastic_index_ilm}"
data_file = open('/app/include/audit-trail/ism-policy.json')
data_json = json.load(data_file)
data_file.close()
response = requests.put(elastic_server+request_suffix, json=data_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index lifecycle policy -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Create an index template
def create_index_template():
request_suffix = f"/_index_template/{elastic_index_template}"
data_file = open('/app/include/audit-trail/index-template.json')
data_json = json.load(data_file)
data_file.close()
response = requests.put(elastic_server+request_suffix, json=data_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index template -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Create an index
def create_first_index():
request_suffix = f"/{elastic_index_name}"
response = requests.put(elastic_server+request_suffix, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"securitytenant":"at-tenant"})
if(response.status_code == 200):
print(f"Index {elastic_index_name} -- CREATED")
print(f"{response.status_code} - {response.text}")
# Function - Create an index alias
def create_index_alias():
request_suffix = f"/_aliases"
request_json = """{
"actions" : [
{ "add" : { "index" : "%s", "alias" : "%s" } }
]
}""" % (elastic_index_name, elastic_index_alias)
response = requests.post(elastic_server+request_suffix, data=request_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index alias -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Refresh index
def refresh_index():
request_suffix = f"/{elastic_index_alias}/_refresh"
response = requests.post(elastic_server+request_suffix, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index -- REFRESHED')
print(f"{response.status_code} - {response.text}")
#----
# Function - Preconfigure Kibana
def configure_kibana():
#Index pattern
data_file = {
'file': open('/app/include/audit-trail/index-pattern.ndjson', 'rb')
}
request_suffix = '/api/saved_objects/_import'
response = requests.post(kibana_server+request_suffix, files=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"osd-xsrf":"true", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index patterns -- IMPORTED')
print(f"{response.status_code} - {response.text}")
# Filters
data_file = {
'file': open('/app/include/audit-trail/filters.ndjson', 'rb')
}
request_suffix = '/api/saved_objects/_import'
response = requests.post(kibana_server+request_suffix, files=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"osd-xsrf":"true", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Filters -- IMPORTED')
print(f"{response.status_code} - {response.text}")
# Search
data_file = {
'file': open('/app/include/audit-trail/search.ndjson', 'rb')
}
request_suffix = '/api/saved_objects/_import'
response = requests.post(kibana_server+request_suffix, files=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"osd-xsrf":"true", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Searches -- IMPORTED')
print(f"{response.status_code} - {response.text}")
#Detections Alerts monitors
request_suffix = "/_plugins/_alerting/monitors"
data_file = open('/app/include/audit-trail/alert.json')
data_json = json.load(data_file)
data_file.close()
response = requests.post(elastic_server+request_suffix, json=data_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Alert monitor uploaded -- CREATED')
print(f"{response.status_code} - {response.text}")
#Dashboard
data_file = {
'file': open('/app/include/audit-trail/dashboard.ndjson', 'rb')
}
request_suffix = '/api/saved_objects/_import?overwrite=true'
response = requests.post(kibana_server+request_suffix, files=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"osd-xsrf":"true", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Dashboard -- IMPORTED')
print(f"{response.status_code} - {response.text}")
# Function - Download JSON logs to local folder
def download_s3_folder(s3_bucket, s3_folder, local_folder=None):
print('JSON download -- STARTED')
bucket = s3.Bucket(s3_bucket)
if not os.path.exists(local_folder):
os.makedirs(local_folder)
for obj in bucket.objects.filter(Prefix=s3_folder):
target = obj.key if local_folder is None \
else os.path.join(local_folder, os.path.relpath(obj.key, s3_folder))
if not os.path.exists(local_folder):
os.makedirs(local_folder)
if obj.key[-1] == '/':
continue
# Downloading JSON logs in a flat-structured way
bucket.download_file(obj.key, local_folder+'/'+target.rsplit('/')[-1])
print('JSON download -- COMPLETE')
# Function - Clean up S3 folder
def delete_objects_s3(s3_bucket, s3_folder):
bucket = s3.Bucket(s3_bucket)
for obj in bucket.objects.filter(Prefix=s3_folder):
if(obj.key != s3_folder+'/'):
bucket.delete_objects(
Delete={
'Objects': [
{
'Key': obj.key
},
]
}
)
print('S3 bucket -- EMPTIED')
# Function - Upload logs to ElasticSearch
def upload_docs_bulk(s3_bucket, s3_folder):
print('JSON upload -- STARTED')
request_suffix = f"/{elastic_index_alias}/_bulk?pipeline={elastic_index_pipeline}"
error_count = 0
for f in os.listdir(s3_local):
if f.endswith(".json"):
with open(f"{s3_local}/{f}", "r") as read_file:
data = json.load(read_file)
result = [json.dumps(record) for record in data]
with open(f"{s3_local}/nd-temp.json", 'w') as obj:
for i in result:
obj.write('{"index":{}}\n')
obj.write(i+'\n')
data_file = open(f"{s3_local}/nd-temp.json", 'rb').read()
response = requests.post(elastic_server+request_suffix, data=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/x-ndjson"})
os.remove(s3_local+"/"+f)
if(response.status_code != 200):
error_count += 1
print(response.text)
print(f"{response.status_code} - {response.text}")
if(os.path.exists(f"{s3_local}/nd-temp.json")):
os.remove(f"{s3_local}/nd-temp.json")
print(f"JSON upload -- COMPLETE -- {error_count} ERRORS")
if(error_count == 0):
delete_objects_s3(s3_bucket, s3_folder)
refresh_index()
# Process - Upload data
def upload_logs():
if(get_config_index_state()):
print("Config index -- EXISTS")
download_s3_folder(s3_bucket, s3_folder, s3_local)
upload_docs_bulk(s3_bucket, s3_folder)
else:
create_tenant()
create_lifecycle_policy()
create_index_template()
create_first_index()
create_index_alias()
create_ingest_pipeline()
configure_kibana()
create_config_index()
download_s3_folder(s3_bucket, s3_folder, s3_local)
upload_docs_bulk(s3_bucket, s3_folder)
### MAIN CONTROL PANEL
upload_logs()
print("Sleep -- STARTED")
time.sleep(sleep_time)
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/functions/requirements.txt
================================================
requests
boto3
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/images/elastic.drawio
================================================
## Security Content
**Security Content** - Opensearch objects that are automatically loaded by the solution. All content is developed taking into account the experience of the Yandex.Cloud Security team and based on the experience of Cloud Clients.
Contains the following Security Content:
- Dashboard showing all use cases and useful statistics
- A set of Saved Queries for easy search of Security events
- An example of Alert for which alerts are configured (The client himself needs to specify the purpose of notifications)
- All interesting event fields are converted to the [Elastic Common Schema (ECS)] format (https://www.elastic.co/guide/en/ecs/current/index.html), full mapping table in the [Object description](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/Описание%20объектов%20eng.docx)
Detailed description in the file [ECS-mapping.docx](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-ELK_main/papers/ ECS-mapping_new.pdf)
## Content update process
Coming soon..to the next version
## Installing the solution with Terraform
To install using terraform, go to the [terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/add-opensearch-solution/auditlogs/export-auditlogs-to- opensearch/terraform)
Based on the results of executing the tf script and the manual actions indicated below, audit trails events from the cloud will be loaded into the opensearch specified by you and security content (dashboard, filters, mapping etc.) will be loaded to work with them
As a result of the installation, you will have a tenant "at-tenant", in which all objects are located
## Set up Alerts and Destination
Alerting and response rules in Opensearch is done using the [Alerting mechanism](https://opensearch.org/docs/latest/monitoring-plugins/alerting/index/)
Our solution already loads the monitor example, you can take it as an example to start and make alerts by analogy. Go to the Alerting - Monitors tab and find "test" there. Press the edit button, scroll down and expand the triggers tab and enter an action in it. Select a pre-created [notification] channel there (https://opensearch.org/docs/latest/notifications-plugin/index/) (for example, slack)
## Install Openasearch
To install opensearch, you can use the official documentation. For example [install with docker](https://opensearch.org/docs/2.1/opensearch/install/index/)
To set up TLS in opensearch dashboard, use [instruction](https://opensearch.org/docs/2.1/dashboards/install/tls/)
To generate a self-signed SSL certificate, use [instruction](https://opensearch.org/docs/2.1/security-plugin/configuration/generate-certificates/)
Or upload your own certificate
Here are test files for installing opensearch in the [deploy-of-opensearch] section(https://github.com/yandex-cloud/yc-solution-library-for-security/tree/add-opensearch-solution/auditlogs/ export-auditlogs-to-opensearch/deploy-of-opensearch)
p.s: don't forget to give the necessary file permissions with the certificate and key
## Recommendations for configuring retention, rollover and snapshots:
[Recommendations for configuring retention, rollover and snapshots](./CONFIGURE-HA.md)
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/deploy-of-opensearch/docker-compose.yaml
================================================
version: '3'
services:
opensearch-node1:
#image: opensearchproject/opensearch:2.0.1
image: opensearchproject/opensearch:2.1.0
container_name: opensearch-node1
environment:
- cluster.name=opensearch-cluster
- node.name=opensearch-node1
- bootstrap.memory_lock=true # along with the memlock settings below, disables swapping
- "OPENSEARCH_JAVA_OPTS=-Xms512m -Xmx512m" # minimum and maximum Java heap size, recommend setting both to 50% of system RAM
- "DISABLE_INSTALL_DEMO_CONFIG=false" # disables execution of install_demo_configuration.sh bundled with security plugin, which installs demo certificates and security configurations to OpenSearch
- "DISABLE_SECURITY_PLUGIN=false" # disables security plugin entirely in OpenSearch by setting plugins.security.disabled: true in opensearch.yml
- "discovery.type=single-node" # disables bootstrap checks that are enabled when network.host is set to a non-loopback address
ulimits:
memlock:
soft: -1
hard: -1
nofile:
soft: 65536 # maximum number of open files for the OpenSearch user, set to at least 65536 on modern systems
hard: 65536
volumes:
- opensearch-data1:/usr/share/opensearch/data
ports:
- 9200:9200
- 9600:9600 # required for Performance Analyzer
networks:
- opensearch-net
opensearch-dashboards:
volumes:
- /usr/share/opensearch-dashboards/config/opensearch_dashboards.yml:/usr/share/opensearch-dashboards/config/opensearch_dashboards.yml #add config
- /usr/share/opensearch-dashboards/config/client-cert.pem:/usr/share/opensearch-dashboards/config/client-cert.pem
- /usr/share/opensearch-dashboards/config/client-cert-key.pem:/usr/share/opensearch-dashboards/config/client-cert-key.pem
- /usr/share/opensearch-dashboards/config/root-ca.pem:/usr/share/opensearch-dashboards/config/root-ca.pem
#image: opensearchproject/opensearch-dashboards:2.0.1
image: opensearchproject/opensearch-dashboards:2.1.0
container_name: opensearch-dashboards
ports:
- 5601:5601
expose:
- "5601"
environment:
#- 'OPENSEARCH_HOSTS=["https://opensearch-node1:9200"]'
- "DISABLE_SECURITY_DASHBOARDS_PLUGIN=false" # disables security dashboards plugin in OpenSearch Dashboards
networks:
- opensearch-net
volumes:
opensearch-data1:
networks:
opensearch-net:
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/deploy-of-opensearch/opensearch_dashboards.yml
================================================
server.host: "0.0.0.0"
opensearch.hosts: ["https://opensearch-node1:9200"]
opensearch.ssl.verificationMode: none
opensearch.username: "kibanaserver"
opensearch.password: "kibanaserver"
opensearch.requestHeadersAllowlist: [ authorization,securitytenant ]
server.ssl.enabled: true
server.ssl.certificate: /usr/share/opensearch-dashboards/config/client-cert.pem
server.ssl.key: /usr/share/opensearch-dashboards/config/client-cert-key.pem
opensearch.ssl.certificateAuthorities: [ "/usr/share/opensearch-dashboards/config/root-ca.pem" ]
opensearch_security.multitenancy.enabled: true
opensearch_security.multitenancy.tenants.preferred: ["Private", "Global"]
opensearch_security.readonly_mode.roles: ["kibana_read_only"]
opensearch_security.cookie.secure: true
#disable_security_dashboards_plugin: false
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/functions/Dockerfile
================================================
FROM python:3.9.1-slim
RUN apt-get update
# docker build нужно запускать из папки export-auditlogs-to-Opensearch чтобы был правильный контекст при подборе include файлов
# пример docker build команды:
# docker build -t s3-opensearch-importer:latest -f ./functions/Dockerfile .
COPY /functions /app/functions
COPY /update-opensearch-scheme/include /app/include
WORKDIR /app
RUN pip install --upgrade pip
RUN pip install -r functions/requirements.txt
CMD ["python3", "functions/main.py"]
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/functions/main.py
================================================
import requests
import json
import os
import boto3
import time
import base64
# Function - Get token
def get_token():
response = requests.get('http://169.254.169.254/computeMetadata/v1/instance/service-accounts/default/token', headers={"Metadata-Flavor":"Google"})
return response.json().get('access_token')
# Function - Decrypt data with KMS key
def decrypt_secret_kms(secret):
token = get_token()
request_suffix = f"{kms_key_id}:decrypt"
request_json_data = {'ciphertext': secret}
response = requests.post('https://kms.yandex/kms/v1/keys/'+request_suffix, data=json.dumps(request_json_data), headers={"Accept":"application/json", "Authorization": "Bearer "+token})
b64_data = response.json().get('plaintext')
return base64.b64decode(b64_data).decode()
# # Configuration - Get ElasticSearch CA.pem
# def get_elastic_cert():
# file = '/app/include/CA.pem'
# if os.path.isfile(file):
# return file
# else:
# url = 'https://storage.yandexcloud.net/cloud-certs/CA.pem'
# response = requests.get(url)
# with open('/app/include/CA.pem', 'wb') as f:
# f.write(response.content)
# return file
# Configuration - Keys
kms_key_id = os.environ['KMS_KEY_ID']
elastic_auth_pw_encr = os.environ['ELK_PASS_ENCR']
s3_key_encr = os.environ['S3_KEY_ENCR']
s3_secret_encr = os.environ['S3_SECRET_ENCR']
# Configuration - Setting up variables for ElasticSearch
elastic_server = os.environ['ELASTIC_SERVER']
elastic_auth_user = os.environ['ELASTIC_AUTH_USER']
elastic_auth_pw = decrypt_secret_kms(elastic_auth_pw_encr)
elastic_index_name = f"{os.environ['ELASTIC_INDEX_NAME']}-000001"
elastic_index_alias = "audit-trails-index"
elastic_index_template = "audit-trails-template"
elastic_index_ilm = "audit-trails-ilm"
elastic_index_pipeline = "audit-trails-pipeline"
kibana_server = os.environ['KIBANA_SERVER']
fals = False #tls validation disable (please enable it when you use valid certificate)
#elastic_cert = get_elastic_cert()
# Configuration - Setting up variables for S3
s3_key = decrypt_secret_kms(s3_key_encr)
s3_secret = decrypt_secret_kms(s3_secret_encr)
s3_bucket = os.environ['S3_BUCKET']
s3_folder = os.environ['S3_FOLDER']
s3_local = '/tmp/s3'
# Configuration - Sleep time
if(os.getenv('SLEEP_TIME') is not None):
sleep_time = int(os.environ['SLEEP_TIME'])
else:
sleep_time = 240
# State - Setting up S3 client
s3 = boto3.resource('s3',
endpoint_url = 'https://storage.yandexcloud.net',
aws_access_key_id = s3_key,
aws_secret_access_key = s3_secret
)
# Create tenant
def create_tenant():
request_suffix = "/_plugins/_security/api/tenants/at-tenant"
request_json = """{
"description": "A tenant for the yandex cloud audit trails events."
}"""
response = requests.put(elastic_server+request_suffix, data=request_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json"})
if(response.status_code == 200):
print('Tenant -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Create config index in ElasticSearch
def create_config_index():
request_suffix = f"/.state-{elastic_index_alias}"
response = requests.get(elastic_server+request_suffix, verify=fals, auth=(elastic_auth_user, elastic_auth_pw))
if(response.status_code == 404):
request_suffix = f"/.state-{elastic_index_alias}/_doc/1"
request_json = """{
"is_configured": true
}"""
response = requests.post(elastic_server+request_suffix, data=request_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json"})
print('Config index -- CREATED')
else:
print('Config index -- EXISTS')
print(f"{response.status_code} - {response.text}")
# Function - Get config index state
def get_config_index_state():
request_suffix = f"/.state-{elastic_index_alias}/_doc/1"
response = requests.get(elastic_server+request_suffix, verify=fals, auth=(elastic_auth_user, elastic_auth_pw))
if(response.status_code != 200):
return False
print(f"{response.status_code} - {response.text}")
return True
# Function - Create ingest pipeline
def create_ingest_pipeline():
request_suffix = f"/_ingest/pipeline/{elastic_index_pipeline}"
data_file = open('/app/include/audit-trail/pipeline.json')
data_json = json.load(data_file)
data_file.close()
response = requests.put(elastic_server+request_suffix, json=data_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Ingest pipeline -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Create an index lifecycle policy
def create_lifecycle_policy():
request_suffix = f"/_plugins/_ism/policies/{elastic_index_ilm}"
data_file = open('/app/include/audit-trail/ism-policy.json')
data_json = json.load(data_file)
data_file.close()
response = requests.put(elastic_server+request_suffix, json=data_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index lifecycle policy -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Create an index template
def create_index_template():
request_suffix = f"/_index_template/{elastic_index_template}"
data_file = open('/app/include/audit-trail/index-template.json')
data_json = json.load(data_file)
data_file.close()
response = requests.put(elastic_server+request_suffix, json=data_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index template -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Create an index
def create_first_index():
request_suffix = f"/{elastic_index_name}"
response = requests.put(elastic_server+request_suffix, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"securitytenant":"at-tenant"})
if(response.status_code == 200):
print(f"Index {elastic_index_name} -- CREATED")
print(f"{response.status_code} - {response.text}")
# Function - Create an index alias
def create_index_alias():
request_suffix = f"/_aliases"
request_json = """{
"actions" : [
{ "add" : { "index" : "%s", "alias" : "%s" } }
]
}""" % (elastic_index_name, elastic_index_alias)
response = requests.post(elastic_server+request_suffix, data=request_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index alias -- CREATED')
print(f"{response.status_code} - {response.text}")
# Function - Refresh index
def refresh_index():
request_suffix = f"/{elastic_index_alias}/_refresh"
response = requests.post(elastic_server+request_suffix, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index -- REFRESHED')
print(f"{response.status_code} - {response.text}")
#----
# Function - Preconfigure Kibana
def configure_kibana():
#Index pattern
data_file = {
'file': open('/app/include/audit-trail/index-pattern.ndjson', 'rb')
}
request_suffix = '/api/saved_objects/_import'
response = requests.post(kibana_server+request_suffix, files=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"osd-xsrf":"true", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Index patterns -- IMPORTED')
print(f"{response.status_code} - {response.text}")
# Filters
data_file = {
'file': open('/app/include/audit-trail/filters.ndjson', 'rb')
}
request_suffix = '/api/saved_objects/_import'
response = requests.post(kibana_server+request_suffix, files=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"osd-xsrf":"true", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Filters -- IMPORTED')
print(f"{response.status_code} - {response.text}")
# Search
data_file = {
'file': open('/app/include/audit-trail/search.ndjson', 'rb')
}
request_suffix = '/api/saved_objects/_import'
response = requests.post(kibana_server+request_suffix, files=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"osd-xsrf":"true", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Searches -- IMPORTED')
print(f"{response.status_code} - {response.text}")
#Detections Alerts monitors
request_suffix = "/_plugins/_alerting/monitors"
data_file = open('/app/include/audit-trail/alert.json')
data_json = json.load(data_file)
data_file.close()
response = requests.post(elastic_server+request_suffix, json=data_json, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/json", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Alert monitor uploaded -- CREATED')
print(f"{response.status_code} - {response.text}")
#Dashboard
data_file = {
'file': open('/app/include/audit-trail/dashboard.ndjson', 'rb')
}
request_suffix = '/api/saved_objects/_import?overwrite=true'
response = requests.post(kibana_server+request_suffix, files=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"osd-xsrf":"true", "securitytenant":"at-tenant"})
if(response.status_code == 200):
print('Dashboard -- IMPORTED')
print(f"{response.status_code} - {response.text}")
# Function - Download JSON logs to local folder
def download_s3_folder(s3_bucket, s3_folder, local_folder=None):
print('JSON download -- STARTED')
bucket = s3.Bucket(s3_bucket)
if not os.path.exists(local_folder):
os.makedirs(local_folder)
for obj in bucket.objects.filter(Prefix=s3_folder):
target = obj.key if local_folder is None \
else os.path.join(local_folder, os.path.relpath(obj.key, s3_folder))
if not os.path.exists(local_folder):
os.makedirs(local_folder)
if obj.key[-1] == '/':
continue
# Downloading JSON logs in a flat-structured way
bucket.download_file(obj.key, local_folder+'/'+target.rsplit('/')[-1])
print('JSON download -- COMPLETE')
# Function - Clean up S3 folder
def delete_objects_s3(s3_bucket, s3_folder):
bucket = s3.Bucket(s3_bucket)
for obj in bucket.objects.filter(Prefix=s3_folder):
if(obj.key != s3_folder+'/'):
bucket.delete_objects(
Delete={
'Objects': [
{
'Key': obj.key
},
]
}
)
print('S3 bucket -- EMPTIED')
# Function - Upload logs to ElasticSearch
def upload_docs_bulk(s3_bucket, s3_folder):
print('JSON upload -- STARTED')
request_suffix = f"/{elastic_index_alias}/_bulk?pipeline={elastic_index_pipeline}"
error_count = 0
for f in os.listdir(s3_local):
if f.endswith(".json"):
with open(f"{s3_local}/{f}", "r") as read_file:
data = json.load(read_file)
result = [json.dumps(record) for record in data]
with open(f"{s3_local}/nd-temp.json", 'w') as obj:
for i in result:
obj.write('{"index":{}}\n')
obj.write(i+'\n')
data_file = open(f"{s3_local}/nd-temp.json", 'rb').read()
response = requests.post(elastic_server+request_suffix, data=data_file, verify=fals, auth=(elastic_auth_user, elastic_auth_pw), headers={"Content-Type":"application/x-ndjson"})
os.remove(s3_local+"/"+f)
if(response.status_code != 200):
error_count += 1
print(response.text)
print(f"{response.status_code} - {response.text}")
if(os.path.exists(f"{s3_local}/nd-temp.json")):
os.remove(f"{s3_local}/nd-temp.json")
print(f"JSON upload -- COMPLETE -- {error_count} ERRORS")
if(error_count == 0):
delete_objects_s3(s3_bucket, s3_folder)
refresh_index()
# Process - Upload data
def upload_logs():
if(get_config_index_state()):
print("Config index -- EXISTS")
download_s3_folder(s3_bucket, s3_folder, s3_local)
upload_docs_bulk(s3_bucket, s3_folder)
else:
create_tenant()
create_lifecycle_policy()
create_index_template()
create_first_index()
create_index_alias()
create_ingest_pipeline()
configure_kibana()
create_config_index()
download_s3_folder(s3_bucket, s3_folder, s3_local)
upload_docs_bulk(s3_bucket, s3_folder)
### MAIN CONTROL PANEL
upload_logs()
print("Sleep -- STARTED")
time.sleep(sleep_time)
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/functions/requirements.txt
================================================
requests
boto3
================================================
FILE: auditlogs/export-auditlogs-to-Opensearch/images/elastic.drawio
================================================
- etc/lists/audit-keys
- etc/lists/amazon/aws-eventnames
- etc/lists/security-eventchannel
- etc/lists/audit-keys
- etc/lists/amazon/aws-eventnames
- etc/lists/security-eventchannel
map(object({
zone = string
cidr = string
})) | n/a | yes |
## Outputs
| Name | Description |
|------|-------------|
| [subnets\_locations](#output\_subnets\_locations) | Mapping Subnet Name to Subnet ID |
| [vpc\_id](#output\_vpc\_id) | Yandex network id |
================================================
FILE: auditlogs/export-auditlogs-to-wazuh/terraform/modules/vpc/main.tf
================================================
resource "yandex_vpc_network" "this" {
name = var.vpc_name
labels = var.labels
}
resource "yandex_vpc_subnet" "this" {
for_each = var.vpc_subnets
network_id = yandex_vpc_network.this.id
name = each.key
v4_cidr_blocks = [each.value.cidr]
zone = each.value.zone
labels = var.labels
}
================================================
FILE: auditlogs/export-auditlogs-to-wazuh/terraform/modules/vpc/outputs.tf
================================================
output "vpc_id" {
description = "Yandex network id"
value = try(yandex_vpc_network.this.id, "")
}
output "subnets_locations" {
description = "Mapping Subnet Name to Subnet ID"
value = [
for s in yandex_vpc_subnet.this :
{
subnet_id = s.id, zone = s.zone
}
]
}
================================================
FILE: auditlogs/export-auditlogs-to-wazuh/terraform/modules/vpc/terraform.tf
================================================
terraform {
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = "0.77.0"
}
}
}
================================================
FILE: auditlogs/export-auditlogs-to-wazuh/terraform/modules/vpc/variables.tf
================================================
variable "vpc_name" {
description = "Yandex vpc name"
type = string
}
variable "vpc_subnets" {
description = "Map of vpc zone with cidr"
type = map(object({
zone = string
cidr = string
}))
}
variable "labels" {
description = "Labels for resources"
type = map(string)
default = {}
}
================================================
FILE: auditlogs/export-k8s-to-s3/README.md
================================================
## Export of kubernetes audit logs to s3/object storage

Prerequisites:
- ✅ Cluster of Managed K8s.
- ✅ Terraform
- ✅ Ask cloud support or your architect for an alpha flag "TRIGGERS_CLOUD_LOGS_ALPHA"
##
1) If you doing this from Russia just create the file and fill it out like this to use yandex network mirror:
```
cat ~/.terraformrc
provider_installation {
network_mirror {
url = "https://terraform-network-mirror.storage.yandexcloud.net/"
}
}
```
2) Fill out the fields in the provider.tf file.
3) Fill out the fields in the terraform.tfvars.example file. (example below)
4) Run:
```
terraform init
terraform apply
```
Example of terraform.tfvars.example file:
```
folder_id = "b1gvnphpkgt8oechmpo02"
cloud_id = "b1g3o4minpkuh10pd2rj2"
cluster_name = "k8s-for-export"
log_bucket_name = "k8s-audit-logs-example"
```
================================================
FILE: auditlogs/export-k8s-to-s3/terraform/00-sa-and-bucket.tf
================================================
#random
resource "random_string" "random" {
length = 4
special = false
upper = false
}
# Create SA for creation bucket
resource "yandex_iam_service_account" "sa-writer" {
folder_id = var.folder_id
name = "sa-for-k8s-export"
}
# Grant permissions send logs to bucket
resource "yandex_resourcemanager_folder_iam_member" "create_bucket" {
depends_on = [yandex_iam_service_account.sa-writer]
folder_id = var.folder_id
role = "storage.admin"
member = "serviceAccount:${yandex_iam_service_account.sa-writer.id}"
}
# Create Static Access Keys
resource "yandex_iam_service_account_static_access_key" "sa-writer-keys" {
depends_on = [yandex_iam_service_account.sa-writer]
service_account_id = yandex_iam_service_account.sa-writer.id
description = "Static access/secret keys for SA"
}
# Create bucket
resource "yandex_storage_bucket" "es-bucket" {
depends_on = [yandex_resourcemanager_folder_iam_member.upload_logs]
access_key = yandex_iam_service_account_static_access_key.sa-writer-keys.access_key
secret_key = yandex_iam_service_account_static_access_key.sa-writer-keys.secret_key
bucket = "${var.log_bucket_name}-${random_string.random.result}"
grant {
id = yandex_iam_service_account.sa-writer-to-bucket.id
type = "CanonicalUser"
permissions = ["READ", "WRITE"]
}
}
#------
# Create SA for read/write bucket
resource "yandex_iam_service_account" "sa-writer-to-bucket" {
folder_id = var.folder_id
name = "sa-for-writing-k8s-for-export"
}
# Grant permissions send logs to bucket
resource "yandex_resourcemanager_folder_iam_member" "upload_logs" {
depends_on = [yandex_iam_service_account.sa-writer-to-bucket]
folder_id = var.folder_id
role = "storage.uploader"
member = "serviceAccount:${yandex_iam_service_account.sa-writer-to-bucket.id}"
}
# Grant permissions send logs to bucket
resource "yandex_resourcemanager_folder_iam_member" "upload_logs2" {
depends_on = [yandex_iam_service_account.sa-writer-to-bucket]
folder_id = var.folder_id
role = "serverless.functions.invoker"
member = "serviceAccount:${yandex_iam_service_account.sa-writer-to-bucket.id}"
}
# Create Static Access Keys
resource "yandex_iam_service_account_static_access_key" "sa-writer-to-bucket-keys" {
depends_on = [yandex_iam_service_account.sa-writer-to-bucket]
service_account_id = yandex_iam_service_account.sa-writer-to-bucket.id
description = "Static access/secret keys for SA"
}
================================================
FILE: auditlogs/export-k8s-to-s3/terraform/03-infra.tf
================================================
data "yandex_kubernetes_cluster" "my_cluster" {
folder_id = var.folder_id
name = var.cluster_name
}
data "yandex_resourcemanager_folder" "my_folder" {
folder_id = var.folder_id
}
================================================
FILE: auditlogs/export-k8s-to-s3/terraform/04-audit-export.tf
================================================
data "archive_file" "function_export" {
type = "zip"
source_dir = "${path.module}/function"
output_path = "${path.module}/sync.zip"
}
resource "yandex_function" "k8s_log_exporter" {
folder_id = var.folder_id
name = "k8s-log-exporter-${data.yandex_kubernetes_cluster.my_cluster.name}"
runtime = "python38"
entrypoint = "main.handler"
memory = "128"
execution_timeout = "30"
service_account_id = yandex_iam_service_account.sa-writer-to-bucket.id
environment = {
AWS_ACCESS_KEY_ID = yandex_iam_service_account_static_access_key.sa-writer-to-bucket-keys.access_key
AWS_SECRET_ACCESS_KEY = yandex_iam_service_account_static_access_key.sa-writer-to-bucket-keys.secret_key
BUCKET_NAME = "${var.log_bucket_name}-${random_string.random.result}"
CLOUD_ID = data.yandex_resourcemanager_folder.my_folder.cloud_id
CLUSTER_ID = data.yandex_kubernetes_cluster.my_cluster.id
FOLDER_ID = var.folder_id
}
user_hash = data.archive_file.function_export.output_base64sha256
content {
zip_filename = data.archive_file.function_export.output_path
}
}
resource "yandex_function_trigger" "logs-trigger" {
depends_on = [yandex_function.k8s_log_exporter]
name = "k8s-log-trigger-${data.yandex_kubernetes_cluster.my_cluster.name}"
folder_id = var.folder_id
function {
id = yandex_function.k8s_log_exporter.id
service_account_id = yandex_iam_service_account.sa-writer-to-bucket.id
}
log_group {
log_group_ids = [
data.yandex_kubernetes_cluster.my_cluster.log_group_id,
]
batch_cutoff = 10
batch_size = 100
}
}
================================================
FILE: auditlogs/export-k8s-to-s3/terraform/function/main.py
================================================
import json
import os
import sys
import uuid
import boto3
import string
import random
from datetime import datetime
def get_random_alphanumeric_string(length):
letters_and_digits = string.ascii_letters + string.digits
result_str = ''.join((random.choice(letters_and_digits) for i in range(length)))
return result_str
client = boto3.client(
service_name='s3',
endpoint_url='https://storage.yandexcloud.net',
region_name='ru-central1'
)
def handler(event, context):
for log_data in event['messages']:
full_log = []
for log_entry in log_data['details']['messages']:
kubernetes_log = json.loads(log_entry['message'])
full_log.append(json.dumps(kubernetes_log))
bucket_name = os.environ.get('BUCKET_NAME')
# object_key = os.environ.get('LOG_PREFIX')+'/'+datetime.now().strftime('%Y-%m-%d-%H:%M:%S')+'-'+get_random_alphanumeric_string(5)
object_key = 'AUDIT/'+os.environ.get('CLUSTER_ID')+'/'+datetime.now().strftime('%Y-%m-%d-%H:%M:%S')+'-'+get_random_alphanumeric_string(5)
object_value = '\n'.join(full_log)
client.put_object(Bucket=bucket_name, Key=object_key, Body=object_value, StorageClass='COLD')
print(object_value)
================================================
FILE: auditlogs/export-k8s-to-s3/terraform/function/requirements.txt
================================================
botocore
boto3
================================================
FILE: auditlogs/export-k8s-to-s3/terraform/provider.tf
================================================
terraform {
required_version = ">= 0.14"
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = ">= 0.72.0"
}
}
}
provider "yandex" {
folder_id = var.folder_id
token = "example"
#service_account_key_file = "./key.json"
}
================================================
FILE: auditlogs/export-k8s-to-s3/terraform/variables.tf
================================================
# Variables for Import
# Initial variables
variable "folder_id" {
description = "The Yandex.Cloud folder id."
type = string
}
variable "cloud_id" {
description = "The Yandex.Cloud cloud id."
type = string
}
variable "region_name" {
description = "The Yandex.Cloud Cloud Region name."
type = string
default = "ru-central1"
}
variable "cluster_name" {
description = "The Yandex.Cloud K8s cluster name."
type = string
}
# S3 Bucket Variables
variable "log_bucket_name" {
type = string
}
================================================
FILE: auditlogs/export-k8s-to-s3-cloud-logging/README.md
================================================
# Export of Kubernetes audit logs to Object Storage
This Terraform example deploys a Cloud Function with a Trigger and scraps the Kubernetes cluster audit logs from Cloud Logging group and stores the logs in the Object Storage bucket.
Cloud Logging group can be created with Yandex Data Streams support, so your audit logs can be forwarded to Yandex Data Stream in parallel.
See [Creating a log group using CLI](https://cloud.yandex.com/en/docs/logging/operations/create-group) instruction for more information.

Prerequisites:
- ✅ Cluster of Managed K8s
- ✅ Cloud Logging logging group
- ✅ Terraform
##
1) If you apply this module from Russian Federation – create the `~/.terraformrc` file and specify Yandex Cloud network mirror:
```
cat ~/.terraformrc
provider_installation {
network_mirror {
url = "https://terraform-network-mirror.storage.yandexcloud.net/"
}
}
```
2) Fill out the fields in the `provider.tf` file: specify the token for authentication, or use service account key file.
3) Create a `private.auto.tfvars` file and fill the required variables. (see example of `private.auto.tfvars` file below)
4) Run:
```
terraform init
terraform apply
```
Example of `private.auto.tfvars` file:
```
cloud_id = "b1g3xxxxxxxxxxxxxxxx"
folder_id = "b1g7xxxxxxxxxxxxxxxx"
cluster_id = "catsxxxxxxxxxxxxxxxx"
logging_group_id = "e23oxxxxxxxxxxxxxxxx"
storage_bucket_name = "audit-log-bucket-xxxxxx"
```
================================================
FILE: auditlogs/export-k8s-to-s3-cloud-logging/terraform/function/main.py
================================================
import boto3
import json
import os
import random
import string
from datetime import datetime
# Variables
config = {
'bucket_name' : os.environ['BUCKET_NAME'],
}
# Function - Random string
def get_random_alphanumeric_string(length):
letters_and_digits = string.ascii_letters + string.digits
result = ''.join((random.choice(letters_and_digits) for i in range(length)))
return result
# Boto client
client = boto3.client(
service_name='s3',
endpoint_url='https://storage.yandexcloud.net',
region_name='ru-central1'
)
# Handler
def handler(event, context):
for log_data in event['messages']:
full_log = []
for log_entry in log_data['details']['messages']:
# Temporary filter
try:
if (log_entry['json_payload']['apiVersion'] == "audit.k8s.io/v1"):
full_log.append(json.dumps(log_entry))
else:
print("wrong apiVersion key")
except KeyError:
print("no apiVersion key")
# Temporary filter end
object_key = 'AUDIT/'+datetime.now().strftime('%Y-%m-%d-%H:%M:%S')+'-'+get_random_alphanumeric_string(5)
object_value = '\n'.join(full_log)
client.put_object(Bucket=config['bucket_name'], Key=object_key, Body=object_value)
print(object_value)
================================================
FILE: auditlogs/export-k8s-to-s3-cloud-logging/terraform/function/requirements.txt
================================================
botocore
boto3
================================================
FILE: auditlogs/export-k8s-to-s3-cloud-logging/terraform/main.tf
================================================
# Various
data "archive_file" "function" {
type = "zip"
source_dir = "${path.module}/function"
output_path = "${path.module}/function.zip"
}
resource "random_string" "suffix" {
length = 4
upper = false
lower = true
number = true
special = false
}
# Cloud Function
resource "yandex_function" "main" {
depends_on = [
yandex_iam_service_account_static_access_key.sa-static-key,
yandex_lockbox_secret_iam_binding.sa-viewer
]
folder_id = var.folder_id
name = "cloud-log-s3-${random_string.suffix.result}"
runtime = "python39"
entrypoint = "main.handler"
memory = "256"
execution_timeout = "60"
service_account_id = yandex_iam_service_account.sa.id
environment = {
BUCKET_NAME = var.storage_bucket_name
}
secrets {
id = yandex_lockbox_secret.secret-aws.id
version_id = yandex_lockbox_secret_version.secret-aws-v1.id
key = "access_key"
environment_variable = "AWS_ACCESS_KEY_ID"
}
secrets {
id = yandex_lockbox_secret.secret-aws.id
version_id = yandex_lockbox_secret_version.secret-aws-v1.id
key = "secret_key"
environment_variable = "AWS_SECRET_ACCESS_KEY"
}
user_hash = data.archive_file.function.output_base64sha256
content {
zip_filename = data.archive_file.function.output_path
}
}
# Cloud trigger
resource "yandex_function_trigger" "cloud-log" {
name = "cloud-log-s3-${random_string.suffix.result}"
description = "cloud-log-s3-${random_string.suffix.result}"
logging {
group_id = var.logging_group_id
batch_cutoff = "30"
batch_size = "100"
stream_names = ["audit"]
}
function {
id = yandex_function.main.id
service_account_id = yandex_iam_service_account.sa-invoker.id
}
}
# Create service account for bucket
resource "yandex_iam_service_account" "sa" {
folder_id = var.folder_id
name = "cloud-log-s3-${random_string.suffix.result}"
description = "cloud-log-s3-${random_string.suffix.result}"
}
resource "yandex_resourcemanager_folder_iam_member" "sa-log-reader" {
folder_id = var.folder_id
member = "serviceAccount:${yandex_iam_service_account.sa.id}"
role = "logging.reader"
}
resource "yandex_resourcemanager_folder_iam_member" "sa-storage-editor" {
folder_id = var.folder_id
member = "serviceAccount:${yandex_iam_service_account.sa.id}"
role = "storage.editor"
}
resource "yandex_resourcemanager_folder_iam_member" "sa-lockbox-payload" {
folder_id = var.folder_id
member = "serviceAccount:${yandex_iam_service_account.sa.id}"
role = "lockbox.payloadViewer"
}
# Create service account for function trigger
resource "yandex_iam_service_account" "sa-invoker" {
folder_id = var.folder_id
name = "cloud-log-s3-invoker-${random_string.suffix.result}"
description = "cloud-log-s3-invoker-${random_string.suffix.result}"
}
resource "yandex_resourcemanager_folder_iam_member" "sa-invoker" {
folder_id = var.folder_id
member = "serviceAccount:${yandex_iam_service_account.sa-invoker.id}"
role = "functions.functionInvoker"
}
# Static access key
resource "yandex_iam_service_account_static_access_key" "sa-static-key" {
service_account_id = yandex_iam_service_account.sa.id
description = "cloud-log-s3-${random_string.suffix.result} static key"
}
# Lockbox
resource "yandex_lockbox_secret" "secret-aws" {
name = "cloud-log-${random_string.suffix.result}"
}
resource "yandex_lockbox_secret_version" "secret-aws-v1" {
secret_id = yandex_lockbox_secret.secret-aws.id
entries {
key = "access_key"
text_value = yandex_iam_service_account_static_access_key.sa-static-key.access_key
}
entries {
key = "secret_key"
text_value = yandex_iam_service_account_static_access_key.sa-static-key.secret_key
}
}
resource "yandex_lockbox_secret_iam_binding" "sa-viewer" {
secret_id = yandex_lockbox_secret.secret-aws.id
role = "viewer"
members = [
"serviceAccount:${yandex_iam_service_account.sa.id}",
]
}
================================================
FILE: auditlogs/export-k8s-to-s3-cloud-logging/terraform/outputs.tf
================================================
output "function" {
value = "${yandex_function.main.name}"
}
================================================
FILE: auditlogs/export-k8s-to-s3-cloud-logging/terraform/provider.tf
================================================
terraform {
required_providers {
yandex = {
source = "yandex-cloud/yandex"
}
}
}
provider "yandex" {
# service_account_key_file = var.provider_key_file
cloud_id = var.cloud_id
folder_id = var.folder_id
zone = var.zone
token = "token"
}
================================================
FILE: auditlogs/export-k8s-to-s3-cloud-logging/terraform/variables.tf
================================================
variable "folder_id" {
description = "Yandex Cloud folder-id"
}
variable "cloud_id" {
description = "Yandex Cloud cloud-id"
}
variable "logging_group_id" {
description = "Cloud Logging group ID"
}
variable "storage_bucket_name" {
description = "Yandex Object Storage bucket name"
}
variable "zone" {
description = "Yandex Cloud region"
default = "ru-central1-a"
}
variable "provider_key_file" {
description = "Yandex Cloud provider key file"
default = "./key.json"
}
================================================
FILE: auditlogs/export-k8s-to-yds/README.md
================================================
## Export of kubernetes audit logs to Yandex Data Streams/Kinesis Data Streams

Prerequisites:
- ✅ Cluster of Managed K8s.
- ✅ Terraform
- ✅ Ask cloud support for an alpha flag "LOGS_ALPHA" and "TRIGGERS_CLOUD_LOGS_ALPHA"
- ✅ [Existing Yandex Data Streams](https://cloud.yandex.ru/services/data-streams)
- ✅ To get the **yds_id** parameter, go to the deployed YDS and copy it from the endpoint tab, for example
https://yds.serverless.yandexcloud.net/ru-central1/b1g3o4minpkuh10pd2rj/**etnrmbadnrson5algn3s**/stream-for-k8s-audit . Parameter etnrmbadnrson5algn3s is yds id
##
1) If you doing this from Russia just create the file and fill it out like this to use yandex network mirror:
```
cat ~/.terraformrc
provider_installation {
network_mirror {
url = "https://terraform-network-mirror.storage.yandexcloud.net/"
}
}
```
2) Fill out the fields in the provider.tf file.
3) Fill out the fields in the terraform.tfvars.example file. (example below)
4) Run:
```
terraform init
terraform apply
```
Example of terraform.tfvars.example file:
```
folder_id = "b1gvnphpkgt8oechmpo0"
cloud_id = "b1g3o4minpkuh10pd2rj"
cluster_name = "k8s-for-export"
yds_stream_name = "stream-for-k8s-audit"
yds_id = "b1g3o4minpkuh10pd2rj"
yds_ydb_id = "etnrmbadnrson5algn3s"
```
================================================
FILE: auditlogs/export-k8s-to-yds/terraform/00-sa-and-bucket.tf
================================================
#random
resource "random_string" "random" {
length = 4
special = false
upper = false
}
#------
# Create SA for read/write yds
resource "yandex_iam_service_account" "sa-writer-to-yds" {
folder_id = var.folder_id
name = "sa-for-writing-k8s-for-export"
}
# Grant permissions send logs to bucket
resource "yandex_resourcemanager_folder_iam_member" "upload_logs" {
depends_on = [yandex_iam_service_account.sa-writer-to-yds]
folder_id = var.folder_id
role = "yds.writer"
member = "serviceAccount:${yandex_iam_service_account.sa-writer-to-yds.id}"
}
# Grant permissions invoke
resource "yandex_resourcemanager_folder_iam_member" "upload_logs2" {
depends_on = [yandex_iam_service_account.sa-writer-to-yds]
folder_id = var.folder_id
role = "serverless.functions.invoker"
member = "serviceAccount:${yandex_iam_service_account.sa-writer-to-yds.id}"
}
# Create Static Access Keys
resource "yandex_iam_service_account_static_access_key" "sa-writer-to-yds-keys" {
depends_on = [yandex_iam_service_account.sa-writer-to-yds]
service_account_id = yandex_iam_service_account.sa-writer-to-yds.id
description = "Static access/secret keys for SA"
}
================================================
FILE: auditlogs/export-k8s-to-yds/terraform/03-infra.tf
================================================
data "yandex_kubernetes_cluster" "my_cluster" {
folder_id = var.folder_id
name = var.cluster_name
}
data "yandex_resourcemanager_folder" "my_folder" {
folder_id = var.folder_id
}
================================================
FILE: auditlogs/export-k8s-to-yds/terraform/04-audit-export.tf
================================================
data "archive_file" "function_export" {
type = "zip"
source_dir = "${path.module}/function"
output_path = "${path.module}/sync.zip"
}
resource "yandex_function" "k8s_log_exporter" {
folder_id = var.folder_id
name = "k8s-log-exporter-${data.yandex_kubernetes_cluster.my_cluster.name}"
runtime = "python38"
entrypoint = "main.handler"
memory = "128"
execution_timeout = "30"
service_account_id = yandex_iam_service_account.sa-writer-to-yds.id
environment = {
AWS_ACCESS_KEY_ID = yandex_iam_service_account_static_access_key.sa-writer-to-yds-keys.access_key
AWS_SECRET_ACCESS_KEY = yandex_iam_service_account_static_access_key.sa-writer-to-yds-keys.secret_key
CLOUD_ID = data.yandex_resourcemanager_folder.my_folder.cloud_id
CLUSTER_ID = data.yandex_kubernetes_cluster.my_cluster.id
FOLDER_ID = var.folder_id
YDS_NAME = var.yds_stream_name
YDS_YDB_ID = var.yds_ydb_id
YDS_ID = var.yds_id
}
user_hash = data.archive_file.function_export.output_base64sha256
content {
zip_filename = data.archive_file.function_export.output_path
}
}
resource "yandex_function_trigger" "logs-trigger" {
depends_on = [yandex_function.k8s_log_exporter]
name = "k8s-log-trigger-${data.yandex_kubernetes_cluster.my_cluster.name}"
folder_id = var.folder_id
function {
id = yandex_function.k8s_log_exporter.id
service_account_id = yandex_iam_service_account.sa-writer-to-yds.id
}
log_group {
log_group_ids = [
data.yandex_kubernetes_cluster.my_cluster.log_group_id,
]
batch_cutoff = 10
batch_size = 100
}
}
================================================
FILE: auditlogs/export-k8s-to-yds/terraform/function/main.py
================================================
import json
import os
import sys
import uuid
import boto3
import string
import random
from datetime import datetime
def get_random_alphanumeric_string(length):
letters_and_digits = string.ascii_letters + string.digits
result_str = ''.join((random.choice(letters_and_digits) for i in range(length)))
return result_str
# client = boto3.client(
# service_name='s3',
# endpoint_url='https://storage.yandexcloud.net',
# region_name='ru-central1'
# )
client = boto3.client(
'kinesis',
endpoint_url='https://yds.serverless.yandexcloud.net',
region_name='ru-central1'
)
def handler(event, context):
yds_name = os.environ.get('YDS_NAME')
yds_id = os.environ.get('YDS_ID')
yds_ydb_id = os.environ.get('YDS_YDB_ID')
folder_name = os.environ.get('CLOUD_ID')
push_to_kinesis = []
for log_data in event['messages']:
for log_entry in log_data['details']['messages']:
push_to_kinesis.append({'Data': log_entry['message'],'PartitionKey': str(get_random_alphanumeric_string(5))} )
response = client.put_records(StreamName="/ru-central1/{folder}/{database}/{stream}".format(folder=folder_name, database=yds_ydb_id, stream=yds_name), Records=push_to_kinesis)
num_of_records = len(push_to_kinesis)
print(f'Records count - {num_of_records}')
print(f'Response from YDS - {response}')
================================================
FILE: auditlogs/export-k8s-to-yds/terraform/function/requirements.txt
================================================
botocore
boto3
================================================
FILE: auditlogs/export-k8s-to-yds/terraform/provider.tf
================================================
terraform {
required_version = ">= 0.14"
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = ">= 0.72.0"
}
}
}
provider "yandex" {
folder_id = var.folder_id
token = "example"
#service_account_key_file = "./key.json"
}
================================================
FILE: auditlogs/export-k8s-to-yds/terraform/terraformrc
================================================
provider_installation {
network_mirror {
url = "https://terraform-network-mirror.storage.yandexcloud.net/"
}
}
================================================
FILE: auditlogs/export-k8s-to-yds/terraform/variables.tf
================================================
# Variables for Import
# Initial variables
variable "folder_id" {
description = "The Yandex.Cloud folder id."
type = string
}
variable "cloud_id" {
description = "The Yandex.Cloud cloud id."
type = string
}
variable "region_name" {
description = "The Yandex.Cloud Cloud Region name."
type = string
default = "ru-central1"
}
variable "cluster_name" {
description = "The Yandex.Cloud K8s cluster name."
type = string
}
variable "yds_stream_name" {
description = "The Yandex.Cloud yds stream name."
type = string
}
variable "yds_ydb_id" {
description = "ID of YDB"
type = string
}
variable "yds_id" {
description = "ID of YDS"
type = string
}
================================================
FILE: auditlogs/trail_monitoring/README.md
================================================
## Monitoring Audit Trails and events in Yandex Cloud Monitoring


### Description
The solution includes recommendations how to monitor Audit Trails performance and its security events using [Yandex Monitoring](https://cloud.yandex.ru/services/monitoring).
- Audit Trails monitoring:
- The status of the Trail object (Active or not Active).
- Count of processed events (the presence of bursts).
- Monitoring of security events:
- The list is presented below.
#### Audit Trails monitoring
- Go to Audit Trails → Monitoring → Open in Monitoring.
- Select the desired dashboard: Trails by status or Delivered events.
- Click the ellipsis, select "Create alert".
- Set up an alert according to the [documentation](https://cloud.yandex.ru/docs/monitoring/operations/alert/create-alert) for a certain threshold. For example, on the "Trails by status" dashboard, enter the condition: status is not equal to 1 in 5 minutes (once a second, Trail sends Metric 1 if alive).

#### Monitoring events from Audit Trails
- Go to Audit Trails → Monitoring → Open in Monitoring → Metric Explorer.
- Generate a request to the desired metric from the list below, for example: "trail.processed_events_count"{folderId="b1gh4nansv4ebqqmeu7b", service="audit-trails", event_type="yandex.cloud.audit.compute.CreateInstance"}"
- Click the ellipsis → Create alert.
- Set up an alert according to the [documentation](https://cloud.yandex.ru/docs/monitoring/operations/alert/create-alert) for your threshold, for example: greater than 0.

#### List of metrics related to Information Security
- UpdateSecurityGroup: Updating a security group.
- UpdateSecretAccessBindings: Assigning rights for a Lockbox secret.
- AddInstanceOneToOneNat: Adding a public IP address for a VM instance.
- RemoveInstanceOneToOneNat: Removing a public IP address from a VM instance.
- DeleteInstance: Deleting a VM instance.
- instancegroup.DeleteInstanceGroup: Deleting an instance group.
- CreateAccessKey: Creating an access key.
- CreateApiKey: Creating an API key.
- DeleteFederation: Deleting a federation.
- UpdateServiceAccountAccessBindings: Updating access bindings.
- DeleteSymmetricKey: Deleting a symmetric key.
- ScheduleSymmetricKeyVersionDestruction: Scheduling destruction of the symmetric key version.
- DeleteCloud: Deleting a cloud.
- DeleteFolder: Deleting a catalog.
- BucketAclUpdate: Updating an ACL bucket.
- BucketDelete: Deleting a bucket.
- BucketPolicyUpdate: Editing bucket access policies.
- CreateNetwork: Creating a cloud network.
- DeleteNetwork: Deleting a cloud network.
================================================
FILE: auditlogs/trail_monitoring/README_RU.md
================================================
## Мониторинг Audit Trails и событий в Yandex Cloud Monitoring


### Описание
Решение содержит рекомендации о том, как мониторить работоспособность самого сервиса Audit Trails и событий безопасности с помощью сервиса [Yandex Monitoring](https://cloud.yandex.ru/services/monitoring)
- Мониторинг самого сервиса Audit Trails:
- статус объета Trail (Active или не Active)
- кол-во обработанных событий (наличие всплесков)
- Мониторинг событий безопасности:
- список представлен ниже
#### Мониторинг самого сервиса Audit Trails
- Перейдите в Audit Trails -> Monitoring -> Открыть в мониторинге
- Выберите необходимый dashboard: "Trails by status" или "Delivered events"
- Нажмите на "..."(троеточие) , выберите "создать алерт"
- Настройте [алерт согласно документации](https://cloud.yandex.ru/docs/monitoring/operations/alert/create-alert) на интересующий вас порог,например на dashboard "Trails by status" условие "status не равен 1 в течении 5 минут" (раз в секунду trail шлет метрику 1, если жив)

#### Мониторинг событий из Audit Trails
- Перейдите в Audit Trails -> Monitoring -> Открыть в мониторинге -> Обзор метрик
- Сформируйте необходимый запрос к желаемой метрике из списка ниже, например: "trail.processed_events_count"{folderId="b1gh4nansv4ebqqmeu7b", service="audit-trails", event_type="yandex.cloud.audit.compute.CreateInstance"}"
- Нажмите на "..." троеточие -> "Создать алерт"
- Настройте [алерт согласно документации](https://cloud.yandex.ru/docs/monitoring/operations/alert/create-alert) на интересующий вас порог, например "Больше 0"

#### Список интересных метрик с точки зрения ИБ
- UpdateSecurityGroup (Изменение группы безопасности)
- UpdateSecretAccessBindings (Назначение прав на lockbox секрет)
- AddInstanceOneToOneNat (Добавление публичного IP-адреса виртуальной машине)
- RemoveInstanceOneToOneNat (Удаление публичного IP-адреса ВМ.)
- DeleteInstance (удаление ВМ)
- instancegroup.DeleteInstanceGroup (удаление группы ВМ)
- CreateAccessKey (Создание ключа доступа)
- CreateApiKey (Создание API ключа)
- DeleteFederation (удаление федерации)
- UpdateServiceAccountAccessBindings (Обновление списка привязок прав доступа)
- DeleteSymmetricKeyy (Удаление симметричного ключа.)
- ScheduleSymmetricKeyVersionDestruction (Запланирование уничтожения версии симметричного ключа.)
- DeleteCloud (Удаление облака)
- DeleteFolder (Удаление папки)
- BucketAclUpdate (Изменение ACL бакета.)
- BucketDelete (Удаление бакета.)
- BucketPolicyUpdate (Изменение политик доступа бакета.)
- CreateNetwork (Создание облачной сети.)
- DeleteNetwork (Удаление облачной сети.)
- др.
================================================
FILE: auditlogs/trails-function-detector/README.md
================================================
## Yandex.Cloud Trails-function-detector: Alerts and response to Information Security events in Audit Trails using Cloud Logging and Cloud Functions + Telegram


 #### To be revised
- Function_trigger on Cloud Logging in Terraform
- Audit Trails in Terraform
#### Description
The solution uses Cloud Functions and Audit Trails to perform:
- Telegram alerts for the following Audit Trails events (optional):
- Create danger, ingress ACL in SG (0.0.0.0/0).
- Change Bucket access to public.
- Assign rights to the secret (Lockbox) to some account.
- To be updated on request based on the [list of current use cases](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches).
- Active response (optional):
- Removing a dangerous security group rule: for Rule No. 1.
- Removing assigned rights for a secret in Lockbox: for Rule #3.
- Telegram alerting for any selected Audit Trails event.
#### Generic diagram

#### Prerequisites:
- :white_check_mark: A custom log group created in Cloud Logging ([instructions](https://cloud.yandex.ru/docs/logging/operations/create-group)).
- :white_check_mark: Audit Trails service enabled with logs output to the Cloud Logging log group ([instructions](https://cloud.yandex.ru/docs/audit-trails/quickstart)).
- :white_check_mark: Service account (it will be granted relevant rights).
- :white_check_mark: A bot created in Telegram ([instructions](https://tlgrm.ru/docs/bots#kak-sozdat-bota)).
- :white_check_mark: ID of the chat with a Telegram bot (to get the Chat ID, first write at least one message to the bot, then use https://api.telegram.org/bot
#### To be revised
- Function_trigger on Cloud Logging in Terraform
- Audit Trails in Terraform
#### Description
The solution uses Cloud Functions and Audit Trails to perform:
- Telegram alerts for the following Audit Trails events (optional):
- Create danger, ingress ACL in SG (0.0.0.0/0).
- Change Bucket access to public.
- Assign rights to the secret (Lockbox) to some account.
- To be updated on request based on the [list of current use cases](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches).
- Active response (optional):
- Removing a dangerous security group rule: for Rule No. 1.
- Removing assigned rights for a secret in Lockbox: for Rule #3.
- Telegram alerting for any selected Audit Trails event.
#### Generic diagram

#### Prerequisites:
- :white_check_mark: A custom log group created in Cloud Logging ([instructions](https://cloud.yandex.ru/docs/logging/operations/create-group)).
- :white_check_mark: Audit Trails service enabled with logs output to the Cloud Logging log group ([instructions](https://cloud.yandex.ru/docs/audit-trails/quickstart)).
- :white_check_mark: Service account (it will be granted relevant rights).
- :white_check_mark: A bot created in Telegram ([instructions](https://tlgrm.ru/docs/bots#kak-sozdat-bota)).
- :white_check_mark: ID of the chat with a Telegram bot (to get the Chat ID, first write at least one message to the bot, then use https://api.telegram.org/bot
 #### Будет доработано
- Function_trigger на CloudLogging в terraform
- AuditTrails в terraform
#### Описание
Решение выполняет c помощью CloudFunctions и AuditTrails:
- Оповщение в telegram на следующие события AuditTrails (опционально):
- 1)"Create danger, ingress ACL in SG (0.0.0.0/0)"
- 2)"Change Bucket access to public"
- 3)"Assign rights to the secret (Lockbox) to some account"
- Будут добавляться по запросам желающих (из [списка актуальных Use cases](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches))
- (Опционально) Активное реагирование:
- Удаление опасного правила группы безопасности (для правила № 1)
- Удаление назначенных прав на секрет в Lockbox (для правила № 3)
- Оповещение в telegram на любое событие AuditTrails (на выбор)
#### Общая схема

#### Пререквизиты
- :white_check_mark: Созданная custom лог группа в CloudLogging ([инструкция](https://cloud.yandex.ru/docs/logging/operations/create-group))
- :white_check_mark: Включенный сервис Audit Trails (с выводом логов в лог группу CloudLogging) ([инструкция](https://cloud.yandex.ru/docs/audit-trails/quickstart))
- :white_check_mark: Сервисный аккаунт (ему будут выданы необходимые права)
- :white_check_mark: Созданный бот в telegram ([инструкция](https://tlgrm.ru/docs/bots#kak-sozdat-bota))
- :white_check_mark: ID чата с telegram ботом (для получения chat-id сначала пишем хотябы одно сообщение боту, далее используем https://api.telegram.org/bot
#### Будет доработано
- Function_trigger на CloudLogging в terraform
- AuditTrails в terraform
#### Описание
Решение выполняет c помощью CloudFunctions и AuditTrails:
- Оповщение в telegram на следующие события AuditTrails (опционально):
- 1)"Create danger, ingress ACL in SG (0.0.0.0/0)"
- 2)"Change Bucket access to public"
- 3)"Assign rights to the secret (Lockbox) to some account"
- Будут добавляться по запросам желающих (из [списка актуальных Use cases](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches))
- (Опционально) Активное реагирование:
- Удаление опасного правила группы безопасности (для правила № 1)
- Удаление назначенных прав на секрет в Lockbox (для правила № 3)
- Оповещение в telegram на любое событие AuditTrails (на выбор)
#### Общая схема

#### Пререквизиты
- :white_check_mark: Созданная custom лог группа в CloudLogging ([инструкция](https://cloud.yandex.ru/docs/logging/operations/create-group))
- :white_check_mark: Включенный сервис Audit Trails (с выводом логов в лог группу CloudLogging) ([инструкция](https://cloud.yandex.ru/docs/audit-trails/quickstart))
- :white_check_mark: Сервисный аккаунт (ему будут выданы необходимые права)
- :white_check_mark: Созданный бот в telegram ([инструкция](https://tlgrm.ru/docs/bots#kak-sozdat-bota))
- :white_check_mark: ID чата с telegram ботом (для получения chat-id сначала пишем хотябы одно сообщение боту, далее используем https://api.telegram.org/botIf Authoritative = true : take roles from all objects in variable "cloud\_user\_role\_mapping" and make **unique** role as a new key of map with members" | `bool` | `false` | no | | [cloud\_id](#input\_cloud\_id) | Cloud-ID where where need to add permissions. Mandatory variable for CLOUD, if omited default CLOUD\_ID will be used | `string` | `null` | no | | [cloud\_user\_role\_mapping](#input\_cloud\_user\_role\_mapping) | Group of IAM User-IDs and it's permissions in CLOUD, where name = JOB Tille(aka IAM Group). Use usernames or user-ids or both
### Example
#cloud\_user\_role\_mapping = [
{
job\_title\_name = "devops"
iam\_users\_names = ["name.surname", ]
fed\_users\_names = ["name.surname@yantoso.ru", ]
roles = ["editor", ]
},
{
job\_title\_name = "developers"
users\_with\_ids = ["userAccount:idxxxxxx1", "federatedUser:idxxxxxx2"]
iam\_users\_names = ["name.surname", ]
roles = ["viewer","k8s.editor",]
},
] | `any` | `[]` | no | | [federation\_id](#input\_federation\_id) | Federation ID, mandatory for 'fed\_users\_names' | `string` | `null` | no | | [folder\_binding\_authoritative](#input\_folder\_binding\_authoritative) | Authoritative. Sets the IAM policy for the FOLDER and replaces any **existing** policy already attached. | `bool` | `false` | no | | [folder\_id](#input\_folder\_id) | Folder-ID where need to add permissions. Mandatory variable for FOLDER, if omited default FOLDER\_ID will be used | `string` | `null` | no | | [folder\_user\_role\_mapping](#input\_folder\_user\_role\_mapping) | Group of IAM User-IDs and it's permissions in FOLDER, where name = JOB Tille(aka IAM Group). Use usernames or user-ids or both
### Example
#folder\_user\_role\_mapping = [
{
job\_title\_name = "devops"
iam\_users\_names = ["name.surname", ]
fed\_users\_names = ["name.surname@yantoso.ru", ]
roles = ["iam.serviceAccounts.user", "k8s.editor", "k8s.cluster-api.cluster-admin", "container-registry.admin"]
},
{
job\_title\_name = "developers"
users\_with\_ids = ["userAccount:idxxxxxx1", "federatedUser:idxxxxxx2"]
roles = ["k8s.viewer",]
},
] | `any` | `[]` | no | | [org\_binding\_authoritative](#input\_org\_binding\_authoritative) | "Authoritative. Sets the IAM policy for the ORGANIZATION and replaces any **existing** policy already attached.
If Authoritative = true : take roles from all objects in variable "org\_user\_role\_mapping" and make **unique** role as a new key of map with members" | `bool` | `false` | no | | [org\_id](#input\_org\_id) | ORGANIZATION-ID where where need to add permissions. Mandatory variable for ORGANIZATION, if omited default ORGANIZATION\_ID will be used | `string` | `null` | no | | [org\_user\_role\_mapping](#input\_org\_user\_role\_mapping) | Group of IAM User-IDs and it's permissions in ORGANIZATION, where name = JOB Tille(aka IAM Group). Use usernames or user-ids or both
### Example
#org\_user\_role\_mapping = [
{
job\_title\_name = "admins"
iam\_users\_names = ["name.surname", ]
fed\_users\_names = ["name.surname@yantoso.ru", ]
roles = ["admin",]
},
{
job\_title\_name = "network\_admins"
sers\_with\_ids = ["userAccount:idxxxxxx1", "federatedUser:idxxxxxx2"]
roles = ["vpc.admin",]
},
] | `any` | `[]` | no | | [sa\_role\_mapping](#input\_sa\_role\_mapping) | List of SA and it's permissions
### Example
sa\_role\_mapping = [
{
name = "sa-cluster"
roles = ["editor",]
},
{
name = "sa-nodes"
roles = ["container-registry.images.puller",]
},
] | `any` | `[]` | no | | [usernames\_to\_ids](#input\_usernames\_to\_ids) | If true Usernames from IAM and Federation will be used as input variables 'iam\_users\_names' and 'fed\_users\_names' | `bool` | `true` | no | ## Outputs | Name | Description | | ----------------------------------------------------------------- | ----------------------------------------------------------- | | [sa\_ids](#output\_sa\_ids) | List IDs of created service accounts | | [sa\_names](#output\_sa\_names) | List Names of created service accounts | | [sa\_object](#output\_sa\_object) | Map with service accounts info , key = service account name | ================================================ FILE: auth_and_access/iam/examples/custom roles/README.md ================================================ # Yandex.SCALE 2021 Assigning roles for to IAM users ## Configure Terraform for Yandex.Cloud - Install [YC cli](https://cloud.yandex.com/docs/cli/quickstart) - Add environment variables for terraform auth in Yandex.Cloud ``` export YC_TOKEN=$(yc iam create-token) ``` ## Quick Start Rename `terraform.tfvars.example` to `terraform.tfvars` and add your values To execute run: ``` terraform init terraform plan terraform apply ``` ================================================ FILE: auth_and_access/iam/examples/custom roles/cloud.tf ================================================ ### IAM module "iam_cloud" { source = "../.." org_id = var.org_id cloud_id = var.cloud_id cloud_user_role_mapping = [ { name = "cloud_admins" users = var.groups.cloud_admins roles = ["admin", ] }, { name = "cloud_members" ### Role Cloud.Member is needed for all users for UI enabling users = concat(var.groups.project_developers, var.groups.project_admins, var.groups.org_admins, var.groups.network_admins, var.groups.sec_ops, var.groups.cloud_admins) roles = ["resource-manager.clouds.member", ] }, ] } ================================================ FILE: auth_and_access/iam/examples/custom roles/organization.tf ================================================ ### IAM module "iam_org" { source = "../.." org_id = var.org_id org_user_role_mapping = [ { name = "organization_admins" users = var.groups.org_admins roles = ["admin", ] }, { name = "organization__network_admins" users = var.groups.network_admins roles = var.role_network_admin }, { name = "organization_sec_ops" users = var.groups.sec_ops roles = var.role_sec_ops }, ] } ================================================ FILE: auth_and_access/iam/examples/custom roles/projects.tf ================================================ ### IAM module "iam_dev_project" { source = "../.." cloud_id = var.cloud_id org_id = var.org_id folder_id = var.dev_folder_id folder_user_role_mapping = [ { name = "project_admins" users = var.groups.project_admins roles = ["admin", ] }, { name = "project_developers" users = var.groups.project_developers roles = var.role_dev_project_developer }, ] } module "iam_prod_project" { source = "../.." cloud_id = var.cloud_id org_id = var.org_id folder_id = var.prod_folder_id folder_user_role_mapping = [ { name = "project_admins" users = var.groups.project_admins roles = ["admin", ] }, { name = "project_developers" users = var.groups.project_developers roles = var.role_prod_project_developer }, ] } ================================================ FILE: auth_and_access/iam/examples/custom roles/terraform.tfvars.example ================================================ ###IDs org_id = "" cloud_id = "" prod_folder_id = "" dev_folder_id = "" ###Users groups = { network_admins = ["userAccount:idxxxxxx", ] org_admins = ["userAccount:idxxxxxx", ] sec_ops = ["userAccount:idxxxxxx", ] cloud_admins = ["userAccount:idxxxxxx", ] project_admins = ["userAccount:idxxxxxx", ] project_developers = ["userAccount:idxxxxxx", ] } ###Custom Roles role_network_admin = ["vpc.admin", "viewer", ] role_sec_ops = ["viewer", "kms.admin"] role_prod_project_developer = ["viewer", ] role_dev_project_developer = [ "k8s.admin", "k8s.cluster-api.cluster-admin", "compute.admin", "container-registry.admin", "load-balancer.privateAdmin", "storage.admin", "mdb.admin", "kms.admin", "iam.serviceAccounts.user", "vpc.user", "viewer" ] ================================================ FILE: auth_and_access/iam/examples/custom roles/variables.tf ================================================ variable "groups" { type = any description = "Map with key=group and value=list with iam users" } variable "role_network_admin" { type = list(any) description = "List of permissions/service roles for organization network admins" } variable "role_sec_ops" { type = list(any) description = "List of permissions/service roles for organization security officers" } variable "role_dev_project_developer" { type = list(any) description = "List of permissions/service roles for project_developers in DEV env" } variable "role_prod_project_developer" { type = list(any) description = "List of permissions/service roles for project_developers in PROD env" } variable "org_id" { type = string description = "ORGANIZATION-ID where where need to add permissions." } variable "dev_folder_id" { type = string description = "DEV Folder-ID where need to add permissions." } variable "prod_folder_id" { type = string description = "PROD Folder-ID where need to add permissions." } variable "cloud_id" { type = string description = "Cloud-ID where where need to add permissions. " } ================================================ FILE: auth_and_access/iam/examples/custom roles/versions.tf ================================================ terraform { required_version = ">= 1.0" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.62" } } } ================================================ FILE: auth_and_access/iam/examples/organization/README.md ================================================ # Assign roles for Organization and Cloud to IAM users Remember to change your **Organization-ID**, **CLOUD-ID**, **USER-ID** in `main.tf`. ## Configure Terraform for Yandex.Cloud - Install [YC cli](https://cloud.yandex.com/docs/cli/quickstart) - Add environment variables for terraform auth in Yandex.Cloud ``` export YC_TOKEN=$(yc iam create-token) ``` ## Quick Start To run this example you need to execute: ``` terraform init terraform plan terraform apply ``` ================================================ FILE: auth_and_access/iam/examples/organization/main.tf ================================================ ### IAM module "iam" { source = "../.." ## Edit with real ORG and CLOUD IDs org_id = "XXXXXXXXXXXXXXXXXXXX" cloud_id = "XXXXXXXXXXXXXXXXXXXX" ## Edit with real IAM users ID org_user_role_mapping = [ { name = "org_network_admins" users = ["userAccount:ajeu8bruia5h8sl53XXX", ] roles = ["vpc.admin", ] }, ] cloud_user_role_mapping = [ { name = "devops" users = ["userAccount:ajeu8bruia5h8sl53XXX", ] roles = ["editor", ] }, ] } ================================================ FILE: auth_and_access/iam/examples/organization/variables.tf ================================================ ================================================ FILE: auth_and_access/iam/examples/organization/versions.tf ================================================ terraform { required_version = ">= 1.0" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.62" } } } ================================================ FILE: auth_and_access/iam/examples/small/README.md ================================================ # Create service accounts and assign roles to IAM users Remember to change your **folder-ID** in variables. ## Configure Terraform for Yandex.Cloud - Install [YC cli](https://cloud.yandex.com/docs/cli/quickstart) - Add environment variables for terraform auth in Yandex.Cloud ``` export YC_TOKEN=$(yc iam create-token) export YC_CLOUD_ID=$(yc config get cloud-id) export YC_FOLDER_ID=$(yc config get folder-id) ``` ## Quick Start To run this example you need to execute: ``` terraform init terraform plan terraform apply ``` ================================================ FILE: auth_and_access/iam/examples/small/main.tf ================================================ ### IAM module "iam" { source = "../.." folder_id = "XXXXXXXXXXXXXXXXXXX" folder_binding_authoritative = false sa_role_mapping = [ { name = "sa-cluster" roles = ["editor"] }, { name = "sa-noroles" roles = [] }, { name = "sa-nodes" roles = ["container-registry.images.puller"] }, ] ## Edit with real IAM users ID folder_user_role_mapping = [ { name = "devops" users = ["serviceAccount:aje0k467i3bs3tst9d97", ] roles = ["iam.serviceAccounts.user", "k8s.admin", "k8s.cluster-api.cluster-admin", "container-registry.admin"] }, { name = "secops" users = ["serviceAccount:ajeg2qiqkhnkq3vms1eg", ] roles = [] }, { name = "developers" users = ["serviceAccount:ajevak8egbjo8v9ddl85", ] roles = ["k8s.viewer", "k8s.cluster-api.editor"] }, ] } ================================================ FILE: auth_and_access/iam/examples/small/outputs.tf ================================================ output "sa_map" { value = module.iam.sa description = "SA Map" } output "sa_names" { value = module.iam.names description = "List of SA names" } ================================================ FILE: auth_and_access/iam/examples/small/variables.tf ================================================ ================================================ FILE: auth_and_access/iam/examples/small/versions.tf ================================================ terraform { required_version = ">= 0.14" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.5" } } } ================================================ FILE: auth_and_access/iam/examples/use usernames/README.md ================================================ # Using IAM users (Yandex ID accounts) and Federated User instead user IDs Remember to change your in variables: * **folder-id** * **cloud-id** * **Users** * **federation_id** if exist ## Configure Terraform for Yandex.Cloud - Install [YC cli](https://cloud.yandex.com/docs/cli/quickstart) - Add environment variables for terraform auth in Yandex.Cloud ``` export YC_TOKEN=$(yc iam create-token) export YC_CLOUD_ID=$(yc config get cloud-id) export YC_FOLDER_ID=$(yc config get folder-id) ``` ## Quick Start To run this example you need to execute: ``` terraform init terraform plan terraform apply ``` ================================================ FILE: auth_and_access/iam/examples/use usernames/main.tf ================================================ ### IAM module "iam" { # !!! Using names instead ids federation_id = "XXXXXXXXXXXXXXXXX" usernames_to_ids = true cloud_id = "XXXXXXXXXXXXXXXX" cloud_user_role_mapping = [ { job_title_name = "admins" iam_users_names = ["name.surname", ] fed_users_names = ["name.surname@yantoso.ru", ] roles = ["admin",] }, { job_title_name = "network_admins" users_with_ids = ["userAccount:idxxxxxx1", "federatedUser:idxxxxxx2"] roles = ["vpc.admin",] }, ] folder_id = "XXXXXXXXXXXXXXXX" folder_user_role_mapping = [ { job_title_name = "devops" iam_users_names = ["name.surname", ] fed_users_names = ["name.surname@yantoso.ru", "name2.surname@yantoso.ru"] users_with_ids = [] roles = ["viewer", ] }, { job_title_name = "developer" iam_users_names = [] fed_users_names = ["name.surname@yantoso.ru"] users_with_ids = ["federatedUser:idxxxxxx2", "userAccount:idxxxxxx1", ] roles = ["k8s.admin", ] }, ] } ================================================ FILE: auth_and_access/iam/examples/use usernames/variables.tf ================================================ ================================================ FILE: auth_and_access/iam/examples/use usernames/versions.tf ================================================ terraform { required_version = ">= 1.0" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.68" } } } ================================================ FILE: auth_and_access/iam/examples/webinar_example/README.md ================================================ # Multi-environment infrastructure with centralized RBAC management Use `iam_mgmt` folder to set roles. Use `data.data.terraform_remote_state` to use newly created service accounts in dev/prod folders. Remember to change your **folder-IDs** in all environment folders. ## Configure Terraform for Yandex.Cloud - Install [YC cli](https://cloud.yandex.com/docs/cli/quickstart) - Add environment variables for terraform auth in Yandex.Cloud ``` export YC_TOKEN=$(yc iam create-token) export YC_CLOUD_ID=$(yc config get cloud-id) export YC_FOLDER_ID=$(yc config get folder-id) ``` ## Quick Start To run this example you need to execute from **all** folders: ``` terraform init terraform plan terraform apply ``` ================================================ FILE: auth_and_access/iam/examples/webinar_example/dev/main.tf ================================================ ### Datasource data "terraform_remote_state" "sa" { backend = "local" config = { path = "../iam_mgmt/terraform.tfstate" } } ### Networking module "vpc" { source = "../modules/networking" labels = var.labels network_description = var.network_description network_name = "${var.env}-${var.network_name}" folder_id = var.folder_id subnets = var.subnets } ### Container Registry resource "yandex_container_registry" "registry" { folder_id = var.folder_id name = "${var.env}-registry" } ### Kubernetes cluster resource "yandex_kubernetes_cluster" "regional_cluster" { folder_id = var.folder_id name = "${var.env}-demo" network_id = module.vpc.id master { regional { region = "ru-central1" dynamic "location" { for_each = module.vpc.subnets content { zone = location.value.zone subnet_id = location.value.id } } } version = var.k8s_version public_ip = true maintenance_policy { auto_upgrade = true } } service_ipv4_range = var.k8s_service_ipv4_range cluster_ipv4_range = var.k8s_pod_ipv4_range release_channel = var.release_channel network_policy_provider = "CALICO" service_account_id = data.terraform_remote_state.sa.outputs.dev_sa["av-dev-sa-cluster"].id node_service_account_id = data.terraform_remote_state.sa.outputs.dev_sa["av-dev-sa-nodes"].id labels = var.labels depends_on = [module.vpc, ] } # ### K8s Node Groups # resource "yandex_kubernetes_node_group" "nodes" { # cluster_id = yandex_kubernetes_cluster.regional_cluster.id # name = "ng-${var.env}" # version = var.k8s_version # instance_template { # platform_id = "standard-v2" # nat = true # resources { # memory = 4 # cores = 2 # } # boot_disk { # type = "network-ssd" # size = 64 # } # scheduling_policy { # preemptible = false # } # } # scale_policy { # fixed_scale { # size = 3 # } # } # allocation_policy { # dynamic "location" { # for_each = module.vpc.subnets # content { # zone = location.value.zone # subnet_id = location.value.id # } # } # } # maintenance_policy { # auto_upgrade = true # auto_repair = true # } # } ================================================ FILE: auth_and_access/iam/examples/webinar_example/dev/variables.tf ================================================ variable "network_name" { description = "Name to be used on all the resources as identifier" type = string } variable "network_description" { description = "An optional description of this resource. Provide this property when you create the resource." type = string default = "terraform-created" } variable "env" { default = "demo" description = "Prefix of different environments where the resources will be created" } variable "folder_id" { type = string description = "Folder-ID where the resources will be created" } variable "subnets" { description = "An optional description of this resource. Provide this property when you create the resource." type = list(object({ zone = string v4_cidr_blocks = string })) default = [ { zone = "ru-central1-a" v4_cidr_blocks = "10.110.0.0/16" }, { zone = "ru-central1-b" v4_cidr_blocks = "10.120.0.0/16" }, { zone = "ru-central1-c" v4_cidr_blocks = "10.130.0.0/16" } ] } variable "labels" { description = "A set of key/value label pairs to assign." type = map(string) default = null } variable "k8s_version" { type = string default = "1.17" description = "Version for Kubernetes Cluster" } variable "release_channel" { type = string default = "REGULAR" description = "Release channel for Kubernetes Cluster" } variable "k8s_service_ipv4_range" { type = string default = "10.150.0.0/16" description = "CIDR for k8s services" } variable "k8s_pod_ipv4_range" { type = string default = "10.140.0.0/16" description = "CIDR for pods in k8s cluster" } ================================================ FILE: auth_and_access/iam/examples/webinar_example/dev/versions.tf ================================================ terraform { required_version = ">= 0.14" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.5" } } } ================================================ FILE: auth_and_access/iam/examples/webinar_example/iam_mgmt/main.tf ================================================ ### IAM dev folder - change folder_id for your own module "iam_dev_folder" { source = "../modules/iam" folder_binding_authoritative = true##!!! folder_id = "XXXXXXXXXXXXXXXXXXXX" folder_user_role_mapping = [ { name = "network-admin-infra" users = ["serviceAccount:ajek2i5oh2u0goj7siad", ] ## Pre-created SA network-admin used as IAM USER roles = ["viewer", "vpc.admin"] }, { name = "developer" users = ["serviceAccount:aje01koskf49t6qkdvm4", ] ## Pre-created SA av-developer-iam-prod used as IAM USER from other folder roles = ["compute.admin", "iam.serviceAccounts.user", "mdb.admin", "k8s.admin", "container-registry.admin", "kms.admin", "vpc.user", "viewer"] }, ] sa_role_mapping = [ { name = "av-dev-sa-cluster" roles = ["editor"] }, { name = "av-dev-sa-nodes" roles = ["container-registry.images.puller"] }, { name = "av-dev-sa-storage" roles = ["storage.editor", "kms.keys.encrypterDecrypter"] }, ] } ### IAM Prod folder - change folder_id for your own module "iam_prod_folder" { source = "../modules/iam" folder_binding_authoritative = true folder_id = "XXXXXXXXXXXXXXXXXXXX" folder_user_role_mapping = [ { name = "network-admin-infra" users = ["serviceAccount:ajek2i5oh2u0goj7siad", ] ## Pre-created SA network-admin used as IAM USER roles = ["viewer", "vpc.admin"] }, { name = "developer" users = ["serviceAccount:ajebr23qsqedf8rpgjk5", ] ## Pre-created SA av-developer-iam used as IAM USER from other folder roles = ["compute.admin", "iam.serviceAccounts.user", "mdb.admin", "k8s.admin", "container-registry.admin", "kms.admin", "vpc.user", "viewer"] }, ] sa_role_mapping = [ { name = "av-prod-sa-cluster" roles = ["editor"] }, { name = "av-prod-sa-nodes" roles = ["container-registry.images.puller"] }, { name = "av-prod-sa-storage" roles = ["storage.editor", "kms.keys.encrypterDecrypter"] }, ] } ### IAM infra folder - change folder_id for your own module "iam_infra_folder" { source = "../modules/iam" folder_binding_authoritative = true folder_id = "XXXXXXXXXXXXXXXXXXXX" folder_user_role_mapping = [ { name = "network-admin-infra" users = ["serviceAccount:ajek2i5oh2u0goj7siad", ] ## Pre-created SA network-admin used as IAM USER roles = ["viewer", "vpc.admin", "compute.admin", "load-balancer.admin",] }, ] sa_role_mapping = [ { name = "infra-sa-cluster" roles = ["editor"] }, { name = "infra-sa-nodes" roles = ["container-registry.images.puller"] }, { name = "infra-sa-noroles" roles = [] }, ] } ================================================ FILE: auth_and_access/iam/examples/webinar_example/iam_mgmt/outputs.tf ================================================ output "dev_sa" { value = module.iam_dev_folder.sa } output "prod_sa" { value = module.iam_prod_folder.sa } ================================================ FILE: auth_and_access/iam/examples/webinar_example/iam_mgmt/variables.tf ================================================ ================================================ FILE: auth_and_access/iam/examples/webinar_example/iam_mgmt/versions.tf ================================================ terraform { required_version = ">= 0.14" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.5" } } } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/.gitignore ================================================ .terraform terraform.tfstate *.tfstate* terraform.tfvars .terraform.lock.hcl ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/.pre-commit-config.yaml ================================================ repos: - repo: git://github.com/antonbabenko/pre-commit-terraform rev: v1.44.0 hooks: - id: terraform_fmt - id: terraform_validate - id: terraform_docs - id: terraform_tflint args: - "--args=--only=terraform_deprecated_interpolation" - "--args=--only=terraform_deprecated_index" - "--args=--only=terraform_unused_declarations" - "--args=--only=terraform_comment_syntax" - "--args=--only=terraform_documented_outputs" - "--args=--only=terraform_documented_variables" - "--args=--only=terraform_typed_variables" - "--args=--only=terraform_module_pinned_source" - "--args=--only=terraform_naming_convention" - "--args=--only=terraform_required_version" - "--args=--only=terraform_required_providers" - "--args=--only=terraform_standard_module_structure" - "--args=--only=terraform_workspace_remote" ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/README.md ================================================ # Identity and Access Management (IAM) Terraform module for Yandex.Cloud ## Features * Create Service accounts and assign them roles in your folder. * Assign roles to IAM users in cloud and/or folder. * You can control **authoritatively** all permissions for cloud and/or folder in **one** terraform manifest if needed. See Authoritative flags. * Replaces IAM groups (aka JOB TITLE) while they are in development. ## Troubleshooting Remember that service accounts in cloud **must** have unique names You can use following `yc cli` commands for diagnostic: ``` yc resource-manager folder list-operations --id XXXXXXXXXXXXXX yc resource-manager folder list-access-bindings --id XXXXXXXXXXXXXX ``` ## Requirements | Name | Version | |------|---------| | terraform | >= 0.14 | | yandex | ~> 0.5 | ## Providers | Name | Version | |------|---------| | yandex | ~> 0.5 | ## Inputs | Name | Description | Type | Default | Required | |------|-------------|------|---------|:--------:| | cloud\_binding\_authoritative | "Authoritative. Sets the IAM policy for the CLOUD and replaces any **existing** policy already attached.
If Authoritative = true : take roles from all objects in variable "cloud\_user\_role\_mapping" and make **unique** role as a new key of map with members" | `bool` | `false` | no | | cloud\_id | Cloud-ID where where need to add permissions. Mandatory variable for CLOUD, if omited default CLOUD\_ID will be used | `string` | `null` | no | | cloud\_user\_role\_mapping | Group of IAM User-IDs and it's permissions in CLOUD, where name = JOB Tille
### Example
#cloud\_user\_role\_mapping = [
{
name = "devops"
users = ["userAccount:idxxxxxx1", "federatedUser:idxxxxxx2"]
roles = ["editor", ]
},
{
name = "developers"
users = ["userAccount:idxxxxxx3"]
roles = ["viewer","k8s.editor",]
},
] | `any` | `[]` | no | | folder\_binding\_authoritative | Authoritative. Sets the IAM policy for the FOLDER and replaces any **existing** policy already attached. | `bool` | `false` | no | | folder\_id | Folder-ID where need to add permissions. Mandatory variable for FOLDER, if omited default FOLDER\_ID will be used | `string` | `null` | no | | folder\_user\_role\_mapping | Group of IAM User-IDs and it's permissions in FOLDER, where name = JOB Tille
### Example
#folder\_user\_role\_mapping = [
{
name = "devops"
users = ["userAccount:idxxxxxx1", "federatedUser:idxxxxxx2"]
roles = ["iam.serviceAccounts.user", "k8s.editor", "k8s.cluster-api.cluster-admin", "container-registry.admin"]
},
{
name = "developers"
users = ["userAccount:idxxxxxx3"]
roles = ["k8s.viewer",]
},
] | `any` | `[]` | no | | sa\_role\_mapping | List of SA and it's permissions
### Example
sa\_role\_mapping = [
{
name = "sa-cluster"
roles = ["editor",]
},
{
name = "sa-nodes"
roles = ["container-registry.images.puller",]
},
] | `any` | `[]` | no | ## Outputs | Name | Description | |------|-------------| | ids | List IDs of created service accounts | | names | List Names of created service accounts | | sa | Map with service accounts info , key = service account name | ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/examples/dev_folder/main.tf ================================================ ### IAM module "iam" { source = "../.." folder_id = "b1g5egku47oq4l7trmmf" folder_binding_authoritative = true sa_role_mapping = [ { name = "sa-cluster" roles = ["editor"] }, { name = "sa-noroles" roles = [] }, { name = "sa-nodes" roles = ["container-registry.images.puller"] }, ] ### Edit with real IAM users ID # folder_user_role_mapping = [ # { # name = "devops" # users = ["serviceAccount:aje0k467i3bs3tst9d97", ] # roles = ["iam.serviceAccounts.user", "k8s.admin", "k8s.cluster-api.cluster-admin", "container-registry.admin"] # }, # { # name = "secops" # users = ["serviceAccount:ajeg2qiqkhnkq3vms1eg", ] # roles = [] # }, # { # name = "developers" # users = ["serviceAccount:ajevak8egbjo8v9ddl85", ] # roles = ["k8s.viewer", "k8s.cluster-api.editor"] # }, # ] } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/examples/dev_folder/outputs.tf ================================================ output "sa_map" { value = module.iam.sa description = "SA Map" } output "sa_names" { value = module.iam.names description = "List of SA names" } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/examples/dev_folder/variables.tf ================================================ ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/examples/dev_folder/versions.tf ================================================ terraform { required_version = ">= 0.14" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.5" } } } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/main.tf ================================================ ### IAM ### Datasource data "yandex_client_config" "client" {} locals { folder_id = var.folder_user_role_mapping == [] && var.sa_role_mapping == [] ? data.yandex_client_config.client.folder_id : var.folder_id cloud_id = var.cloud_id == null ? data.yandex_client_config.client.cloud_id : var.cloud_id } ### SA resource "yandex_iam_service_account" "sa" { for_each = { for v in var.sa_role_mapping : v.name => v } name = each.key folder_id = local.folder_id } locals { folder_user_mappings = chunklist(flatten([for v in var.folder_user_role_mapping : setproduct(v.users, v.roles)]), 2) sa_role_mapping = { for v in var.sa_role_mapping : v.name => v } sa_mappings = chunklist(flatten([for k, v in yandex_iam_service_account.sa : setproduct([v.id], local.sa_role_mapping[v.name].roles)]), 2) } ###Folder Permissions #### Authoritative data "yandex_iam_policy" "bindings" { dynamic "binding" { for_each = [for v in local.folder_user_mappings : { member = v[0], role = v[1] }] content { role = binding.value.role members = [binding.value.member, ] } } dynamic "binding" { for_each = [for v in local.sa_mappings : { member = v[0], role = v[1] }] content { role = binding.value.role members = ["serviceAccount:${binding.value.member}", ] } } } resource "yandex_resourcemanager_folder_iam_policy" "folder_bindings_policy" { count = var.folder_binding_authoritative == false ? 0 : 1 folder_id = local.folder_id policy_data = data.yandex_iam_policy.bindings.policy_data } ####Permissions NON-Authoritative resource "yandex_resourcemanager_folder_iam_member" "folder_sa_member" { count = var.folder_binding_authoritative == false ? length(local.sa_mappings) : 0 folder_id = local.folder_id member = "serviceAccount:${element(local.sa_mappings, count.index)[0]}" role = element(local.sa_mappings, count.index)[1] } resource "yandex_resourcemanager_folder_iam_member" "folder_user_member" { count = var.folder_binding_authoritative == false ? length(local.folder_user_mappings) : 0 folder_id = local.folder_id member = element(local.folder_user_mappings, count.index)[0] role = element(local.folder_user_mappings, count.index)[1] } ### Cloud Permissions locals { cloud_user_mappings = chunklist(flatten([for v in var.cloud_user_role_mapping : setproduct(v.users, v.roles)]), 2) } #### Authoritative resource "yandex_resourcemanager_cloud_iam_binding" "cloud_binding" { for_each = { for v in local.cloud_user_mappings : v[1] => v[0]... if var.cloud_binding_authoritative == true } cloud_id = local.cloud_id members = each.value role = each.key } #### NON-Authoritative resource "yandex_resourcemanager_cloud_iam_member" "cloud_member" { count = var.cloud_binding_authoritative == false ? length(local.cloud_user_mappings) : 0 cloud_id = local.cloud_id member = element(local.cloud_user_mappings, count.index)[0] role = element(local.cloud_user_mappings, count.index)[1] } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/outputs.tf ================================================ output "ids" { description = "List IDs of created service accounts" value = [for v in yandex_iam_service_account.sa : v.id] } output "names" { description = "List Names of created service accounts" value = [for v in yandex_iam_service_account.sa : v.name] } output "sa" { description = "Map with service accounts info , key = service account name" value = { for v in yandex_iam_service_account.sa : v.name => v } } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/iam/variables.tf ================================================ variable "folder_id" { default = null type = string description = "Folder-ID where need to add permissions. Mandatory variable for FOLDER, if omited default FOLDER_ID will be used" } variable "folder_binding_authoritative" { type = bool default = false description = "Authoritative. Sets the IAM policy for the FOLDER and replaces any **existing** policy already attached." } variable "folder_user_role_mapping" { default = [] type = any description = <
list(object({
zone = string
v4_cidr_blocks = string
})) | [| no | ## Outputs | Name | Description | |------|-------------| | id | ID of created network for internal communications | | subnets | List of maps of subnets used in vpc network: key = v4\_cidr\_block | | v4\_cidr\_blocks | List of v4\_cidr\_blocks used in vpc network | | zones | List of zones used in vpc network | ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/networking/main.tf ================================================ ### Datasource data "yandex_client_config" "client" {} ### Locals locals { folder_id = var.folder_id == null ? data.yandex_client_config.client.folder_id : var.folder_id } resource "yandex_vpc_network" "this" { description = var.network_description name = var.network_name labels = var.labels folder_id = local.folder_id } resource "yandex_vpc_subnet" "this" { for_each = { for v in var.subnets : v.v4_cidr_blocks => v } name = "${var.network_name}-${each.value.zone}:${each.value.v4_cidr_blocks}" description = "${var.network_name} subnet for zone ${each.value.zone}" v4_cidr_blocks = [each.value.v4_cidr_blocks] zone = each.value.zone network_id = yandex_vpc_network.this.id folder_id = local.folder_id labels = var.labels } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/networking/outputs.tf ================================================ output "id" { description = "ID of created network for internal communications" value = yandex_vpc_network.this.id } output "zones" { description = "List of zones used in vpc network" value = distinct([for subnet in yandex_vpc_subnet.this : subnet.zone]) } output "v4_cidr_blocks" { description = "List of v4_cidr_blocks used in vpc network" value = flatten([for subnet in yandex_vpc_subnet.this : subnet.v4_cidr_blocks]) } output "subnets" { description = "List of maps of subnets used in vpc network: key = v4_cidr_block" value = { for v in yandex_vpc_subnet.this : v.v4_cidr_blocks[0] => map( "id", v.id, "name", v.name, "zone", v.zone ) } } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/networking/variables.tf ================================================ variable "network_name" { description = "Name to be used on all the resources as identifier" type = string } variable "network_description" { description = "An optional description of this resource. Provide this property when you create the resource." type = string default = "terraform-created" } variable "folder_id" { type = string default = null description = "Folder-ID where the resources will be created" } variable "subnets" { description = "Describe your subnets preferences" type = list(object({ zone = string v4_cidr_blocks = string })) default = [ { zone = "ru-central1-a" v4_cidr_blocks = "10.110.0.0/16" }, { zone = "ru-central1-b" v4_cidr_blocks = "10.120.0.0/16" }, { zone = "ru-central1-c" v4_cidr_blocks = "10.130.0.0/16" } ] } variable "labels" { description = "A set of key/value label pairs to assign." type = map(string) default = null } ================================================ FILE: auth_and_access/iam/examples/webinar_example/modules/networking/versions.tf ================================================ terraform { required_version = ">= 0.14" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.5" } } } ================================================ FILE: auth_and_access/iam/examples/webinar_example/prod/main.tf ================================================ ### Datasource data "terraform_remote_state" "sa" { backend = "local" config = { path = "../iam_mgmt/terraform.tfstate" } } ### Networking module "vpc" { source = "../modules/networking" labels = var.labels network_description = var.network_description network_name = "${var.env}-${var.network_name}" folder_id = var.folder_id subnets = var.subnets } ### Container Registry resource "yandex_container_registry" "registry" { folder_id = var.folder_id name = "${var.env}-registry" } ### Kubernetes cluster resource "yandex_kubernetes_cluster" "regional_cluster" { folder_id = var.folder_id name = "${var.env}-demo" network_id = module.vpc.id master { regional { region = "ru-central1" dynamic "location" { for_each = module.vpc.subnets content { zone = location.value.zone subnet_id = location.value.id } } } version = var.k8s_version public_ip = true maintenance_policy { auto_upgrade = true } } service_ipv4_range = var.k8s_service_ipv4_range cluster_ipv4_range = var.k8s_pod_ipv4_range release_channel = var.release_channel network_policy_provider = "CALICO" service_account_id = data.terraform_remote_state.sa.outputs.prod_sa["av-prod-sa-cluster"].id node_service_account_id = data.terraform_remote_state.sa.outputs.prod_sa["av-prod-sa-nodes"].id labels = var.labels depends_on = [module.vpc, ] } # ### K8s Node Groups # resource "yandex_kubernetes_node_group" "nodes" { # cluster_id = yandex_kubernetes_cluster.regional_cluster.id # name = "ng-${var.env}" # version = var.k8s_version # instance_template { # platform_id = "standard-v2" # nat = true # resources { # memory = 4 # cores = 2 # } # boot_disk { # type = "network-ssd" # size = 64 # } # scheduling_policy { # preemptible = false # } # } # scale_policy { # fixed_scale { # size = 3 # } # } # allocation_policy { # dynamic "location" { # for_each = module.vpc.subnets # content { # zone = location.value.zone # subnet_id = location.value.id # } # } # } # maintenance_policy { # auto_upgrade = true # auto_repair = true # } # } ================================================ FILE: auth_and_access/iam/examples/webinar_example/prod/variables.tf ================================================ variable "network_name" { description = "Name to be used on all the resources as identifier" type = string } variable "network_description" { description = "An optional description of this resource. Provide this property when you create the resource." type = string default = "terraform-created" } variable "env" { default = "demo" description = "Prefix of different environments where the resources will be created" } variable "folder_id" { type = string description = "Folder-ID where the resources will be created" } variable "subnets" { description = "An optional description of this resource. Provide this property when you create the resource." type = list(object({ zone = string v4_cidr_blocks = string })) default = [ { zone = "ru-central1-a" v4_cidr_blocks = "10.110.0.0/16" }, { zone = "ru-central1-b" v4_cidr_blocks = "10.120.0.0/16" }, { zone = "ru-central1-c" v4_cidr_blocks = "10.130.0.0/16" } ] } variable "labels" { description = "A set of key/value label pairs to assign." type = map(string) default = null } variable "k8s_version" { type = string default = "1.17" description = "Version for Kubernetes Cluster" } variable "release_channel" { type = string default = "REGULAR" description = "Release channel for Kubernetes Cluster" } variable "k8s_service_ipv4_range" { type = string default = "10.150.0.0/16" description = "CIDR for k8s services" } variable "k8s_pod_ipv4_range" { type = string default = "10.140.0.0/16" description = "CIDR for pods in k8s cluster" } ================================================ FILE: auth_and_access/iam/examples/webinar_example/prod/versions.tf ================================================ terraform { required_version = ">= 0.14" required_providers { yandex = { source = "yandex-cloud/yandex" version = "~> 0.5" } } } ================================================ FILE: auth_and_access/iam/main.tf ================================================ ### Datasource data "yandex_client_config" "client" {} locals { folder_id = var.folder_id == null ? data.yandex_client_config.client.folder_id : var.folder_id cloud_id = var.cloud_id == null ? data.yandex_client_config.client.cloud_id : var.cloud_id #org_id = var.org_id == null ? data.yandex_client_config.client.organization_id : var.org_id org_id = var.org_id } ### SA resource "yandex_iam_service_account" "sa" { for_each = { for v in var.sa_role_mapping : v.name => v } name = each.key folder_id = local.folder_id } ###Folder Permissions data "yandex_organizationmanager_saml_federation_user_account" "folder_account" { for_each = toset(flatten([for v in var.folder_user_role_mapping : v.fed_users_names if var.federation_id != null && var.usernames_to_ids == true])) federation_id = var.federation_id name_id = each.key } data "yandex_iam_user" "folder_account" { for_each = toset(flatten([for v in var.folder_user_role_mapping : v.iam_users_names if var.usernames_to_ids == true])) login = each.key } locals { sa_role_mapping = { for v in var.sa_role_mapping : v.name => v } sa_mappings = chunklist(flatten([for k, v in yandex_iam_service_account.sa : setproduct([v.id], local.sa_role_mapping[v.name].roles)]), 2) folder_fed_users_names = { for b in var.folder_user_role_mapping : b.job_title_name => flatten([for key, value in data.yandex_organizationmanager_saml_federation_user_account.folder_account : "federatedUser:${value.id}" if contains(b.fed_users_names, value.name_id)]) } folder_iam_users_names = { for b in var.folder_user_role_mapping : b.job_title_name => flatten([for key, value in data.yandex_iam_user.folder_account : "userAccount:${value.id}" if contains(b.iam_users_names, value.login)]) } folder_users_with_ids = { for b in var.folder_user_role_mapping : b.job_title_name => b.users_with_ids } folder_fed_user_mappings = flatten([for v in var.folder_user_role_mapping : setproduct(local.folder_fed_users_names[v.job_title_name], v.roles)]) folder_iam_user_mappings = flatten([for v in var.folder_user_role_mapping : setproduct(local.folder_iam_users_names[v.job_title_name], v.roles)]) folder_id_user_mappings = flatten([for v in var.folder_user_role_mapping : setproduct(local.folder_users_with_ids[v.job_title_name], v.roles)]) folder_user_mappings = distinct(chunklist(concat(local.folder_fed_user_mappings, local.folder_iam_user_mappings, local.folder_id_user_mappings), 2)) } #### Authoritative data "yandex_iam_policy" "bindings" { count = var.folder_binding_authoritative == false ? 0 : 1 dynamic "binding" { for_each = [for v in local.folder_user_mappings : { member = v[0], role = v[1] }] content { role = binding.value.role members = [binding.value.member, ] } } dynamic "binding" { for_each = [for v in local.sa_mappings : { member = v[0], role = v[1] }] content { role = binding.value.role members = ["serviceAccount:${binding.value.member}", ] } } } resource "yandex_resourcemanager_folder_iam_policy" "folder_bindings_policy" { count = var.folder_binding_authoritative == false ? 0 : 1 folder_id = local.folder_id policy_data = data.yandex_iam_policy.bindings[0].policy_data } #### NON-Authoritative resource "yandex_resourcemanager_folder_iam_member" "folder_sa_member" { count = var.folder_binding_authoritative == false ? length(local.sa_mappings) : 0 folder_id = local.folder_id member = "serviceAccount:${element(local.sa_mappings, count.index)[0]}" role = element(local.sa_mappings, count.index)[1] } resource "yandex_resourcemanager_folder_iam_member" "folder_user_member" { count = var.folder_binding_authoritative == false ? length(local.folder_user_mappings) : 0 folder_id = local.folder_id member = element(local.folder_user_mappings, count.index)[0] role = element(local.folder_user_mappings, count.index)[1] } ### Cloud Permissions data "yandex_organizationmanager_saml_federation_user_account" "cloud_account" { for_each = toset(flatten([for v in var.cloud_user_role_mapping : v.fed_users_names if var.federation_id != null && var.usernames_to_ids == true])) federation_id = var.federation_id name_id = each.key } data "yandex_iam_user" "cloud_account" { for_each = toset(flatten([for v in var.cloud_user_role_mapping : v.iam_users_names if var.usernames_to_ids == true])) login = each.key } locals { cloud_fed_users_names = { for b in var.cloud_user_role_mapping : b.job_title_name => flatten([for key, value in data.yandex_organizationmanager_saml_federation_user_account.cloud_account : "federatedUser:${value.id}" if contains(b.fed_users_names, value.name_id)]) } cloud_iam_users_names = { for b in var.cloud_user_role_mapping : b.job_title_name => flatten([for key, value in data.yandex_iam_user.cloud_account : "userAccount:${value.id}" if contains(b.iam_users_names, value.login)]) } cloud_users_with_ids = { for b in var.cloud_user_role_mapping : b.job_title_name => b.users_with_ids } cloud_fed_user_mappings = flatten([for v in var.cloud_user_role_mapping : setproduct(local.cloud_fed_users_names[v.job_title_name], v.roles)]) cloud_iam_user_mappings = flatten([for v in var.cloud_user_role_mapping : setproduct(local.cloud_iam_users_names[v.job_title_name], v.roles)]) cloud_id_user_mappings = flatten([for v in var.cloud_user_role_mapping : setproduct(local.cloud_users_with_ids[v.job_title_name], v.roles)]) cloud_user_mappings = distinct(chunklist(concat(local.cloud_fed_user_mappings, local.cloud_iam_user_mappings, local.cloud_id_user_mappings), 2)) } #### Authoritative resource "yandex_resourcemanager_cloud_iam_binding" "cloud_binding" { for_each = { for v in local.cloud_user_mappings : v[1] => v[0]... if var.cloud_binding_authoritative == true } cloud_id = local.cloud_id members = each.value role = each.key } #### NON-Authoritative resource "yandex_resourcemanager_cloud_iam_member" "cloud_member" { count = var.cloud_binding_authoritative == false ? length(local.cloud_user_mappings) : 0 cloud_id = local.cloud_id member = element(local.cloud_user_mappings, count.index)[0] role = element(local.cloud_user_mappings, count.index)[1] } ### Organization Permissions data "yandex_organizationmanager_saml_federation_user_account" "org_account" { for_each = toset(flatten([for v in var.org_user_role_mapping : v.fed_users_names if var.federation_id != null && var.usernames_to_ids == true])) federation_id = var.federation_id name_id = each.key } data "yandex_iam_user" "org_account" { for_each = toset(flatten([for v in var.org_user_role_mapping : v.iam_users_names if var.usernames_to_ids == true])) login = each.key } locals { ##### {job=[ids]} org_fed_users_names = { for b in var.org_user_role_mapping : b.job_title_name => flatten([for key, value in data.yandex_organizationmanager_saml_federation_user_account.org_account : "federatedUser:${value.id}" if contains(b.fed_users_names, value.name_id)]) } org_iam_users_names = { for b in var.org_user_role_mapping : b.job_title_name => flatten([for key, value in data.yandex_iam_user.org_account : "userAccount:${value.id}" if contains(b.iam_users_names, value.login)]) } org_users_with_ids = { for b in var.org_user_role_mapping : b.job_title_name => b.users_with_ids } #####[id-role pairs] per type org_fed_user_mappings = flatten([for v in var.org_user_role_mapping : setproduct(local.org_fed_users_names[v.job_title_name], v.roles)]) org_iam_user_mappings = flatten([for v in var.org_user_role_mapping : setproduct(local.org_iam_users_names[v.job_title_name], v.roles)]) org_id_user_mappings = flatten([for v in var.org_user_role_mapping : setproduct(local.org_users_with_ids[v.job_title_name], v.roles)]) #####list[pairs] org_user_mappings = distinct(chunklist(concat(local.org_fed_user_mappings, local.org_iam_user_mappings, local.org_id_user_mappings), 2)) } #### Authoritative resource "yandex_organizationmanager_organization_iam_binding" "org_binding" { for_each = { for v in local.org_user_mappings : v[1] => v[0]... if var.org_binding_authoritative == true } organization_id = local.org_id members = each.value role = each.key } #### NON-Authoritative resource "yandex_organizationmanager_organization_iam_member" "org_member" { count = var.org_binding_authoritative == false ? length(local.org_user_mappings) : 0 organization_id = local.org_id member = element(local.org_user_mappings, count.index)[0] role = element(local.org_user_mappings, count.index)[1] } ================================================ FILE: auth_and_access/iam/outputs.tf ================================================ output "sa_ids" { description = "List IDs of created service accounts" value = [for v in yandex_iam_service_account.sa : v.id] } output "sa_names" { description = "List Names of created service accounts" value = [for v in yandex_iam_service_account.sa : v.name] } output "sa_object" { description = "Map with service accounts info , key = service account name" value = { for v in yandex_iam_service_account.sa : v.name => v } } ================================================ FILE: auth_and_access/iam/variables.tf ================================================ ### Name convertion variable "usernames_to_ids" { description = "If true Usernames from IAM and Federation will be used as input variables 'iam_users_names' and 'fed_users_names'" type = bool default = true } variable "federation_id" { description = "Federation ID, mandatory for 'fed_users_names'" type = string default = null } ###Folder variable "folder_id" { default = null type = string description = "Folder-ID where need to add permissions. Mandatory variable for FOLDER, if omited default FOLDER_ID will be used" } variable "folder_binding_authoritative" { type = bool default = false description = "Authoritative. Sets the IAM policy for the FOLDER and replaces any **existing** policy already attached." } variable "folder_user_role_mapping" { default = [] type = any description = <
{
"v4_cidr_blocks": "10.110.0.0/16",
"zone": "ru-central1-a"
},
{
"v4_cidr_blocks": "10.120.0.0/16",
"zone": "ru-central1-b"
},
{
"v4_cidr_blocks": "10.130.0.0/16",
"zone": "ru-central1-c"
}
]
 В данном решение `IdP` развёртывается в виде виртуальной машины с [Keycloak](https://keycloak.org).
Данное решение реализовано в виде двух Terraform модулей:
* [keycloak-deploy](#kc-deploy)
* [keycloak-config](#kc-config)
Разбиение решения на два модуля вызвано тем, что [Keycloak Terraform провайдер](https://registry.tfpla.net/providers/mrparkers/keycloak/latest/docs) требует уже работающего (alive) Keycloak.
### Модуль keycloak-deploy
Модуль `keycloak-deploy` создаёт следующие объекты в Yandex Cloud:
* кластер [Managed Service for PostgreSQL](https://cloud.yandex.ru/docs/managed-postgresql/) - для хранения конфигурации Keycloak
* сертификат [Let's Encrypt](https://letsencrypt.org/) для веб-сервера Keycloak
* статический [публичный IP-адрес](https://cloud.yandex.ru/docs/vpc/concepts/address#public-addresses) для ВМ Keycloak
* [группу безопасности](https://cloud.yandex.ru/docs/vpc/concepts/security-groups) для ВМ Keycloak
* ВМ с решением Keycloak
С полным списком входных параметров модуля можно ознакомиться [по ссылке](./keycloak-deploy/variables.tf).
После завершения своей работы модуль возвращает значение `FQDN` для ВМ с развёрнутым решением Keycloak, например, `kc1.mydom.net`
### Модуль keycloak-config
Модуль `keycloak-config` выполняет следующие действия:
* создаёт [федерацию удостоверений](https://cloud.yandex.ru/docs/organization/add-federation) в Yandex Cloud
* создаёт Realm и сопутствующие объекты в конфигурации Keycloak
* обеспечивает обмен сертификатами между федерацией Yandex Cloud и Keycloak Realm
* создаёт учётную запись для тестового пользователя в Keycloak
* импортирует учётную запись тестового пользователя из Keycloak в организацию Yandex Cloud
С полным списком входных параметров модуля можно ознакомиться [по ссылке](./keycloak-config/variables.tf).
После завершения своей работы модуль возвращает значение `URL` федерации удостоверений, например, `https://console.yandex.ru/federations/bpf3375ucdgp5dxq823tt`
### Синхронизация данных между TF модулями
Модуль `keycloak-config` использует часть входных и выходных данных модуля `keycloak-deploy`.
Развёртывание решения требует последовательного запуска сначала модуля `keycloak-deploy`, а затем модуля `keycloak-config`.
Для исключения ошибок при ручном переносе данных из одного модуля в другой рекомендуется использовать скрипт [sync.sh](./examples/keycloak-config/sync.sh), который синхронизирует нужные данные из модуля `keycloak-deploy` в модуль `keycloak-config`.
## Внешние зависимости
Решение должно развёртываться в уже подготовленной инфраструктуре Yandex Cloud.
Значения параметров инфраструктуры должны передаваться в `TF модули` решения в виде входных переменных.
Перед развёртывание решения в Yandex Cloud уже должны существовать следующие объекты:
* каталог облачных ресурсов (folder) в котором будут развёртываться компоненты решения (`kc_folder_name`)
* [публичная зона](https://cloud.yandex.ru/docs/dns/concepts/dns-zone#public-zones) в сервисе [Cloud DNS](https://cloud.yandex.ru/docs/dns/). Домен, который будет создаваться в сервисе Cloud DNS должен быть предварительно `делегирован` со стороны регистратора домена (`dns_zone_name`)
* сеть (network) в которой будут развёртываться компоненты решения (`kc_network_name`)
* подсеть (subnet) в которой будут развёртываться компоненты решения (`kc_subnet_name`)
В списке выше в круглых скобках указаны имена входных переменных для развёртывания из [keycloak-deploy](./examples/keycloak-deploy/main.tf).
## Порядок развёртывания решения
Развёртывание решения предполагается под управлением ОС `Linux` или `MacOS`.
Развёртывание решения под управлением ОС `Windows` не тестировалось.
1. Загрузить решение из репозитория на [github.com](https://github.com/yandex-cloud/yc-solution-library-for-security):
```bash
curl -s https://raw.githubusercontent.com/yandex-cloud/yc-solution-library-for-security/master/auth_and_access/keycloak/examples/install.sh | bash
```
2. Перейти в папку с примером развёртывания модуля [keycloak-deploy](./examples/keycloak-deploy/):
```bash
cd keycloak/keycloak-deploy
pwd
```
3. `Важно!` Убедиться что все [внешние зависимости](#ext-dep) созданы.
4. Проверить значения переменных в файле [main.tf](./examples/keycloak-deploy/main.tf) и скорректировать их при необходимости.
5. Выполнить инициализацию Terraform:
```bash
source ../env-yc.sh
terraform init
```
6. Выполнить развёртывание `keycloak-deploy`:
```bash
terraform apply
```
Обработка запроса на выдачу сертификата в сервисе [Let's Encrypt](https://letsencrypt.org/) может выполняться `до 30 минут`!
7. Опционально. Проверить состояние выданного сертификата Let's Encrypt:
```bash
yc cm certificate list
```
8. Перейти в папку с примером развёртывания модуля [keycloak-config](./examples/keycloak-config/):
```bash
cd ../keycloak-config
pwd
```
9. Выполнить синхронизацию параметров между TF модулями:
```bash
bash sync.sh
```
10. Проверить значения переменных в файле [main.tf](./examples/keycloak-config/main.tf) и скорректировать их при необходимости.
11. Выполнить инициализацию Terraform:
```bash
terraform init
```
12. Выполнить развёртывание `keycloak-config`:
```bash
terraform apply
```
13. Опционально. Проверить наличие тестовой учётной записи Keycloak в организации Yandex Cloud с помощью `yc CLI`:
```bash
ORG_ID=$(cat terraform.tfstate | jq -r '.resources[] | select(.type == ('\"yandex_organizationmanager_saml_federation\"')) | .instances[0].attributes.organization_id')
yc organization-manager user list --organization-id=$ORG_ID
```
## Результаты развёртывания
В результате развёртывания решения в Yandex Cloud будут созданы следующие объекты:
* [федерация удостоверений]((https://cloud.yandex.ru/docs/organization/add-federation)) в указанной [организации](https://cloud.yandex.ru/docs/organization/add-federation)
* `сертификат` [Let's Encrypt](https://letsencrypt.org/) для ВМ с Keycloak в сервисе [Certificate Manager](https://cloud.yandex.ru/docs/certificate-manager/)
* `виртуальная машина` с IdP Keycloak интегрированная с федерацией на стороне Yandex Cloud
* `запись в Yandex Cloud DNS` с публичным IP-адресом ВМ Keycloak
* `учётная запись` пользователя в IdP Keycloak и её синхронизация в организации Yandex Cloud
После развёртывания решения останется выдать необходимые [роли](https://cloud.yandex.ru/docs/iam/concepts/access-control/roles) на нужные облачные ресурсы для созданной в организации учётной записи пользователя.
================================================
FILE: auth_and_access/keycloak/examples/README.md
================================================
# Пример развёртывания Keycloak с помощью Terraform модулей
* [keycloak-deploy](../keycloak-deploy/)
* [keycloak-config](../keycloak-config/)
================================================
FILE: auth_and_access/keycloak/examples/env-yc.sh
================================================
#!/bin/bash
export YC_TOKEN=$(yc iam create-token)
export TF_VAR_YC_CLOUD_ID=$(yc config get cloud-id)
================================================
FILE: auth_and_access/keycloak/examples/install.sh
================================================
#!/bin/bash
REPO="https://raw.githubusercontent.com/yandex-cloud/yc-solution-library-for-security/master/auth_and_access/keycloak"
mkdir -p keycloak/keycloak-deploy
mkdir -p keycloak/keycloak-config
FILES="examples/env-yc.sh keycloak/env-yc.sh
examples/keycloak-deploy/main.tf keycloak/keycloak-deploy/main.tf
examples/keycloak-deploy/variables.tf keycloak/keycloak-deploy/variables.tf
examples/keycloak-config/main.tf keycloak/keycloak-config/main.tf
examples/keycloak-config/sync.sh keycloak/keycloak-config/sync.sh"
echo "$FILES" | while read URL FILE;
do
curl -sl "$REPO/$URL" -o "$FILE"
done
================================================
FILE: auth_and_access/keycloak/examples/keycloak-config/main.tf
================================================
# ==================================
# Terraform & Provider Configuration
# ==================================
terraform {
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = "~> 0.84.0"
}
null = {
source = "hashicorp/null"
version = "~> 3.2.1"
}
# https://registry.tfpla.net/providers/mrparkers/keycloak/latest/docs
keycloak = {
source = "mrparkers/keycloak"
version = "~> 4.1.0"
}
}
}
# ===========================
# Call keycloak-config module
# ===========================
module "keycloak-config" {
source = "git::https://github.com/yandex-cloud/yc-solution-library-for-security.git//auth_and_access/keycloak/keycloak-config"
labels = { tag = "keycloak-config" }
# =====================
# Org/Federation values
# =====================
org_id = "bpfqdgu3d2815fyixlks"
fed_name = "kc-fed"
kc_user = {
name = "user1"
pass = "Gu95-paSw38"
domain = "mydom.net"
}
# ==================
# Keycloak VM values
# ==================
kc_realm_name = "kc1"
kc_realm_descr = "My Keycloak Realm"
kc_fqdn = "kc1.mydom.net"
kc_port = "8443"
kc_adm_user = "admin"
kc_adm_pass = "Fr#dR3n48Ga-Mov"
}
================================================
FILE: auth_and_access/keycloak/examples/keycloak-config/sync.sh
================================================
#!/bin/bash
# Sync required input and output values
# from keycloak-deploy to keycloak-config
SRC_PATH="../keycloak-deploy"
SRC_FN=main.tf
DST_FN=main.tf
KC_FQDN=$(terraform -chdir=$SRC_PATH output -raw kc_fqdn)
KC_PORT=$(grep kc_port $SRC_PATH/$SRC_FN | awk -F "\"" '{print $2}')
KC_ADM_USER=$(grep kc_adm_user $SRC_PATH/$SRC_FN | awk -F "\"" '{print $2}')
KC_ADM_PASS=$(grep kc_adm_pass $SRC_PATH/$SRC_FN | awk -F "\"" '{print $2}')
if [[ "$OSTYPE" == "linux-gnu"* ]]; then
sed -i "s/kc_fqdn.*/kc_fqdn = \"$KC_FQDN\"/" $DST_FN
sed -i "s/kc_port.*/kc_port = \"$KC_PORT\"/" $DST_FN
sed -i "s/kc_adm_user.*/kc_adm_user = \"$KC_ADM_USER\"/" $DST_FN
sed -i "s/kc_adm_pass.*/kc_adm_pass = \"$KC_ADM_PASS\"/" $DST_FN
elif [[ "$OSTYPE" == "darwin"* ]]; then
sed -i '' "s/kc_fqdn.*/kc_fqdn = \"$KC_FQDN\"/" $DST_FN
sed -i '' "s/kc_port.*/kc_port = \"$KC_PORT\"/" $DST_FN
sed -i '' "s/kc_adm_user.*/kc_adm_user = \"$KC_ADM_USER\"/" $DST_FN
sed -i '' "s/kc_adm_pass.*/kc_adm_pass = \"$KC_ADM_PASS\"/" $DST_FN
fi
================================================
FILE: auth_and_access/keycloak/examples/keycloak-deploy/main.tf
================================================
# ==================================
# Terraform & Provider Configuration
# ==================================
terraform {
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = "~> 0.84.0"
}
}
}
# ===========================
# Call keycloak-deploy module
# ===========================
module "keycloak-deploy" {
source = "git::https://github.com/yandex-cloud/yc-solution-library-for-security.git//auth_and_access/keycloak/keycloak-deploy"
cloud_id = var.YC_CLOUD_ID
labels = { tag = "keycloak-deploy" }
# ==================
# Keycloak VM values
# ==================
kc_image_folder_id = "standard-images"
kc_image_name = "ubuntu-22-04-lts-v20221226"
kc_folder_name = "infra"
kc_zone_id = "ru-central1-b"
kc_network_name = "infra-net"
kc_subnet_name = "infra-subnet-b"
kc_hostname = "kc1"
kc_vm_sg_name = "kc-sg"
kc_vm_username = "admin"
kc_vm_ssh_key_file = "~/.ssh/id_rsa.pub"
# KC FQDN --> kc1.mydom.net
dns_zone_name = "mydom-net"
kc_ver = "20.0.2"
kc_port = "8443"
kc_adm_user = "admin"
kc_adm_pass = "Fr#dR3n48Ga-Mov"
# =================
# PostgreSQL values
# =================
pg_db_ver = "15"
pg_db_name = "kc1-db"
pg_db_user = "dbadmin"
pg_db_pass = "My82Sup@paS98"
# ===================
# Certificates values
# ===================
kc_cert_path = "/usr/local/etc/certs"
le_cert_name = "kc1"
le_cert_descr = "LE Certificate for Keycloak VM"
le_cert_pub_chain = "cert-pub-chain.pem"
le_cert_priv_key = "cert-priv-key.pem"
}
output "kc_fqdn" {
value = "${module.keycloak-deploy.kc_fqdn}"
}
================================================
FILE: auth_and_access/keycloak/examples/keycloak-deploy/variables.tf
================================================
variable "YC_CLOUD_ID" {
description = "Cloud ID"
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/README.md
================================================
# Keycloak-config Terraform module
================================================
FILE: auth_and_access/keycloak/keycloak-config/federation.tf
================================================
# ========================================================
# YC Federation resource
# Import Keycloak resources into Federation & Organization
# ========================================================
# Create YC Federation
resource "yandex_organizationmanager_saml_federation" kc_fed {
name = var.fed_name
organization_id = var.org_id
issuer = "https://${var.kc_fqdn}:${var.kc_port}/realms/${var.kc_realm_name}"
sso_url = "https://${var.kc_fqdn}:${var.kc_port}/realms/${var.kc_realm_name}/protocol/saml"
sso_binding = "POST"
auto_create_account_on_login = true
security_settings {
encrypted_assertions = true
}
}
# Add Keycloak certificate to the YC Federation
resource "null_resource" "federation_cert" {
provisioner "local-exec" {
command = <<-CMD
echo -----BEGIN CERTIFICATE-----\\n $(curl -s https://${var.kc_fqdn}:${var.kc_port}/realms/${var.kc_realm_name}/protocol/saml/descriptor | awk '{split($0,lst,"X509Certificate>"); print substr(lst[2],1,length(lst[2])-5)}')\\n-----END CERTIFICATE----- | tee ${abspath(path.cwd)}/${var.kc_realm_name}-cert.pem
yc organization-manager federation saml certificate create \
--name=${var.fed_name} \
--federation-id=${yandex_organizationmanager_saml_federation.kc_fed.id} \
--certificate-file=${abspath(path.cwd)}/${var.kc_realm_name}-cert.pem
CMD
}
depends_on = [
keycloak_realm.realm
]
}
# Import Test user account to YC Organization from Keycloak
data "yandex_organizationmanager_saml_federation_user_account" kc_test_user {
federation_id = "${yandex_organizationmanager_saml_federation.kc_fed.id}"
name_id = var.kc_user.name
depends_on = [
null_resource.federation_cert
]
}
output "federation_url" {
value = "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}"
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/keycloak-config.tf
================================================
# ================================
# Keycloak configuration resources
# ================================
# https://registry.tfpla.net/providers/mrparkers/keycloak/latest/docs
provider "keycloak" {
client_id = "admin-cli"
username = var.kc_adm_user
password = var.kc_adm_pass
url = "https://${var.kc_fqdn}:${var.kc_port}"
}
resource "keycloak_realm" "realm" {
realm = var.kc_realm_name
enabled = true
display_name = var.kc_realm_descr
display_name_html = "${var.kc_realm_descr}"
ssl_required = "external"
registration_allowed = false
registration_email_as_username = false
remember_me = false
verify_email = false
reset_password_allowed = false
login_with_email_allowed = false
internationalization {
supported_locales = [ "en" ]
default_locale = "en"
}
security_defenses {
headers {
x_frame_options = "DENY"
content_security_policy = "frame-src 'self'; frame-ancestors 'self'; object-src 'none';"
content_security_policy_report_only = ""
x_content_type_options = "nosniff"
x_robots_tag = "none"
x_xss_protection = "1; mode=block"
strict_transport_security = "max-age=31536000; includeSubDomains"
}
brute_force_detection {
permanent_lockout = false
max_login_failures = 10
wait_increment_seconds = 60
quick_login_check_milli_seconds = 1000
minimum_quick_login_wait_seconds = 60
max_failure_wait_seconds = 900
failure_reset_time_seconds = 43200
}
}
}
resource "keycloak_saml_client" "client" {
realm_id = keycloak_realm.realm.id
name = "${var.fed_name}-federation"
enabled = true
client_id = "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}"
base_url = "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}"
valid_redirect_uris = [ "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}" ]
idp_initiated_sso_relay_state = "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}"
assertion_consumer_redirect_url = "https://console.cloud.yandex.ru"
sign_documents = true
sign_assertions = true
include_authn_statement = true
name_id_format = "username"
force_name_id_format = false
signature_algorithm = "RSA_SHA256"
signature_key_name = "CERT_SUBJECT"
full_scope_allowed = true
client_signature_required = true
force_post_binding = true
encrypt_assertions = true
signing_certificate = file("${abspath(path.module)}/${var.yc_cert}")
encryption_certificate = file("${abspath(path.module)}/${var.yc_cert}")
}
resource "keycloak_generic_protocol_mapper" "role_list_mapper" {
realm_id = keycloak_realm.realm.id
client_id = keycloak_saml_client.client.id
name = "role list"
protocol = "saml"
protocol_mapper = "saml-role-list-mapper"
config = {
"attribute.name" = "Role"
"attribute.nameformat" = "Basic"
"single" = "true"
}
}
resource "keycloak_saml_user_property_protocol_mapper" "property_email" {
realm_id = keycloak_realm.realm.id
client_id = keycloak_saml_client.client.id
name = "X500 email"
user_property = "email"
friendly_name = "email"
saml_attribute_name = "urn:oid:1.2.840.113549.1.9.1"
saml_attribute_name_format = "URI Reference"
}
resource "keycloak_saml_user_property_protocol_mapper" "property_givenname" {
realm_id = keycloak_realm.realm.id
client_id = keycloak_saml_client.client.id
name = "X500 givenName"
user_property = "firstName"
friendly_name = "givenName"
saml_attribute_name = "urn:oid:2.5.4.42"
saml_attribute_name_format = "URI Reference"
}
resource "keycloak_saml_user_property_protocol_mapper" "property_surname" {
realm_id = keycloak_realm.realm.id
client_id = keycloak_saml_client.client.id
name = "X500 surname"
user_property = "lastName"
friendly_name = "surname"
saml_attribute_name = "urn:oid:2.5.4.4"
saml_attribute_name_format = "URI Reference"
}
# Keycloak test user account
resource "keycloak_user" "test_user" {
realm_id = keycloak_realm.realm.id
username = var.kc_user.name
enabled = true
first_name = var.kc_user.name
last_name = var.kc_user.name
email = "${var.kc_user.name}@${var.kc_user.domain}"
attributes = {}
initial_password {
value = var.kc_user.pass
temporary = false
}
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/providers.tf
================================================
# ==================================
# Terraform & Provider Configuration
# ==================================
terraform {
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = "~> 0.84.0"
}
null = {
source = "hashicorp/null"
version = "~> 3.2.1"
}
# https://registry.tfpla.net/providers/mrparkers/keycloak/latest/docs
keycloak = {
source = "mrparkers/keycloak"
version = "~> 4.1.0"
}
}
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/variables.tf
================================================
# =======================================
# Keycloak-config module. Input variables
# =======================================
variable "labels" {
description = "A set of key/value label pairs to assign."
type = map(string)
default = null
}
# ========================
# Org/Federation variables
# ========================
variable "org_id" {
description = "YC Organization ID"
type = string
default = null
}
variable "fed_name" {
description = "YC Federation name"
type = string
default = null
}
variable "yc_cert" {
description = "Yandex Cloud SSL certificate"
type = string
default = "yc-root.crt"
}
variable "kc_user" {
description = "Keycloak test user account"
type = map(string) # name & password
default = {}
}
# =====================
# Keycloak VM variables
# =====================
variable "kc_fqdn" {
description = "Keycloak public DNS FQDN"
type = string
default = null
}
variable "kc_port" {
description = "Keycloak HTTPS port listener"
type = string
default = null
}
variable "kc_adm_user" {
description = "Keycloak admin user name"
type = string
default = null
}
variable "kc_adm_pass" {
description = "Keycloak admin user password"
type = string
default = null
}
variable "kc_realm_name" {
description = "Keycloak Realm name"
type = string
default = null
}
variable "kc_realm_descr" {
description = "Keycloak Realm description"
type = string
default = null
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/yc-root.crt
================================================
-----BEGIN CERTIFICATE-----
MIIDjzCCAnegAwIBAgIUF3bSIPKEcz0+93czW8h814WWGl8wDQYJKoZIhvcNAQEL
BQAwVzELMAkGA1UEBhMCUlUxDzANBgNVBAgMBk1vc2NvdzEPMA0GA1UECgwGWWFu
ZGV4MRUwEwYDVQQLDAxZYW5kZXguQ2xvdWQxDzANBgNVBAMMBllhbmRleDAeFw0y
MDAyMTIwODI2NTVaFw0yNTAyMTIwODI2NTVaMFcxCzAJBgNVBAYTAlJVMQ8wDQYD
VQQIDAZNb3Njb3cxDzANBgNVBAoMBllhbmRleDEVMBMGA1UECwwMWWFuZGV4LkNs
b3VkMQ8wDQYDVQQDDAZZYW5kZXgwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEK
AoIBAQDYVcxqC0Ienc85C2oD93GvYB172VSPYuy7umjHa/8Xy8KUGmAjO1pJA2Qv
grs0AmymueM6d6Uw0C7MsDY/Z3eOid9ZRnbmJtfx2MzmyA91Y0ZvcIxYXWa4kloE
iLUMGs94ixgBat+erKN836NVF4mFOtLUsueMOkQkdFw6RPlw9NccEmWxb/XfzA2f
ceCjWFeJt1RQSAMPxmsd+s9NmsaZ7dFsn1Vx/ACLdlzxhyCjf7A5FIRZUxEHQF5U
OP7z2bKkErDivFj19XhZ2whHmHNKy2pvrzZ0ufoy2+isW5HzEn1+DO3hwX8pKOOv
jtKi5vqtsdjteGDmF2+lm+RxrkL/AgMBAAGjUzBRMB0GA1UdDgQWBBRVWZqkoCfZ
HnN6vDN6d5l2tQGp7jAfBgNVHSMEGDAWgBRVWZqkoCfZHnN6vDN6d5l2tQGp7jAP
BgNVHRMBAf8EBTADAQH/MA0GCSqGSIb3DQEBCwUAA4IBAQA4/gJ1/dawiBYa4hYp
CFsnWIgoJ9iLgG6mOZ6q0xT8X/zAPkA9EeB75OdFPFruAydRlihdiVfrjbdOYoEg
rTbF1jtWAAK+YQpLohrLp070h5PzXMMvso8Tkg4phxLEGhtsHg+SMFipvg0uTG1C
WttgnHy8tWfrjbrF2MPA846ibHu7nPjhwoQxdd5kILPYLTANc3YzwaiN96f6flZg
edkVDUHMT2AVMpFvbYb1jNqULQ9Xyl5ebdTqLVzJ1WWDN7rUGdv2qDrHOlHeBMU3
2S6djwOizttFSwkj2q0FXAH8UFBTDS63gjSwJVzoSHaeFXo+6iT1b1eKj8sdxcbE
3rA+
-----END CERTIFICATE-----
================================================
FILE: auth_and_access/keycloak/keycloak-deploy/README.md
================================================
# Keycloak-deploy Terraform module
================================================
FILE: auth_and_access/keycloak/keycloak-deploy/dns-cm.tf
================================================
# ===================================
# DNS & Certificate Manager resources
# ===================================
data "yandex_dns_zone" "kc_dns_zone" {
folder_id = "${data.yandex_resourcemanager_folder.kc_folder.id}"
name = var.dns_zone_name
}
locals {
kc_fqdn = "${var.kc_hostname}.${trimsuffix(data.yandex_dns_zone.kc_dns_zone.zone,".")}"
}
# Create DNS record for Keycloak VM with created public ip address
resource "yandex_dns_recordset" "kc_dns_rec" {
zone_id = data.yandex_dns_zone.kc_dns_zone.id
name = var.kc_hostname
type = "A"
ttl = 300
data = ["${yandex_vpc_address.kc_pub_ip.external_ipv4_address[0].address}"]
}
# Create request to the Let's Encrypt service for Keycloak's VM certificate
resource "yandex_cm_certificate" "kc_le_cert" {
folder_id = "${data.yandex_resourcemanager_folder.kc_folder.id}"
name = var.le_cert_name
domains = [ "${local.kc_fqdn}" ]
managed {
challenge_type = "DNS_CNAME"
}
}
# Create domain validation DNS record for Let's Encrypt service
resource "yandex_dns_recordset" "validation_dns_rec" {
zone_id = data.yandex_dns_zone.kc_dns_zone.id
name = yandex_cm_certificate.kc_le_cert.challenges[0].dns_name
type = yandex_cm_certificate.kc_le_cert.challenges[0].dns_type
data = [yandex_cm_certificate.kc_le_cert.challenges[0].dns_value]
ttl = 60
}
output "kc_fqdn" {
value = local.kc_fqdn
}
================================================
FILE: auth_and_access/keycloak/keycloak-deploy/kc-setup.sh
================================================
# ===============================
# Keycloak VM provisioning script
# ===============================
# Get Keycloak input data
source kc-data.sh
# Change Timezone
timedatectl set-timezone Europe/Moscow
# Install Packages
apt-get update > /dev/null
apt-get install -y unzip openjdk-18-jre jq > /dev/null
# Install Yandex Cloud CLI (yc CLI)
YC_PATH="/opt/yc"
mkdir -p ${YC_PATH}
curl -s -O https://storage.yandexcloud.net/yandexcloud-yc/install.sh
chmod u+x install.sh
./install.sh -a -i ${YC_PATH}/ 2>/dev/null
ln -s ${YC_PATH}/bin/yc /usr/bin/yc
rm -f install.sh
sed -i "\$ a source ${YC_PATH}/completion.bash.inc" /etc/profile
# Configuring yc CLI
VM_ID=$(curl -s http://169.254.169.254/latest/meta-data/instance-id)
FOLDER_ID=$(yc compute instance get $VM_ID --format=json | jq -r .folder_id )
CLOUD_ID=$(yc resource folder get $FOLDER_ID --format=json | jq -r .cloud_id)
yc config profile create default
yc config set cloud-id $CLOUD_ID
yc config set folder-id $FOLDER_ID
unset CLOUD_ID FOLDER_ID VM_ID
# Get Keycloak distro and put files to the right place
curl -sLO https://github.com/keycloak/keycloak/releases/download/$KC_VER/keycloak-$KC_VER.zip
unzip -q keycloak-$KC_VER.zip
rm -f keycloak-$KC_VER/bin/*.bat
mkdir -p /opt/keycloak
cp -R keycloak-$KC_VER/* /opt/keycloak
rm -rf keycloak-$KC_VER/ keycloak-$KC_VER.zip
export PATH=$PATH:/opt/keycloak/bin
kc.sh build
# Get Let's Encrypt certificate from the YC Certificate Manager
# Let's Encrypt should validate certificate request within 30 minutes
mkdir -p $KC_CERT_PATH
status=None
while [ $status != 'ISSUED' ]
do
status=$(yc cm certificate get --full --name=$KC_CERT_NAME --format=json | jq -r .status)
echo $(date +'%H:%M:%S') $status
sleep 60
done
yc cm certificate download --name=$KC_CERT_NAME --chain=$KC_CERT_PATH/$KC_CERT_PUB --key=$KC_CERT_PATH/$KC_CERT_PRIV > /dev/null
# Prepare systemd things
groupadd keycloak
useradd -r -g keycloak -d /opt/keycloak -s /sbin/nologin keycloak
chown -R keycloak:keycloak /opt/keycloak
chmod o+x /opt/keycloak/bin/
cat <
В данном решение `IdP` развёртывается в виде виртуальной машины с [Keycloak](https://keycloak.org).
Данное решение реализовано в виде двух Terraform модулей:
* [keycloak-deploy](#kc-deploy)
* [keycloak-config](#kc-config)
Разбиение решения на два модуля вызвано тем, что [Keycloak Terraform провайдер](https://registry.tfpla.net/providers/mrparkers/keycloak/latest/docs) требует уже работающего (alive) Keycloak.
### Модуль keycloak-deploy
Модуль `keycloak-deploy` создаёт следующие объекты в Yandex Cloud:
* кластер [Managed Service for PostgreSQL](https://cloud.yandex.ru/docs/managed-postgresql/) - для хранения конфигурации Keycloak
* сертификат [Let's Encrypt](https://letsencrypt.org/) для веб-сервера Keycloak
* статический [публичный IP-адрес](https://cloud.yandex.ru/docs/vpc/concepts/address#public-addresses) для ВМ Keycloak
* [группу безопасности](https://cloud.yandex.ru/docs/vpc/concepts/security-groups) для ВМ Keycloak
* ВМ с решением Keycloak
С полным списком входных параметров модуля можно ознакомиться [по ссылке](./keycloak-deploy/variables.tf).
После завершения своей работы модуль возвращает значение `FQDN` для ВМ с развёрнутым решением Keycloak, например, `kc1.mydom.net`
### Модуль keycloak-config
Модуль `keycloak-config` выполняет следующие действия:
* создаёт [федерацию удостоверений](https://cloud.yandex.ru/docs/organization/add-federation) в Yandex Cloud
* создаёт Realm и сопутствующие объекты в конфигурации Keycloak
* обеспечивает обмен сертификатами между федерацией Yandex Cloud и Keycloak Realm
* создаёт учётную запись для тестового пользователя в Keycloak
* импортирует учётную запись тестового пользователя из Keycloak в организацию Yandex Cloud
С полным списком входных параметров модуля можно ознакомиться [по ссылке](./keycloak-config/variables.tf).
После завершения своей работы модуль возвращает значение `URL` федерации удостоверений, например, `https://console.yandex.ru/federations/bpf3375ucdgp5dxq823tt`
### Синхронизация данных между TF модулями
Модуль `keycloak-config` использует часть входных и выходных данных модуля `keycloak-deploy`.
Развёртывание решения требует последовательного запуска сначала модуля `keycloak-deploy`, а затем модуля `keycloak-config`.
Для исключения ошибок при ручном переносе данных из одного модуля в другой рекомендуется использовать скрипт [sync.sh](./examples/keycloak-config/sync.sh), который синхронизирует нужные данные из модуля `keycloak-deploy` в модуль `keycloak-config`.
## Внешние зависимости
Решение должно развёртываться в уже подготовленной инфраструктуре Yandex Cloud.
Значения параметров инфраструктуры должны передаваться в `TF модули` решения в виде входных переменных.
Перед развёртывание решения в Yandex Cloud уже должны существовать следующие объекты:
* каталог облачных ресурсов (folder) в котором будут развёртываться компоненты решения (`kc_folder_name`)
* [публичная зона](https://cloud.yandex.ru/docs/dns/concepts/dns-zone#public-zones) в сервисе [Cloud DNS](https://cloud.yandex.ru/docs/dns/). Домен, который будет создаваться в сервисе Cloud DNS должен быть предварительно `делегирован` со стороны регистратора домена (`dns_zone_name`)
* сеть (network) в которой будут развёртываться компоненты решения (`kc_network_name`)
* подсеть (subnet) в которой будут развёртываться компоненты решения (`kc_subnet_name`)
В списке выше в круглых скобках указаны имена входных переменных для развёртывания из [keycloak-deploy](./examples/keycloak-deploy/main.tf).
## Порядок развёртывания решения
Развёртывание решения предполагается под управлением ОС `Linux` или `MacOS`.
Развёртывание решения под управлением ОС `Windows` не тестировалось.
1. Загрузить решение из репозитория на [github.com](https://github.com/yandex-cloud/yc-solution-library-for-security):
```bash
curl -s https://raw.githubusercontent.com/yandex-cloud/yc-solution-library-for-security/master/auth_and_access/keycloak/examples/install.sh | bash
```
2. Перейти в папку с примером развёртывания модуля [keycloak-deploy](./examples/keycloak-deploy/):
```bash
cd keycloak/keycloak-deploy
pwd
```
3. `Важно!` Убедиться что все [внешние зависимости](#ext-dep) созданы.
4. Проверить значения переменных в файле [main.tf](./examples/keycloak-deploy/main.tf) и скорректировать их при необходимости.
5. Выполнить инициализацию Terraform:
```bash
source ../env-yc.sh
terraform init
```
6. Выполнить развёртывание `keycloak-deploy`:
```bash
terraform apply
```
Обработка запроса на выдачу сертификата в сервисе [Let's Encrypt](https://letsencrypt.org/) может выполняться `до 30 минут`!
7. Опционально. Проверить состояние выданного сертификата Let's Encrypt:
```bash
yc cm certificate list
```
8. Перейти в папку с примером развёртывания модуля [keycloak-config](./examples/keycloak-config/):
```bash
cd ../keycloak-config
pwd
```
9. Выполнить синхронизацию параметров между TF модулями:
```bash
bash sync.sh
```
10. Проверить значения переменных в файле [main.tf](./examples/keycloak-config/main.tf) и скорректировать их при необходимости.
11. Выполнить инициализацию Terraform:
```bash
terraform init
```
12. Выполнить развёртывание `keycloak-config`:
```bash
terraform apply
```
13. Опционально. Проверить наличие тестовой учётной записи Keycloak в организации Yandex Cloud с помощью `yc CLI`:
```bash
ORG_ID=$(cat terraform.tfstate | jq -r '.resources[] | select(.type == ('\"yandex_organizationmanager_saml_federation\"')) | .instances[0].attributes.organization_id')
yc organization-manager user list --organization-id=$ORG_ID
```
## Результаты развёртывания
В результате развёртывания решения в Yandex Cloud будут созданы следующие объекты:
* [федерация удостоверений]((https://cloud.yandex.ru/docs/organization/add-federation)) в указанной [организации](https://cloud.yandex.ru/docs/organization/add-federation)
* `сертификат` [Let's Encrypt](https://letsencrypt.org/) для ВМ с Keycloak в сервисе [Certificate Manager](https://cloud.yandex.ru/docs/certificate-manager/)
* `виртуальная машина` с IdP Keycloak интегрированная с федерацией на стороне Yandex Cloud
* `запись в Yandex Cloud DNS` с публичным IP-адресом ВМ Keycloak
* `учётная запись` пользователя в IdP Keycloak и её синхронизация в организации Yandex Cloud
После развёртывания решения останется выдать необходимые [роли](https://cloud.yandex.ru/docs/iam/concepts/access-control/roles) на нужные облачные ресурсы для созданной в организации учётной записи пользователя.
================================================
FILE: auth_and_access/keycloak/examples/README.md
================================================
# Пример развёртывания Keycloak с помощью Terraform модулей
* [keycloak-deploy](../keycloak-deploy/)
* [keycloak-config](../keycloak-config/)
================================================
FILE: auth_and_access/keycloak/examples/env-yc.sh
================================================
#!/bin/bash
export YC_TOKEN=$(yc iam create-token)
export TF_VAR_YC_CLOUD_ID=$(yc config get cloud-id)
================================================
FILE: auth_and_access/keycloak/examples/install.sh
================================================
#!/bin/bash
REPO="https://raw.githubusercontent.com/yandex-cloud/yc-solution-library-for-security/master/auth_and_access/keycloak"
mkdir -p keycloak/keycloak-deploy
mkdir -p keycloak/keycloak-config
FILES="examples/env-yc.sh keycloak/env-yc.sh
examples/keycloak-deploy/main.tf keycloak/keycloak-deploy/main.tf
examples/keycloak-deploy/variables.tf keycloak/keycloak-deploy/variables.tf
examples/keycloak-config/main.tf keycloak/keycloak-config/main.tf
examples/keycloak-config/sync.sh keycloak/keycloak-config/sync.sh"
echo "$FILES" | while read URL FILE;
do
curl -sl "$REPO/$URL" -o "$FILE"
done
================================================
FILE: auth_and_access/keycloak/examples/keycloak-config/main.tf
================================================
# ==================================
# Terraform & Provider Configuration
# ==================================
terraform {
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = "~> 0.84.0"
}
null = {
source = "hashicorp/null"
version = "~> 3.2.1"
}
# https://registry.tfpla.net/providers/mrparkers/keycloak/latest/docs
keycloak = {
source = "mrparkers/keycloak"
version = "~> 4.1.0"
}
}
}
# ===========================
# Call keycloak-config module
# ===========================
module "keycloak-config" {
source = "git::https://github.com/yandex-cloud/yc-solution-library-for-security.git//auth_and_access/keycloak/keycloak-config"
labels = { tag = "keycloak-config" }
# =====================
# Org/Federation values
# =====================
org_id = "bpfqdgu3d2815fyixlks"
fed_name = "kc-fed"
kc_user = {
name = "user1"
pass = "Gu95-paSw38"
domain = "mydom.net"
}
# ==================
# Keycloak VM values
# ==================
kc_realm_name = "kc1"
kc_realm_descr = "My Keycloak Realm"
kc_fqdn = "kc1.mydom.net"
kc_port = "8443"
kc_adm_user = "admin"
kc_adm_pass = "Fr#dR3n48Ga-Mov"
}
================================================
FILE: auth_and_access/keycloak/examples/keycloak-config/sync.sh
================================================
#!/bin/bash
# Sync required input and output values
# from keycloak-deploy to keycloak-config
SRC_PATH="../keycloak-deploy"
SRC_FN=main.tf
DST_FN=main.tf
KC_FQDN=$(terraform -chdir=$SRC_PATH output -raw kc_fqdn)
KC_PORT=$(grep kc_port $SRC_PATH/$SRC_FN | awk -F "\"" '{print $2}')
KC_ADM_USER=$(grep kc_adm_user $SRC_PATH/$SRC_FN | awk -F "\"" '{print $2}')
KC_ADM_PASS=$(grep kc_adm_pass $SRC_PATH/$SRC_FN | awk -F "\"" '{print $2}')
if [[ "$OSTYPE" == "linux-gnu"* ]]; then
sed -i "s/kc_fqdn.*/kc_fqdn = \"$KC_FQDN\"/" $DST_FN
sed -i "s/kc_port.*/kc_port = \"$KC_PORT\"/" $DST_FN
sed -i "s/kc_adm_user.*/kc_adm_user = \"$KC_ADM_USER\"/" $DST_FN
sed -i "s/kc_adm_pass.*/kc_adm_pass = \"$KC_ADM_PASS\"/" $DST_FN
elif [[ "$OSTYPE" == "darwin"* ]]; then
sed -i '' "s/kc_fqdn.*/kc_fqdn = \"$KC_FQDN\"/" $DST_FN
sed -i '' "s/kc_port.*/kc_port = \"$KC_PORT\"/" $DST_FN
sed -i '' "s/kc_adm_user.*/kc_adm_user = \"$KC_ADM_USER\"/" $DST_FN
sed -i '' "s/kc_adm_pass.*/kc_adm_pass = \"$KC_ADM_PASS\"/" $DST_FN
fi
================================================
FILE: auth_and_access/keycloak/examples/keycloak-deploy/main.tf
================================================
# ==================================
# Terraform & Provider Configuration
# ==================================
terraform {
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = "~> 0.84.0"
}
}
}
# ===========================
# Call keycloak-deploy module
# ===========================
module "keycloak-deploy" {
source = "git::https://github.com/yandex-cloud/yc-solution-library-for-security.git//auth_and_access/keycloak/keycloak-deploy"
cloud_id = var.YC_CLOUD_ID
labels = { tag = "keycloak-deploy" }
# ==================
# Keycloak VM values
# ==================
kc_image_folder_id = "standard-images"
kc_image_name = "ubuntu-22-04-lts-v20221226"
kc_folder_name = "infra"
kc_zone_id = "ru-central1-b"
kc_network_name = "infra-net"
kc_subnet_name = "infra-subnet-b"
kc_hostname = "kc1"
kc_vm_sg_name = "kc-sg"
kc_vm_username = "admin"
kc_vm_ssh_key_file = "~/.ssh/id_rsa.pub"
# KC FQDN --> kc1.mydom.net
dns_zone_name = "mydom-net"
kc_ver = "20.0.2"
kc_port = "8443"
kc_adm_user = "admin"
kc_adm_pass = "Fr#dR3n48Ga-Mov"
# =================
# PostgreSQL values
# =================
pg_db_ver = "15"
pg_db_name = "kc1-db"
pg_db_user = "dbadmin"
pg_db_pass = "My82Sup@paS98"
# ===================
# Certificates values
# ===================
kc_cert_path = "/usr/local/etc/certs"
le_cert_name = "kc1"
le_cert_descr = "LE Certificate for Keycloak VM"
le_cert_pub_chain = "cert-pub-chain.pem"
le_cert_priv_key = "cert-priv-key.pem"
}
output "kc_fqdn" {
value = "${module.keycloak-deploy.kc_fqdn}"
}
================================================
FILE: auth_and_access/keycloak/examples/keycloak-deploy/variables.tf
================================================
variable "YC_CLOUD_ID" {
description = "Cloud ID"
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/README.md
================================================
# Keycloak-config Terraform module
================================================
FILE: auth_and_access/keycloak/keycloak-config/federation.tf
================================================
# ========================================================
# YC Federation resource
# Import Keycloak resources into Federation & Organization
# ========================================================
# Create YC Federation
resource "yandex_organizationmanager_saml_federation" kc_fed {
name = var.fed_name
organization_id = var.org_id
issuer = "https://${var.kc_fqdn}:${var.kc_port}/realms/${var.kc_realm_name}"
sso_url = "https://${var.kc_fqdn}:${var.kc_port}/realms/${var.kc_realm_name}/protocol/saml"
sso_binding = "POST"
auto_create_account_on_login = true
security_settings {
encrypted_assertions = true
}
}
# Add Keycloak certificate to the YC Federation
resource "null_resource" "federation_cert" {
provisioner "local-exec" {
command = <<-CMD
echo -----BEGIN CERTIFICATE-----\\n $(curl -s https://${var.kc_fqdn}:${var.kc_port}/realms/${var.kc_realm_name}/protocol/saml/descriptor | awk '{split($0,lst,"X509Certificate>"); print substr(lst[2],1,length(lst[2])-5)}')\\n-----END CERTIFICATE----- | tee ${abspath(path.cwd)}/${var.kc_realm_name}-cert.pem
yc organization-manager federation saml certificate create \
--name=${var.fed_name} \
--federation-id=${yandex_organizationmanager_saml_federation.kc_fed.id} \
--certificate-file=${abspath(path.cwd)}/${var.kc_realm_name}-cert.pem
CMD
}
depends_on = [
keycloak_realm.realm
]
}
# Import Test user account to YC Organization from Keycloak
data "yandex_organizationmanager_saml_federation_user_account" kc_test_user {
federation_id = "${yandex_organizationmanager_saml_federation.kc_fed.id}"
name_id = var.kc_user.name
depends_on = [
null_resource.federation_cert
]
}
output "federation_url" {
value = "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}"
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/keycloak-config.tf
================================================
# ================================
# Keycloak configuration resources
# ================================
# https://registry.tfpla.net/providers/mrparkers/keycloak/latest/docs
provider "keycloak" {
client_id = "admin-cli"
username = var.kc_adm_user
password = var.kc_adm_pass
url = "https://${var.kc_fqdn}:${var.kc_port}"
}
resource "keycloak_realm" "realm" {
realm = var.kc_realm_name
enabled = true
display_name = var.kc_realm_descr
display_name_html = "${var.kc_realm_descr}"
ssl_required = "external"
registration_allowed = false
registration_email_as_username = false
remember_me = false
verify_email = false
reset_password_allowed = false
login_with_email_allowed = false
internationalization {
supported_locales = [ "en" ]
default_locale = "en"
}
security_defenses {
headers {
x_frame_options = "DENY"
content_security_policy = "frame-src 'self'; frame-ancestors 'self'; object-src 'none';"
content_security_policy_report_only = ""
x_content_type_options = "nosniff"
x_robots_tag = "none"
x_xss_protection = "1; mode=block"
strict_transport_security = "max-age=31536000; includeSubDomains"
}
brute_force_detection {
permanent_lockout = false
max_login_failures = 10
wait_increment_seconds = 60
quick_login_check_milli_seconds = 1000
minimum_quick_login_wait_seconds = 60
max_failure_wait_seconds = 900
failure_reset_time_seconds = 43200
}
}
}
resource "keycloak_saml_client" "client" {
realm_id = keycloak_realm.realm.id
name = "${var.fed_name}-federation"
enabled = true
client_id = "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}"
base_url = "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}"
valid_redirect_uris = [ "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}" ]
idp_initiated_sso_relay_state = "https://console.cloud.yandex.ru/federations/${yandex_organizationmanager_saml_federation.kc_fed.id}"
assertion_consumer_redirect_url = "https://console.cloud.yandex.ru"
sign_documents = true
sign_assertions = true
include_authn_statement = true
name_id_format = "username"
force_name_id_format = false
signature_algorithm = "RSA_SHA256"
signature_key_name = "CERT_SUBJECT"
full_scope_allowed = true
client_signature_required = true
force_post_binding = true
encrypt_assertions = true
signing_certificate = file("${abspath(path.module)}/${var.yc_cert}")
encryption_certificate = file("${abspath(path.module)}/${var.yc_cert}")
}
resource "keycloak_generic_protocol_mapper" "role_list_mapper" {
realm_id = keycloak_realm.realm.id
client_id = keycloak_saml_client.client.id
name = "role list"
protocol = "saml"
protocol_mapper = "saml-role-list-mapper"
config = {
"attribute.name" = "Role"
"attribute.nameformat" = "Basic"
"single" = "true"
}
}
resource "keycloak_saml_user_property_protocol_mapper" "property_email" {
realm_id = keycloak_realm.realm.id
client_id = keycloak_saml_client.client.id
name = "X500 email"
user_property = "email"
friendly_name = "email"
saml_attribute_name = "urn:oid:1.2.840.113549.1.9.1"
saml_attribute_name_format = "URI Reference"
}
resource "keycloak_saml_user_property_protocol_mapper" "property_givenname" {
realm_id = keycloak_realm.realm.id
client_id = keycloak_saml_client.client.id
name = "X500 givenName"
user_property = "firstName"
friendly_name = "givenName"
saml_attribute_name = "urn:oid:2.5.4.42"
saml_attribute_name_format = "URI Reference"
}
resource "keycloak_saml_user_property_protocol_mapper" "property_surname" {
realm_id = keycloak_realm.realm.id
client_id = keycloak_saml_client.client.id
name = "X500 surname"
user_property = "lastName"
friendly_name = "surname"
saml_attribute_name = "urn:oid:2.5.4.4"
saml_attribute_name_format = "URI Reference"
}
# Keycloak test user account
resource "keycloak_user" "test_user" {
realm_id = keycloak_realm.realm.id
username = var.kc_user.name
enabled = true
first_name = var.kc_user.name
last_name = var.kc_user.name
email = "${var.kc_user.name}@${var.kc_user.domain}"
attributes = {}
initial_password {
value = var.kc_user.pass
temporary = false
}
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/providers.tf
================================================
# ==================================
# Terraform & Provider Configuration
# ==================================
terraform {
required_providers {
yandex = {
source = "yandex-cloud/yandex"
version = "~> 0.84.0"
}
null = {
source = "hashicorp/null"
version = "~> 3.2.1"
}
# https://registry.tfpla.net/providers/mrparkers/keycloak/latest/docs
keycloak = {
source = "mrparkers/keycloak"
version = "~> 4.1.0"
}
}
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/variables.tf
================================================
# =======================================
# Keycloak-config module. Input variables
# =======================================
variable "labels" {
description = "A set of key/value label pairs to assign."
type = map(string)
default = null
}
# ========================
# Org/Federation variables
# ========================
variable "org_id" {
description = "YC Organization ID"
type = string
default = null
}
variable "fed_name" {
description = "YC Federation name"
type = string
default = null
}
variable "yc_cert" {
description = "Yandex Cloud SSL certificate"
type = string
default = "yc-root.crt"
}
variable "kc_user" {
description = "Keycloak test user account"
type = map(string) # name & password
default = {}
}
# =====================
# Keycloak VM variables
# =====================
variable "kc_fqdn" {
description = "Keycloak public DNS FQDN"
type = string
default = null
}
variable "kc_port" {
description = "Keycloak HTTPS port listener"
type = string
default = null
}
variable "kc_adm_user" {
description = "Keycloak admin user name"
type = string
default = null
}
variable "kc_adm_pass" {
description = "Keycloak admin user password"
type = string
default = null
}
variable "kc_realm_name" {
description = "Keycloak Realm name"
type = string
default = null
}
variable "kc_realm_descr" {
description = "Keycloak Realm description"
type = string
default = null
}
================================================
FILE: auth_and_access/keycloak/keycloak-config/yc-root.crt
================================================
-----BEGIN CERTIFICATE-----
MIIDjzCCAnegAwIBAgIUF3bSIPKEcz0+93czW8h814WWGl8wDQYJKoZIhvcNAQEL
BQAwVzELMAkGA1UEBhMCUlUxDzANBgNVBAgMBk1vc2NvdzEPMA0GA1UECgwGWWFu
ZGV4MRUwEwYDVQQLDAxZYW5kZXguQ2xvdWQxDzANBgNVBAMMBllhbmRleDAeFw0y
MDAyMTIwODI2NTVaFw0yNTAyMTIwODI2NTVaMFcxCzAJBgNVBAYTAlJVMQ8wDQYD
VQQIDAZNb3Njb3cxDzANBgNVBAoMBllhbmRleDEVMBMGA1UECwwMWWFuZGV4LkNs
b3VkMQ8wDQYDVQQDDAZZYW5kZXgwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEK
AoIBAQDYVcxqC0Ienc85C2oD93GvYB172VSPYuy7umjHa/8Xy8KUGmAjO1pJA2Qv
grs0AmymueM6d6Uw0C7MsDY/Z3eOid9ZRnbmJtfx2MzmyA91Y0ZvcIxYXWa4kloE
iLUMGs94ixgBat+erKN836NVF4mFOtLUsueMOkQkdFw6RPlw9NccEmWxb/XfzA2f
ceCjWFeJt1RQSAMPxmsd+s9NmsaZ7dFsn1Vx/ACLdlzxhyCjf7A5FIRZUxEHQF5U
OP7z2bKkErDivFj19XhZ2whHmHNKy2pvrzZ0ufoy2+isW5HzEn1+DO3hwX8pKOOv
jtKi5vqtsdjteGDmF2+lm+RxrkL/AgMBAAGjUzBRMB0GA1UdDgQWBBRVWZqkoCfZ
HnN6vDN6d5l2tQGp7jAfBgNVHSMEGDAWgBRVWZqkoCfZHnN6vDN6d5l2tQGp7jAP
BgNVHRMBAf8EBTADAQH/MA0GCSqGSIb3DQEBCwUAA4IBAQA4/gJ1/dawiBYa4hYp
CFsnWIgoJ9iLgG6mOZ6q0xT8X/zAPkA9EeB75OdFPFruAydRlihdiVfrjbdOYoEg
rTbF1jtWAAK+YQpLohrLp070h5PzXMMvso8Tkg4phxLEGhtsHg+SMFipvg0uTG1C
WttgnHy8tWfrjbrF2MPA846ibHu7nPjhwoQxdd5kILPYLTANc3YzwaiN96f6flZg
edkVDUHMT2AVMpFvbYb1jNqULQ9Xyl5ebdTqLVzJ1WWDN7rUGdv2qDrHOlHeBMU3
2S6djwOizttFSwkj2q0FXAH8UFBTDS63gjSwJVzoSHaeFXo+6iT1b1eKj8sdxcbE
3rA+
-----END CERTIFICATE-----
================================================
FILE: auth_and_access/keycloak/keycloak-deploy/README.md
================================================
# Keycloak-deploy Terraform module
================================================
FILE: auth_and_access/keycloak/keycloak-deploy/dns-cm.tf
================================================
# ===================================
# DNS & Certificate Manager resources
# ===================================
data "yandex_dns_zone" "kc_dns_zone" {
folder_id = "${data.yandex_resourcemanager_folder.kc_folder.id}"
name = var.dns_zone_name
}
locals {
kc_fqdn = "${var.kc_hostname}.${trimsuffix(data.yandex_dns_zone.kc_dns_zone.zone,".")}"
}
# Create DNS record for Keycloak VM with created public ip address
resource "yandex_dns_recordset" "kc_dns_rec" {
zone_id = data.yandex_dns_zone.kc_dns_zone.id
name = var.kc_hostname
type = "A"
ttl = 300
data = ["${yandex_vpc_address.kc_pub_ip.external_ipv4_address[0].address}"]
}
# Create request to the Let's Encrypt service for Keycloak's VM certificate
resource "yandex_cm_certificate" "kc_le_cert" {
folder_id = "${data.yandex_resourcemanager_folder.kc_folder.id}"
name = var.le_cert_name
domains = [ "${local.kc_fqdn}" ]
managed {
challenge_type = "DNS_CNAME"
}
}
# Create domain validation DNS record for Let's Encrypt service
resource "yandex_dns_recordset" "validation_dns_rec" {
zone_id = data.yandex_dns_zone.kc_dns_zone.id
name = yandex_cm_certificate.kc_le_cert.challenges[0].dns_name
type = yandex_cm_certificate.kc_le_cert.challenges[0].dns_type
data = [yandex_cm_certificate.kc_le_cert.challenges[0].dns_value]
ttl = 60
}
output "kc_fqdn" {
value = local.kc_fqdn
}
================================================
FILE: auth_and_access/keycloak/keycloak-deploy/kc-setup.sh
================================================
# ===============================
# Keycloak VM provisioning script
# ===============================
# Get Keycloak input data
source kc-data.sh
# Change Timezone
timedatectl set-timezone Europe/Moscow
# Install Packages
apt-get update > /dev/null
apt-get install -y unzip openjdk-18-jre jq > /dev/null
# Install Yandex Cloud CLI (yc CLI)
YC_PATH="/opt/yc"
mkdir -p ${YC_PATH}
curl -s -O https://storage.yandexcloud.net/yandexcloud-yc/install.sh
chmod u+x install.sh
./install.sh -a -i ${YC_PATH}/ 2>/dev/null
ln -s ${YC_PATH}/bin/yc /usr/bin/yc
rm -f install.sh
sed -i "\$ a source ${YC_PATH}/completion.bash.inc" /etc/profile
# Configuring yc CLI
VM_ID=$(curl -s http://169.254.169.254/latest/meta-data/instance-id)
FOLDER_ID=$(yc compute instance get $VM_ID --format=json | jq -r .folder_id )
CLOUD_ID=$(yc resource folder get $FOLDER_ID --format=json | jq -r .cloud_id)
yc config profile create default
yc config set cloud-id $CLOUD_ID
yc config set folder-id $FOLDER_ID
unset CLOUD_ID FOLDER_ID VM_ID
# Get Keycloak distro and put files to the right place
curl -sLO https://github.com/keycloak/keycloak/releases/download/$KC_VER/keycloak-$KC_VER.zip
unzip -q keycloak-$KC_VER.zip
rm -f keycloak-$KC_VER/bin/*.bat
mkdir -p /opt/keycloak
cp -R keycloak-$KC_VER/* /opt/keycloak
rm -rf keycloak-$KC_VER/ keycloak-$KC_VER.zip
export PATH=$PATH:/opt/keycloak/bin
kc.sh build
# Get Let's Encrypt certificate from the YC Certificate Manager
# Let's Encrypt should validate certificate request within 30 minutes
mkdir -p $KC_CERT_PATH
status=None
while [ $status != 'ISSUED' ]
do
status=$(yc cm certificate get --full --name=$KC_CERT_NAME --format=json | jq -r .status)
echo $(date +'%H:%M:%S') $status
sleep 60
done
yc cm certificate download --name=$KC_CERT_NAME --chain=$KC_CERT_PATH/$KC_CERT_PUB --key=$KC_CERT_PATH/$KC_CERT_PRIV > /dev/null
# Prepare systemd things
groupadd keycloak
useradd -r -g keycloak -d /opt/keycloak -s /sbin/nologin keycloak
chown -R keycloak:keycloak /opt/keycloak
chmod o+x /opt/keycloak/bin/
cat <[| no | | [app\_cidrs2](#input\_app\_cidrs2) | n/a | `list(string)` |
"192.168.1.0/24",
"192.168.50.0/24",
"192.168.70.0/24"
]
[| no | | [app\_cidrs3](#input\_app\_cidrs3) | n/a | `list(string)` |
"172.16.1.0/24",
"172.16.2.0/24",
"172.16.3.0/24"
]
[| no | | [network\_names](#input\_network\_names) | Yandex Cloud default Zone for provisoned resources | `list(string)` |
"10.10.1.0/24",
"10.10.2.0/24",
"10.10.3.0/24"
]
[| no | | [org\_id](#input\_org\_id) | organization\_id | `string` | `""` | no | | [zones](#input\_zones) | Yandex.Cloud default Zone for provisoned resources | `list(string)` |
"a",
"b",
"c"
]
[| no | ## Outputs No outputs. ================================================ FILE: auth_and_access/org_iac_iam/cloud-level-state/folders_and_bindings.tf ================================================ #Give sa-web-app-tf permission on cloud data "yandex_resourcemanager_cloud" "web-app" { cloud_id = var.CLOUD_ID } data "yandex_iam_service_account" "sa-web-app-tf" { name = "sa-web-app-tf" folder_id = var.FOLDER_ID } resource "yandex_resourcemanager_cloud_iam_member" "compute-admin" { cloud_id = "${data.yandex_resourcemanager_cloud.web-app.id}" role = "compute.admin" member = "serviceAccount:${data.yandex_iam_service_account.sa-web-app-tf.id}" } resource "yandex_resourcemanager_cloud_iam_member" "vpc-admin" { cloud_id = "${data.yandex_resourcemanager_cloud.web-app.id}" role = "vpc.admin" member = "serviceAccount:${data.yandex_iam_service_account.sa-web-app-tf.id}" } resource "yandex_resourcemanager_cloud_iam_member" "dns-admin" { cloud_id = "${data.yandex_resourcemanager_cloud.web-app.id}" role = "dns.admin" member = "serviceAccount:${data.yandex_iam_service_account.sa-web-app-tf.id}" } resource "yandex_resourcemanager_cloud_iam_member" "mdb-admin" { cloud_id = "${data.yandex_resourcemanager_cloud.web-app.id}" role = "mdb.admin" member = "serviceAccount:${data.yandex_iam_service_account.sa-web-app-tf.id}" } resource "yandex_resourcemanager_cloud_iam_member" "storageadmin" { cloud_id = "${data.yandex_resourcemanager_cloud.web-app.id}" role = "storage.admin" member = "serviceAccount:${data.yandex_iam_service_account.sa-web-app-tf.id}" } resource "yandex_resourcemanager_cloud_iam_member" "viewer" { cloud_id = "${data.yandex_resourcemanager_cloud.web-app.id}" role = "viewer" member = "serviceAccount:${data.yandex_iam_service_account.sa-web-app-tf.id}" } resource "yandex_resourcemanager_cloud_iam_member" "serviceAccounts-admin" { cloud_id = "${data.yandex_resourcemanager_cloud.web-app.id}" role = "editor" # soon will be alter on "iam.editor" member = "serviceAccount:${data.yandex_iam_service_account.sa-web-app-tf.id}" } #create sa-app and it binding (prod and non-prod) #prod data "yandex_resourcemanager_folder" "prod-folder" { name = "prod" } data "yandex_resourcemanager_folder" "nonprod-folder" { name = "nonprod" } resource "yandex_iam_service_account" "sa-app-prod" { name = "sa-app-prod" folder_id = data.yandex_resourcemanager_folder.prod-folder.id } resource "yandex_resourcemanager_folder_iam_member" "sa-app-prod-bind1" { folder_id = data.yandex_resourcemanager_folder.prod-folder.id role = "lockbox.payloadViewer" member = "serviceAccount:${yandex_iam_service_account.sa-app-prod.id}" } resource "yandex_resourcemanager_folder_iam_member" "sa-app-prod-bind2" { folder_id = data.yandex_resourcemanager_folder.prod-folder.id role = "storage.uploader" member = "serviceAccount:${yandex_iam_service_account.sa-app-prod.id}" } #non-prod resource "yandex_iam_service_account" "sa-app-non-prod" { name = "sa-app-non-prod" folder_id = data.yandex_resourcemanager_folder.prod-folder.id } resource "yandex_resourcemanager_folder_iam_member" "sa-app-non-prod-bind1" { folder_id = data.yandex_resourcemanager_folder.nonprod-folder.id role = "lockbox.payloadViewer" member = "serviceAccount:${yandex_iam_service_account.sa-app-non-prod.id}" } resource "yandex_resourcemanager_folder_iam_member" "sa-app-non-prod-bind2" { folder_id = data.yandex_resourcemanager_folder.nonprod-folder.id role = "storage.uploader" member = "serviceAccount:${yandex_iam_service_account.sa-app-non-prod.id}" } ================================================ FILE: auth_and_access/org_iac_iam/cloud-level-state/provider.tf ================================================ # ================================== # Terraform & Provider Configuration # ================================== terraform { required_providers { yandex = { source = "yandex-cloud/yandex" } } required_version = ">= 0.13" } provider "yandex" { service_account_key_file = "./sa-key.json" #token = "" cloud_id = var.CLOUD_ID #folder_id = "" } ================================================ FILE: auth_and_access/org_iac_iam/cloud-level-state/terraform_tfvars ================================================ CLOUD_ID = "b1g960ai8eokqvrtinsc" FOLDER_ID = "b1g1m61ve5t5c7gib04l" ================================================ FILE: auth_and_access/org_iac_iam/cloud-level-state/variables.tf ================================================ variable "CLOUD_ID" { description = "cloud_id of your cloud" type = string default = "" } variable "FOLDER_ID" { description = "folder id of first folder" type = string default = "" } variable "zones" { description = "Yandex.Cloud default Zone for provisoned resources" type = list(string) default = ["ru-central1-a", "ru-central1-b", "ru-central1-c"] } variable "network_names" { description = "Yandex Cloud default Zone for provisoned resources" type = list(string) default = ["a", "b", "c"] } variable "app_cidrs" { type = list(string) default = ["192.168.1.0/24", "192.168.50.0/24", "192.168.70.0/24"] } variable "app_cidrs2" { type = list(string) default = ["172.16.1.0/24", "172.16.2.0/24", "172.16.3.0/24"] } variable "app_cidrs3" { type = list(string) default = ["10.10.1.0/24", "10.10.2.0/24", "10.10.3.0/24"] } variable "org_id" { description = "organization_id" type = string default = "" } ================================================ FILE: auth_and_access/org_iac_iam/cloud-level-state/vpc.tf ================================================ # Создание VPC сети resource "yandex_vpc_network" "vpc-web-app" { name = "vpc-web-app" folder_id = var.FOLDER_ID } # Создание подсетей в prod folder resource "yandex_vpc_subnet" "prod-subnet" { folder_id = data.yandex_resourcemanager_folder.prod-folder.id count = 3 name = "prod-${element(var.network_names, count.index)}" zone = element(var.zones, count.index) network_id = yandex_vpc_network.vpc-web-app.id v4_cidr_blocks = [element(var.app_cidrs3, count.index)] } # Создание подсетей в non-prod folder resource "yandex_vpc_subnet" "non-prod-subnet" { folder_id = data.yandex_resourcemanager_folder.nonprod-folder.id count = 3 name = "non-prod-${element(var.network_names, count.index)}" zone = element(var.zones, count.index) network_id = yandex_vpc_network.vpc-web-app.id v4_cidr_blocks = [element(var.app_cidrs2, count.index)] } ================================================ FILE: auth_and_access/org_iac_iam/images/iam_iac.drawio ================================================
"ru-central1-a",
"ru-central1-b",
"ru-central1-c"
]
 1. Сервисный аккаунт обращается к секрету Lockbox через REST
2. Lockbox проверяет права на секрет и на ключ, расшифровывает секрет
3. В гостевую ОС возвращается JSON с секретом
После применения сценария развертывания скрипт удаляет все промежуточные файлы с секретами и удаляет сервисный аккаунт.
# Настройка окружения
Предполагаем, что у вас уже есть доступ в Yandex Cloud, вы знаете идентификатор своего облака (`cloud-id`) и [идентификатор каталога](https://cloud.yandex.ru/docs/resource-manager/operations/folder/get-id) (`folder-id`) в вашем облаке где будут создаваться облачные ресурсы.
## Установка YC CLI
Для развёртывания рабочего окружения установим инструмент `Yandex Cloud CLI (yc)` на свой компьютер (подробная [инструкция](https://cloud.yandex.ru/docs/cli/operations/install-cli#interactive)).
## Установка git
Для загрузки рецепта Terraform установите git [по инструкции](https://git-scm.com/book/ru/v2/Введение-Установка-Git).
## Установка Terraform
Установите инструмент `Terraform` на свой компьютер (если он уже не установлен) по [(инструкции)](https://cloud.yandex.ru/docs/tutorials/infrastructure-management/terraform-quickstart#install-terraform).
### Установка Terraform для Windows:
Распакуйте архив и скопируйте файл terraform.exe в каталог `C:\Windows\System32`
Для корректной установки всех необходимых ресурсов Terraform создайте в домашнем каталоге (`/home/
1. Сервисный аккаунт обращается к секрету Lockbox через REST
2. Lockbox проверяет права на секрет и на ключ, расшифровывает секрет
3. В гостевую ОС возвращается JSON с секретом
После применения сценария развертывания скрипт удаляет все промежуточные файлы с секретами и удаляет сервисный аккаунт.
# Настройка окружения
Предполагаем, что у вас уже есть доступ в Yandex Cloud, вы знаете идентификатор своего облака (`cloud-id`) и [идентификатор каталога](https://cloud.yandex.ru/docs/resource-manager/operations/folder/get-id) (`folder-id`) в вашем облаке где будут создаваться облачные ресурсы.
## Установка YC CLI
Для развёртывания рабочего окружения установим инструмент `Yandex Cloud CLI (yc)` на свой компьютер (подробная [инструкция](https://cloud.yandex.ru/docs/cli/operations/install-cli#interactive)).
## Установка git
Для загрузки рецепта Terraform установите git [по инструкции](https://git-scm.com/book/ru/v2/Введение-Установка-Git).
## Установка Terraform
Установите инструмент `Terraform` на свой компьютер (если он уже не установлен) по [(инструкции)](https://cloud.yandex.ru/docs/tutorials/infrastructure-management/terraform-quickstart#install-terraform).
### Установка Terraform для Windows:
Распакуйте архив и скопируйте файл terraform.exe в каталог `C:\Windows\System32`
Для корректной установки всех необходимых ресурсов Terraform создайте в домашнем каталоге (`/home/If Authoritative = true : take roles from all objects in variable "cloud\_user\_role\_mapping" and make **unique** role as a new key of map with members" | `bool` | `false` | no | | cloud\_id | Cloud-ID where where need to add permissions. Mandatory variable for CLOUD, if omited default CLOUD\_ID will be used | `string` | `null` | no | | cloud\_user\_role\_mapping | Group of IAM User-IDs and it's permissions in CLOUD, where name = JOB Tille
### Example
#cloud\_user\_role\_mapping = [
{
name = "devops"
users = ["userAccount:idxxxxxx1", "federatedUser:idxxxxxx2"]
roles = ["editor", ]
},
{
name = "developers"
users = ["userAccount:idxxxxxx3"]
roles = ["viewer","k8s.editor",]
},
] | `any` | `[]` | no | | folder\_binding\_authoritative | Authoritative. Sets the IAM policy for the FOLDER and replaces any **existing** policy already attached. | `bool` | `false` | no | | folder\_id | Folder-ID where need to add permissions. Mandatory variable for FOLDER, if omited default FOLDER\_ID will be used | `string` | `null` | no | | folder\_user\_role\_mapping | Group of IAM User-IDs and it's permissions in FOLDER, where name = JOB Tille
### Example
#folder\_user\_role\_mapping = [
{
name = "devops"
users = ["userAccount:idxxxxxx1", "federatedUser:idxxxxxx2"]
roles = ["iam.serviceAccounts.user", "k8s.editor", "k8s.cluster-api.cluster-admin", "container-registry.admin"]
},
{
name = "developers"
users = ["userAccount:idxxxxxx3"]
roles = ["k8s.viewer",]
},
] | `any` | `[]` | no | | sa\_role\_mapping | List of SA and it's permissions
### Example
sa\_role\_mapping = [
{
name = "sa-cluster"
roles = ["editor",]
},
{
name = "sa-nodes"
roles = ["container-registry.images.puller",]
},
] | `any` | `[]` | no | ## Outputs | Name | Description | |------|-------------| | ids | List IDs of created service accounts | | names | List Names of created service accounts | | sa | Map with service accounts info , key = service account name | ================================================ FILE: kubernetes-security/auth_and_access/role-model-example/terraform/modules/iam/main.tf ================================================ ### IAM ### Datasource data "yandex_client_config" "client" {} locals { folder_id = var.folder_user_role_mapping == [] && var.sa_role_mapping == [] ? data.yandex_client_config.client.folder_id : var.folder_id cloud_id = var.cloud_id == null ? data.yandex_client_config.client.cloud_id : var.cloud_id } ### SA resource "yandex_iam_service_account" "sa" { for_each = { for v in var.sa_role_mapping : v.name => v } name = each.key folder_id = local.folder_id } locals { folder_user_mappings = chunklist(flatten([for v in var.folder_user_role_mapping : setproduct(v.users, v.roles)]), 2) sa_role_mapping = { for v in var.sa_role_mapping : v.name => v } sa_mappings = chunklist(flatten([for k, v in yandex_iam_service_account.sa : setproduct([v.id], local.sa_role_mapping[v.name].roles)]), 2) } ###Folder Permissions #### Authoritative data "yandex_iam_policy" "bindings" { count = var.folder_binding_authoritative == false ? 0 : 1 dynamic "binding" { for_each = [for v in local.folder_user_mappings : { member = v[0], role = v[1] }] content { role = binding.value.role members = [binding.value.member, ] } } dynamic "binding" { for_each = [for v in local.sa_mappings : { member = v[0], role = v[1] }] content { role = binding.value.role members = ["serviceAccount:${binding.value.member}", ] } } } resource "yandex_resourcemanager_folder_iam_policy" "folder_bindings_policy" { count = var.folder_binding_authoritative == false ? 0 : 1 folder_id = local.folder_id policy_data = data.yandex_iam_policy.bindings[0].policy_data } ####Permissions NON-Authoritative resource "yandex_resourcemanager_folder_iam_member" "folder_sa_member" { count = var.folder_binding_authoritative == false ? length(local.sa_mappings) : 0 folder_id = local.folder_id member = "serviceAccount:${element(local.sa_mappings, count.index)[0]}" role = element(local.sa_mappings, count.index)[1] } resource "yandex_resourcemanager_folder_iam_member" "folder_user_member" { count = var.folder_binding_authoritative == false ? length(local.folder_user_mappings) : 0 folder_id = local.folder_id member = element(local.folder_user_mappings, count.index)[0] role = element(local.folder_user_mappings, count.index)[1] } ### Cloud Permissions locals { cloud_user_mappings = chunklist(flatten([for v in var.cloud_user_role_mapping : setproduct(v.users, v.roles)]), 2) } #### Authoritative resource "yandex_resourcemanager_cloud_iam_binding" "cloud_binding" { for_each = { for v in local.cloud_user_mappings : v[1] => v[0]... if var.cloud_binding_authoritative == true } cloud_id = local.cloud_id members = each.value role = each.key } #### NON-Authoritative resource "yandex_resourcemanager_cloud_iam_member" "cloud_member" { count = var.cloud_binding_authoritative == false ? length(local.cloud_user_mappings) : 0 cloud_id = local.cloud_id member = element(local.cloud_user_mappings, count.index)[0] role = element(local.cloud_user_mappings, count.index)[1] } ================================================ FILE: kubernetes-security/auth_and_access/role-model-example/terraform/modules/iam/outputs.tf ================================================ output "ids" { description = "List IDs of created service accounts" value = [for v in yandex_iam_service_account.sa : v.id] } output "names" { description = "List Names of created service accounts" value = [for v in yandex_iam_service_account.sa : v.name] } output "sa" { description = "Map with service accounts info , key = service account name" value = { for v in yandex_iam_service_account.sa : v.name => v } } ================================================ FILE: kubernetes-security/auth_and_access/role-model-example/terraform/modules/iam/variables.tf ================================================ variable "folder_id" { default = null type = string description = "Folder-ID where need to add permissions. Mandatory variable for FOLDER, if omited default FOLDER_ID will be used" } variable "folder_binding_authoritative" { type = bool default = false description = "Authoritative. Sets the IAM policy for the FOLDER and replaces any **existing** policy already attached." } variable "folder_user_role_mapping" { default = [] type = any description = <
 [Osquery](https://github.com/osquery/osquery) is a tool that allows you to get information about the OS in the format of [SQL queries](https://osquery.io/schema/current/#file_events).
Tasks solved:
- [Query configs, OS/device settings, proccess, open ports, packets](https://github.com/osquery/osquery#what-is-osquery)
- [File Integrity Monitoring with osquery](https://osquery.readthedocs.io/en/stable/deployment/file-integrity-monitoring/)
- [Reading syslog with osquery](https://osquery.readthedocs.io/en/stable/deployment/syslog/)
- [Anomaly detection with osquery](https://osquery.readthedocs.io/en/stable/deployment/anomaly-detection/)
- [Process and socket auditing with osquery ((including eBPF)](https://osquery.readthedocs.io/en/stable/deployment/process-auditing/)
- [Collecting information about containers on the host](https://www.uptycs.com/blog/get-started-using-osquery-for-container-security)
##
[Osquery](https://github.com/osquery/osquery) is a tool that allows you to get information about the OS in the format of [SQL queries](https://osquery.io/schema/current/#file_events).
Tasks solved:
- [Query configs, OS/device settings, proccess, open ports, packets](https://github.com/osquery/osquery#what-is-osquery)
- [File Integrity Monitoring with osquery](https://osquery.readthedocs.io/en/stable/deployment/file-integrity-monitoring/)
- [Reading syslog with osquery](https://osquery.readthedocs.io/en/stable/deployment/syslog/)
- [Anomaly detection with osquery](https://osquery.readthedocs.io/en/stable/deployment/anomaly-detection/)
- [Process and socket auditing with osquery ((including eBPF)](https://osquery.readthedocs.io/en/stable/deployment/process-auditing/)
- [Collecting information about containers on the host](https://www.uptycs.com/blog/get-started-using-osquery-for-container-security)
##
 #### Installing Osquery in K8s
**Specifics of K8s installation**
- It makes sense to install Osquery on K8s nodes in the [daemonset](https://kubernetes.io/docs/concepts/workloads/controllers/daemonset/) format.
- For Osquery to run correctly, you must have access to the K8s node /proc directory and have the flag [hostPID=true](https://github.com/BishopFox/badPods/tree/main/manifests/hostpid), but as the test has shown, that's not enough, and when accessing the /proc host directory from inside the container, the container still has access only to its processes. This is because of the [/proc directory specifics](https://stackoverflow.com/questions/47072586/docker-access-host-proc).
- For this reason (and also based on the test results), we decided to: set for the container the following parameters: `hostNetwork`: *true*, `hostPID`: *true*, `hostIPC`: *true*, `hostPath`: *path: /*, and execute 'chroot' from the container to the host namespace. This entails risks associated with a privileged pod and going beyond the container. These risks can be minimized by a separate namespace with this container and a correct RBAC + Policy Engine, Network Policy, and others.
There are two ways to downgrade container privileges:
- Install the Osquery agent not via K8s, but directly on the nodes (difficulties in administration).
- One team mentions in their [article](https://developer.ibm.com/articles/monitoring-containers-osquery/) that they solved this task by developing a custom extension in [osquery-go](https://github.com/kolide/osquery-go/blob/master/README.md), changing its default folder from /proc to /host/proc, so you just need to mount this folder without any priviledges. **Research is needed**.
**Installing Osquery components in K8s**
#### Installing Osquery in K8s
**Specifics of K8s installation**
- It makes sense to install Osquery on K8s nodes in the [daemonset](https://kubernetes.io/docs/concepts/workloads/controllers/daemonset/) format.
- For Osquery to run correctly, you must have access to the K8s node /proc directory and have the flag [hostPID=true](https://github.com/BishopFox/badPods/tree/main/manifests/hostpid), but as the test has shown, that's not enough, and when accessing the /proc host directory from inside the container, the container still has access only to its processes. This is because of the [/proc directory specifics](https://stackoverflow.com/questions/47072586/docker-access-host-proc).
- For this reason (and also based on the test results), we decided to: set for the container the following parameters: `hostNetwork`: *true*, `hostPID`: *true*, `hostIPC`: *true*, `hostPath`: *path: /*, and execute 'chroot' from the container to the host namespace. This entails risks associated with a privileged pod and going beyond the container. These risks can be minimized by a separate namespace with this container and a correct RBAC + Policy Engine, Network Policy, and others.
There are two ways to downgrade container privileges:
- Install the Osquery agent not via K8s, but directly on the nodes (difficulties in administration).
- One team mentions in their [article](https://developer.ibm.com/articles/monitoring-containers-osquery/) that they solved this task by developing a custom extension in [osquery-go](https://github.com/kolide/osquery-go/blob/master/README.md), changing its default folder from /proc to /host/proc, so you just need to mount this folder without any priviledges. **Research is needed**.
**Installing Osquery components in K8s**
Expand for viewing..........⬇️
**The prepared configuration includes:** - Basic Osquery config with the following options enabled: - Integrity control of critical K8s nodes files (according to CIS Benchmark). - [Osquery packs](https://github.com/osquery/osquery/tree/master/packs) included: incident response, vuln-management; - Proccess events enable. - A configuration file with a script that checks for an Osquery binary on the K8s node and, if necessary, copies it and runs - Network Policies that, by default, prohibit all incoming and outgoing traffic for the Osquery namespace. **Prerequisites:** - A deployed cluster of [Managed Service for Kubernetes](https://cloud.yandex.ru/docs/managed-kubernetes/quickstart). **Installation using Helm:** - Download values.yaml: ``` helm inspect values oci://cr.yandex/sol/osquery-ds-yc --version 0.1.0 > values.yaml ``` - If necessary, customize the configuration in the file or set parameters during installation. - Run installation with the parameters: ``` helm install osquery-ds-yc \ oci://cr.yandex/sol/osquery-ds-yc --version 0.1.0 \ --namespace osquery \ --create-namespace \ -f values.yaml \ --set osqueryArgs="--verbose --disable_events=false --enable_file_events=true --disable_audit=false --audit_allow_config=true --audit_persist=true --audit_allow_process_events=true" ``` - * To enable eBPF proccess events, add the flag `--enable_bpf_events=true` and access the `bpf_process_events` table. Read more in the [docs](https://osquery.readthedocs.io/en/stable/deployment/process-auditing/) **Installation with kubectl apply:** - Download the repository files: ``` git clone https://github.com/yandex-cloud/yc-solution-library-for-security.git ``` - Go to the folder: ``` cd /yc-solution-library-for-security/kubernetes-security/osquery-kubequery/osquery-install-daemonset/ ``` - If necessary, customize the files configmap-config.yaml and configmap-pack_conf.yaml. - Run the following commands: ``` kubectl apply -f ./ns.yaml kubectl apply -f ./ ``` **TBD: Creating a Helm chart**
Expand for viewing..........⬇️
 [Filebeat](https://www.elastic.co/beats/filebeat) is used to send data to ELK. Filebeat has a built-in [Osquery module](https://www.elastic.co/guide/en/beats/filebeat/current/filebeat-module-osquery.html). It's installed using [Helm chart](https://github.com/elastic/helm-charts/tree/main/filebeat). **Prerequisites:** - A deployed cluster of [Managed Service for ElasticSearch](https://cloud.yandex.ru/docs/managed-elasticsearch/operations/cluster-create). - Credentials for the cluster. **Installing components in K8s:** - Go to the folder: ``` cd /yc-solution-library-for-security/kubernetes-security/osquery-kubequery/filebeat-helm/ ``` - Download a certificate for Managed Elastic service (shared by all): ``` mkdir ~/.elasticsearch && \ wget "https://storage.yandexcloud.net/cloud-certs/CA.pem" -O ~/.elasticsearch/root.crt && \ chmod 0600 ~/.elasticsearch/root.crt cp ~/.elasticsearch/root.crt ./elastic-certificate.pem ``` - Create a secret with an ELK certificate in a K8s cluster: ``` kubectl create secret generic elastic-certificate-pem --from-file=./elastic-certificate.pem ``` - Create a secret with ELK credentials in a K8s cluster (replace with your values): ``` kubectl create secret generic security-master-credentials --from-literal=username=admin --from-literal=password=P@ssword ``` - Prepare an existing ./values.yaml file in the folder (edit). ``` Set the ELK name for the extraEnvs host: extraEnvs: - name: "ELASTICSEARCH_HOSTS" value: "c-c9qfrs7u8i6g59dkb0vj.rw.mdb.yandexcloud.net:9200" Edit the configuration file if needed. ``` - Install the Helm chart with the modified Helm file named "values" ``` helm repo add elastic https://helm.elastic.co helm install filebeat elastic/filebeat -f values.yaml ``` - Check for entries in the ELK database in the Filebeat-osquery index (create an index pattern). - A Filebeat-osquery index will appear in Elastic. - **TBD: Creating a separate dashboard in ELK for Osquery (installed packages, shell commands, open ports, OS versions, node versions, etc.).**
Expand for viewing..........⬇️
 To send results to Splunk, use [fluentd splunk hec plugin](https://github.com/splunk/fluent-plugin-splunk-hec). It's installed using [helm-chart](https://github.com/splunk/splunk-connect-for-kubernetes/tree/develop/helm-chart/splunk-connect-for-kubernetes/charts/splunk-kubernetes-logging). **Prerequisites:** - Splunk has been deployed. - [HTTP Event Collector](https://docs.splunk.com/Documentation/SplunkCloud/8.2.2105/Data/UsetheHTTPEventCollector#Configure_HTTP_Event_Collector_on_Splunk_Enterprise) has been configured. - You have a HEC token for sending events. **Installing components in K8s** - Go to the folder: ``` cd /yc-solution-library-for-security/kubernetes-security/osquery-kubequery/fluentsplunk-helm/ ``` - Prepare an existing ./values.yaml file in the folder (edit) or download the [original one](https://github.com/splunk/splunk-connect-for-kubernetes/blob/develop/helm-chart/splunk-connect-for-kubernetes/charts/splunk-kubernetes-logging/values.yaml). - Set the Splunk host name: ``` splunk: hec: host: 51.250.7.127 (specify your value) ``` - Install a Helm chart specifying the ./values.yaml file, your HEC Token, and SSL settings: ``` helm install my-splunk-logging -f values.yaml --set splunk.hec.insecureSSL=true --set splunk.hec.token=Expand for viewing..........⬇️
 - Go to the folder: ``` cd /yc-solution-library-for-security/kubernetes-security/osquery-kubequery/kubequery/kubequery-with-elastic-filebeat/ ``` - Create a namespace: ``` kubectl create ns kubequery ``` - Download a certificate for Managed Elastic service (shared by all): ``` mkdir ~/.elasticsearch && \ wget "https://storage.yandexcloud.net/cloud-certs/CA.pem" -O ~/.elasticsearch/root.crt && \ chmod 0600 ~/.elasticsearch/root.crt cp ~/.elasticsearch/root.crt ./elastic-certificate.pem ``` - Create a secret with an ELK certificate in the K8s cluster: ``` kubectl create secret generic elastic-certificate-pem --from-file=./elastic-certificate.pem -n kubequery ``` - Create a secret with ELK credentials in the K8s cluster (replace with your values): ``` kubectl create secret generic security-master-credentials --from-literal=username=admin --from-literal=password=P@ssword -n kubequery ``` - In the ./configmap-filebeat.yaml file, specify the value of `output.elasticsearch`: *hosts: "c-c9qfrs7u8i6g59dkb0vj.rw.mdb.yandexcloud.net:9200"* (your value). - Download Helm chart files using the command: ``` git clone https://github.com/Uptycs/kubequery.git ``` - Copy the prepared files to the chart folder: ``` cp ./*.yaml ./kubequery/charts/kubequery/templates/ ``` - Delete the ns creation file from the chart folder: ``` rm ./kubequery/charts/kubequery/templates/namespace.yaml ``` - In the ./kubequery/charts/kubequery/values.yaml file, specify the value of the cluster name `cluster`: *mycluster*. - Install Helm chart from a local working folder: ``` helm install my-kubequery ./kubequery/charts/kubequery/ ``` A filebeat-kubequery index will appear in Elastic. **TBD: Creating a Helm chart for convenience and contributing it to kubequery**Expand for viewing..........⬇️
 - Go to the folder: ``` cd /yc-solution-library-for-security/kubernetes-security/osquery-kubequery/kubequery/kubequery-with-splunk/ ``` - Create a namespace: ``` kubectl create ns kubequery ``` - Create a secret to store an HEC token: ``` kubectl create secret generic splunk-hec-secret --from-literal=splunk_hec_token= [Osquery](https://github.com/osquery/osquery) - инструмент, который позволяет получать информацию об ОС в формате [SQL запросов](https://osquery.io/schema/current/#file_events).
Решаемые задачи:
- [Query configs, OS/device settings, proccess, open ports, packets](https://github.com/osquery/osquery#what-is-osquery)
- [File Integrity Monitoring with osquery](https://osquery.readthedocs.io/en/stable/deployment/file-integrity-monitoring/)
- [Reading syslog with osquery](https://osquery.readthedocs.io/en/stable/deployment/syslog/)
- [Anomaly detection with osquery](https://osquery.readthedocs.io/en/stable/deployment/anomaly-detection/)
- [Process and socket auditing with osquery (включая eBPF)](https://osquery.readthedocs.io/en/stable/deployment/process-auditing/)
- [Сбор Информации о containers на хосте)](https://www.uptycs.com/blog/get-started-using-osquery-for-container-security)
- др.
##
[Osquery](https://github.com/osquery/osquery) - инструмент, который позволяет получать информацию об ОС в формате [SQL запросов](https://osquery.io/schema/current/#file_events).
Решаемые задачи:
- [Query configs, OS/device settings, proccess, open ports, packets](https://github.com/osquery/osquery#what-is-osquery)
- [File Integrity Monitoring with osquery](https://osquery.readthedocs.io/en/stable/deployment/file-integrity-monitoring/)
- [Reading syslog with osquery](https://osquery.readthedocs.io/en/stable/deployment/syslog/)
- [Anomaly detection with osquery](https://osquery.readthedocs.io/en/stable/deployment/anomaly-detection/)
- [Process and socket auditing with osquery (включая eBPF)](https://osquery.readthedocs.io/en/stable/deployment/process-auditing/)
- [Сбор Информации о containers на хосте)](https://www.uptycs.com/blog/get-started-using-osquery-for-container-security)
- др.
##
 #### Установка osquery в k8s
**Особенности установки в k8s**:
- Устанавливать osquery на k8s ноды логично в виде [daemonset](https://kubernetes.io/docs/concepts/workloads/controllers/daemonset/)
- osquery для корректной работы необходимо иметь доступ к директории k8s ноды "/proc" и иметь установленный флаг [hostPID=true] (https://github.com/BishopFox/badPods/tree/main/manifests/hostpid), но как выяснилось в результате теста этого недостаточно и при обращении изнутри контейнера к хостовой директории /proc контейнер все равно имеет доступ только к своим процессам. Это связано с [особенностями /proc директории](https://stackoverflow.com/questions/47072586/docker-access-host-proc)
- По причине выше и результатам тестов было найдено решение: устанавливать контейнеру параметры: hostNetwork: true, hostPID: true, hostIPC: true, "hostPath:path: /" и выполнять из него chroot в хостовый namespace. Это влечет за собой риски связанные с привелигированным подом и выходом за пределы контейнера, которые могут быть минимизированы отдельным namespace с данным контейнером и правильным RBAC + policy engine, network policy, и др.
Существуют 2 способа понизить привилегии контейнера:
- устанавливать агент osquery не через k8s, а напрямую на ноды (трудности в администрировании)
- одна команда [в статье](https://developer.ibm.com/articles/monitoring-containers-osquery/) упоминает, что справилась с этой задачей разработав свой кастомный extension используя [osquery-go](https://github.com/kolide/osquery-go/blob/master/README.md) и в нем изменили default folder с /proc на /host/proc тем самым требуется лишь монтирование данного фолдера без привелегий **Необходим research**
**Установка компонентов osquery в k8s**
#### Установка osquery в k8s
**Особенности установки в k8s**:
- Устанавливать osquery на k8s ноды логично в виде [daemonset](https://kubernetes.io/docs/concepts/workloads/controllers/daemonset/)
- osquery для корректной работы необходимо иметь доступ к директории k8s ноды "/proc" и иметь установленный флаг [hostPID=true] (https://github.com/BishopFox/badPods/tree/main/manifests/hostpid), но как выяснилось в результате теста этого недостаточно и при обращении изнутри контейнера к хостовой директории /proc контейнер все равно имеет доступ только к своим процессам. Это связано с [особенностями /proc директории](https://stackoverflow.com/questions/47072586/docker-access-host-proc)
- По причине выше и результатам тестов было найдено решение: устанавливать контейнеру параметры: hostNetwork: true, hostPID: true, hostIPC: true, "hostPath:path: /" и выполнять из него chroot в хостовый namespace. Это влечет за собой риски связанные с привелигированным подом и выходом за пределы контейнера, которые могут быть минимизированы отдельным namespace с данным контейнером и правильным RBAC + policy engine, network policy, и др.
Существуют 2 способа понизить привилегии контейнера:
- устанавливать агент osquery не через k8s, а напрямую на ноды (трудности в администрировании)
- одна команда [в статье](https://developer.ibm.com/articles/monitoring-containers-osquery/) упоминает, что справилась с этой задачей разработав свой кастомный extension используя [osquery-go](https://github.com/kolide/osquery-go/blob/master/README.md) и в нем изменили default folder с /proc на /host/proc тем самым требуется лишь монтирование данного фолдера без привелегий **Необходим research**
**Установка компонентов osquery в k8s**
Развернуть для просмотра..........⬇️
**Подготовленная конфигурация включает**: - основной конфиг osquery с включенным: - контролем целостности критичных k8s nodes файлов (согласно CIS Benchmark) - включенными [osquery packs](https://github.com/osquery/osquery/tree/master/packs): "incident response", "vuln-management" - включенным proccess events - конфиг со скриптом, который проверяет наличие osquery бинарника на k8s ноде и при необходимости копирует его и запускает - network policy, которые по умолчанию запрещают весь входящий и исходящший траффик namespace "osquery" **Прериквизиты**: - развернутый кластер [Managed Service for Kubernetes](https://cloud.yandex.ru/docs/managed-kubernetes/quickstart) **Установка с помощью helm**: - скачайте values.yaml: ``` helm inspect values oci://cr.yandex/sol/osquery-ds-yc --version 0.1.0 > values.yaml ``` - при необходимости кастомизируйте конфигурацию в файле либо задайте параметры при установке - выполгните установку с параметрами: ``` helm install osquery-ds-yc \ oci://cr.yandex/sol/osquery-ds-yc --version 0.1.0 \ --namespace osquery \ --create-namespace \ -f values.yaml \ --set osqueryArgs="--verbose --disable_events=false --enable_file_events=true --disable_audit=false --audit_allow_config=true --audit_persist=true --audit_allow_process_events=true" ``` - * для включения eBPF proccess events добавьте флаг "--enable_bpf_events=true" и обращайтесь к таблице "bpf_process_events". Подробнее в [док](https://osquery.readthedocs.io/en/stable/deployment/process-auditing/) **Установка с помощью kubectl apply**: - скачайте файлы репозитория ``` git clone https://github.com/yandex-cloud/yc-solution-library-for-security.git ``` - перейдите в папку ``` cd /yc-solution-library-for-security/kubernetes-security/osquery-kubequery/osquery-install-daemonset/ ``` - при необходимости кастомизируйте файлы: configmap-config.yaml, configmap-pack_conf.yaml - выполните команду ``` kubectl apply -f ./ns.yaml kubectl apply -f ./ ``` - **TBD: создание helm chart**
Развернуть для просмотра..........⬇️
 Для отправки в ELK используется [filebeat](https://www.elastic.co/beats/filebeat). Filebeat имеет встроенный [модуль osquery](https://www.elastic.co/guide/en/beats/filebeat/current/filebeat-module-osquery.html). Устанавливается с помощью [helm-chart](https://github.com/elastic/helm-charts/tree/main/filebeat). **Прериквизиты**: - развернутый кластер [Managed Service for Elasticsearch](https://cloud.yandex.ru/docs/managed-elasticsearch/operations/cluster-create) - credentials от кластера **Установка компонентов в k8s** - перейдите в папку ``` cd /yc-solution-library-for-security/kubernetes-security/osquery-kubequery/filebeat-helm/ ``` - скачайте сертификат Managed Elastic сервиса (общий для всех) ``` mkdir ~/.elasticsearch && \ wget "https://storage.yandexcloud.net/cloud-certs/CA.pem" -O ~/.elasticsearch/root.crt && \ chmod 0600 ~/.elasticsearch/root.crt cp ~/.elasticsearch/root.crt ./elastic-certificate.pem ``` - создать секрет с сертификатом ELK в кластере k8s ``` kubectl create secret generic elastic-certificate-pem --from-file=./elastic-certificate.pem ``` - создать секрет с credentials ELK в кластере k8s (заменить на свои) ``` kubectl create secret generic security-master-credentials --from-literal=username=admin --from-literal=password=P@ssword ``` - подготовить существующий в папке файл ./values.yaml (отредактикровать) ``` задать имя elk хоста extraEnvs: - name: "ELASTICSEARCH_HOSTS" value: "c-c9qfrs7u8i6g59dkb0vj.rw.mdb.yandexcloud.net:9200" при необходимости поменять конфигурационный файл ``` - установить helm chart с указанием модифицированного helm файла values ``` helm repo add elastic https://helm.elastic.co helm install filebeat elastic/filebeat -f values.yaml ``` - проверить наличие записей в базе ELK в индексе filebeat-osquery (создать index pattern) - в elastic появится index "filebeat-osquery" - **TBD: создание отделього dashboard в ELK для osquery (установленные пакеты, шел команды, открытые порты, версии ос и нод и т.д.)**
 - Безопасность Kubernetes
- Аутентификация и управление доступом Managed Kubernetes:
- [Пример настройки ролевых моделей и политик в Managed Service for Kubernetes](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/auth_and_access/role-model-example/README_RU.md)
- Сбор, мониторинг и анализ аудит логов:
- [Анализ логов безопасности k8s в ELK: аудит-логи, policy engine, falco](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_k8s)
- [Экспорт Cilium Flow Logs в Object Storage(s3)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/cilium-s3)
- [Экспорт k8s аудит логов в s3/object storage](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-k8s-to-s3/README.md)
- [Экспорт k8s аудит логов в Yandex Data Streams/Kinesis Data Streams](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-k8s-to-yds)
- Шифрование данных и управление ключами/секретами Managed Kubernetes
- [Управление секретами c SecretManager(Lockbox,Vault)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/encrypt_and_keys/secret-management/README_RU.md)
- Безопасная конфигурация Managed Kubernetes:
- [osquery и kubequery в k8s: osquery (защита k8s nodes), kubequery (анализ конфиг. всего k8s) ](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/osquery-kubequery/README_RU.md)
- CVE mitigations:
- [CVE-2022-0185](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/cve-quickfix/CVE-2022-0185)
- [CVE-2021-4034](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/cve-quickfix/CVE-2021-4034)
- [Таблица сравениня функций решений по безопасности k8s](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/kubernetes-security/choice_of_solutions/Сравнение_функций_k8s_security.pdf)
- [Интеграция Starboard с Yandex Cloud Container Registry с целью сканирования запущенных образов](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/starboard_and_yc-cr/README_RU.md)
##
- Безопасность Kubernetes
- Аутентификация и управление доступом Managed Kubernetes:
- [Пример настройки ролевых моделей и политик в Managed Service for Kubernetes](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/auth_and_access/role-model-example/README_RU.md)
- Сбор, мониторинг и анализ аудит логов:
- [Анализ логов безопасности k8s в ELK: аудит-логи, policy engine, falco](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_k8s)
- [Экспорт Cilium Flow Logs в Object Storage(s3)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/cilium-s3)
- [Экспорт k8s аудит логов в s3/object storage](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-k8s-to-s3/README.md)
- [Экспорт k8s аудит логов в Yandex Data Streams/Kinesis Data Streams](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-k8s-to-yds)
- Шифрование данных и управление ключами/секретами Managed Kubernetes
- [Управление секретами c SecretManager(Lockbox,Vault)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/encrypt_and_keys/secret-management/README_RU.md)
- Безопасная конфигурация Managed Kubernetes:
- [osquery и kubequery в k8s: osquery (защита k8s nodes), kubequery (анализ конфиг. всего k8s) ](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/osquery-kubequery/README_RU.md)
- CVE mitigations:
- [CVE-2022-0185](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/cve-quickfix/CVE-2022-0185)
- [CVE-2021-4034](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/cve-quickfix/CVE-2021-4034)
- [Таблица сравениня функций решений по безопасности k8s](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/kubernetes-security/choice_of_solutions/Сравнение_функций_k8s_security.pdf)
- [Интеграция Starboard с Yandex Cloud Container Registry с целью сканирования запущенных образов](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/kubernetes-security/starboard_and_yc-cr/README_RU.md)
##
 - CI/CD Security
- Secure CI/CD на базе Managed GitLab:
- [Вебинар+материалы:Обнаружение Log4shell и др. уязвимостей в CI/CD на базе Managed GitLab](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/secure_ci_cd_with_webinar):
- [Обнаружение уязвимостей в CI/CD (Ultimate лицензия)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/secure_ci_cd_with_webinar)
- [Обнаружение уязвимостей в CI/CD (Free лицензия)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/secure_ci_cd_with_webinar)
- [Security in Gtilab instance check-list](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/secure_ci_cd_with_webinar/gitlab_instance_sec_checklist/README_RU.md)
- [Выступление про комплаенс и devsecops](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/devsecops-scale/README.md)
#
- CI/CD Security
- Secure CI/CD на базе Managed GitLab:
- [Вебинар+материалы:Обнаружение Log4shell и др. уязвимостей в CI/CD на базе Managed GitLab](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/secure_ci_cd_with_webinar):
- [Обнаружение уязвимостей в CI/CD (Ultimate лицензия)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/secure_ci_cd_with_webinar)
- [Обнаружение уязвимостей в CI/CD (Free лицензия)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/secure_ci_cd_with_webinar)
- [Security in Gtilab instance check-list](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/secure_ci_cd_with_webinar/gitlab_instance_sec_checklist/README_RU.md)
- [Выступление про комплаенс и devsecops](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/secure_ci_cd/devsecops-scale/README.md)
#
 - Безопасность Terraform
- [Сканирование tf файлов с помощью checkov](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/terraform-sec/checkov-yc)
- [Хранение состояния Terraform в Yandex.Cloud Object Storage](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/terraform-sec/remote-backend)
#
- Безопасность Terraform
- [Сканирование tf файлов с помощью checkov](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/terraform-sec/checkov-yc)
- [Хранение состояния Terraform в Yandex.Cloud Object Storage](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/terraform-sec/remote-backend)
#
 # Обратная связь и пожелания
- Доработки, ошибки, contribute: Заводите, пожалуйста с помощью github issue/pr
- Вопросы, пожелания, консультации: Пишите нам в телеграм https://t.me/YandexCloudSecurity
#### Референсная архитектура

================================================
FILE: README.md
================================================
# Yandex Cloud Security Solutions Library
This repo contains Security Solutions from Yandex Cloud Team.
The repository is Archived.
🚚 Solutions from this repository has been moved to https://github.com/yandex-cloud-examples/yc-security-solutions-library
================================================
FILE: README_EN.md
================================================
# 🔐 Yandex.Cloud Security Solution Library
**Yandex.Cloud Security Solution Library** is a set of examples and recommendations collected in a public repository on GitHub. Its purpose is to help companies build a secure infrastructure in the cloud and meet the requirements of various regulators and standards. Yandex.Cloud team has selected the most common tasks that arise when building security in the cloud. They have tested and described relevant scenarios in detail.
#### Brief webinar
[](https://www.youtube.com/watch?v=WZOB9ow0WrA)
#### ☑️ Yandex.Cloud Security Checklist
Checklist for security in the Yandex.Cloud infrastructure
https://cloud.yandex.com/en/docs/overview/security/domains/checklist
# List of solutions
- 🕸 Network security
- [Example of setting up Security Groups (dev/stage/prod): Terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/network-sec/segmentation)
- [Example of installing a VM instance with a firewall (NGFW): Check Point](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/network-sec/checkpoint-1VM)
- [Example of installing two VM instances with an NGFW Check Point: **Active-Active**](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/network-sec/checkpoint-2VM_active-active/README.md)
- [Example of installing two NGFW Check Point VMs: **Active-Passive**](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/network-sec/checkpoint-2VM_active-passive/README.md)
- [An example of creating a site-to-site VPN connection to Yandex.Cloud: Terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/network-sec/vpn)
- 🔑 Authentication and access control
- [Развертывание и управление организацией и правами доступа через IaC terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auth_and_access/org_iac_iam)
- [IAM module with usage examples](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auth_and_access/iam#identity-and-access-management-iam-terraform-module-for-yandexcloud)
- [LDAP user and group synchronization script](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auth_and_access/ad-sync)
- 🦠 Protection against malicious code
- [Deploying Kaspersky Antivirus in Yandex.Cloud (Compute Instance, COI)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/malware-defense/kaspersy-install-in-yc)
- 🐞 Vulnerability management
- [Fault-tolerant operation of PT Application Firewall based on Yandex.Cloud](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/vuln-mgmt/unmng-waf-ptaf-cluster)
- [Installing a vulnerable web application (DVWA) in Yandex.Cloud using Terraform for Managed WAF testing](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/vuln-mgmt/vulnerable-web-app-waf-test)
- [Testing AntiDDos system using Yandex Load Testing](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/vuln-mgmt/anti-ddos-lt/README.md)
- 🔏 Data encryption and key and secret management
- [Encrypting secrets with KMS when transferring the keys to the COI VM container Yandex.Cloud: Terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/encrypt_and_keys/terraform%2BKMS%2BCOI)
- [Encrypting a VM disk in the cloud using YC KMS](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/encrypt_and_keys/encrypt_disk_VM)
- [Yandex Cloud Lockbox password solution](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/encrypt_and_keys/terraform-lockbox-vm-credentials)
- 🔎 Collecting, monitoring, and analyzing audit logs
- [Collecting, monitoring and analyzing audit logs in Yandex Managed Opensearch](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-Opensearch/README_EN.md)
- [Collecting, monitoring and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main)
- [Collecting, monitoring, and analyzing audit logs in an external SIEM ArcSight](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ArcSight)
- [Collecting, monitoring, and analyzing audit logs in an external Splunk](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-Splunk)
- [Collecting, monitoring, and analyzing audit logs in an external Wazuh](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-wazuh/README.md)
- [Use cases and important security events in audit logs](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches)
- [Trails-function-detector: Alerts and response to Information Security events in Audit Trails using Cloud Logging and Cloud Functions + Telegram](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/trails-function-detector)
- [Monitoring Audit Trails and events in Yandex Cloud Monitoring](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/trail_monitoring)
- 👮 Secure configuration
- [Example of a secure configuration for Yandex Cloud Object Storage: Terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/configuration/hardening_bucket)
##
# Обратная связь и пожелания
- Доработки, ошибки, contribute: Заводите, пожалуйста с помощью github issue/pr
- Вопросы, пожелания, консультации: Пишите нам в телеграм https://t.me/YandexCloudSecurity
#### Референсная архитектура

================================================
FILE: README.md
================================================
# Yandex Cloud Security Solutions Library
This repo contains Security Solutions from Yandex Cloud Team.
The repository is Archived.
🚚 Solutions from this repository has been moved to https://github.com/yandex-cloud-examples/yc-security-solutions-library
================================================
FILE: README_EN.md
================================================
# 🔐 Yandex.Cloud Security Solution Library
**Yandex.Cloud Security Solution Library** is a set of examples and recommendations collected in a public repository on GitHub. Its purpose is to help companies build a secure infrastructure in the cloud and meet the requirements of various regulators and standards. Yandex.Cloud team has selected the most common tasks that arise when building security in the cloud. They have tested and described relevant scenarios in detail.
#### Brief webinar
[](https://www.youtube.com/watch?v=WZOB9ow0WrA)
#### ☑️ Yandex.Cloud Security Checklist
Checklist for security in the Yandex.Cloud infrastructure
https://cloud.yandex.com/en/docs/overview/security/domains/checklist
# List of solutions
- 🕸 Network security
- [Example of setting up Security Groups (dev/stage/prod): Terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/network-sec/segmentation)
- [Example of installing a VM instance with a firewall (NGFW): Check Point](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/network-sec/checkpoint-1VM)
- [Example of installing two VM instances with an NGFW Check Point: **Active-Active**](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/network-sec/checkpoint-2VM_active-active/README.md)
- [Example of installing two NGFW Check Point VMs: **Active-Passive**](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/network-sec/checkpoint-2VM_active-passive/README.md)
- [An example of creating a site-to-site VPN connection to Yandex.Cloud: Terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/network-sec/vpn)
- 🔑 Authentication and access control
- [Развертывание и управление организацией и правами доступа через IaC terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auth_and_access/org_iac_iam)
- [IAM module with usage examples](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auth_and_access/iam#identity-and-access-management-iam-terraform-module-for-yandexcloud)
- [LDAP user and group synchronization script](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auth_and_access/ad-sync)
- 🦠 Protection against malicious code
- [Deploying Kaspersky Antivirus in Yandex.Cloud (Compute Instance, COI)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/malware-defense/kaspersy-install-in-yc)
- 🐞 Vulnerability management
- [Fault-tolerant operation of PT Application Firewall based on Yandex.Cloud](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/vuln-mgmt/unmng-waf-ptaf-cluster)
- [Installing a vulnerable web application (DVWA) in Yandex.Cloud using Terraform for Managed WAF testing](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/vuln-mgmt/vulnerable-web-app-waf-test)
- [Testing AntiDDos system using Yandex Load Testing](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/vuln-mgmt/anti-ddos-lt/README.md)
- 🔏 Data encryption and key and secret management
- [Encrypting secrets with KMS when transferring the keys to the COI VM container Yandex.Cloud: Terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/encrypt_and_keys/terraform%2BKMS%2BCOI)
- [Encrypting a VM disk in the cloud using YC KMS](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/encrypt_and_keys/encrypt_disk_VM)
- [Yandex Cloud Lockbox password solution](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/encrypt_and_keys/terraform-lockbox-vm-credentials)
- 🔎 Collecting, monitoring, and analyzing audit logs
- [Collecting, monitoring and analyzing audit logs in Yandex Managed Opensearch](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-Opensearch/README_EN.md)
- [Collecting, monitoring and analyzing audit logs in Yandex Managed Service for Elasticsearch (ELK)](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ELK_main)
- [Collecting, monitoring, and analyzing audit logs in an external SIEM ArcSight](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-ArcSight)
- [Collecting, monitoring, and analyzing audit logs in an external Splunk](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-Splunk)
- [Collecting, monitoring, and analyzing audit logs in an external Wazuh](https://github.com/yandex-cloud/yc-solution-library-for-security/blob/master/auditlogs/export-auditlogs-to-wazuh/README.md)
- [Use cases and important security events in audit logs](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/_use_cases_and_searches)
- [Trails-function-detector: Alerts and response to Information Security events in Audit Trails using Cloud Logging and Cloud Functions + Telegram](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/trails-function-detector)
- [Monitoring Audit Trails and events in Yandex Cloud Monitoring](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/trail_monitoring)
- 👮 Secure configuration
- [Example of a secure configuration for Yandex Cloud Object Storage: Terraform](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/configuration/hardening_bucket)
##


 # Version
**Version-1.0**
- Changelog:
- First version
- Docker images:
- `cr.yandex/sol/cilium-s3:1`
- Helm chart:
- `cr.yandex/sol/cilium-s3-chart:0.1.0`
## Solution Description
Connects via gRPC to hubble-relay and sends netflow events to Object Storage
Then you can pick up these events from Object Storage to any SIEM using [GeeseFS](https://cloud.yandex.ru/docs/storage/tools/geesefs) or other aws compatible plugins
Or using prepared Object Storage integrations in the following SIEMs:
- [Object storage to Splunk](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-Splunk)
- Cilium flow logs to Elasticsearch Скоро!!!
## Installing with helm
#### Prerequisites
- :white_check_mark: Yandex Managed Service for Kubernetes® [with Cilium CNI enabled](https://cloud.yandex.ru/docs/managed-kubernetes/quickstart#kubernetes-cluster-create)
- :white_check_mark: [Object Storage Bucket](https://cloud.yandex.ru/docs/storage/quickstart)
- :white_check_mark: [Created static keys for service account](https://cloud.yandex.ru/docs/iam/operations/sa/create-access-key)
- :white_check_mark: [Installed Helm client](https://helm.sh/ru/docs/intro/install/)
#### Install helm-chart
Install helm hart by replacing the values with your own (specified in the prerequisites)
```Python
helm install cilium-s3-chart oci://cr.yandex/sol/cilium-s3-chart --version 0.1.0 --namespace cilium-s3 --create-namespace \
--set yandex.secretaccesskey=
# Version
**Version-1.0**
- Changelog:
- First version
- Docker images:
- `cr.yandex/sol/cilium-s3:1`
- Helm chart:
- `cr.yandex/sol/cilium-s3-chart:0.1.0`
## Solution Description
Connects via gRPC to hubble-relay and sends netflow events to Object Storage
Then you can pick up these events from Object Storage to any SIEM using [GeeseFS](https://cloud.yandex.ru/docs/storage/tools/geesefs) or other aws compatible plugins
Or using prepared Object Storage integrations in the following SIEMs:
- [Object storage to Splunk](https://github.com/yandex-cloud/yc-solution-library-for-security/tree/master/auditlogs/export-auditlogs-to-Splunk)
- Cilium flow logs to Elasticsearch Скоро!!!
## Installing with helm
#### Prerequisites
- :white_check_mark: Yandex Managed Service for Kubernetes® [with Cilium CNI enabled](https://cloud.yandex.ru/docs/managed-kubernetes/quickstart#kubernetes-cluster-create)
- :white_check_mark: [Object Storage Bucket](https://cloud.yandex.ru/docs/storage/quickstart)
- :white_check_mark: [Created static keys for service account](https://cloud.yandex.ru/docs/iam/operations/sa/create-access-key)
- :white_check_mark: [Installed Helm client](https://helm.sh/ru/docs/intro/install/)
#### Install helm-chart
Install helm hart by replacing the values with your own (specified in the prerequisites)
```Python
helm install cilium-s3-chart oci://cr.yandex/sol/cilium-s3-chart --version 0.1.0 --namespace cilium-s3 --create-namespace \
--set yandex.secretaccesskey=